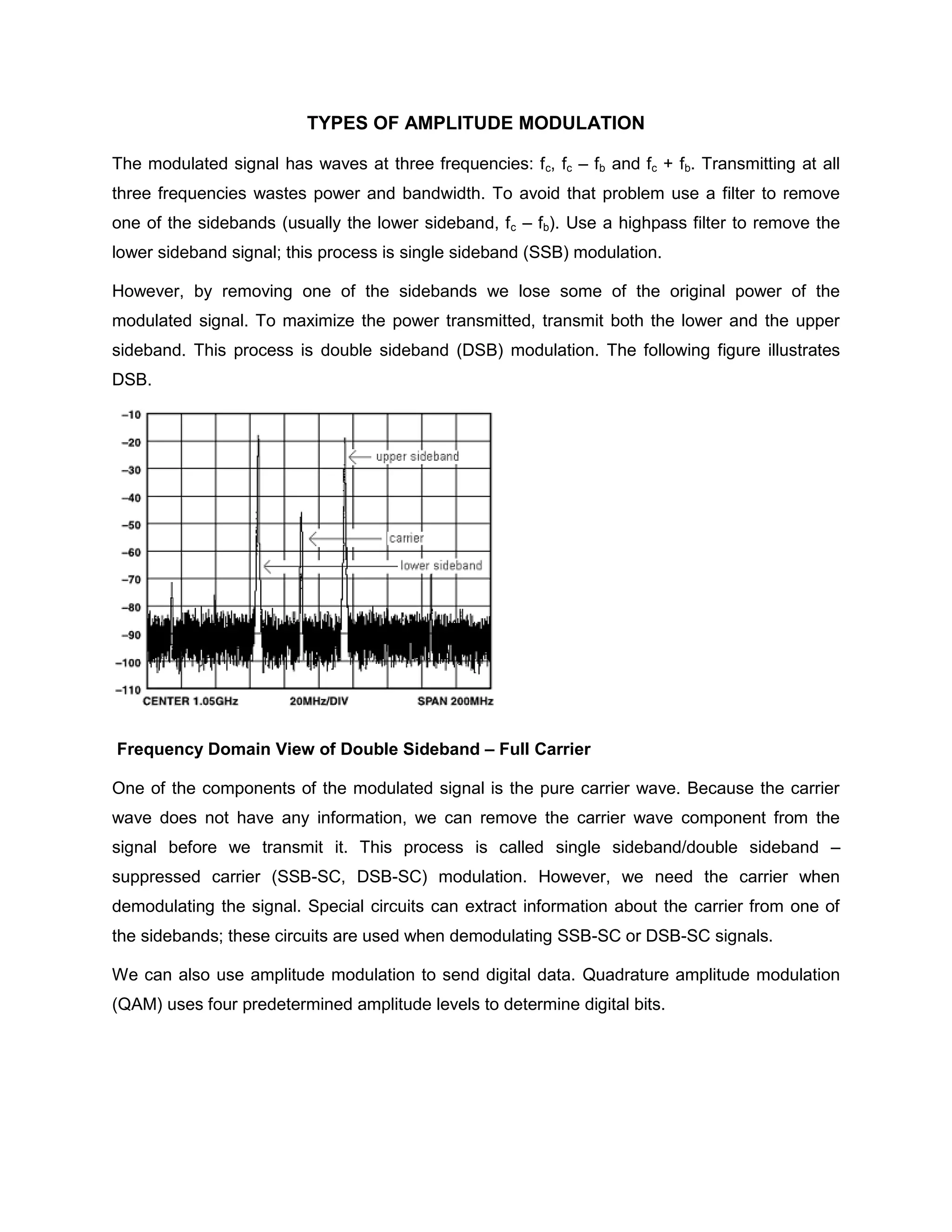
This document discusses types of amplitude modulation including:
- Double sideband full carrier (DSB-FC) which transmits both sidebands and the carrier.
- Double sideband suppressed carrier (DSB-SC) which transmits both sidebands but suppresses the carrier.
- Single sideband suppressed carrier (SSB-SC) which transmits either the upper or lower sideband and suppresses the carrier.
It also discusses power utilization in amplitude modulation, noting that only 33% of transmitted power is used to carry information in the sidebands, while the rest is wasted in the carrier. Finally, it defines modulation index as the ratio of modulation signal amplitude to carrier amplitude, with