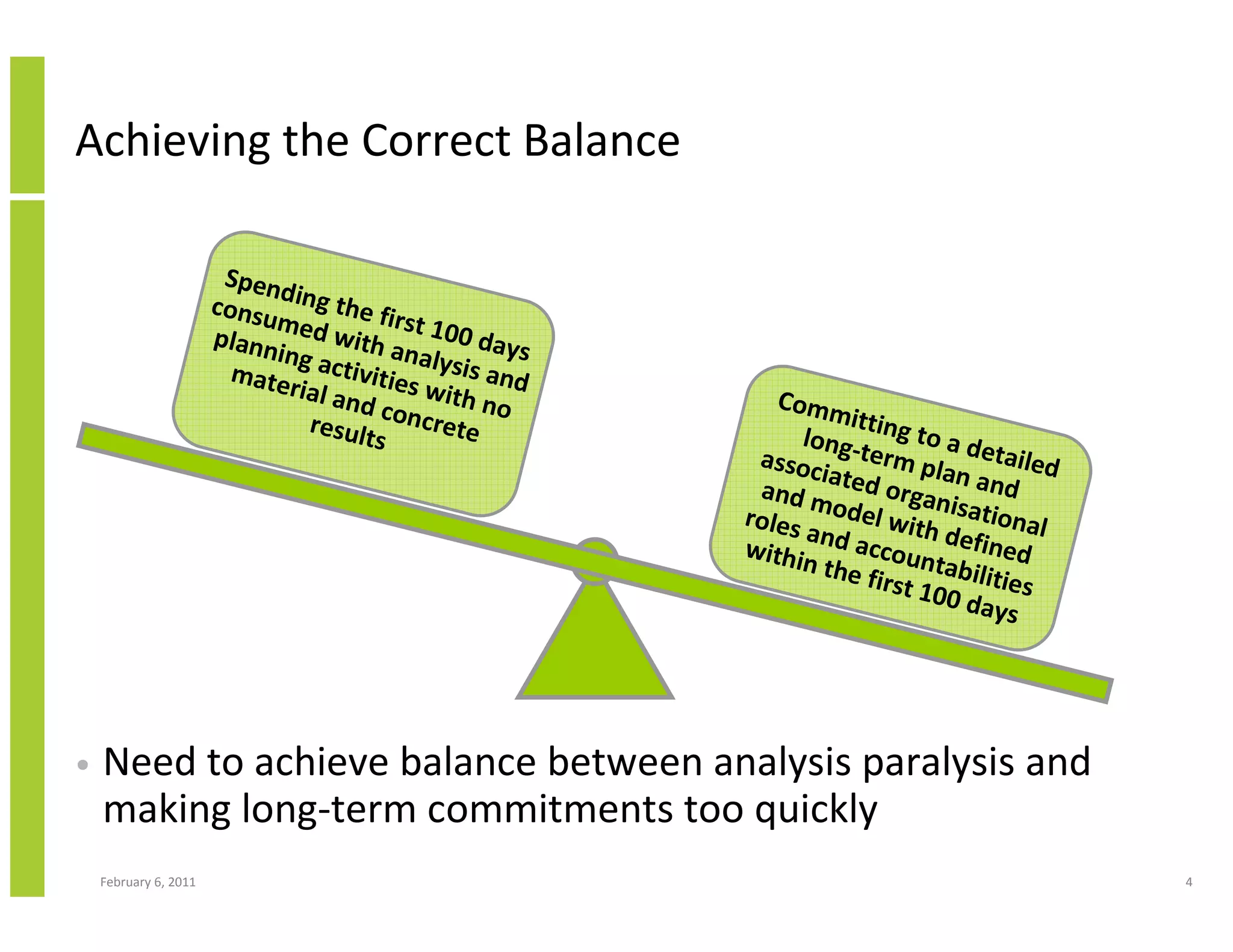
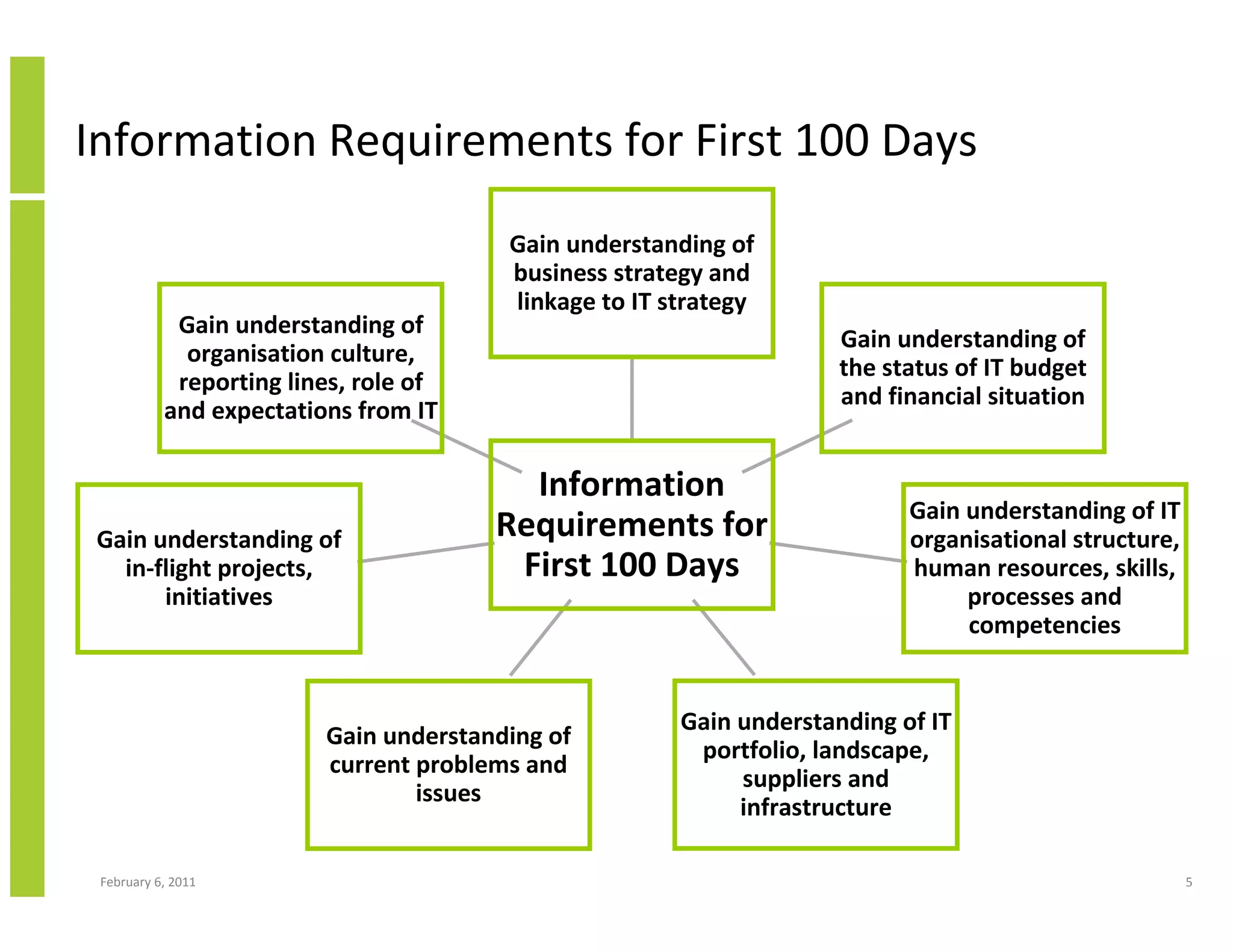
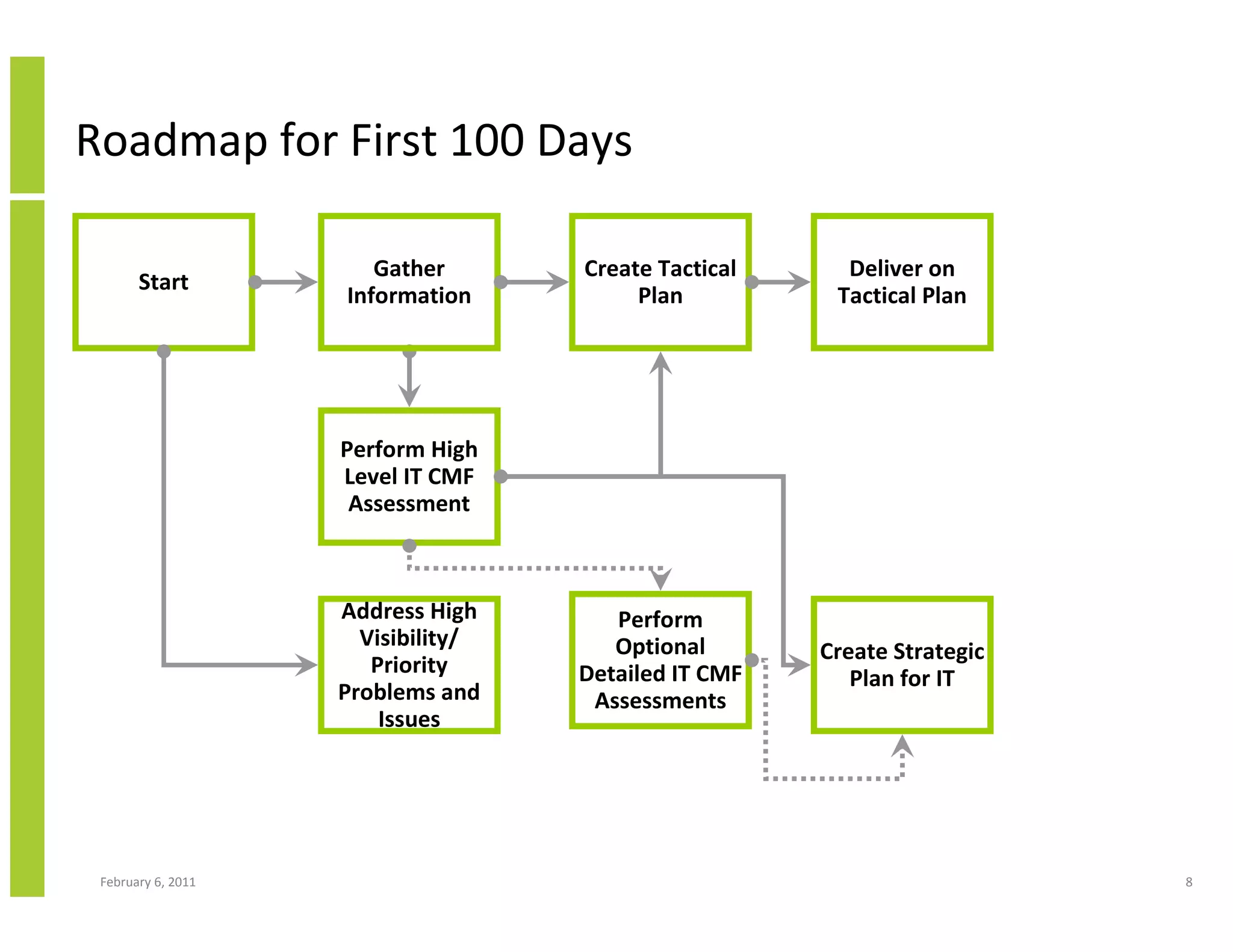
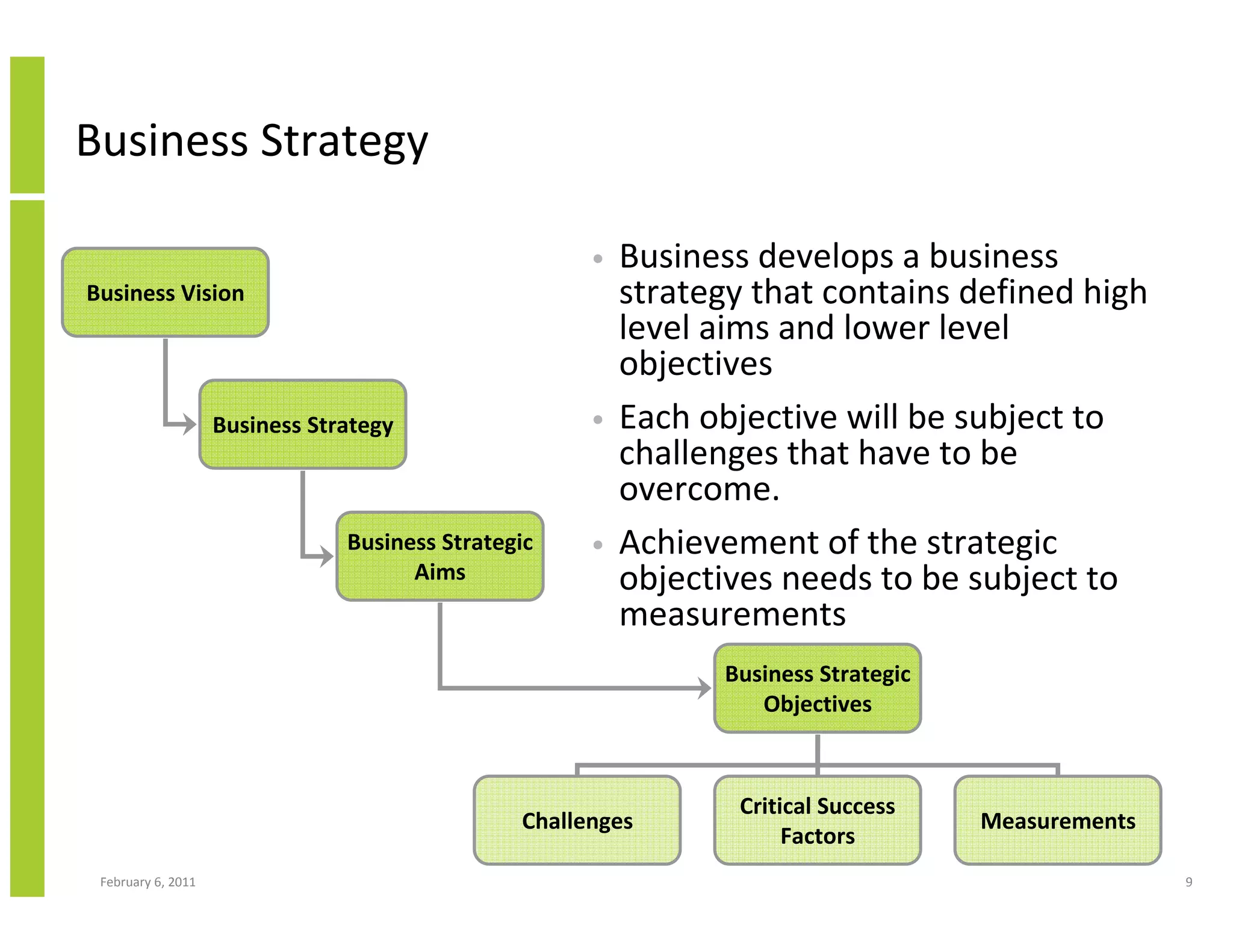
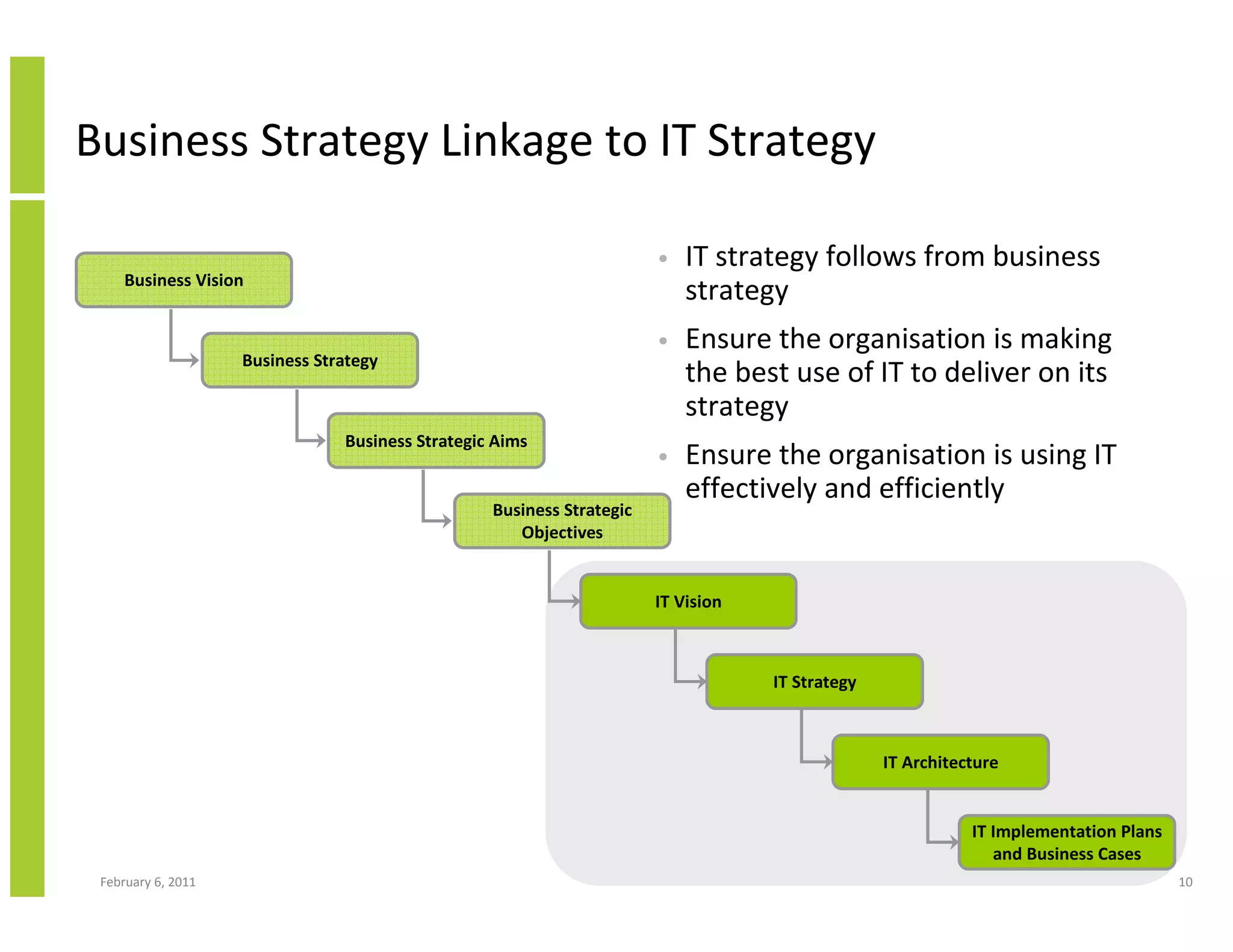
