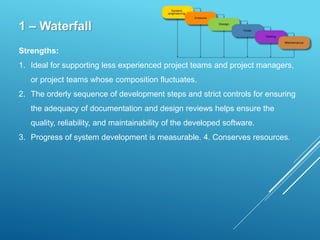
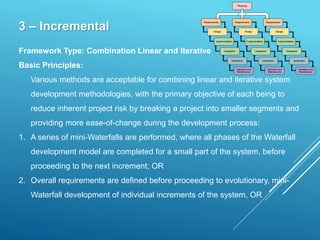
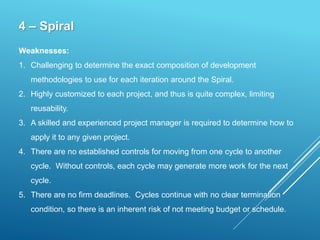
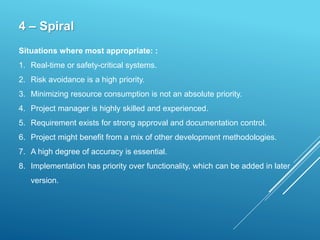
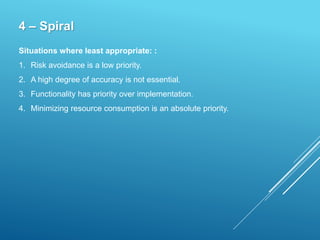
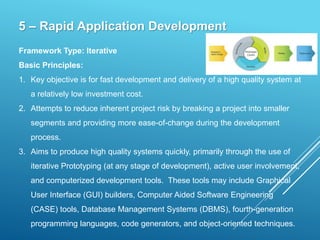
The document discusses various system development methodologies: Waterfall, Prototyping, Incremental, Spiral, and Rapid Application Development (RAD). For each methodology, it describes the framework type, basic principles, strengths, weaknesses, and situations where most/least appropriate. The Waterfall methodology is described in the most detail. It emphasizes structured development processes but can be inflexible. Prototyping focuses on iterative development and user involvement. Incremental combines linear and iterative approaches. Spiral emphasizes risk assessment. RAD aims for fast delivery through tools, iteration, and user involvement.