1. The document provides an overview of the history and development of UNIX/Linux operating systems. It originated from projects in the 1960s and was further developed by Ken Thompson, Dennis Ritchie and others.
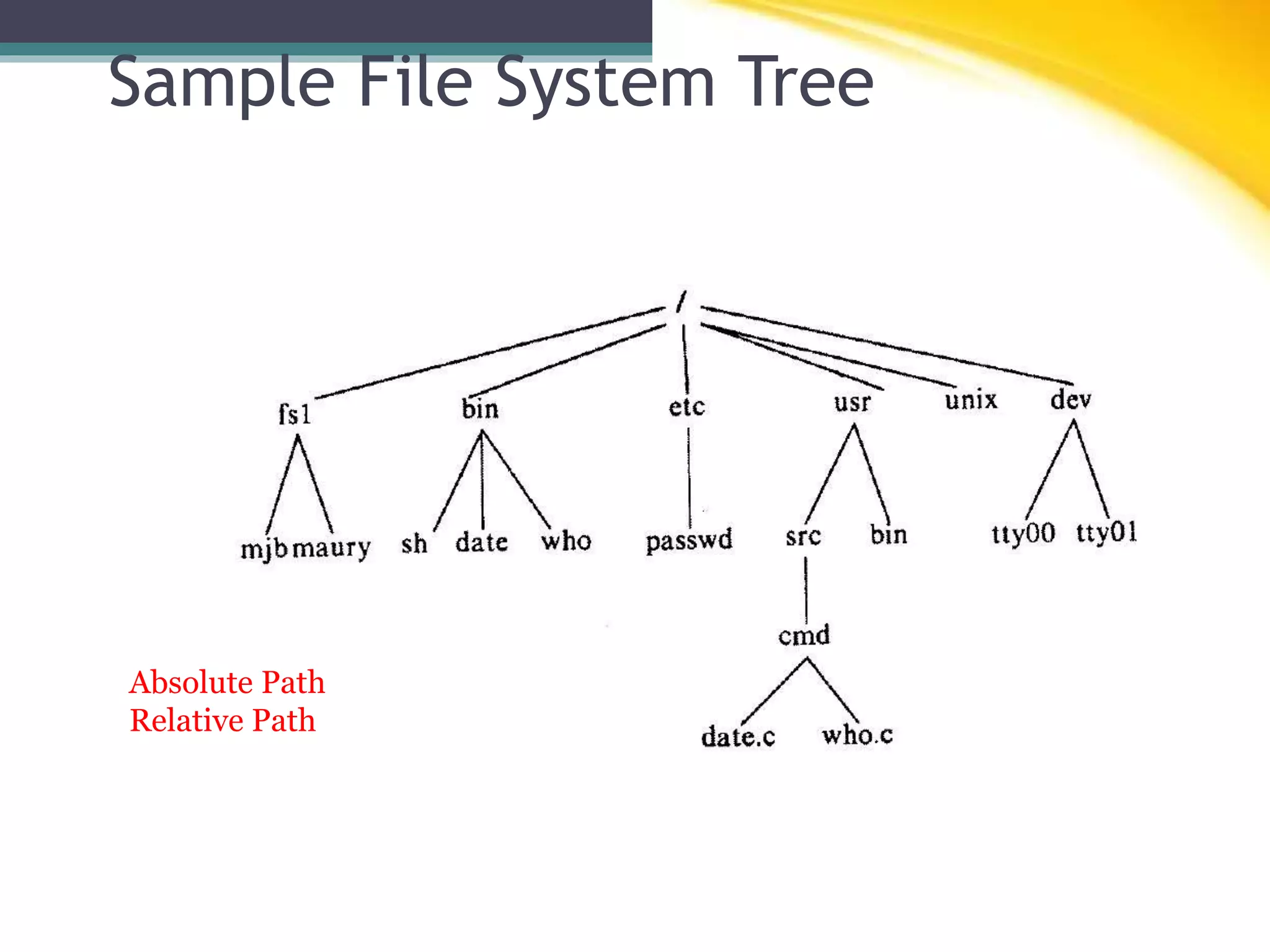