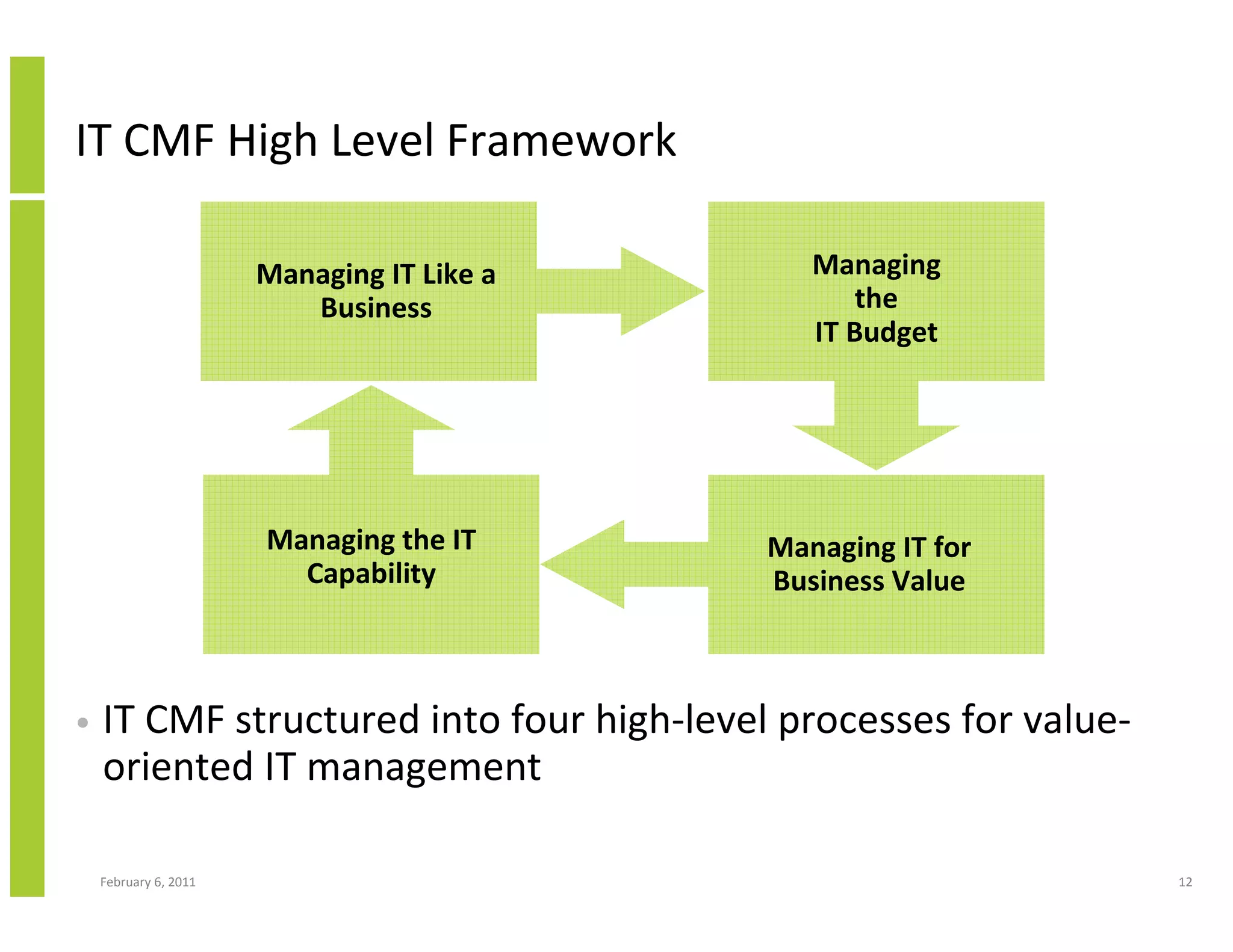
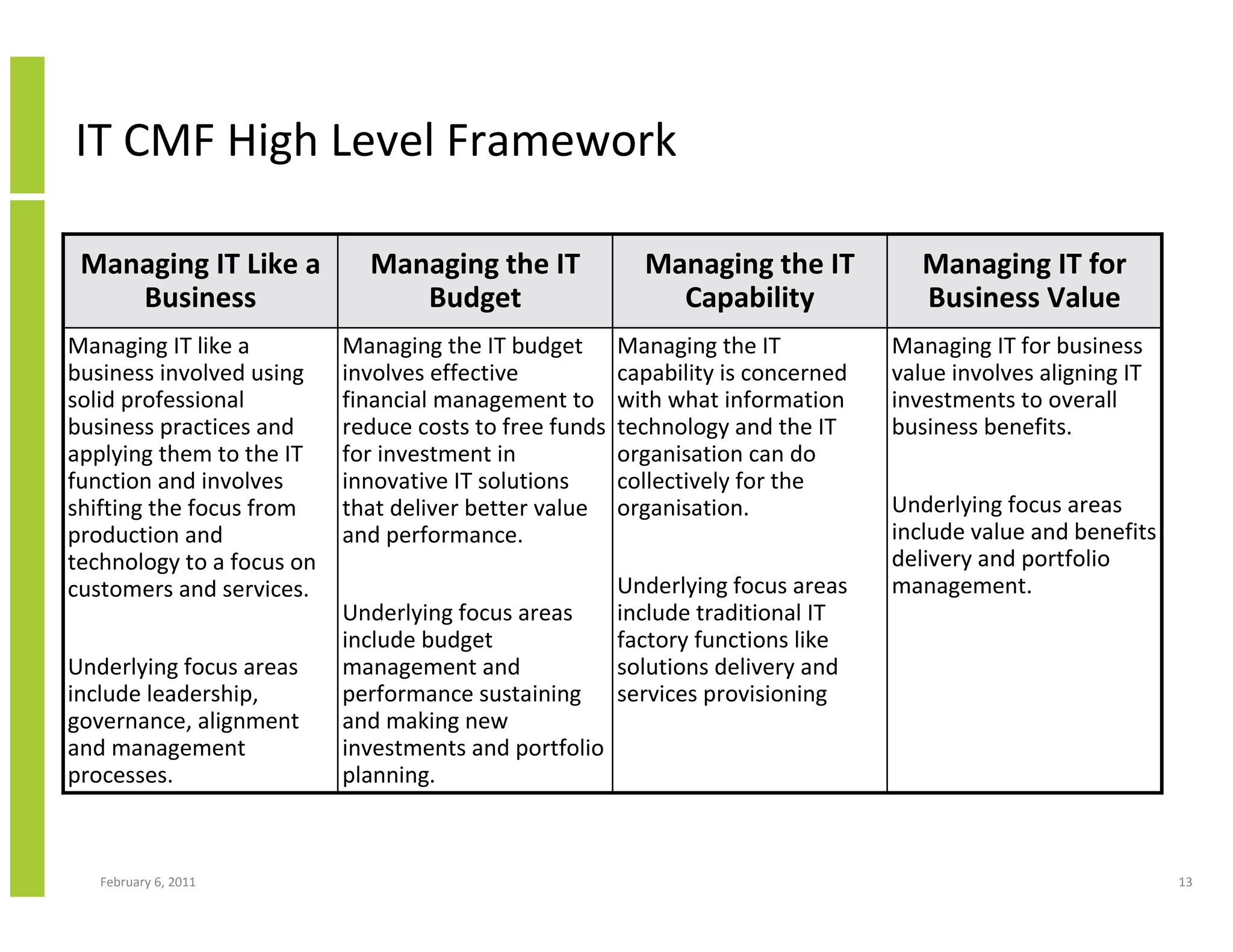
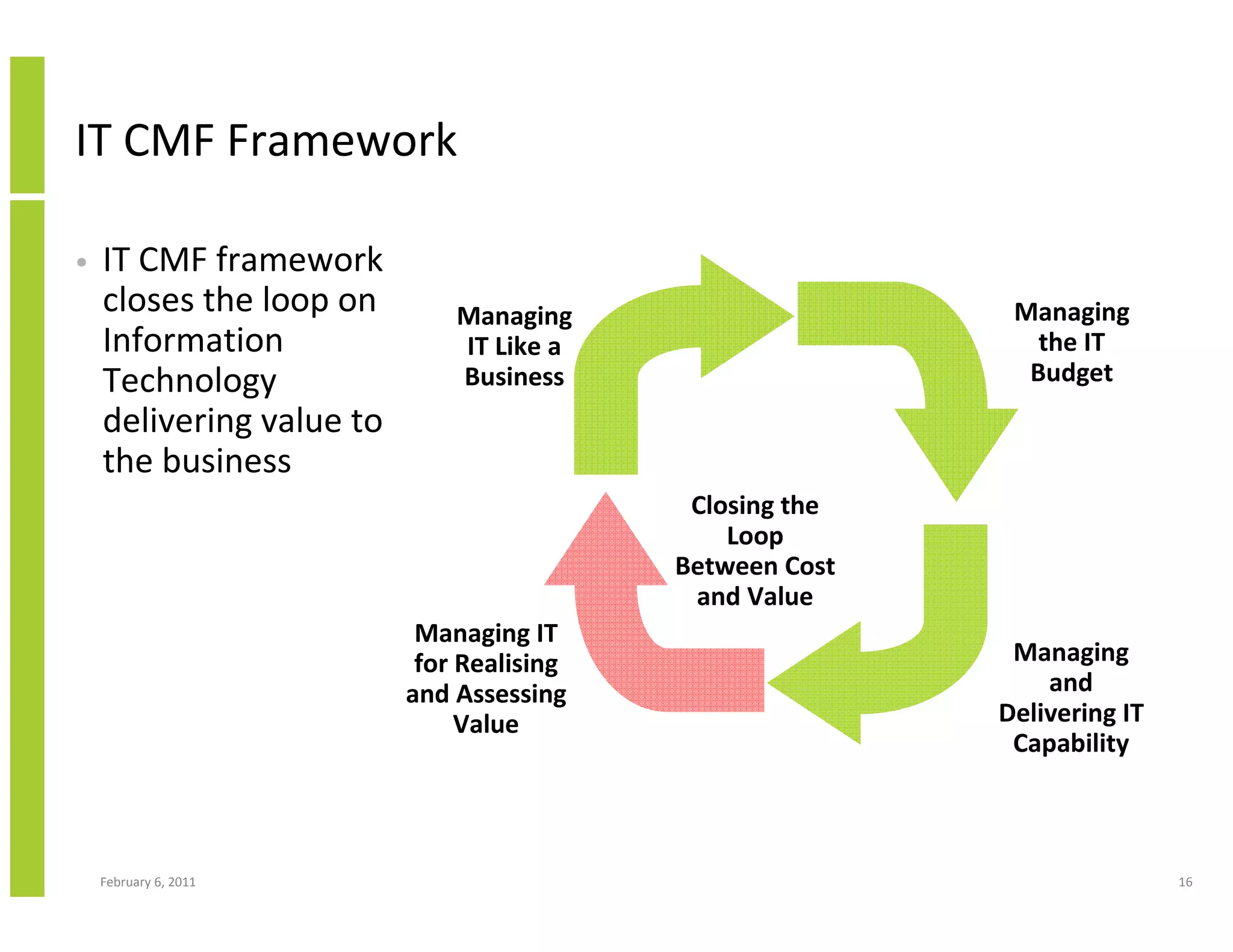
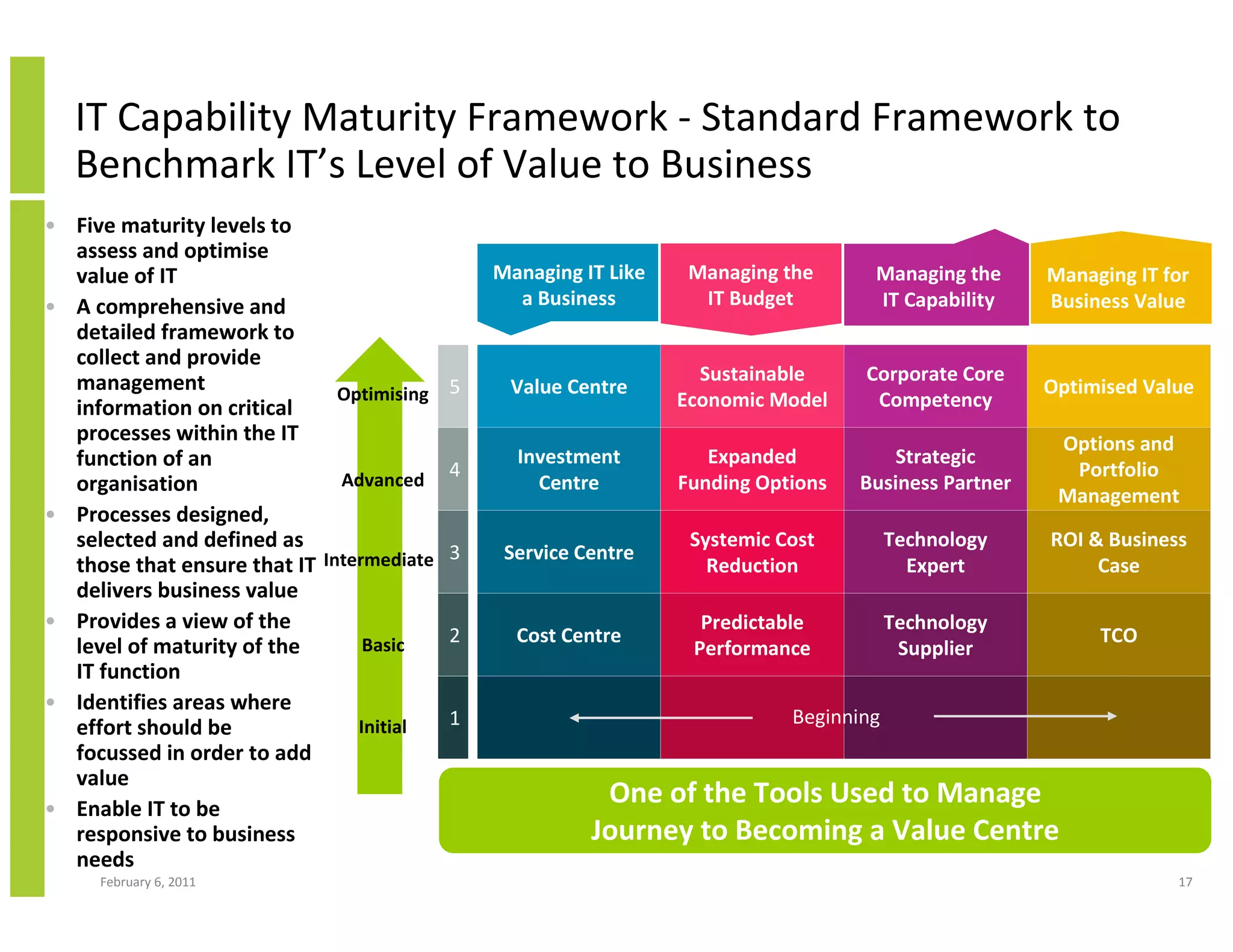
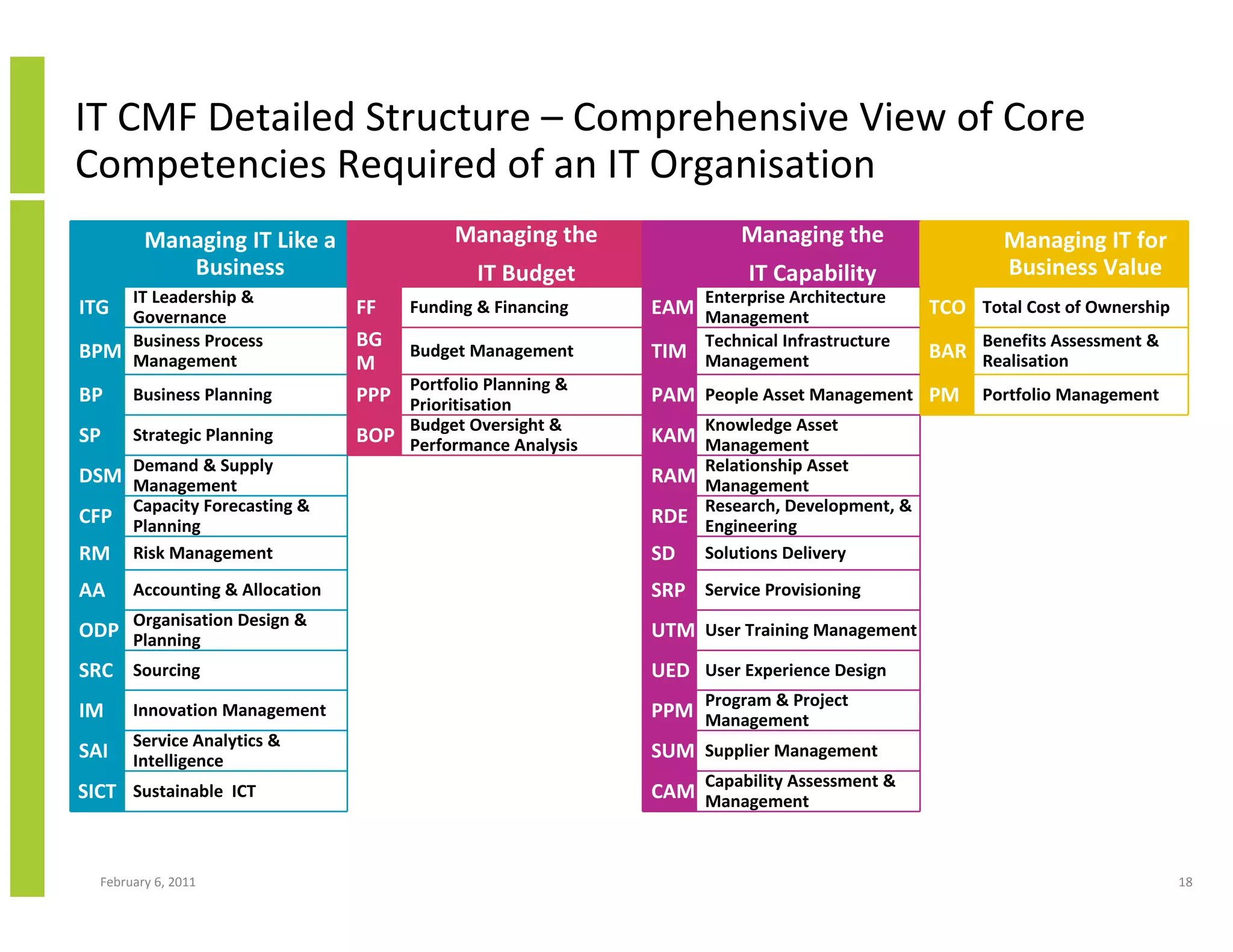
