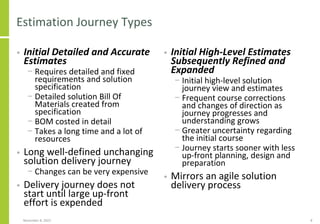
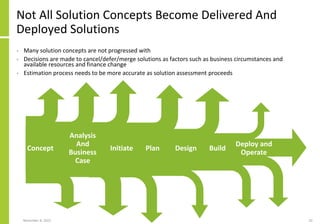
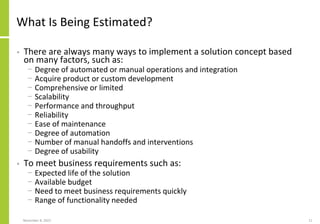
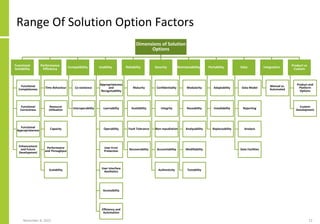
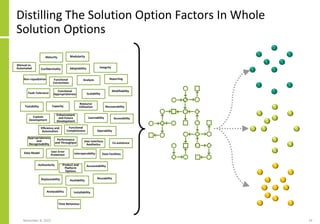
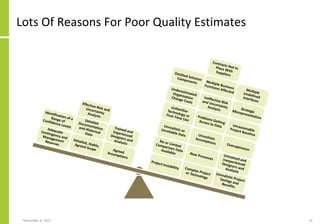
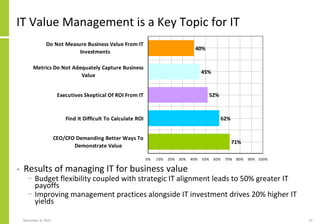
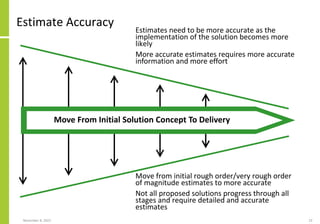
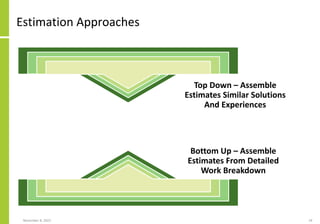
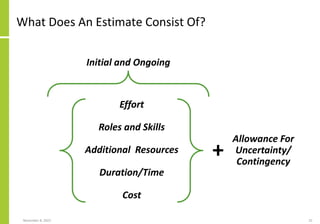
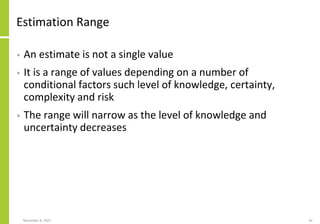
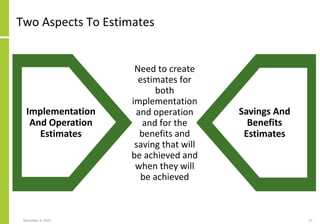
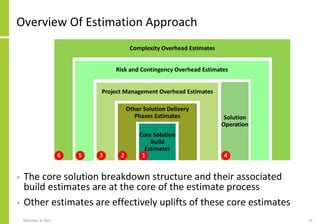
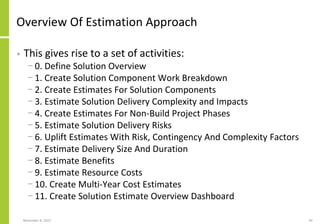
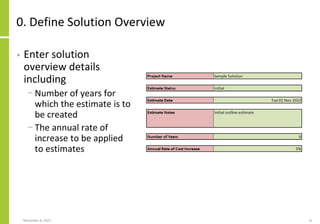
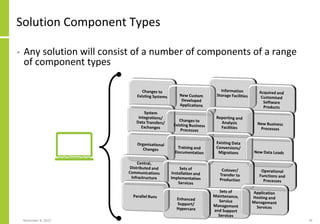
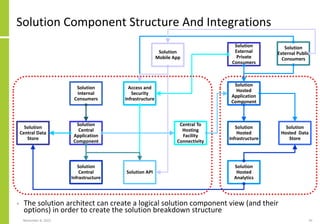
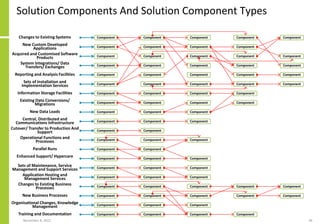
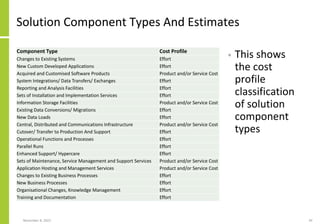
