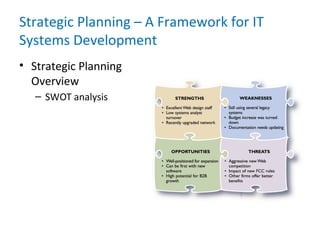
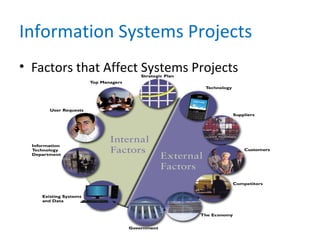
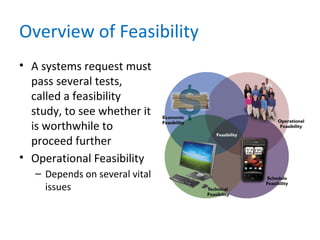
This chapter discusses analyzing the business case for IT projects. It explains that strategic planning helps companies develop mission statements and goals to guide projects. Systems projects are typically initiated to improve performance or reduce costs. During preliminary investigation, analysts evaluate feasibility and priority by analyzing costs, benefits, and factors affecting the proposed project. They then present results and recommendations to management in a report.