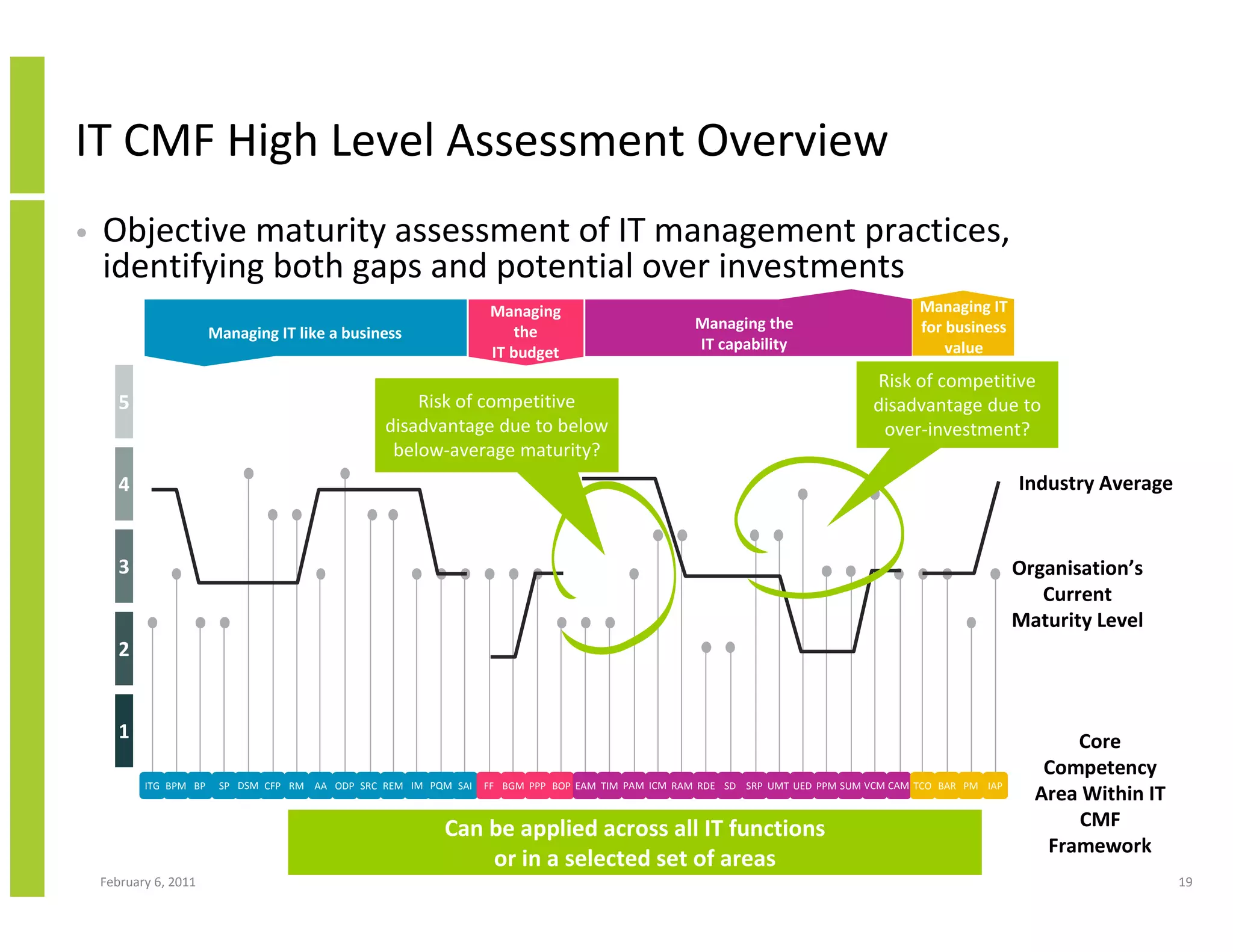
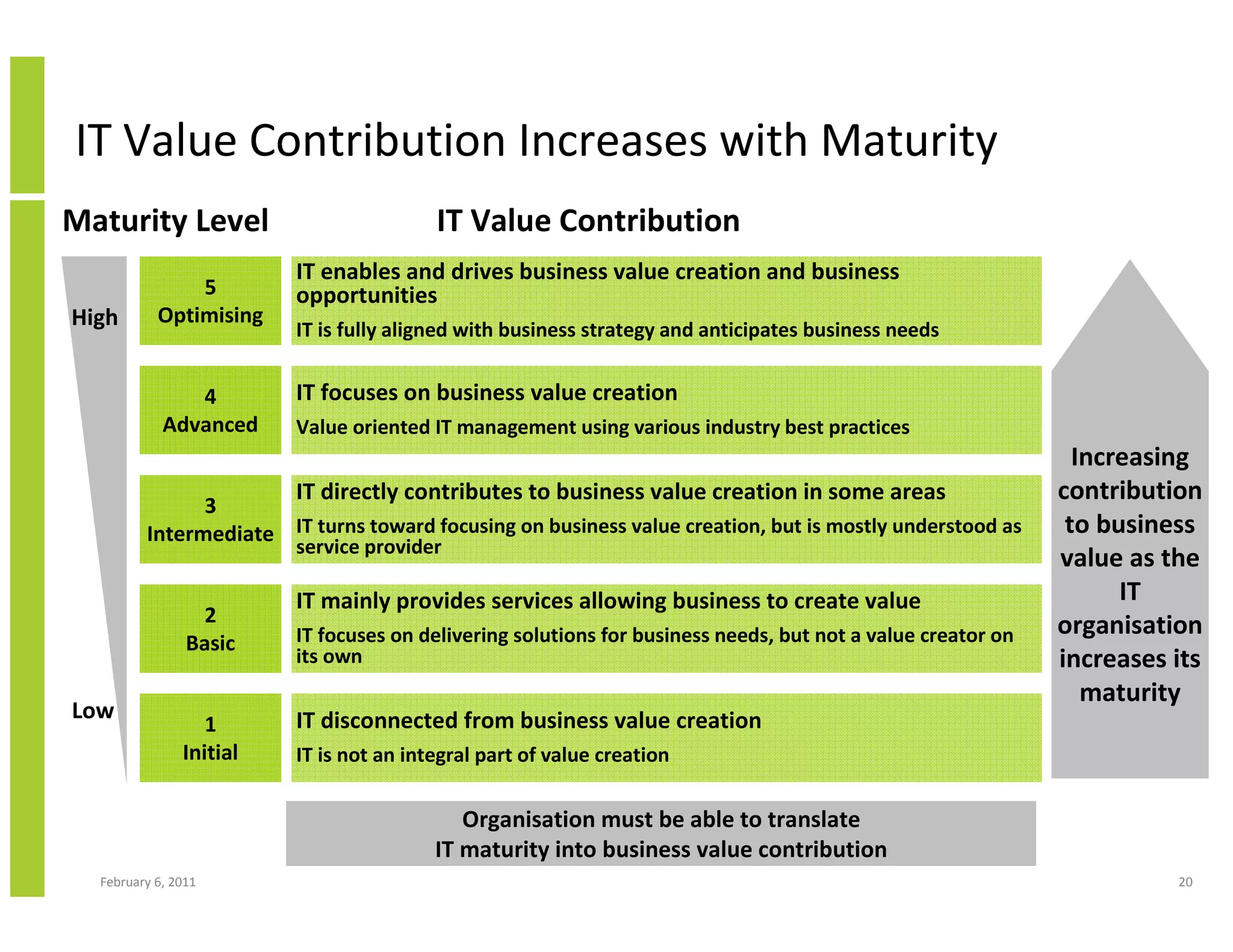
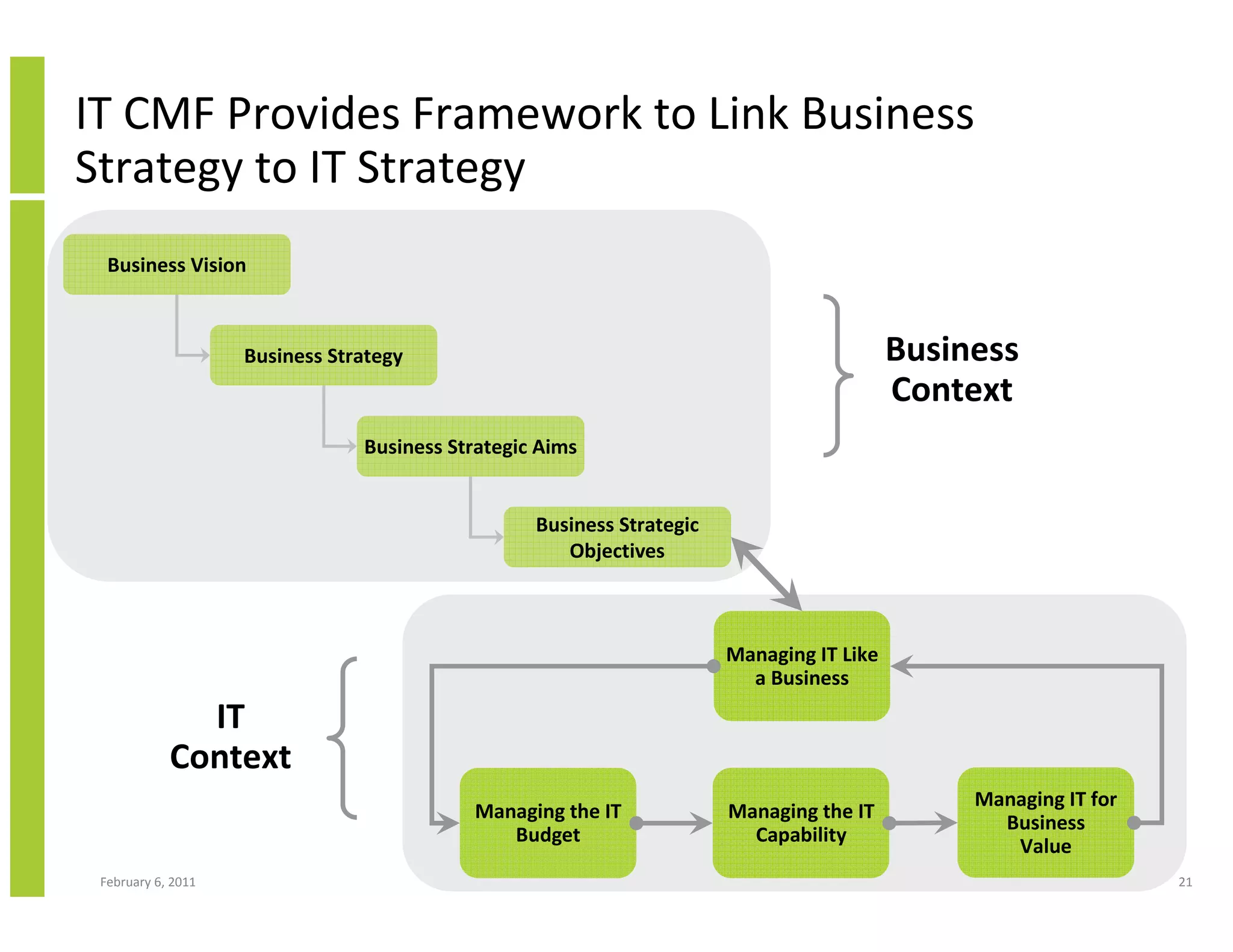
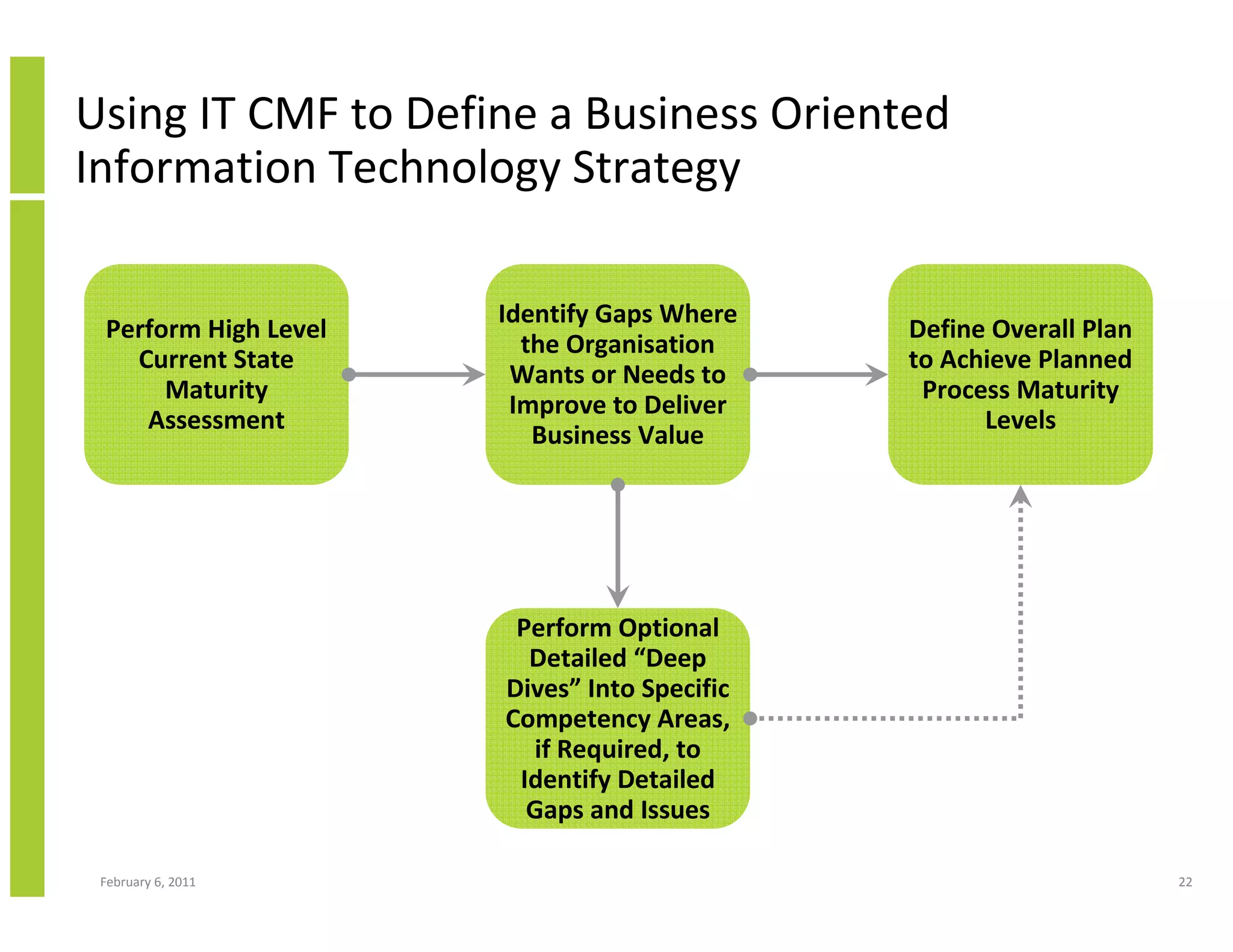
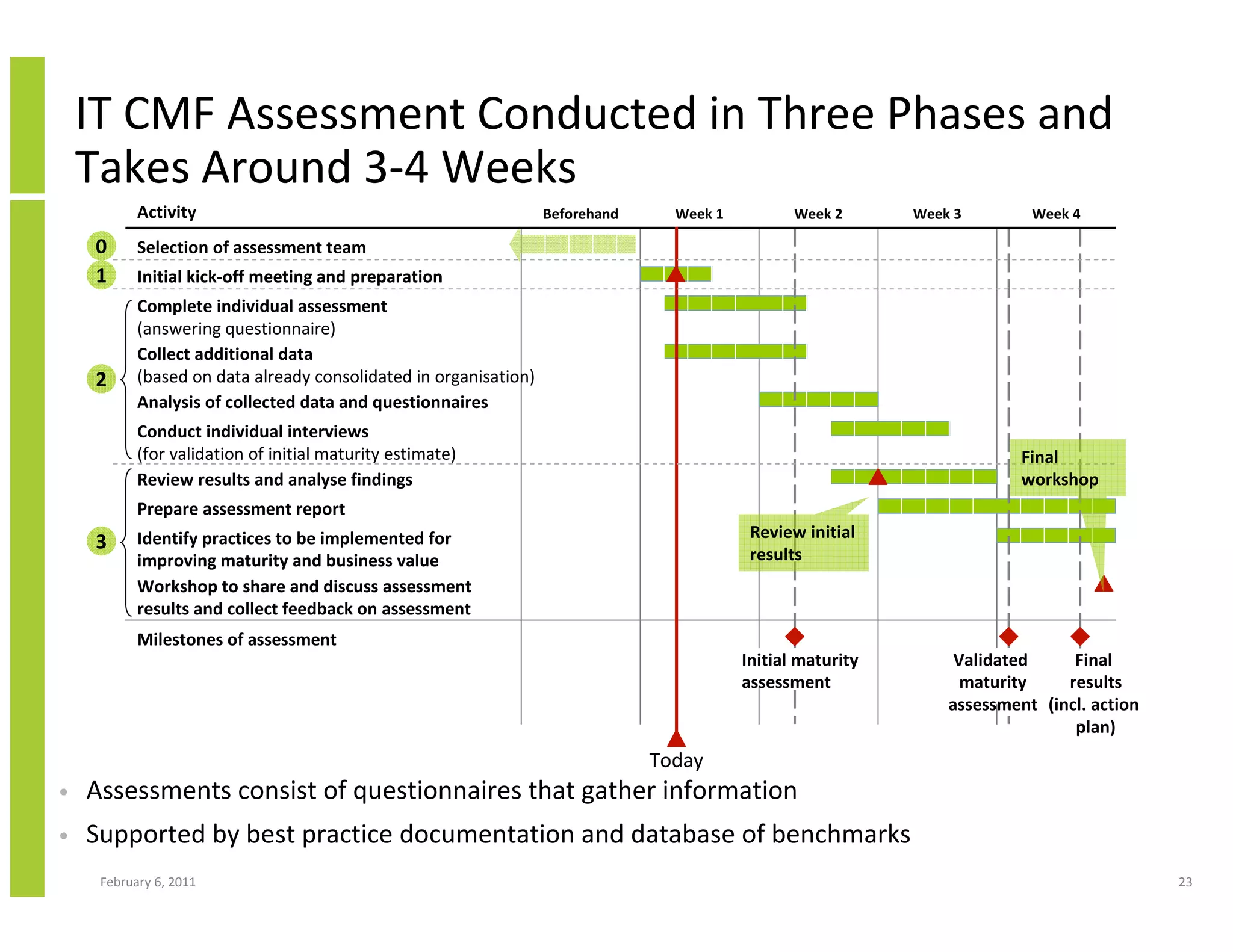