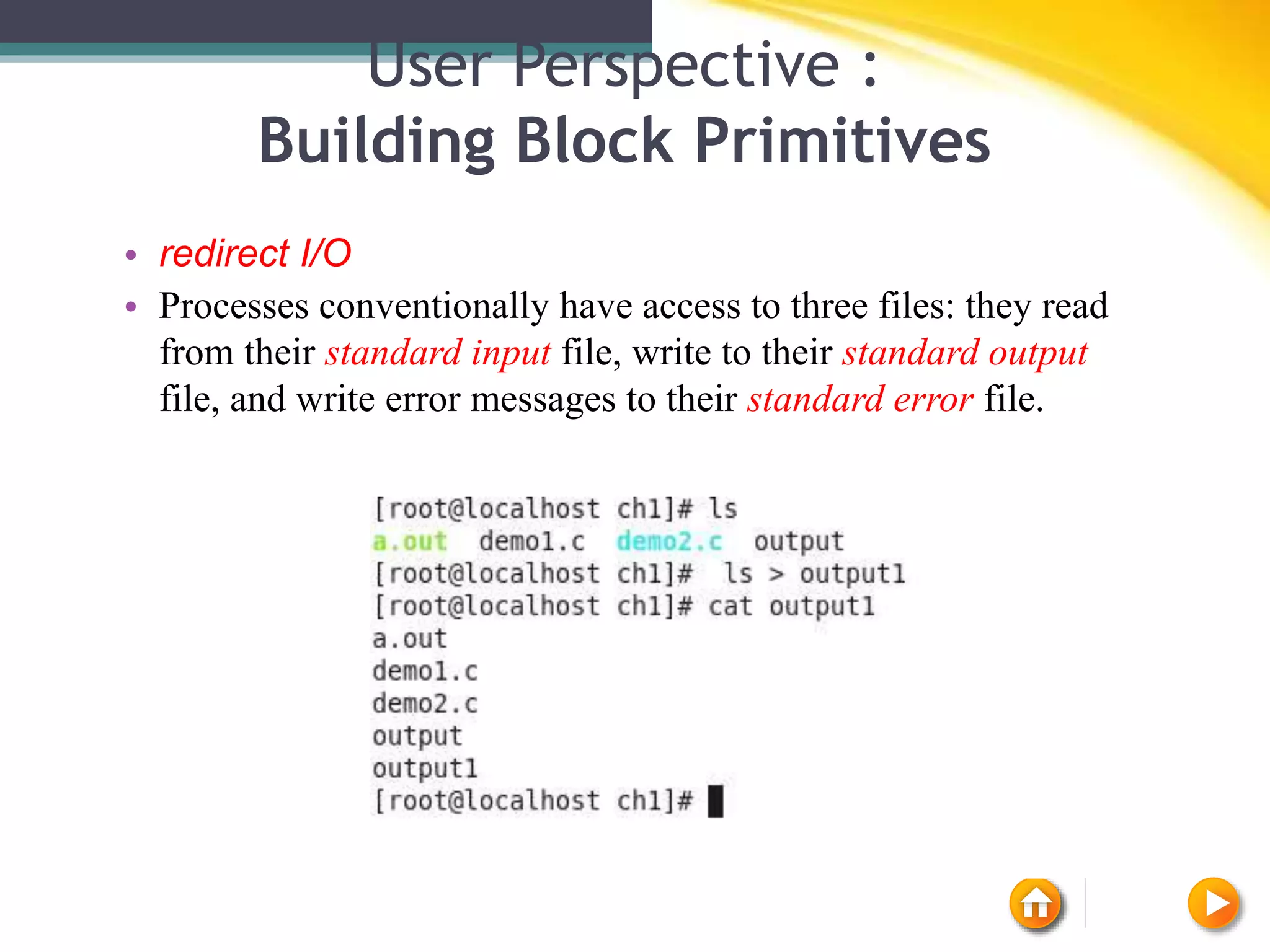
2. UNIX became popular due to its modular design, use of a hierarchical file system, treating all system resources as files, and ability to combine simple programs together.