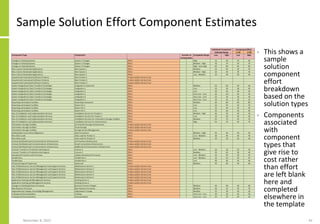
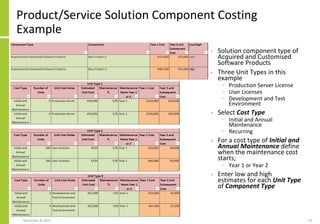
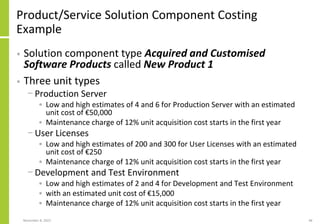
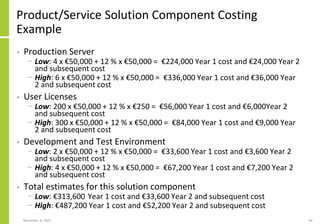
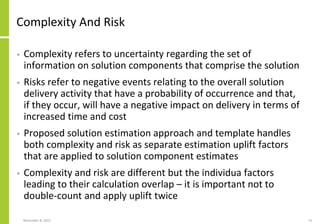
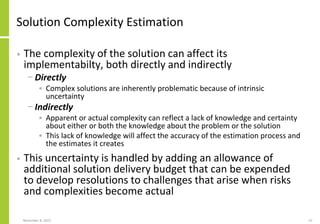
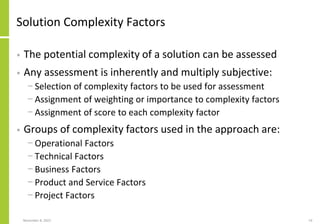
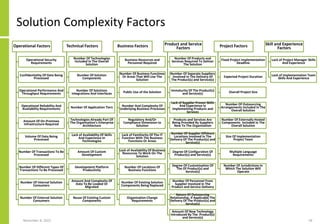
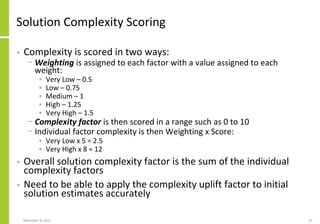
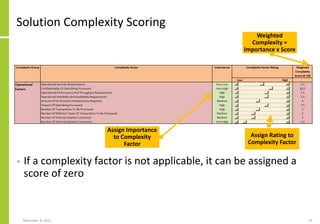
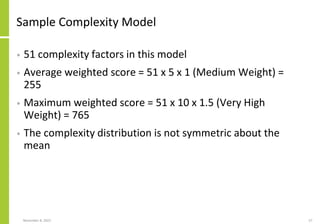
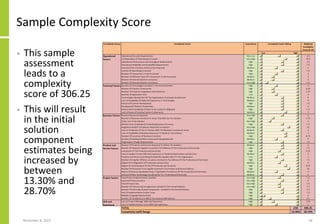
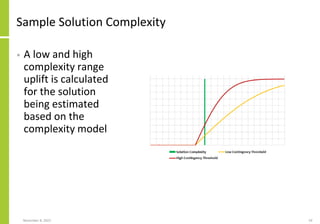
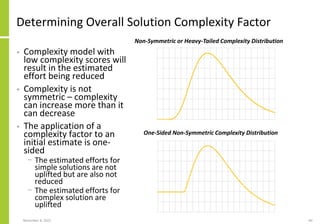
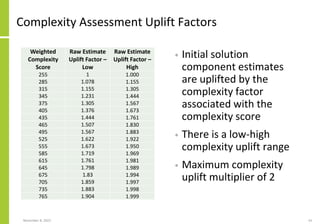
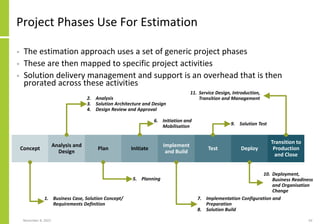
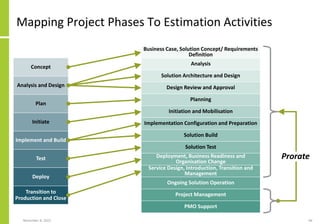
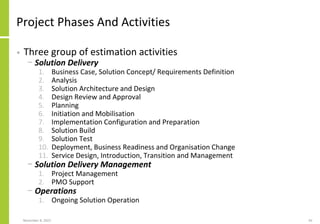