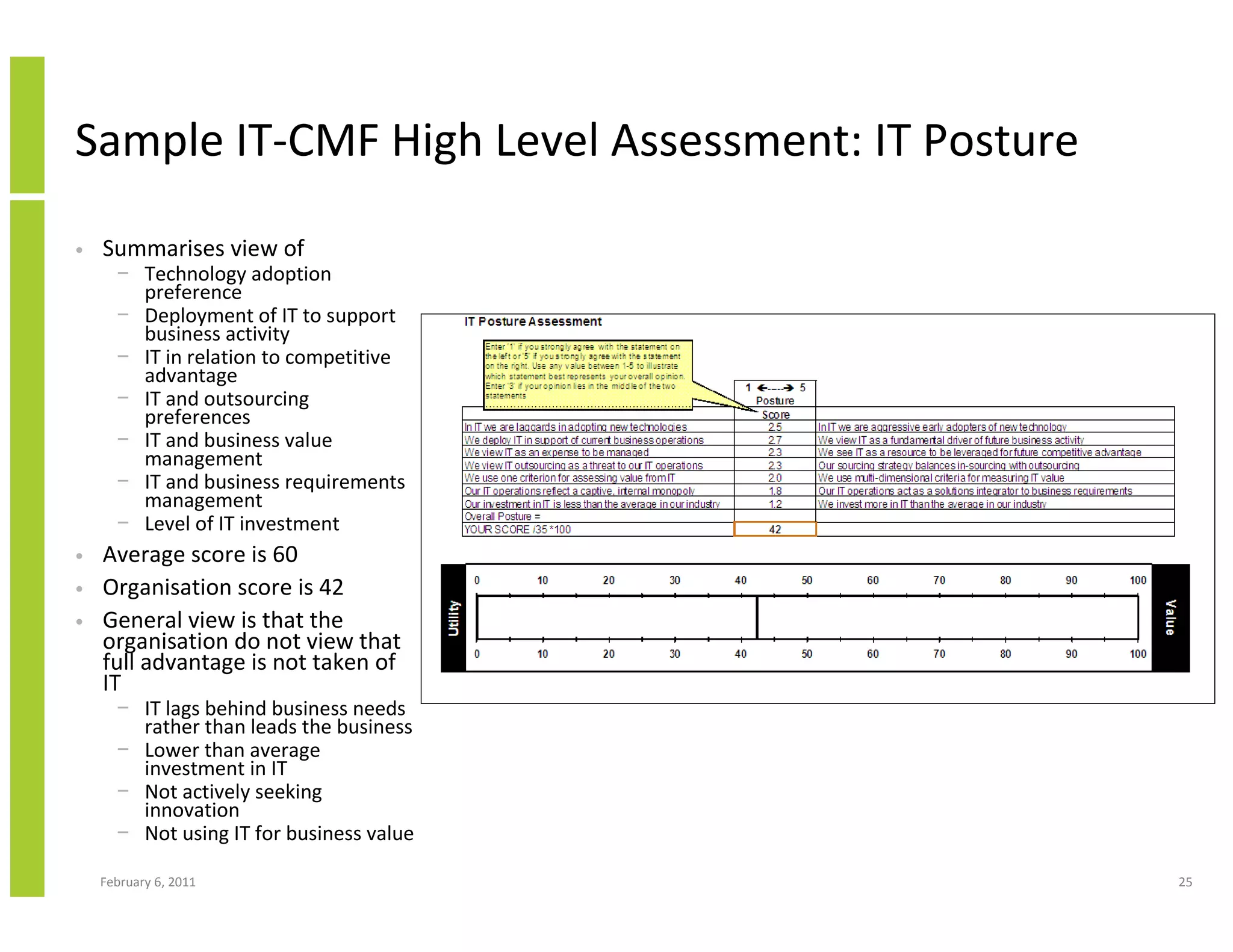
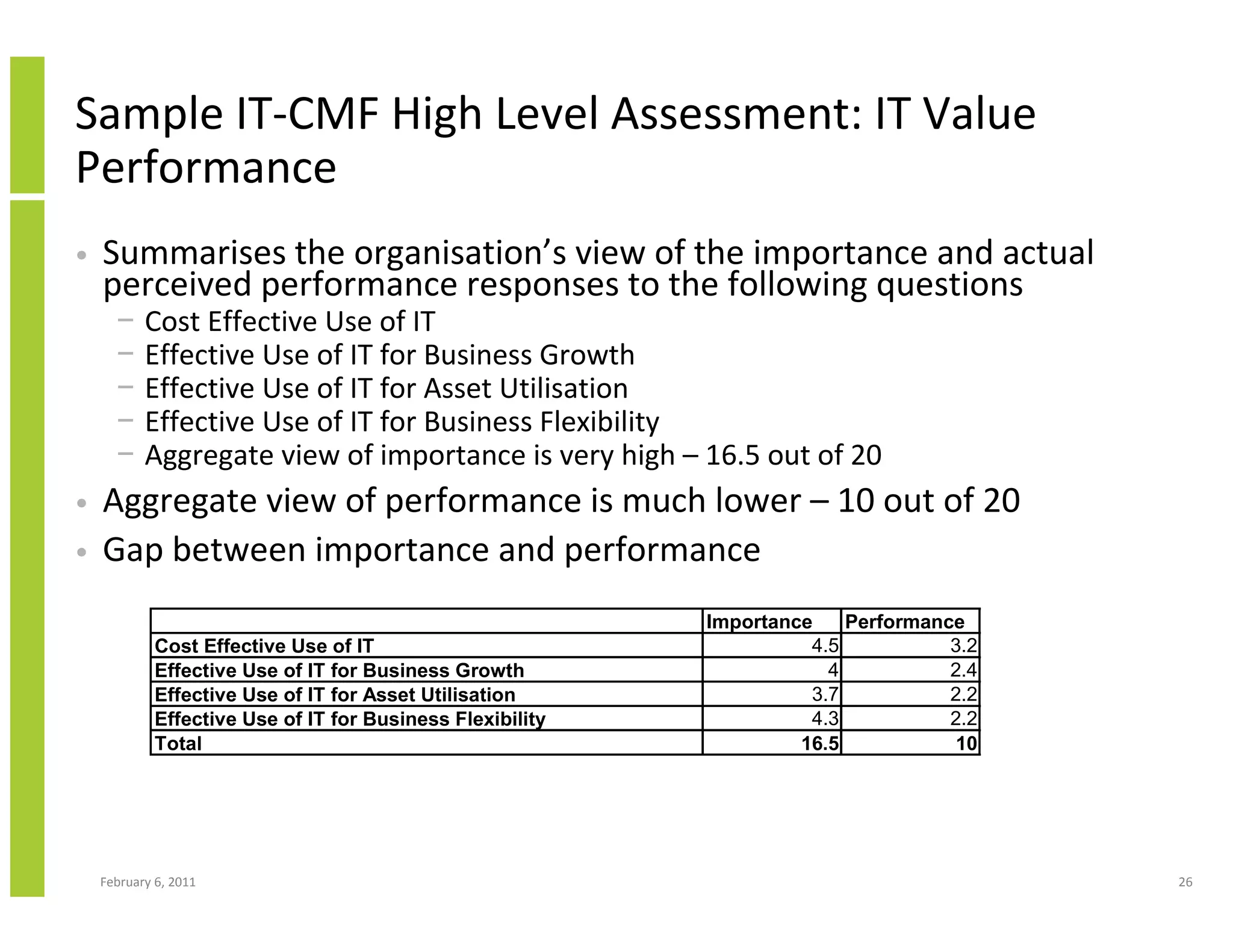
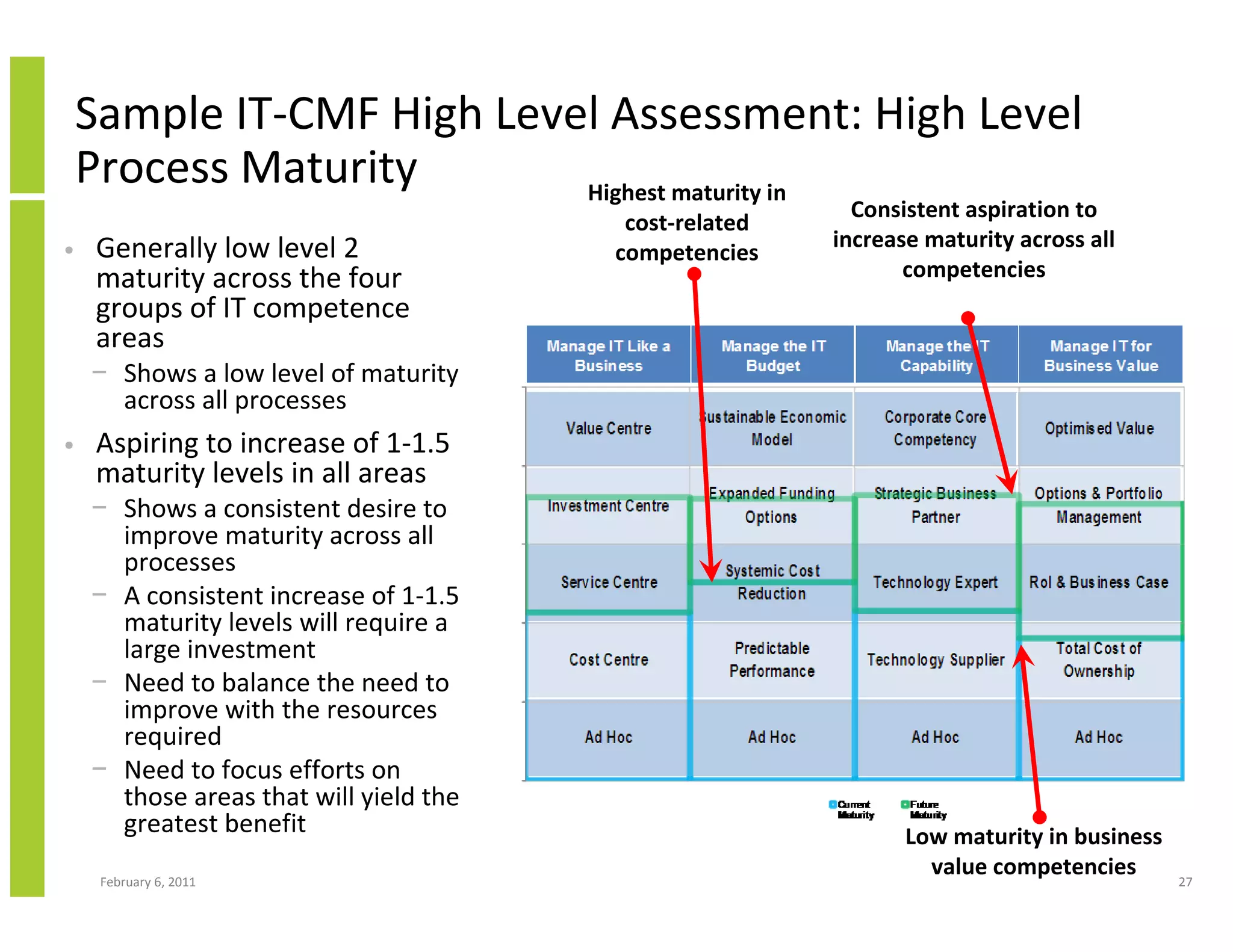
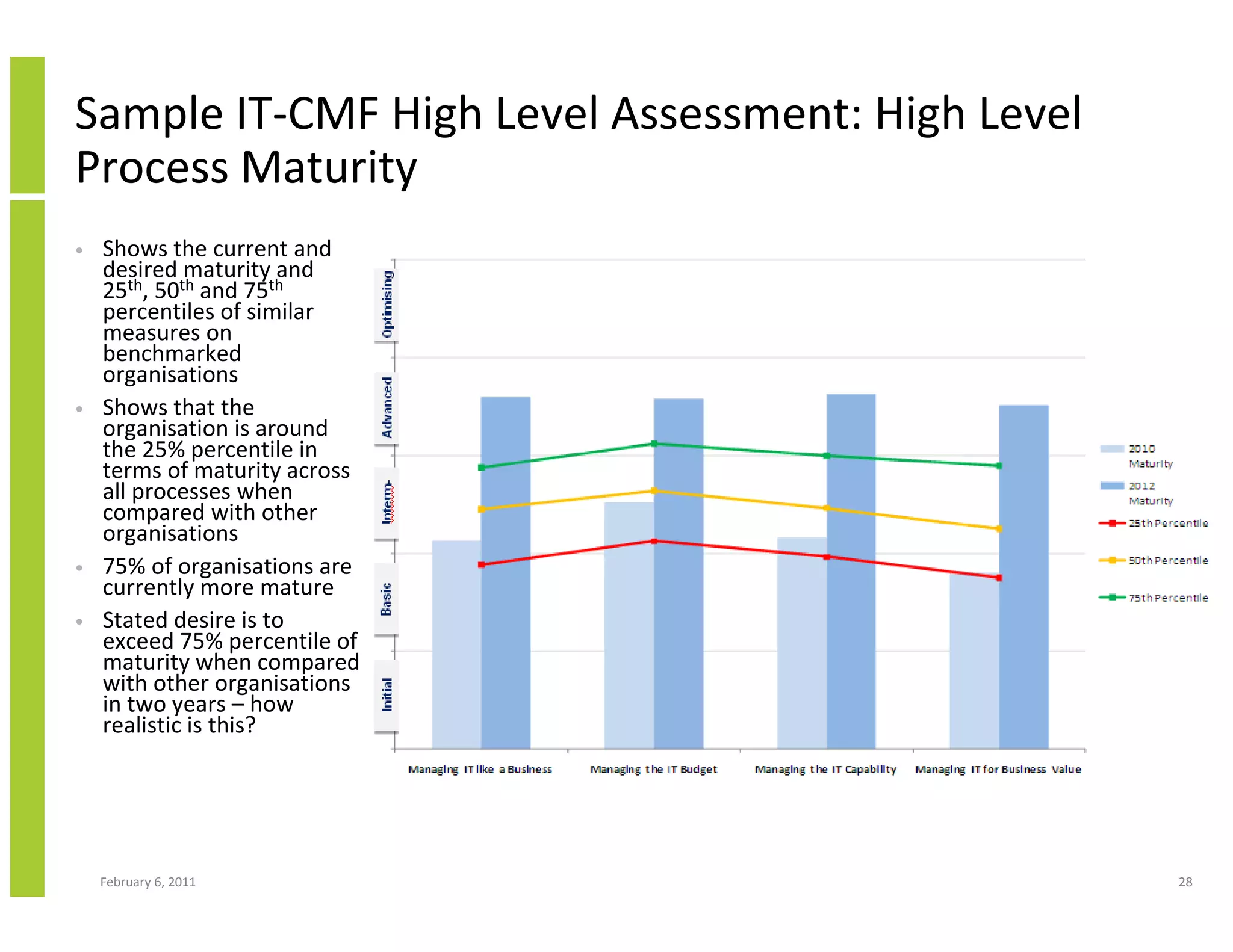
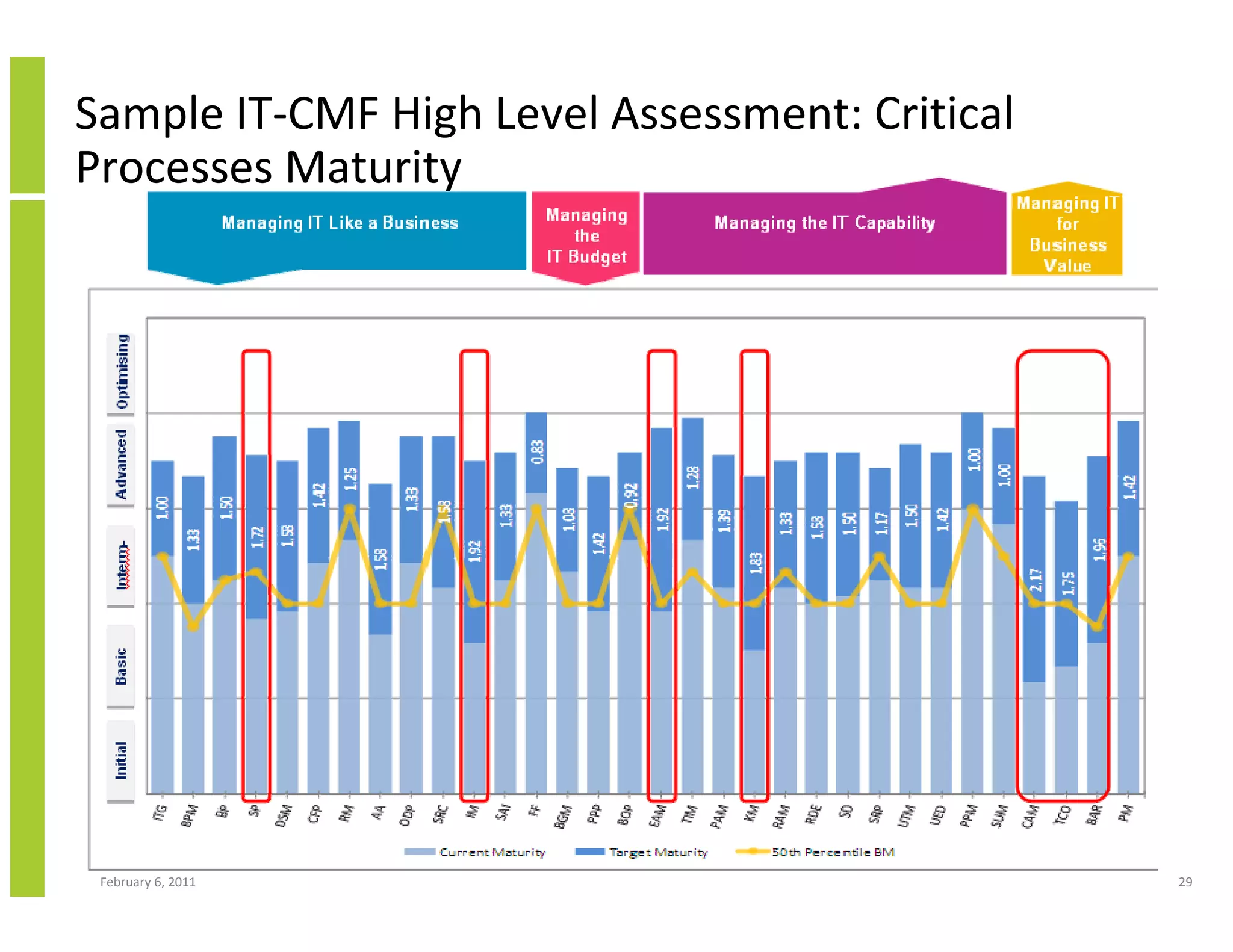