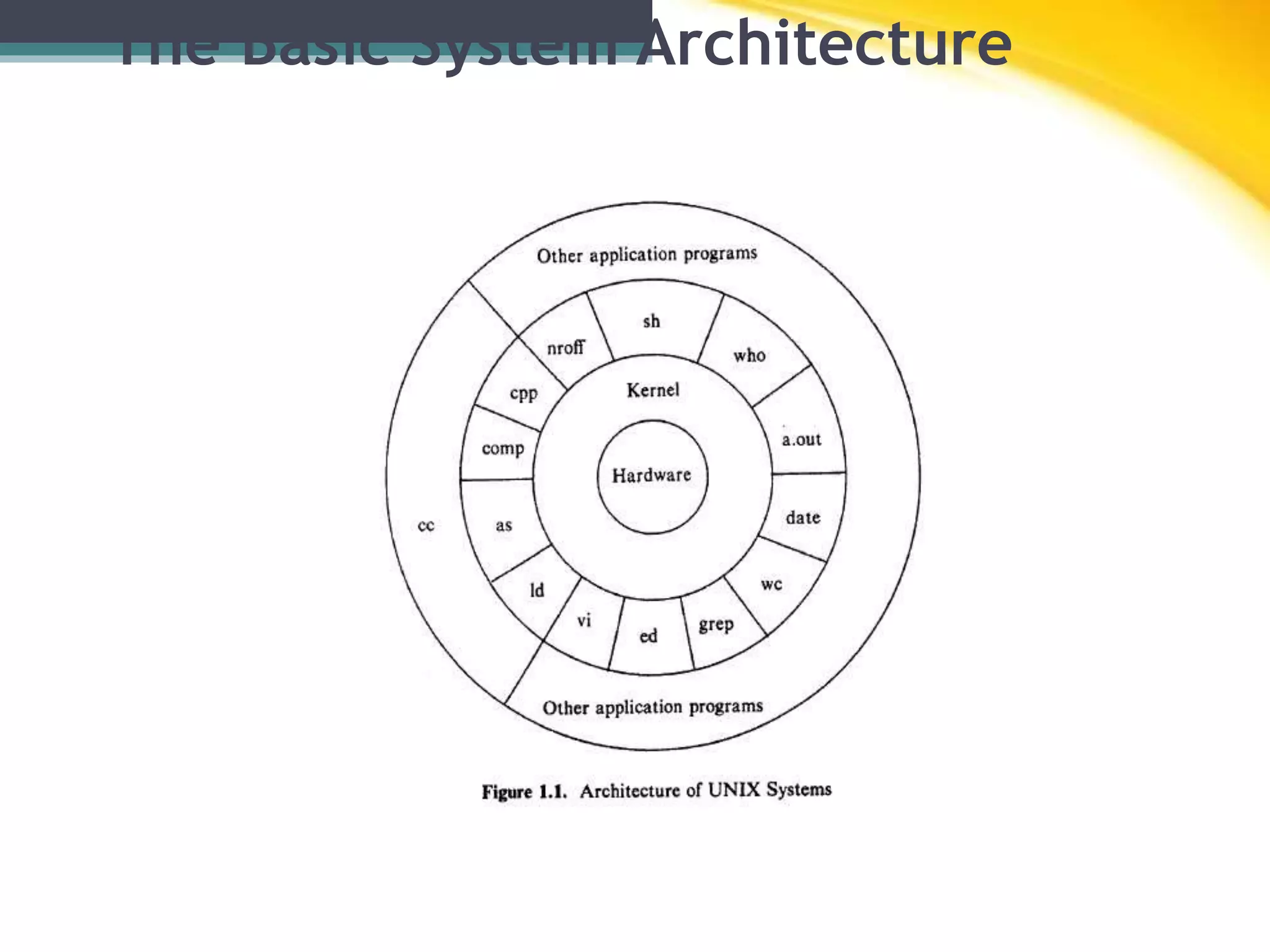
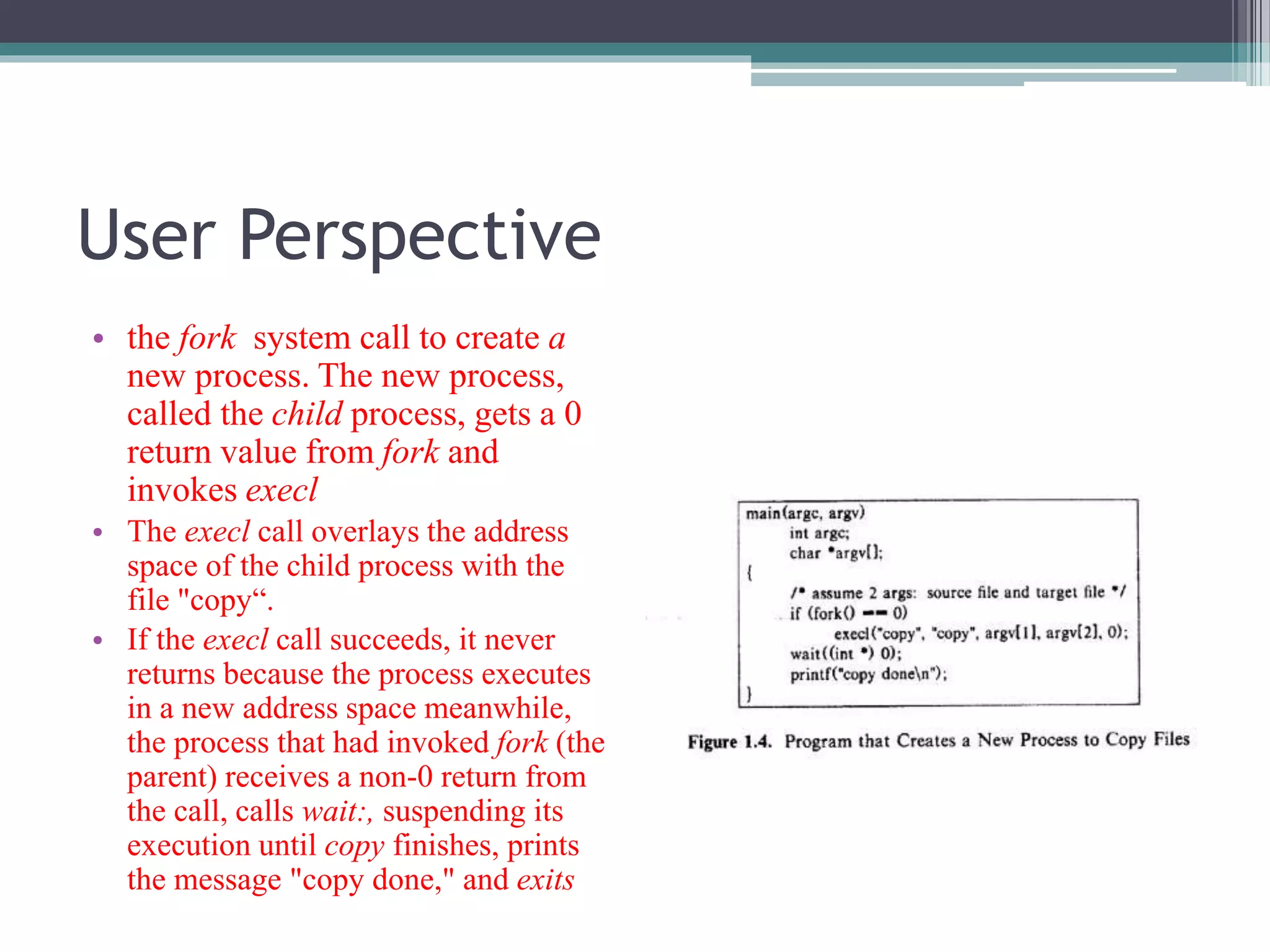
