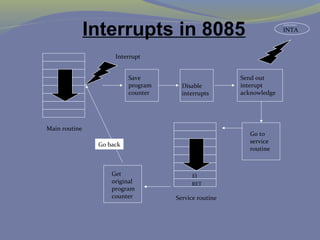
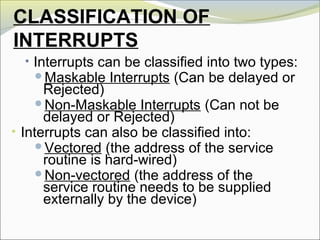
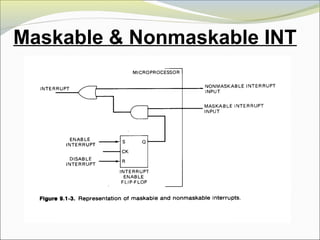
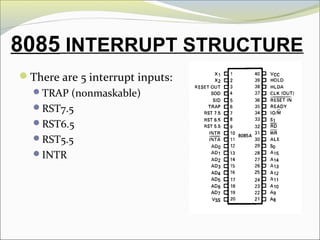
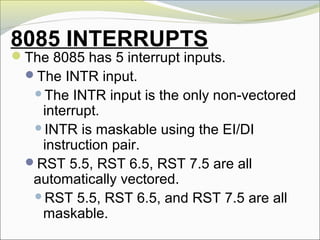
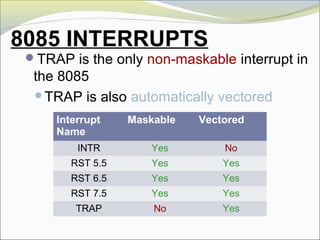
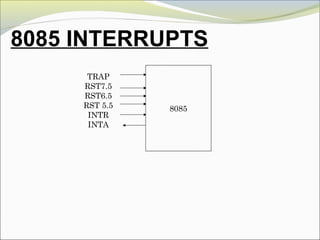
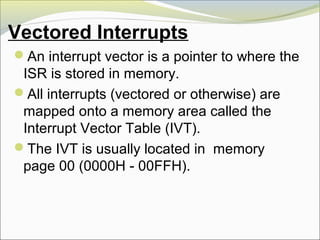
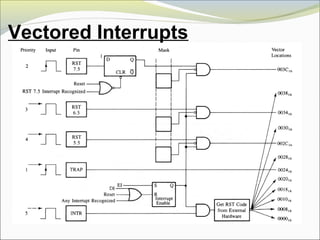
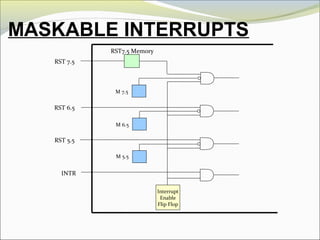
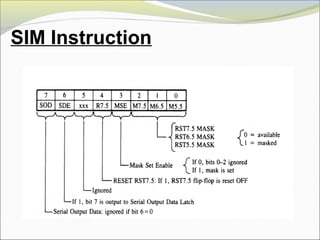
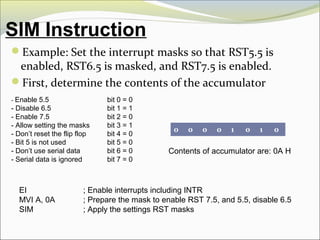
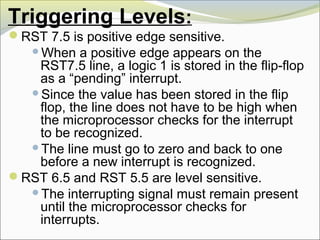
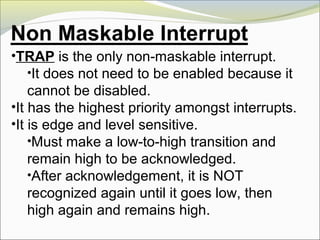
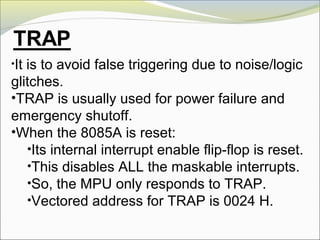
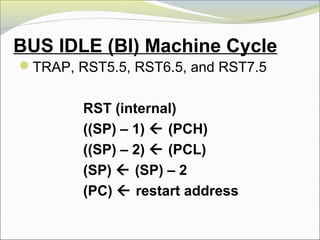
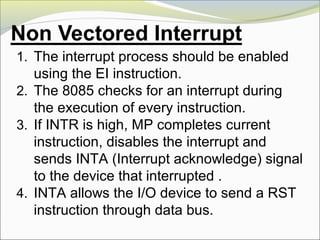
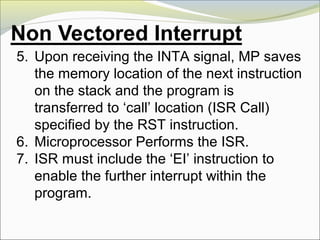
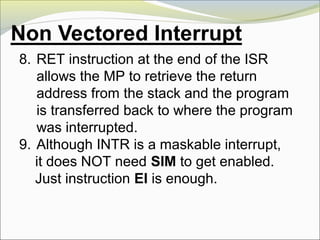