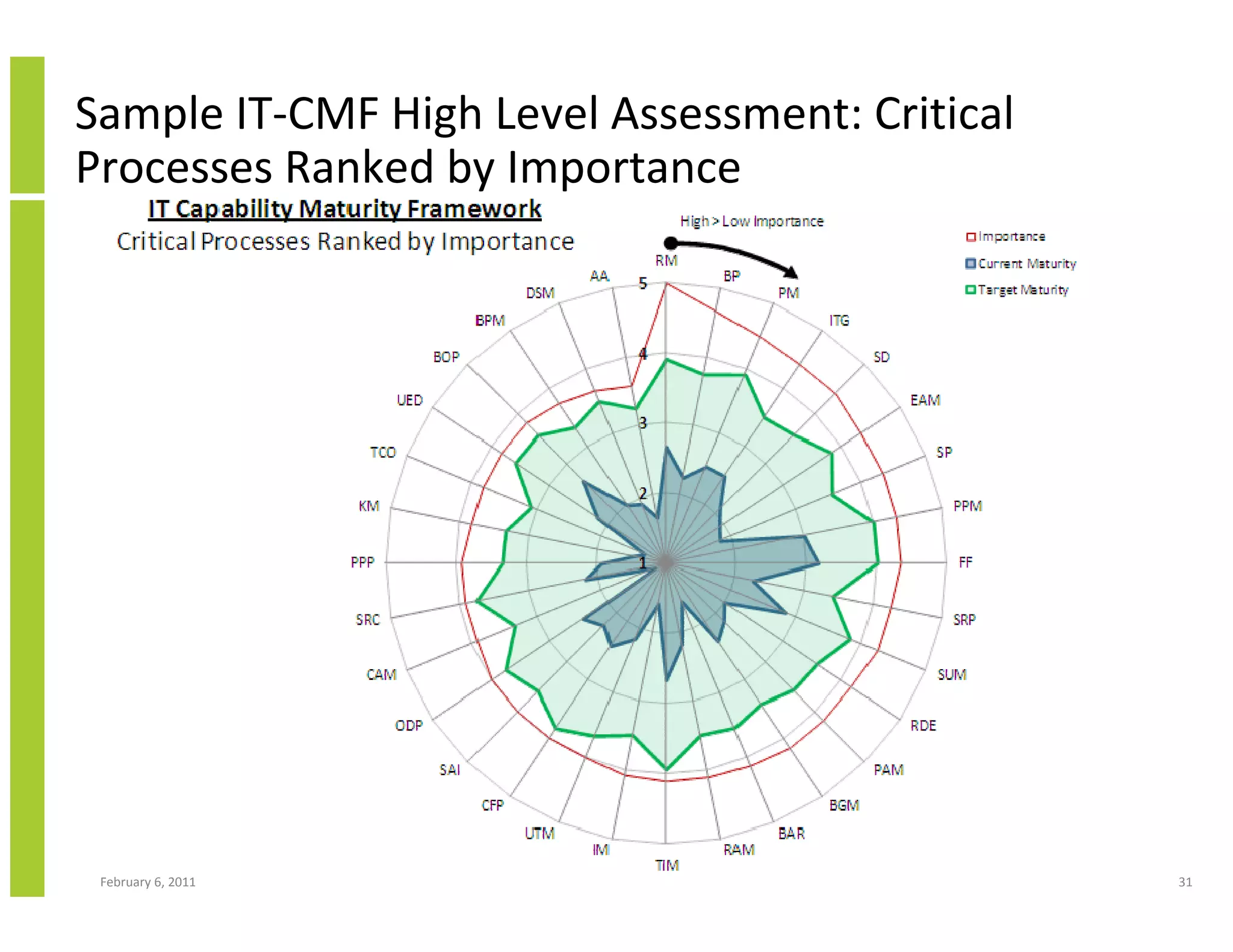
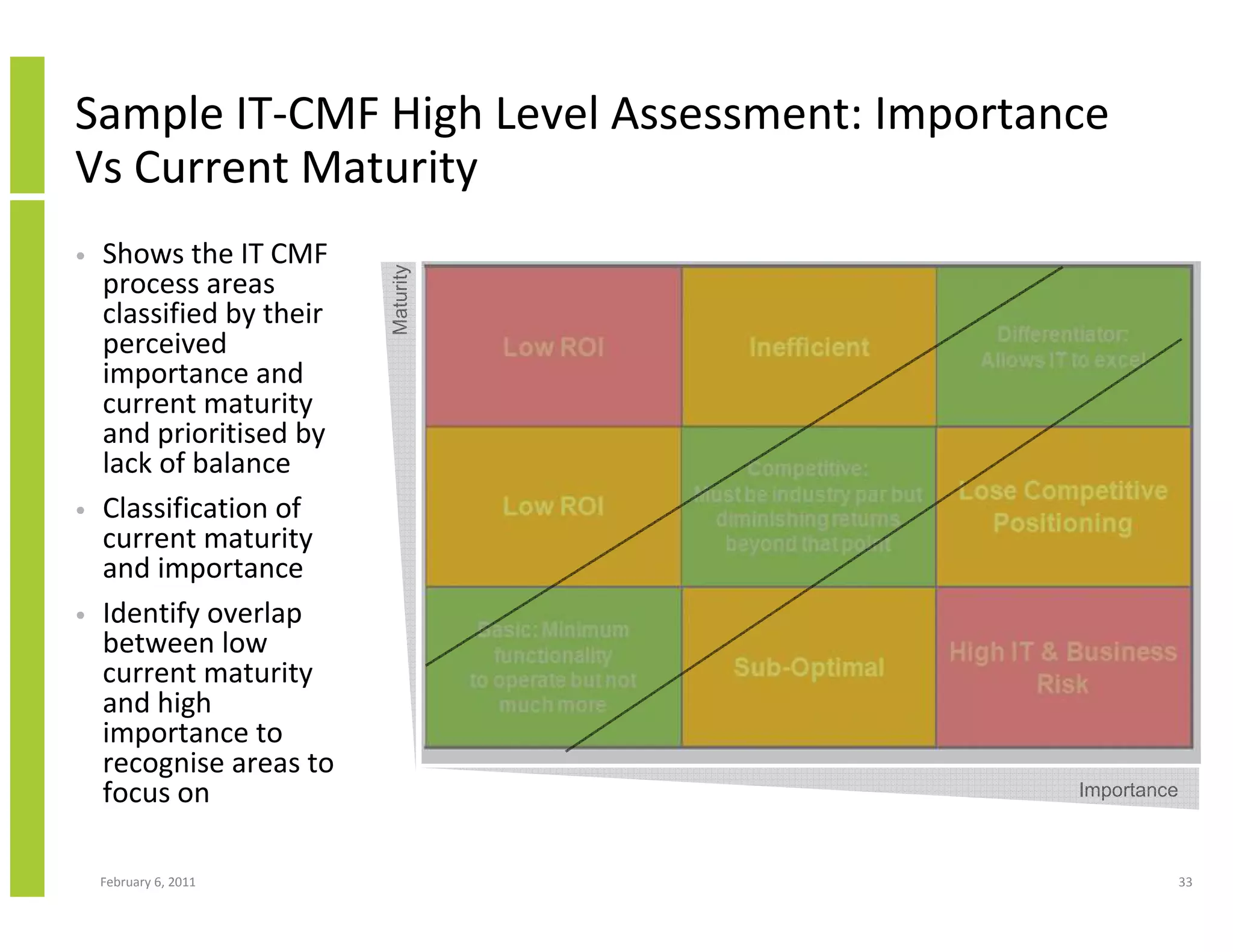
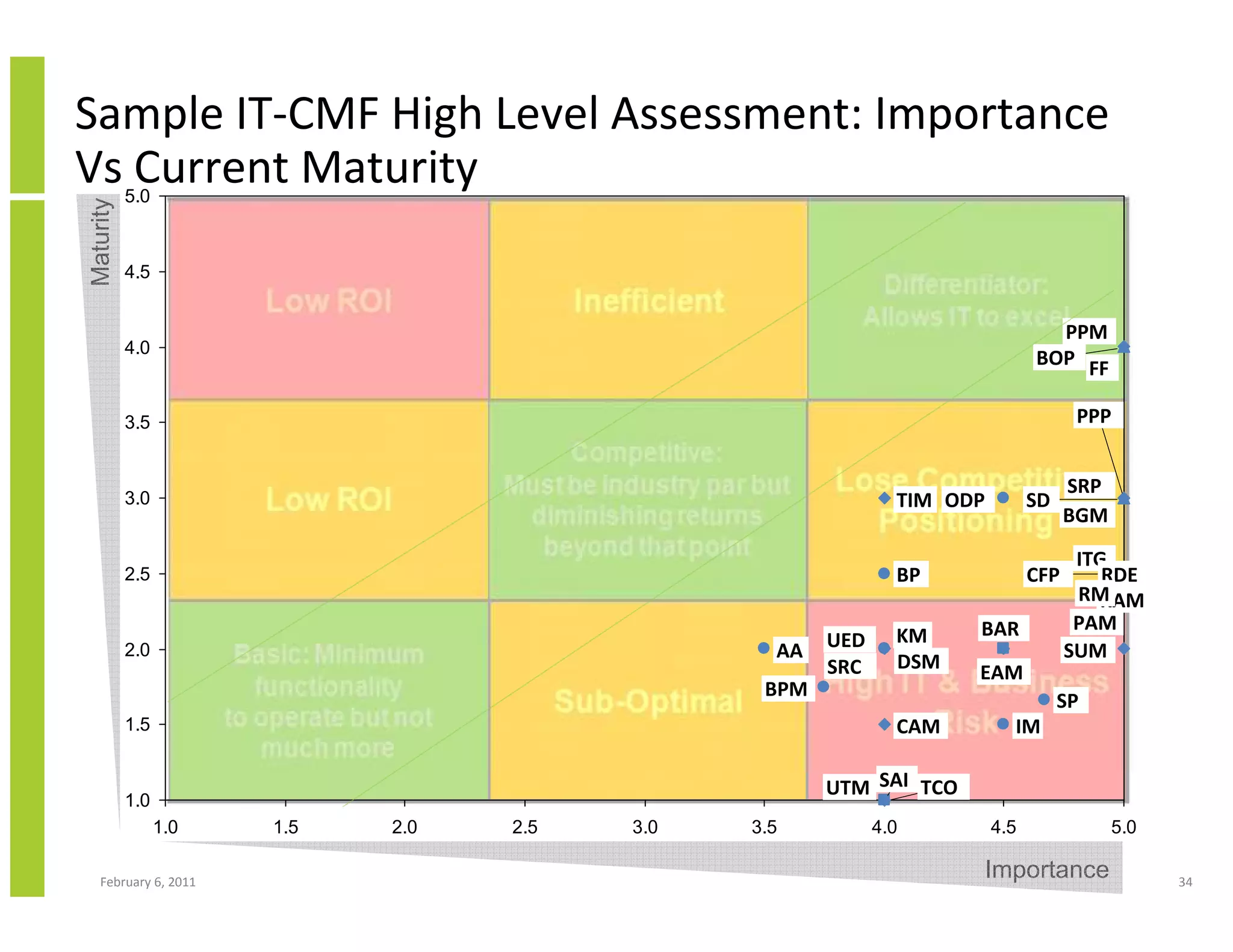
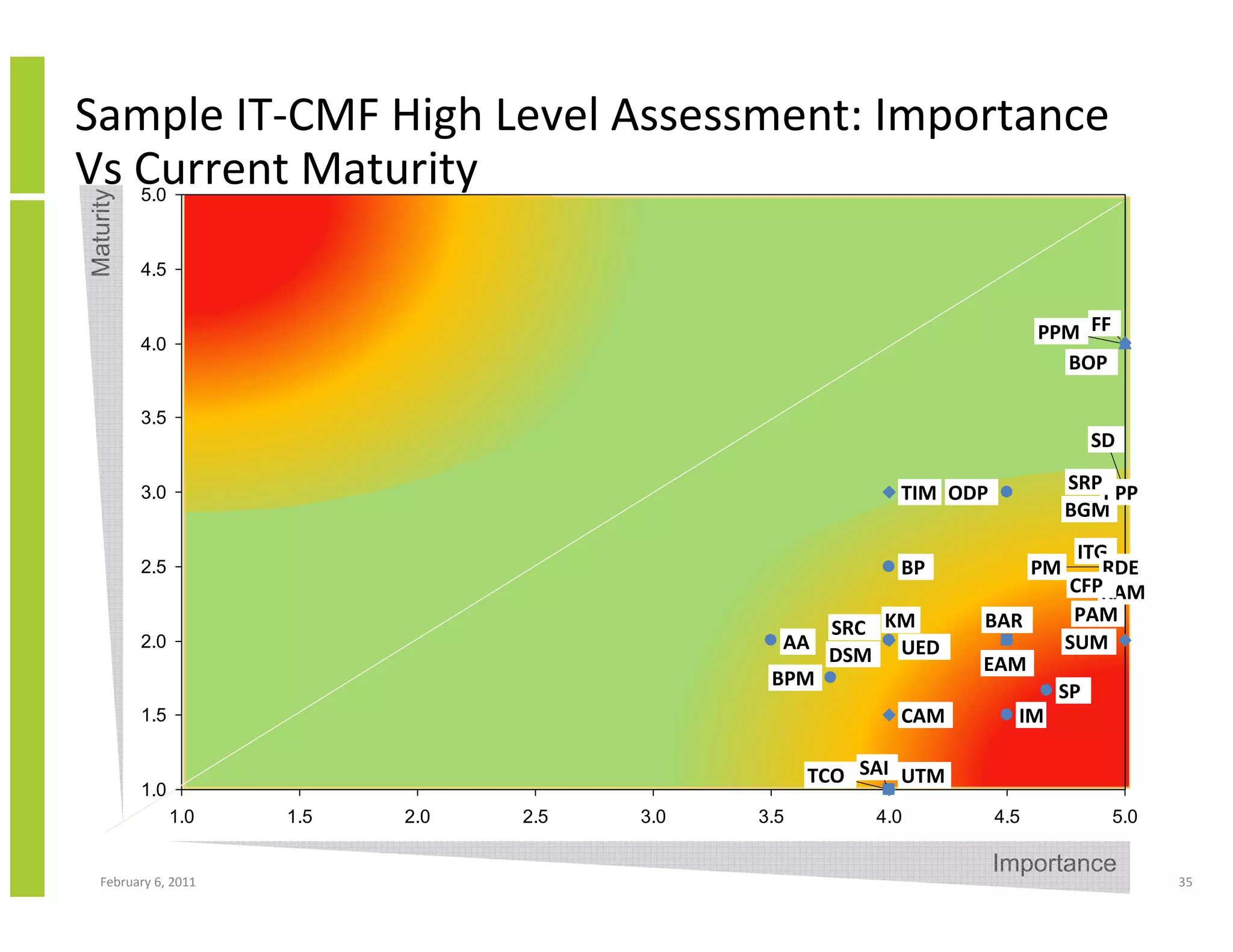
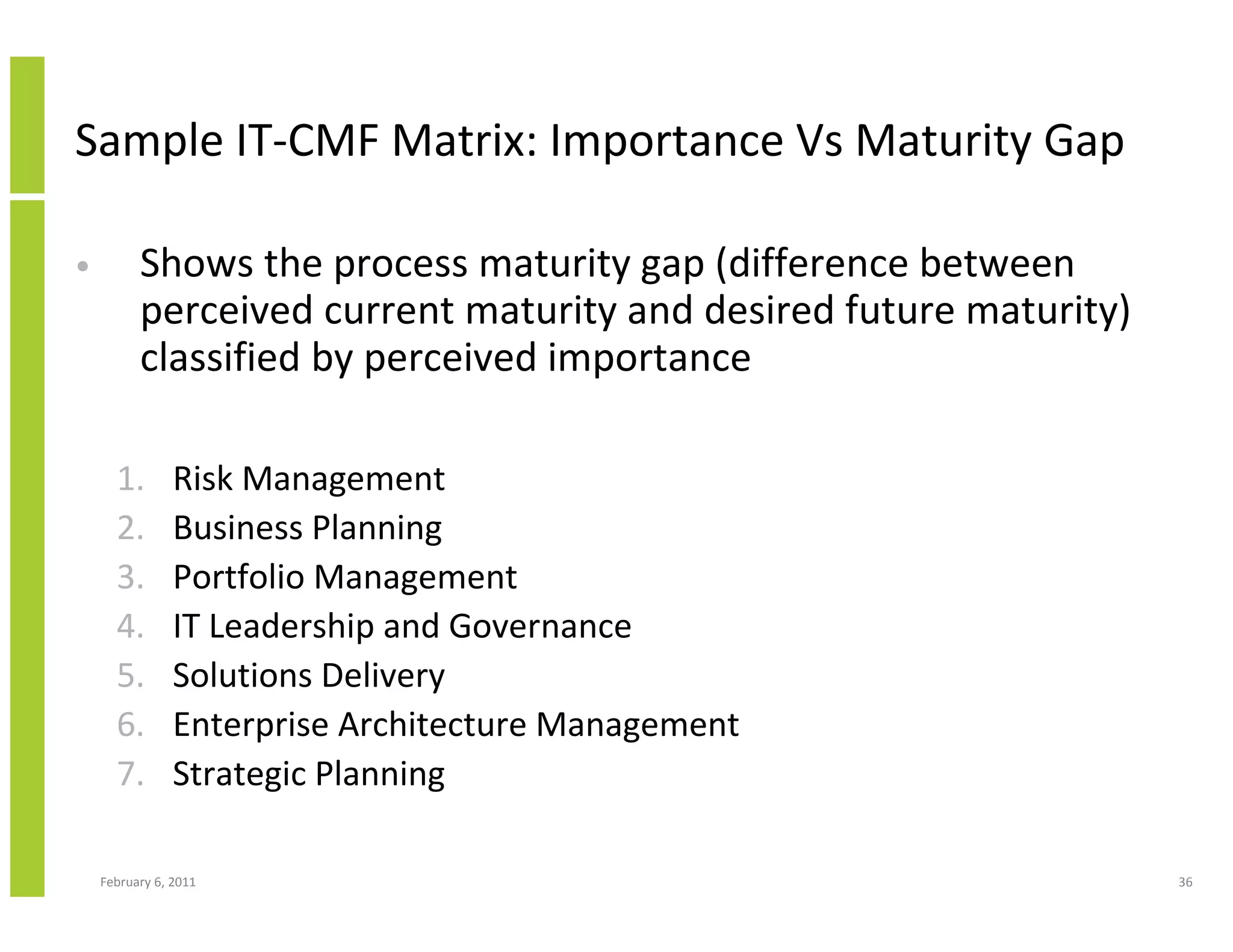