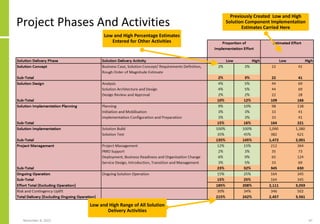
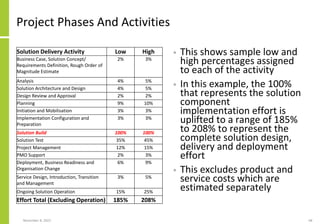
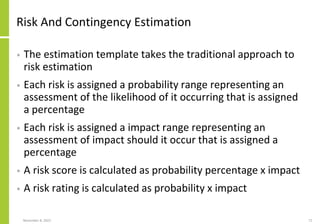
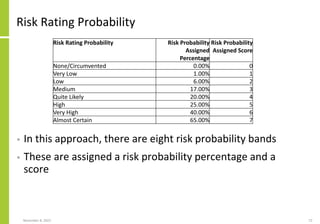
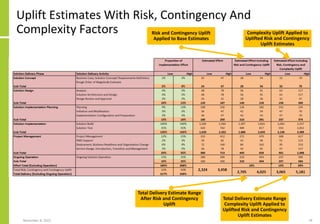
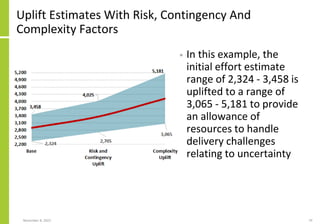
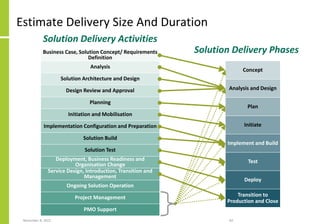
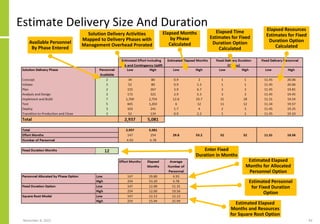
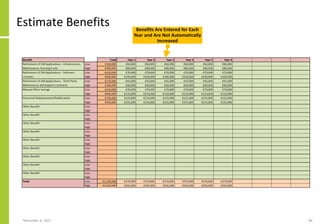
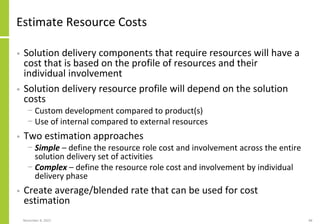
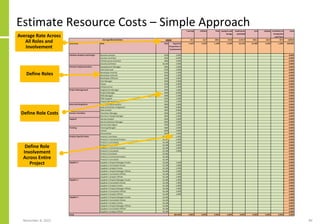
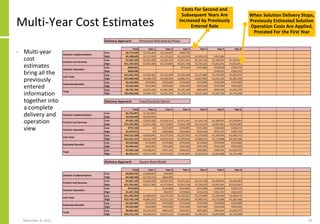
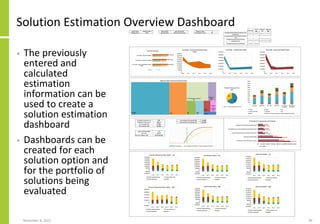
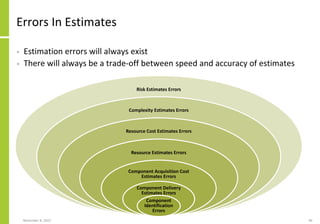
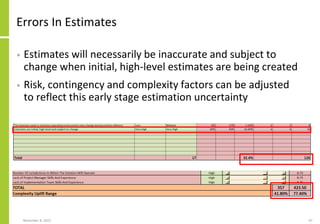
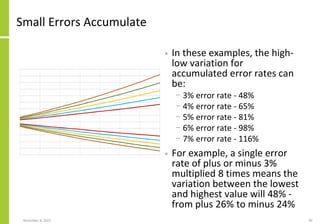
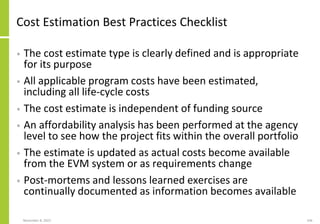
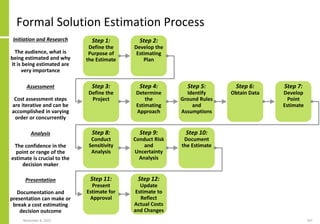
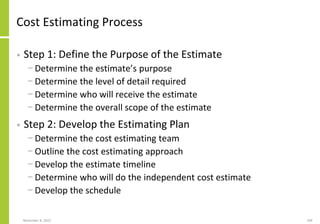
