Openvz booth
•Download as ODP, PDF•
1 like•930 views
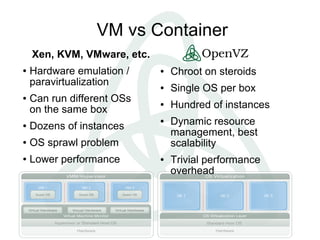
This document compares virtual machines (VMs) to containers and discusses their differences. It notes that VMs have higher overhead than containers and can support more instances per server. Containers offer near-native performance and scale better. The document also outlines ongoing and future work to further integrate container technologies into the Linux kernel to provide capabilities like checkpoint/restore and live migration of containers across servers.
Report
Share
Report
Share
Recommended
Re-Think of Virtualization and Containerization

The Hyper view on Container and Virtual Machine --- the similar parts and the different parts. The sildes was presented in Open Source Operating System Annual Technical Conference 2015 at Tsinghua University, Beijing on Nov 28th.
OSv: probably the best OS for cloud workloads you've never hear of

OSv is the revolutionary new open source technology that combines the power of virtualization and micro-services architecture. This combination allows unmodified applications deployed in a virtualized environment to outperform bare-metal deployments. Yes. You've heard it right: for the first time ever we can stop asking the question of how much performance would I lose if I virtualize. OSv lets you ask a different question: how much would my application gain in performance if I virtualize it. This talk will start by looking into the architecture of OSv and the kind of optimizations it makes possible for native, unmodified applications. We will then focus on JVM-specific optimizations and specifically on speedups available to big data management distributed applications. Finally, we will look into the relationship between OSv and Docker and how that layering can help make OSv a secret sauce for turbo-charging Cloud Foundry application deployments.
OSv – The OS designed for the Cloud

A lot of the cloud discussion centers around which hypervisors are the best, and which
management tools will simplify one's life the most. But is it the whole story? While addressing the problems from the lower and higher layers, the middle man -- the guest operating system -- is
usually left behind.
This talk will introduce OSv — a new from-scratch operating system written by a group of
former Linux veterans designed specifically for cloud deployments. We will showcase the
operating system architecture and explain the performance and manageability improvements that
can be expected
Live migrating a container: pros, cons and gotchas

In this talk I will briefly show why you might want to live migrate a container, why you might want to avoid doing this and what can be done instead. The main topic of the talk would to demonstrate why live migrating a container is more complex than live migrating a virtual machines and what can be done with this complexity.
Alex Fishman - Virtualizing the Cloud

Alex Fishman's slid deck from his presentation at OpenStack Israel May 2013
Nested Virtualization Update from Intel

Nested Virtualization is becoming hot and required to support multiple emerging usage models like XenClient, McAFee Deep Safe, HyperV etc. After enabling nested VMX support for Xen, we have been working on improving its quality and performance to make it run well with these new usages. In the session, we would like update current status of nested virtualization support in Xen, and also demonstrate what we are doing along with new hardware-assisted nested virtulization in this area.
Recommended
Re-Think of Virtualization and Containerization

The Hyper view on Container and Virtual Machine --- the similar parts and the different parts. The sildes was presented in Open Source Operating System Annual Technical Conference 2015 at Tsinghua University, Beijing on Nov 28th.
OSv: probably the best OS for cloud workloads you've never hear of

OSv is the revolutionary new open source technology that combines the power of virtualization and micro-services architecture. This combination allows unmodified applications deployed in a virtualized environment to outperform bare-metal deployments. Yes. You've heard it right: for the first time ever we can stop asking the question of how much performance would I lose if I virtualize. OSv lets you ask a different question: how much would my application gain in performance if I virtualize it. This talk will start by looking into the architecture of OSv and the kind of optimizations it makes possible for native, unmodified applications. We will then focus on JVM-specific optimizations and specifically on speedups available to big data management distributed applications. Finally, we will look into the relationship between OSv and Docker and how that layering can help make OSv a secret sauce for turbo-charging Cloud Foundry application deployments.
OSv – The OS designed for the Cloud