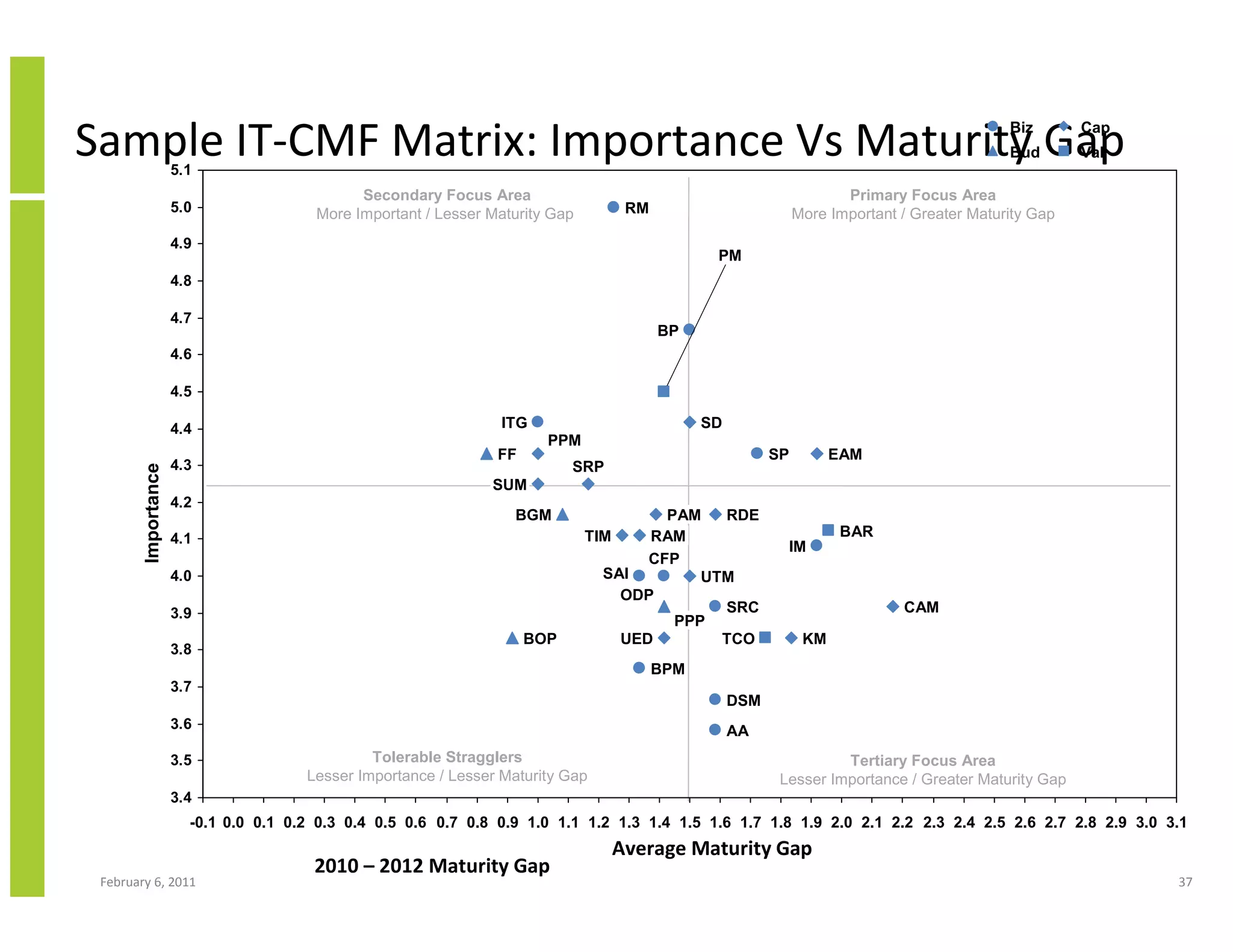
The document outlines the importance of the first 100 days for a newly appointed Chief Information Officer (CIO) by using the Innovation Value Institute's IT Capability Maturity Framework (IT-CMF) to establish a strategic roadmap. It emphasizes the need for effective communication, relationship building, and the crafting of both tactical and strategic plans that align IT with business objectives. The IT-CMF framework is presented as a tool to assess current IT practices, identify areas for improvement, and measure progress in delivering business value.