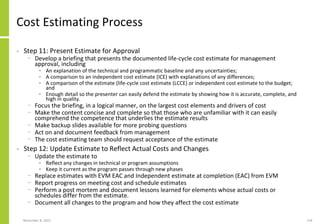
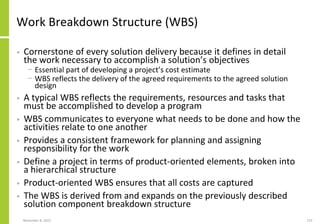
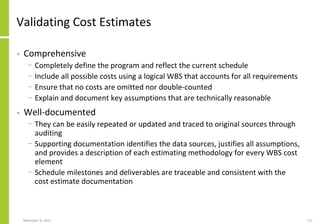
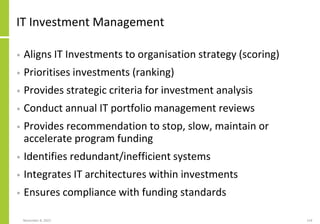
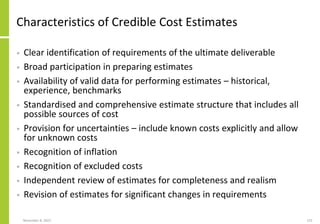
This document discusses solution architecture and estimation, emphasizing the importance of creating accurate delivery estimates by solution architects who understand the components and constraints of a solution. It outlines types of estimates, the investment management process, and various factors influencing solution design and costs, while also highlighting challenges and common issues like strategic misrepresentation. A structured estimation approach is detailed, proposing a method to create reliable and repeatable solution delivery estimates.