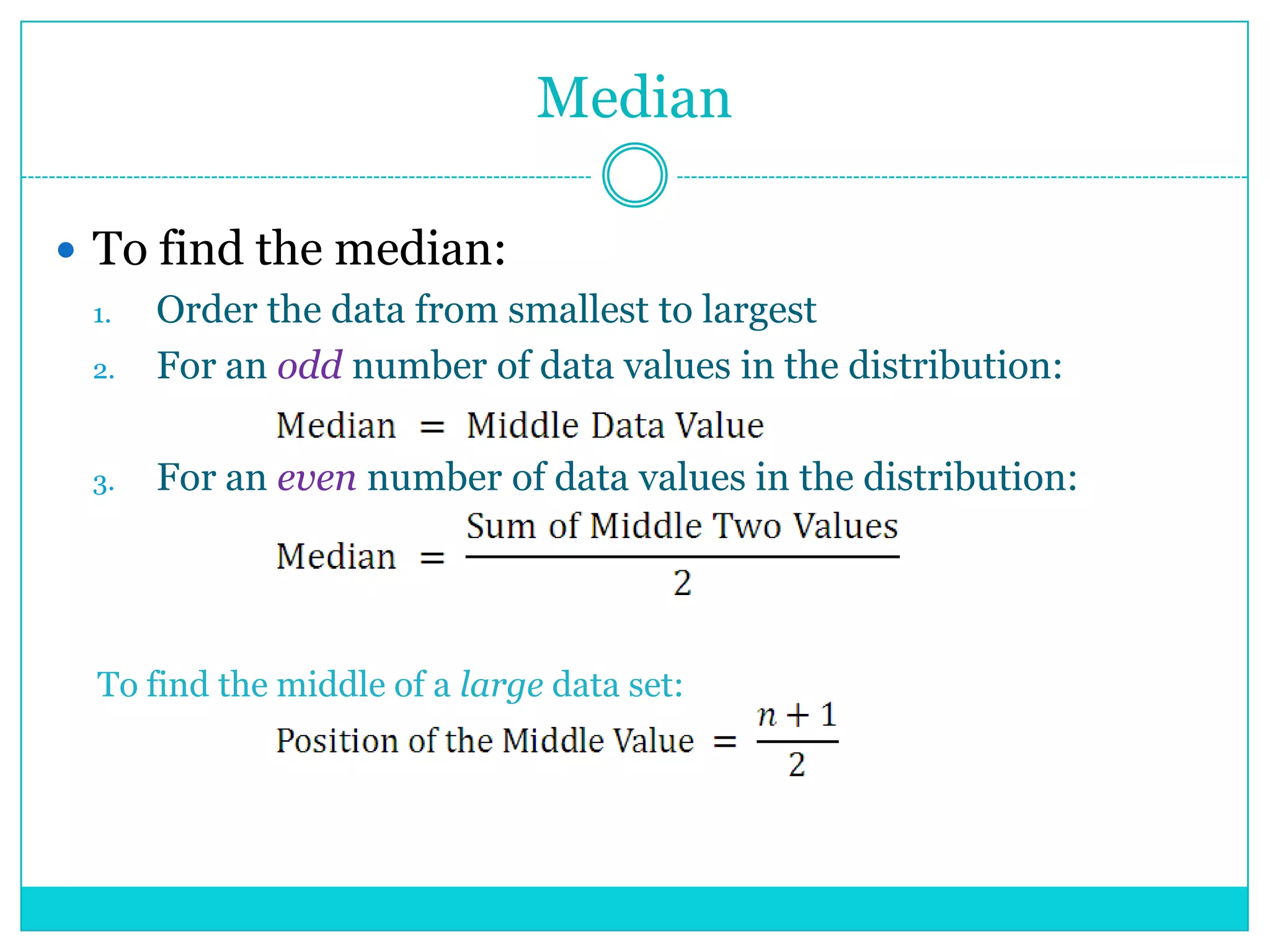
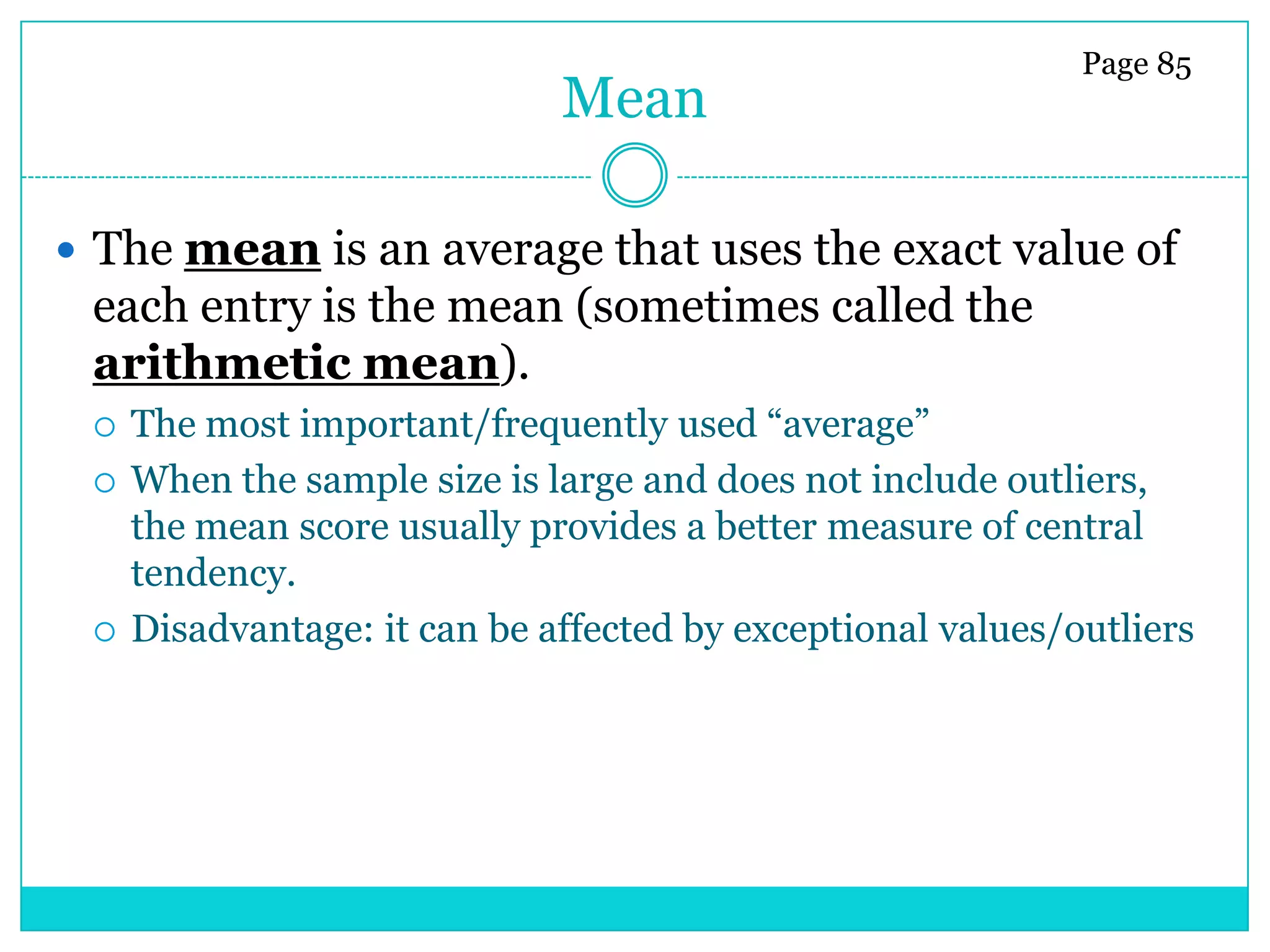
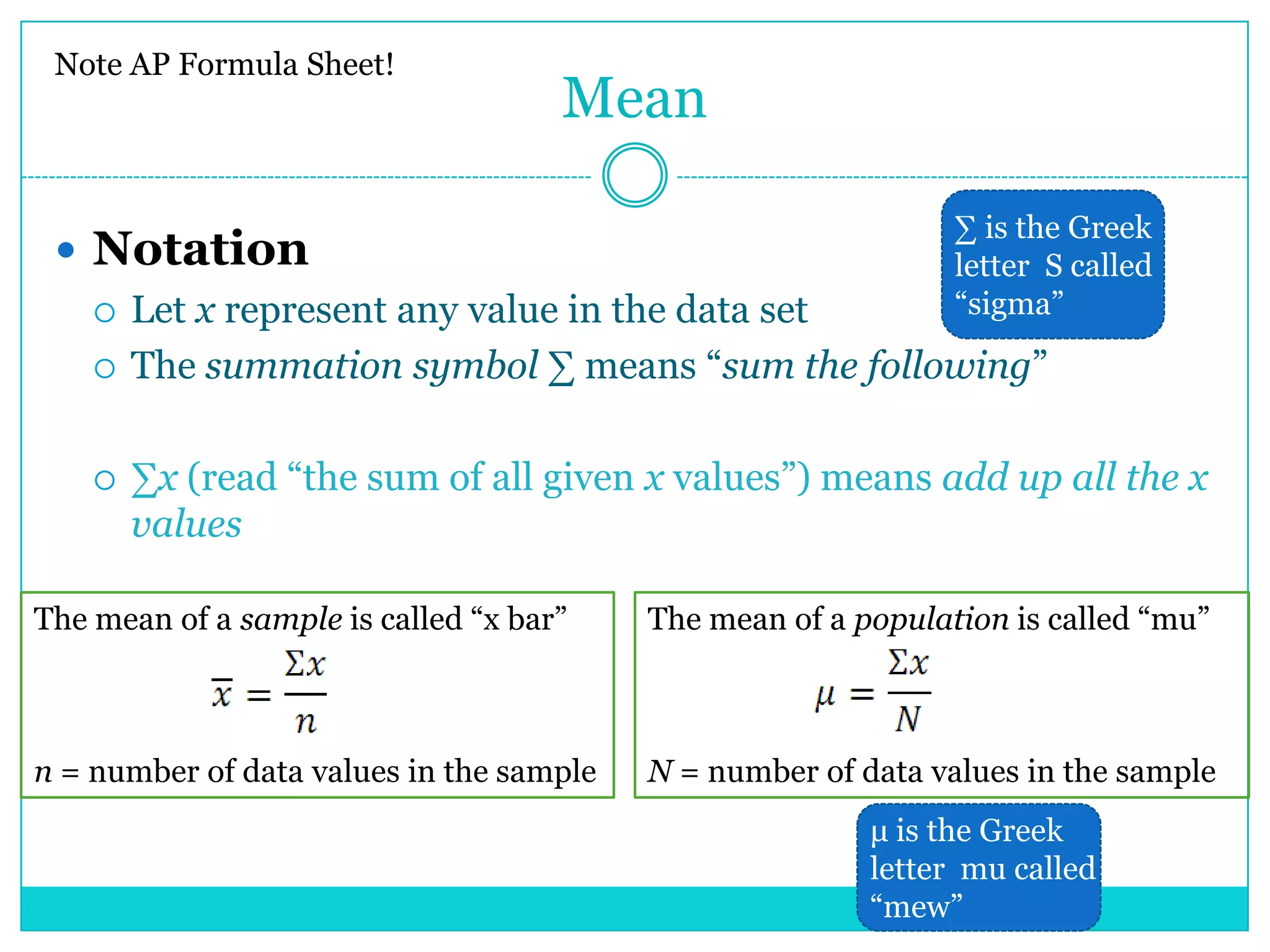
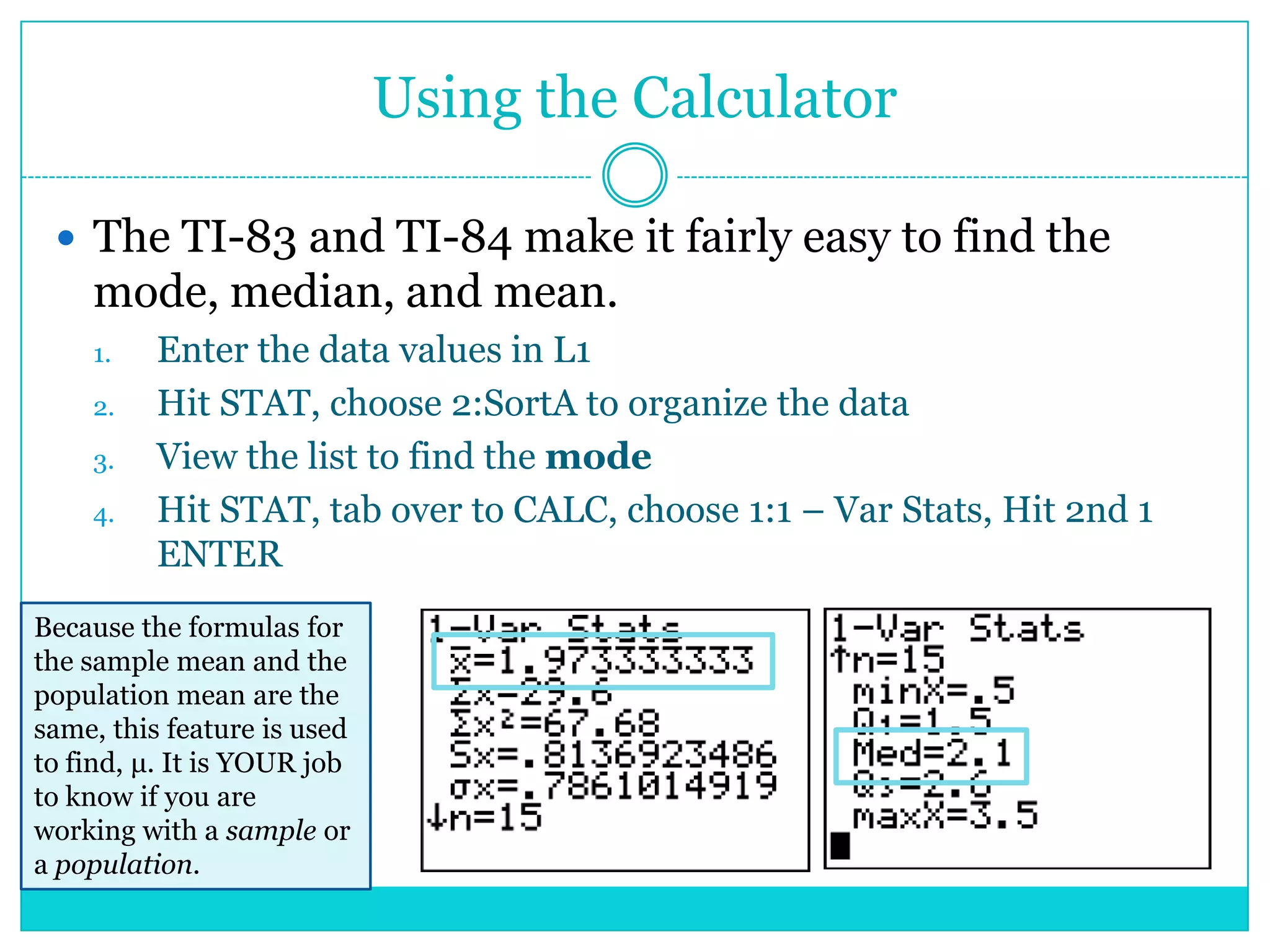
