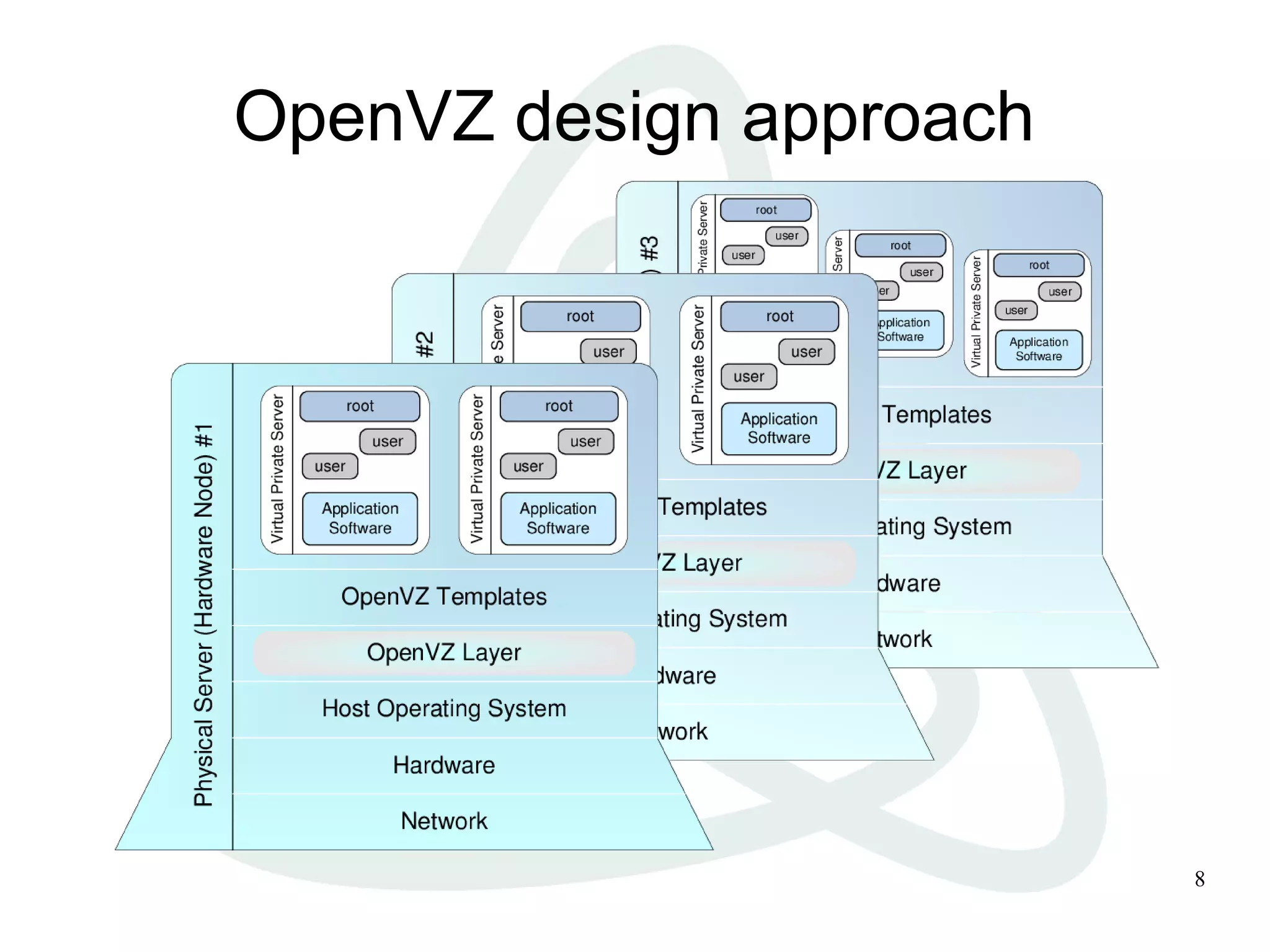
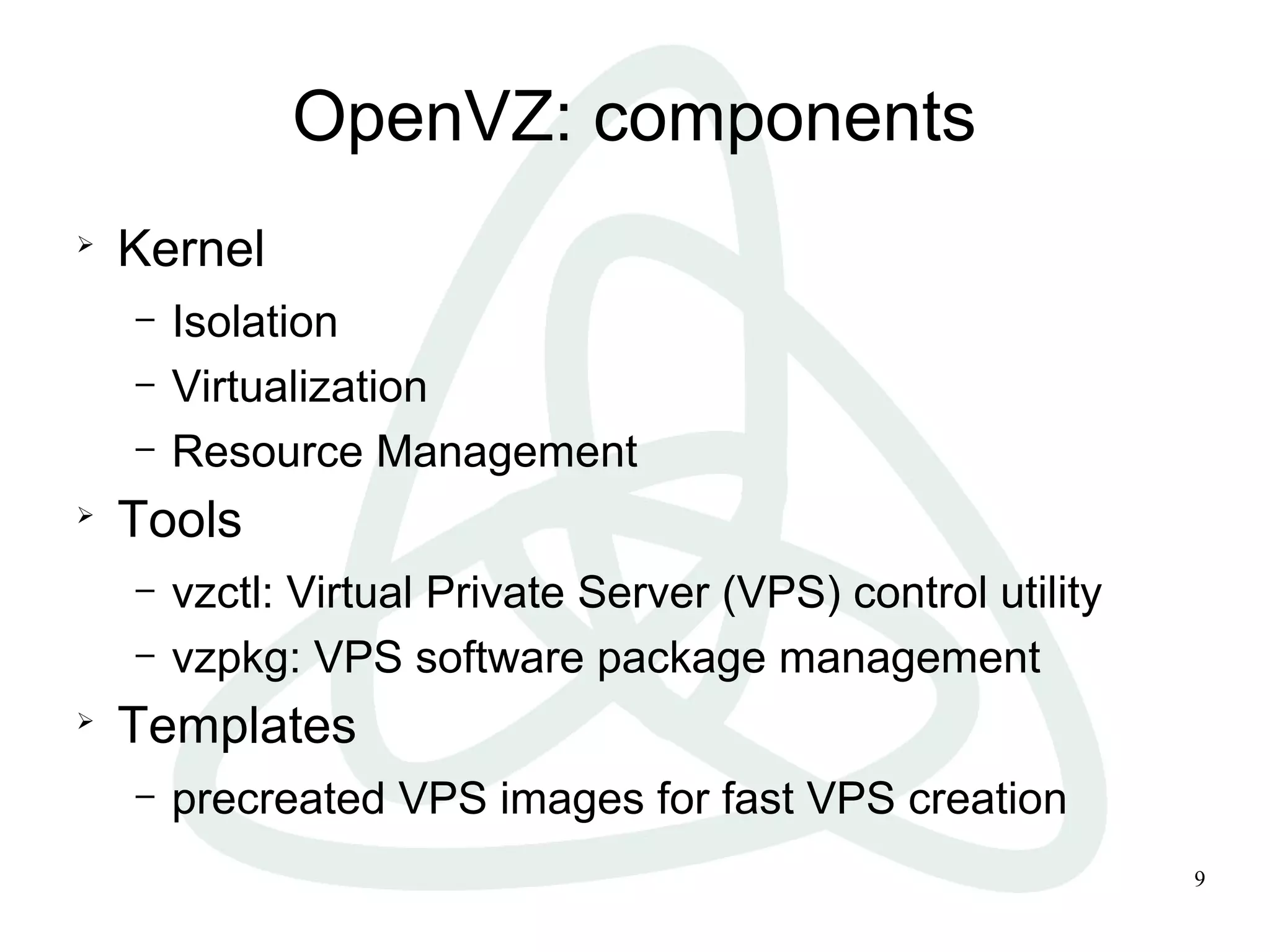
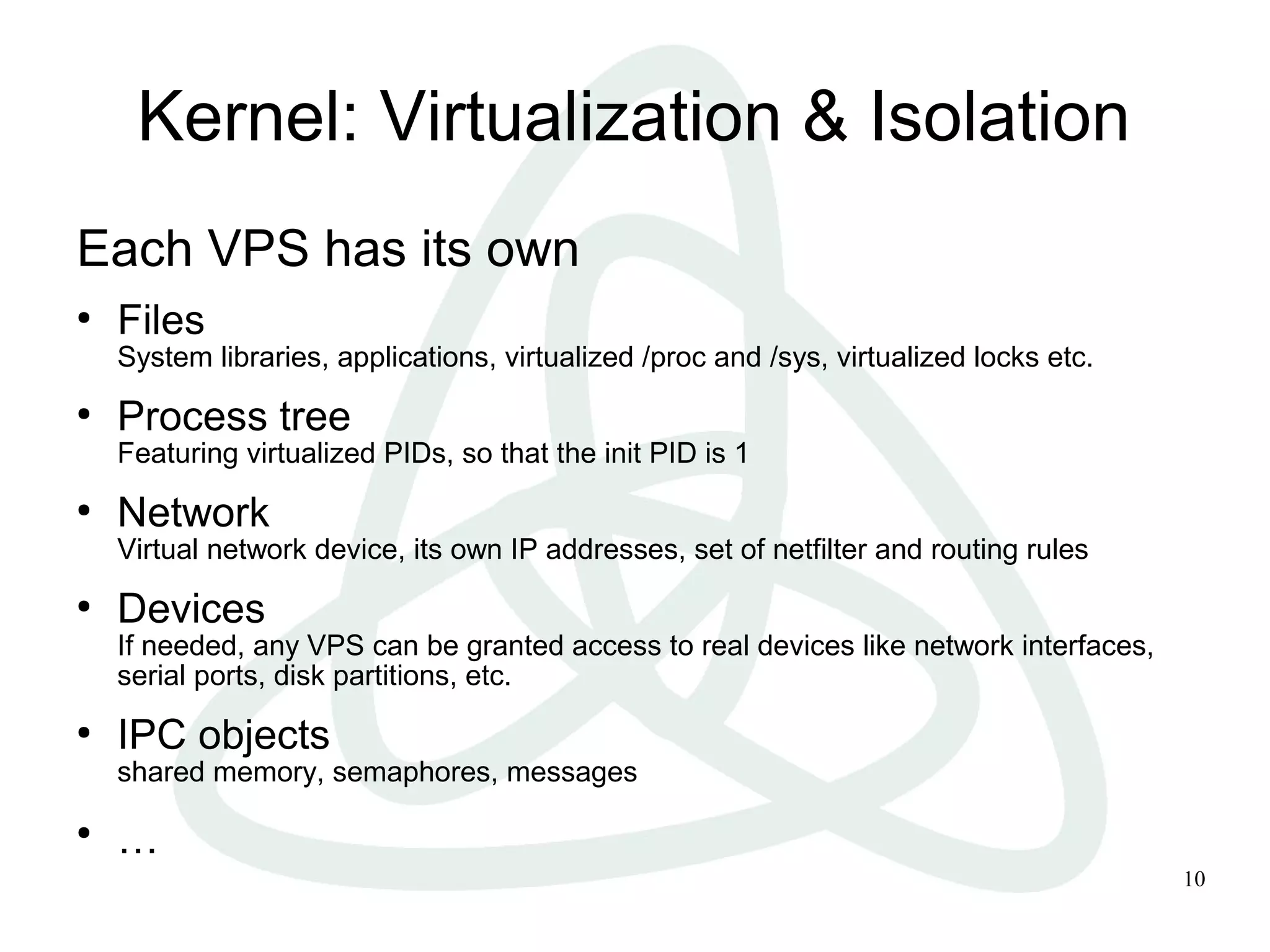
