This document discusses language engineering and introduces a framework for building flexible and adaptable processing chains using combinatory logic. It proposes:
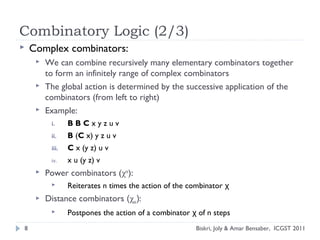
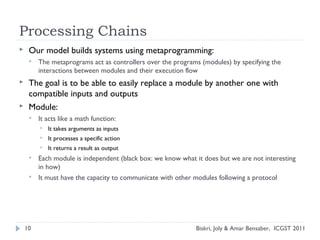
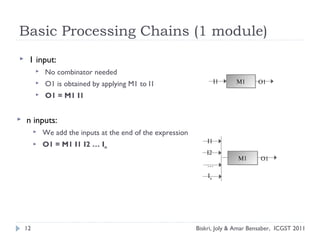
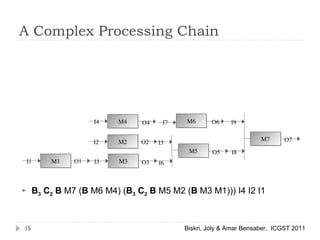
1) Using typed modules that can be composed together in processing chains using combinators like B, C, and Φ to ensure coherence.
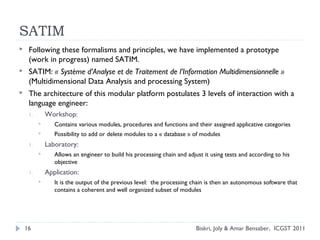
2) Implementing a prototype called SATIM that allows engineers to select modules, build processing chains, and test them before deploying as autonomous software applications.
3) Aiming to address needs for coherence, flexibility, and easy communication between programs through replacing modules as long as inputs and outputs are compatible.