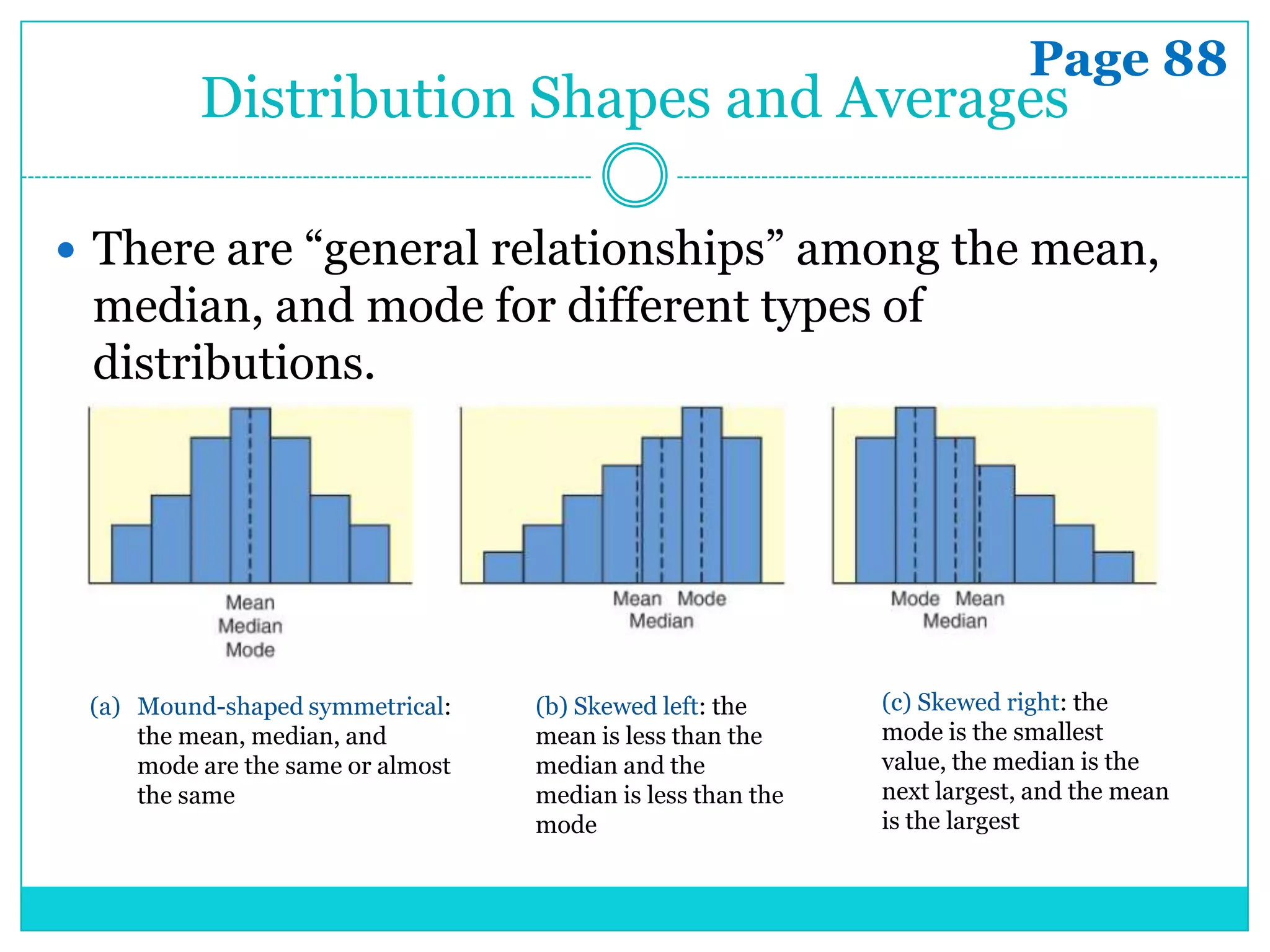
This document discusses different measures of central tendency including the mode, median, and mean. It provides definitions and explanations of how to calculate each one. The mode is the most frequently occurring value, the median is the middle value of an ordered data set, and the mean is the average found by summing all values and dividing by the number of values. The document contrasts these measures and discusses which to use based on the measurement level of the data and shape of the distribution. It also provides examples of how to interpret the mean and median when comparing multiple data sets. Homework problems are assigned from the text.