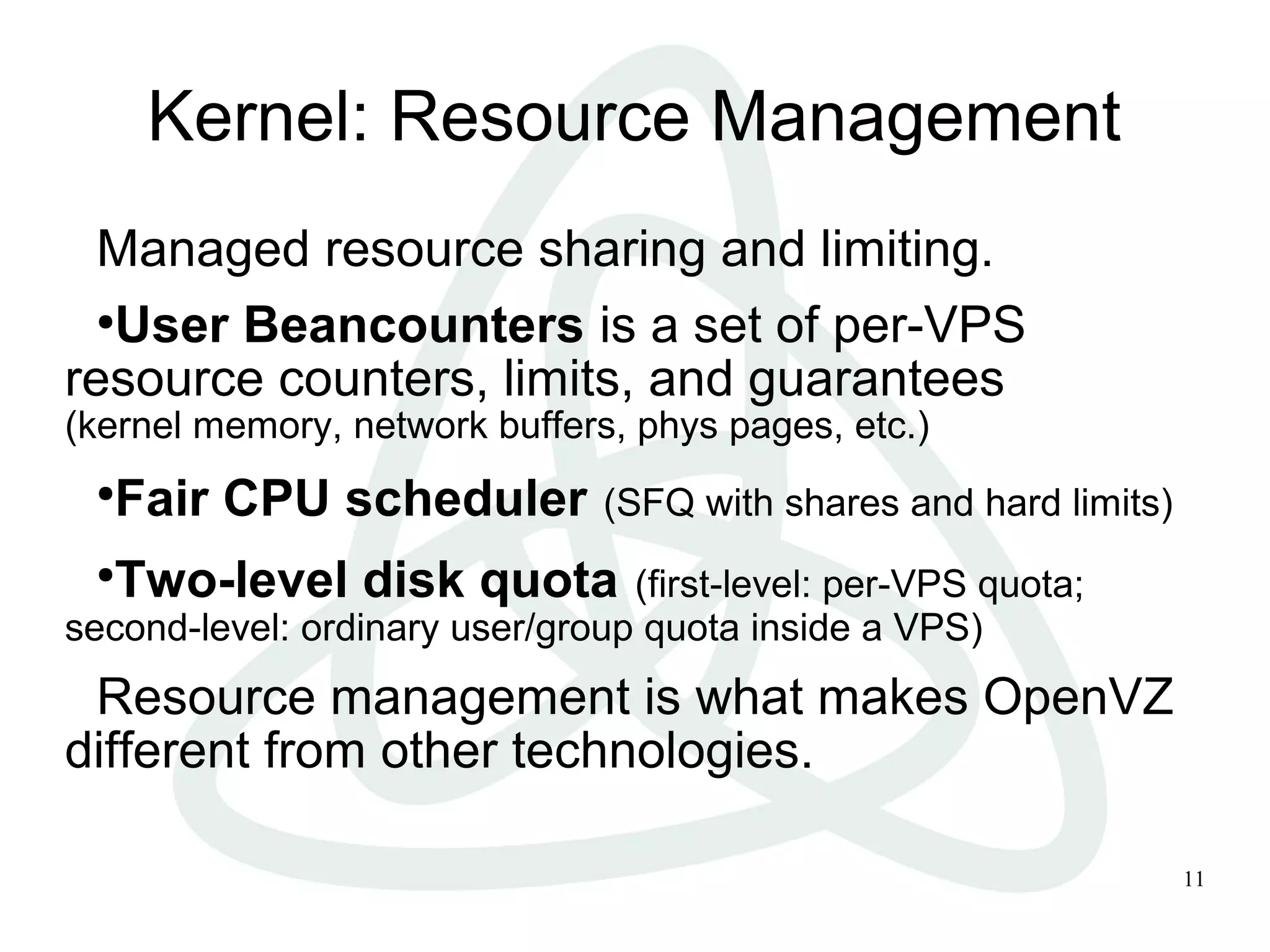
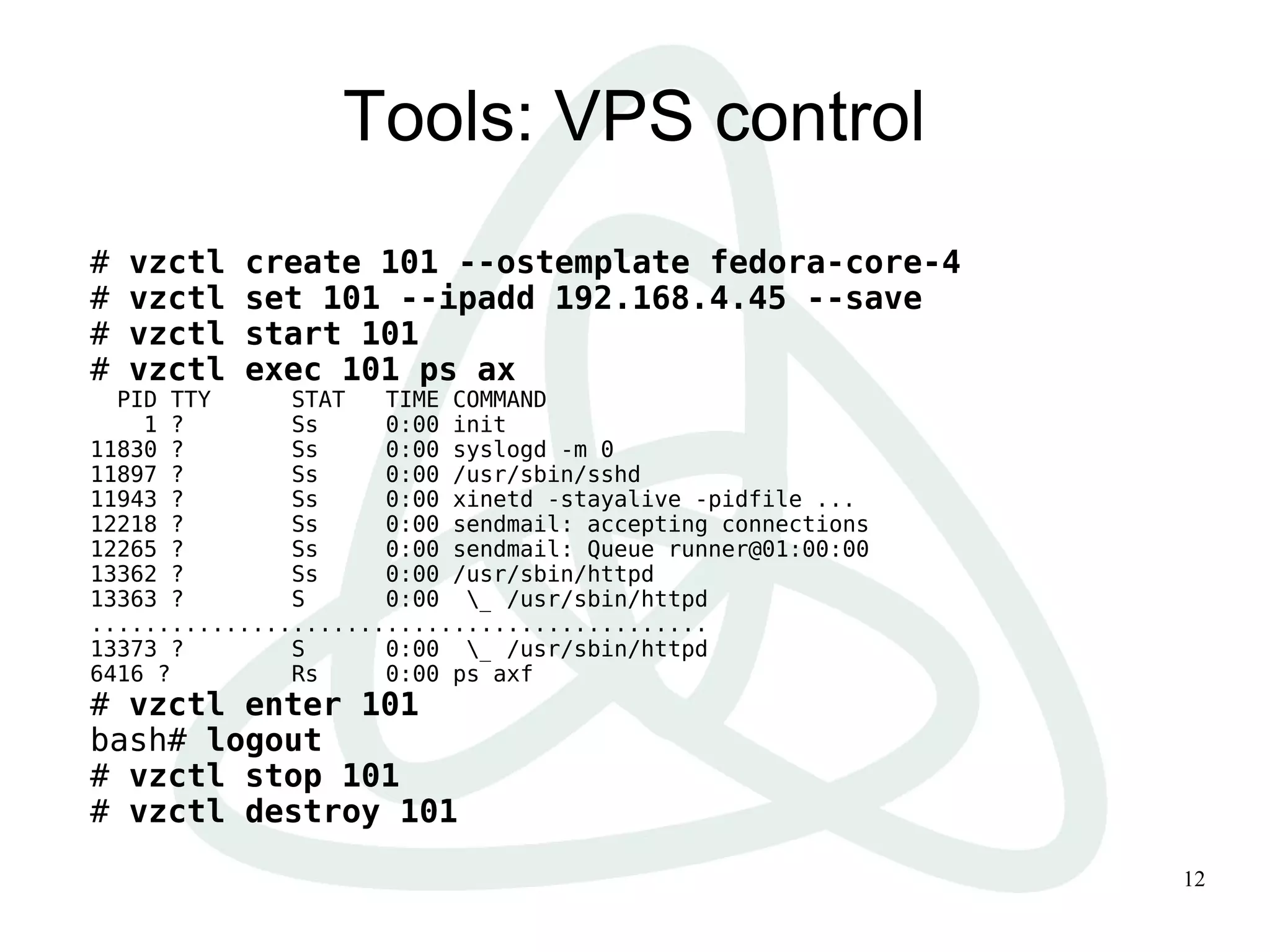
Virtualization creates an abstraction layer between physical hardware and the software that uses it. OpenVZ is an OS-level virtualization technology that partitions a physical Linux server's resources to run multiple isolated Linux systems. It provides high density and performance by running guest operating systems within the same kernel as the host. OpenVZ uses kernel features and tools to isolate guest environments, manage shared resources, and easily provision and migrate virtual private servers.