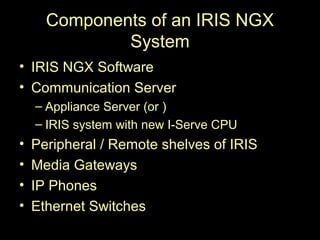
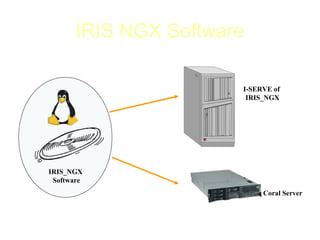
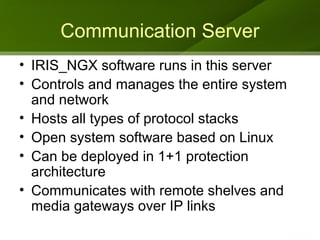
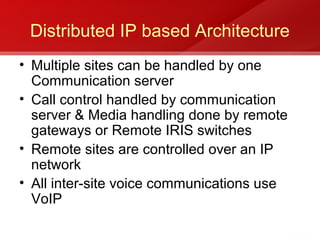
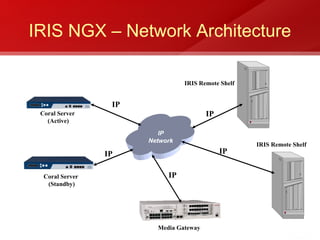
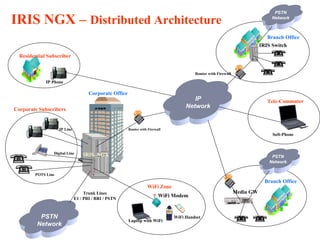
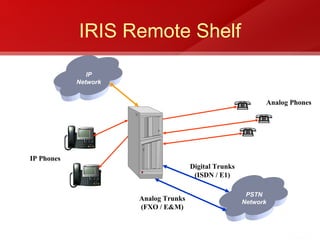
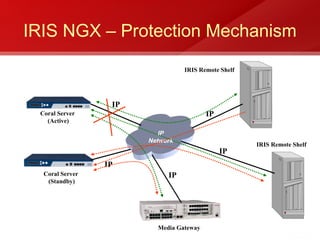
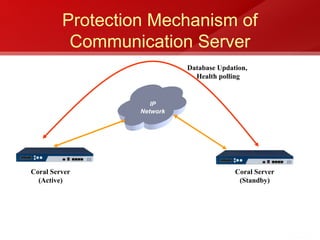
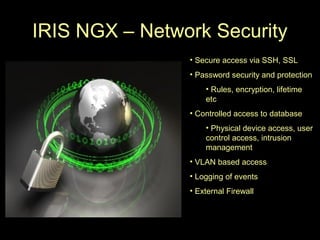
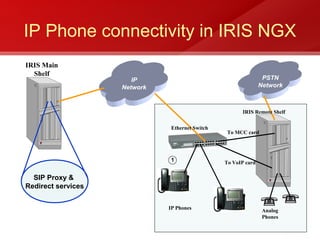
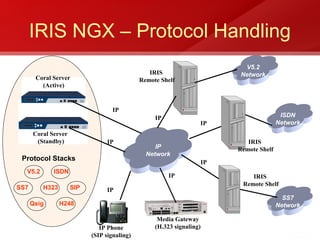
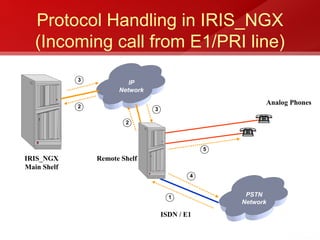
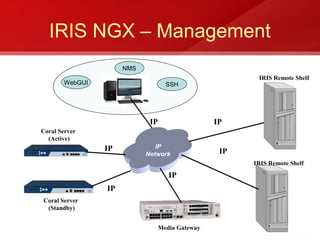
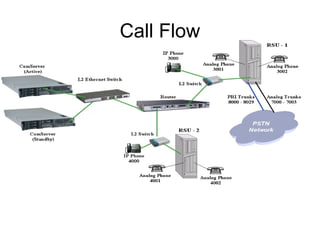
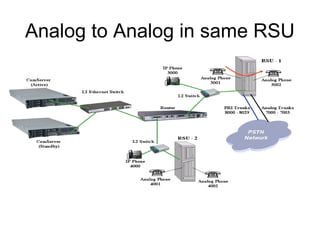
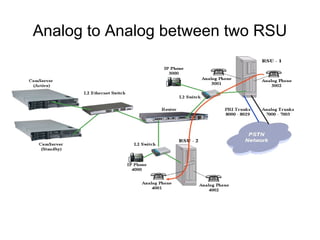
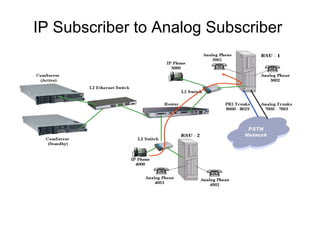
IRIS NGX is a next generation IP-based switching platform that supports both soft and hardware-based switching. It provides a flexible, distributed architecture for integrating IP networks and supports various interfaces and protocols. The system includes IRIS NGX software, communication servers, peripheral shelves, media gateways, and IP phones. It offers advantages like seamless IP network integration, efficient network capacity expansion, and high reliability.