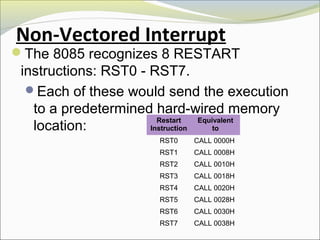
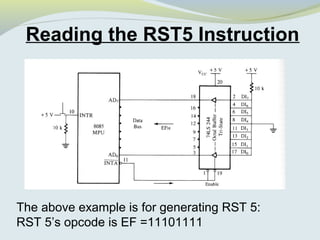
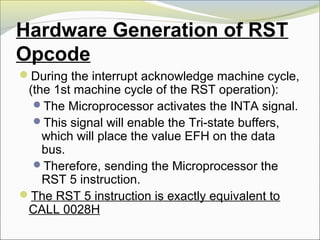
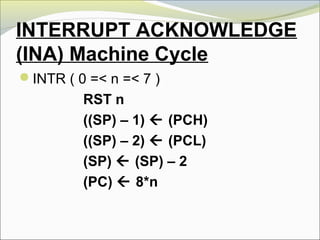
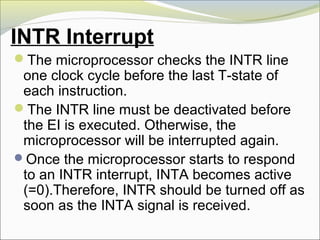
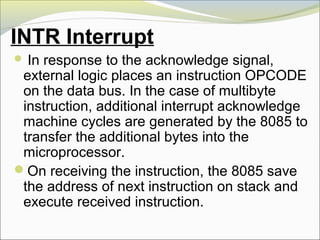
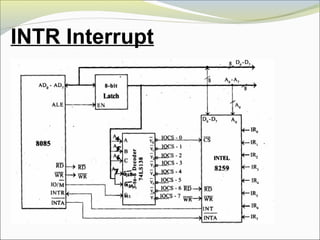
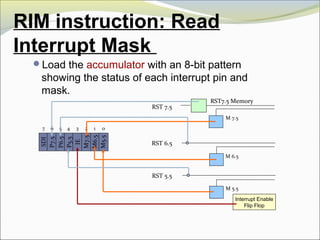
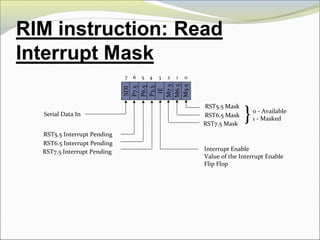
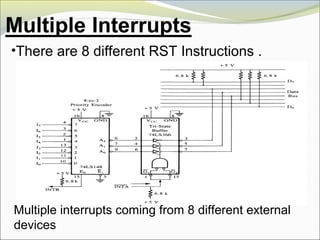
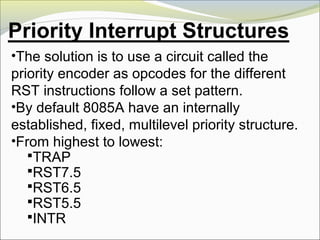
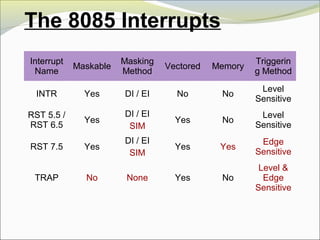
The document discusses interrupts in the 8085 microprocessor. It describes how interrupts work, including the different types of interrupts, how interrupt requests are handled, and the interrupt acknowledge process. It also covers interrupt masking, vectored interrupts, and the interrupt structures in 8085 systems.