A lot of the cloud discussion centers around which hypervisors are the best, and which
management tools will simplify one's life the most. But is it the whole story? While addressing the problems from the lower and higher layers, the middle man -- the guest operating system -- is
usually left behind.
This talk will introduce OSv — a new from-scratch operating system written by a group of
former Linux veterans designed specifically for cloud deployments. We will showcase the
operating system architecture and explain the performance and manageability improvements that
can be expected
Live migrating a container: pros, cons and gotchas

In this talk I will briefly show why you might want to live migrate a container, why you might want to avoid doing this and what can be done instead. The main topic of the talk would to demonstrate why live migrating a container is more complex than live migrating a virtual machines and what can be done with this complexity.
Alex Fishman - Virtualizing the Cloud

Alex Fishman's slid deck from his presentation at OpenStack Israel May 2013
Nested Virtualization Update from Intel

Nested Virtualization is becoming hot and required to support multiple emerging usage models like XenClient, McAFee Deep Safe, HyperV etc. After enabling nested VMX support for Xen, we have been working on improving its quality and performance to make it run well with these new usages. In the session, we would like update current status of nested virtualization support in Xen, and also demonstrate what we are doing along with new hardware-assisted nested virtulization in this area.
Dockersh and a brief intro to the docker internals

Dockersh is a new tool to give a login shell into per-user Docker containers. (https://github.com/Yelp/dockersh) This talk will be an illustrated tour of what dockersh does, and why it might be useful to you. During this journey we’ll dive into the Go programming language, + libcontainer (the technologies Docker is built on) in addition to the facilities Docker uses in the kernel (Namespaces, Cgroups and Capabilities), how these work, and how normal mortals can (ab)use them for fun and profit
You Call that Micro, Mr. Docker? How OSv and Unikernels Help Micro-services S...

OSv is the new open source unikernel technology that combines the power of virtualization and micro-services architecture. This combination allows unmodified applications to be packaged just like Docker containers while at the same time outperform bare-metal deployments. Yes. You've heard it right: for the first time ever we can stop asking the question of how much performance would I lose if I virtualize. OSv lets you ask a different question: how much would my application gain in performance if I virtualize it. This talk will start by looking into the architecture of OSv and the kind of optimizations it makes possible for native, unmodified applications. We will then focus on JVM-specific optimizations and specifically on speedups available to micro-service oriented applications when they are being deployed on OSv.
runC: The little engine that could (run Docker containers) by Docker Captain ...

With the announcement of the OCI by Solomon Hykes at last summer's DockerCon, a Docker-contributed reference implementation of the OCI spec, called runC, was born. While some of you may have tried runC or have a history of poking at the OS layer integration library to Linux namespaces, cgroups and the like (known as libcontainer), many of you may not know what runC offers. In this talk Phil Estes, Docker engine maintainer who has also contributed to libcontainer and runC, will show what's possible using runC as a lightweight and fast runtime environment to experiment with lower-level features of the container runtime. Phil will introduce a conversion tool called "riddler", which can inspect and convert container configurations from Docker into the proper OCI configuration bundle for easy conversion between the two environments. He'll also demonstrate how to make custom configurations for trying out security features like user namespaces and seccomp profiles.
OpenNebulaConf 2016 - Measuring and tuning VM performance by Boyan Krosnov, S...

In this session we'll explore measuring VM performance and evaluating changes to settings or infrastructure which can affect performance positively. We'll also share the best current practice for architecture for high performance clouds from our experience.
XPDS14: Xen 4.5 Roadmap - Konrad Wilk, Oracle

Konrad Wilk is a Software Development Manager at Oracle. His group’s mission is to make Linux and Xen Project virtualization better and faster. As part of this work, Konrad has been the maintainer of the Xen Project subsystem in Linux, Xen Project maintainer and now also Release Manager for the 4.5 release of the Xen Project Hypervisor. Konrad has been active in the Linux and Xen Project communities for more than 6 years and was instrumental in adding Xen Project support to the Linux Kernel.
Project kronos open_stack_design_summit

http://blog.xen.org/index.php/2011/10/07/xen-openstack-design-summit/
Whats New in Havana--Nova

Part of Mirantis "What's New in Havana" Webinar, representing Nova features
Nexenta at VMworld Hands-on Lab

View the performance metrics that turned the heads of VMware, EMC, and NetApp at VMworld 2011.
See the reason why Nexenta is now the single biggest threat to legacy storage.
OpenNebulaConf 2016 - Hypervisors and Containers Hands-on Workshop by Jaime M...

