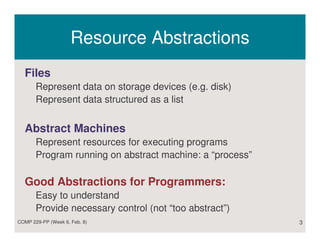
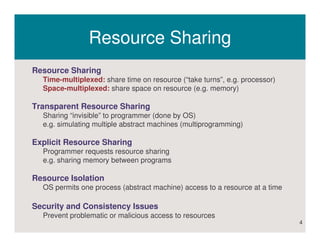
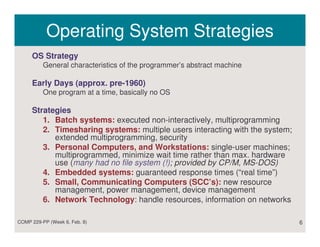
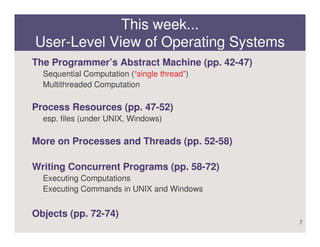
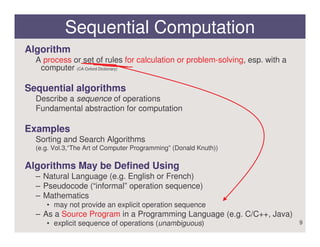
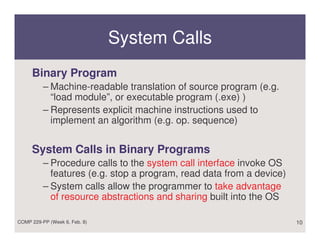
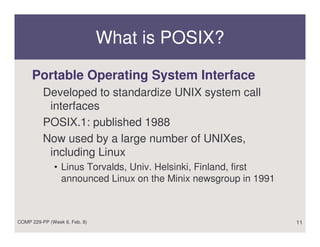
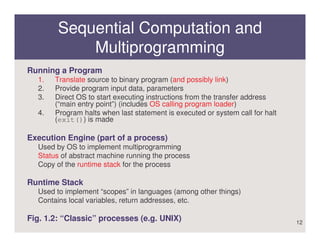
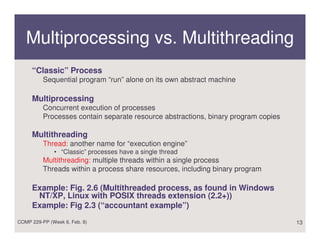
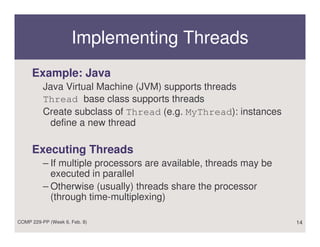
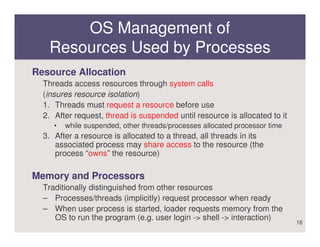
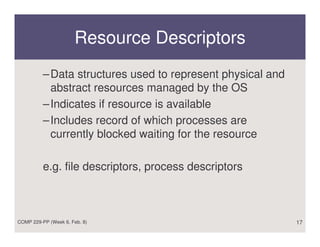
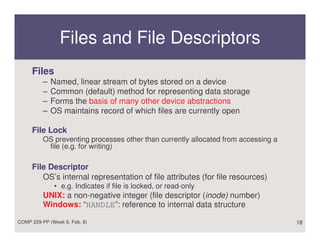
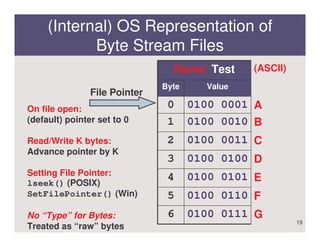
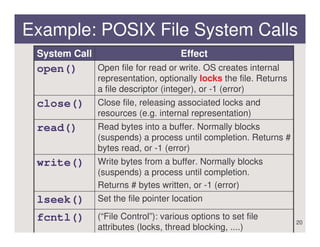
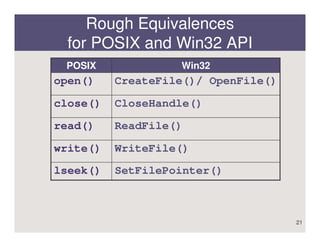
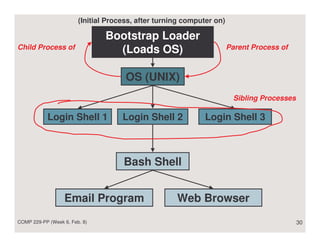
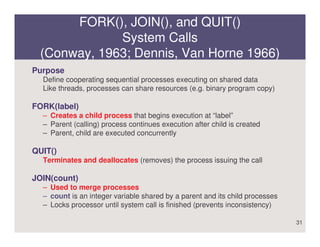
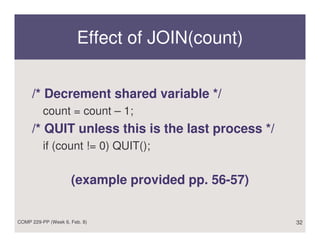
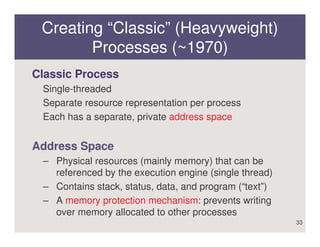
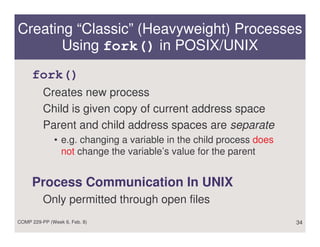
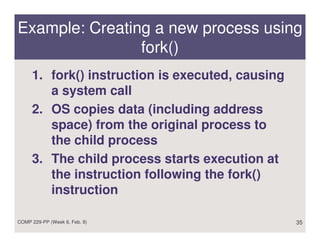
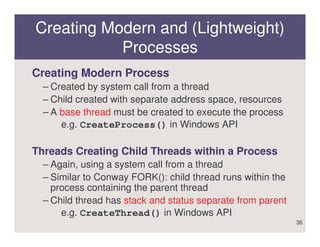
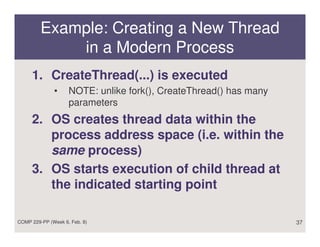
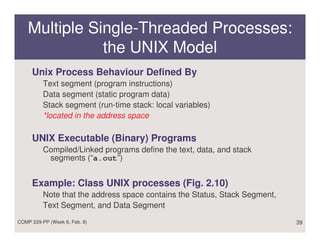
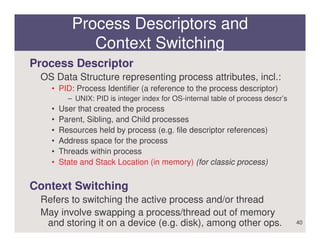
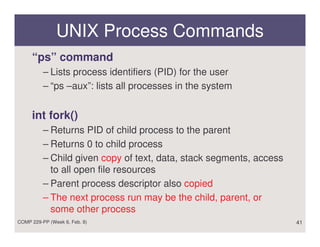
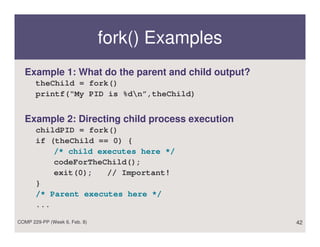
The document discusses the user-level view of operating systems and how they manage resources for program execution through abstractions like files, processes, and threads, allowing for sequential and concurrent computation, with processes providing separate address spaces while threads share resources within a process. Key system calls like fork(), join(), and quit() are used to create and manage processes, while open(), read(), write(), and close() manipulate file resources.
![Changing Program Data Dynamically:
execve()
int execve(char *path,char *argv[],char *envp[]);
program arguments environment
variables
Effect of execve()
– Replaces text, data, and stack areas using the program
loader
– After loading, stack is cleared, variables initialized
– Program is started (call does not return)
System Calls to Wait for Child Process to Stop:
wait(): block until any child process terminates
waitpid(P): block until child process with PID P terminates
43](https://image.slidesharecdn.com/userlevelviewofos-120927060652-phpapp02/85/User-level-view-of-os-43-320.jpg)