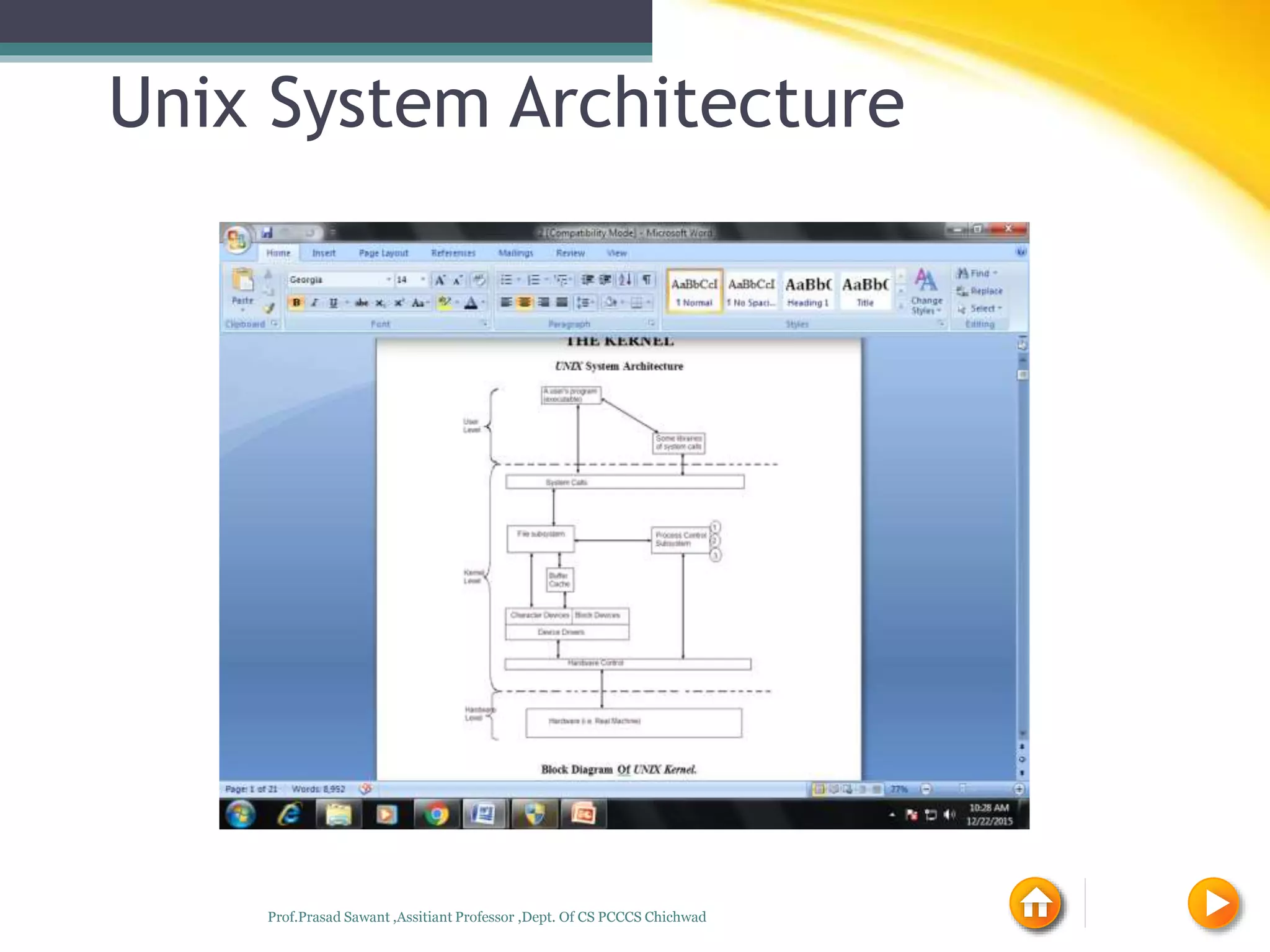
3. The basic architecture of UNIX involves application programs interacting with the kernel via system calls to perform tasks like process and memory management.