In this 90-minute hands-on workshop, some of the key contributors to OpenNebula will walk attendees through the configuration and integration aspects of the computing subsystem in OpenNebula. The session will also include lightning talks by community members describing aspects related to Hypervisors and Containers with OpenNebula:
Deployment scenarios
Integration
Tuning & debugging
Best practices
OSv at Cassandra Summit

OSv is a new, high-performance OS for virtual machines in the cloud. Designed to run one application per guest with minimal overhead, OSv eliminates important bottlenecks for NoSQL applications through improvements in memory management, network I/O, and scheduling. And many important bottlenecks for NoSQL applications are tunable on a conventional OS, but do not require tuning in the OSv environment.
OSv is fully stateless and can be configured at runtime with cloud-init or through a REST API, with zero configuration files. OSv offers unified tracing from the application layer through the JVM and the OS kernel. Attendees will learn how to boot Cassandra in one second, and create a simple cluster in a minute.
OpenNebula Conf 2014: CentOS, QA an OpenNebula - Christoph Galuschka

CentOS, the Community Enterprise OS, uses Opennebula as virtualization plattform for its automated QA-process. The opennebula setup consists of 3 nodes, all running CentOS-6, who handle the following tasks:
– sunstone as cloud controller
– local mirror/DNS-Server/http-Server for the VMs to pull in packages
– one VM to run a jenkins instance to launch the various tests (ci.de.centos.org)
– nginx on the cloud controller to forward http traffic to the jenkins VM
A public git repository (http://www.gitorious.org/testautomation) is used to allow whoever wants to contribute to pull the current test suite – t_functional, a series of bash scripts used to do funtional tests of various applications, binaries, configuration files and Trademark issues. As new tests are added to the repo via personal clones and merge requests, those tests first need to complete a test run via jenkins. Each test run currently consists of 4 VMs (one for each arch for C5 and C6 – C7 to come), which run the complete test suite. All VMs used for theses tests are instantiated and torn down on demand, whenever the call to testrun a personal clone is issued (via IRC).
Once completed successfully, the request is merged into the main repo. The jenkins node monitors this repository and which automatically triggers another complete test run.
Besides these triggered test runs, the test suite is automatically triggered daily to run. This is used to verify functionality of published updates – a handfull of failty updates have allready been discovered this way.
Besides t_functional, the Linux Test Project Suite of tests is also run on a daily basis, also to verify functionality of the OS and all updates.
The third setup is used to test the available and functional integrity of published docker images for CentOS.
All these tests are later – during the QA-phase of a point release – used to verify functionality of new packages inside the CentOS QA-Setup.
Gluster as Native Storage for Containers - past, present and future

Gluster as Native Storage for Containers - past, present and future
Michael Adam and Humble Devassy Chirammal
Gluster Summit, Prague
Civil War: LXD vs Docker

A review about the scenarios with most expectations always from an OpenNebula’s
integration point of view. What can we expect nowadays of both technologies and
what should they improve in the future.
Talk held at the OpenNebula Techday Barcelona 2017:
https://opennebula.org/community/techdays/techday-barcelona-2017/
Xen versus kvm_slides_20080623

We present initial results from and quantitative analysis of two leading open source hypervisors, Xen and KVM. This study focuses on the overall performance, performance isolation, and scalability of virtual machines running on these hypervisors. Our comparison was carried out using a benchmark suite that we developed to make the results easily repeatable. Our goals are to understand how the different architectural decisions taken by different hypervisor developers affect the resulting hypervisors, to help hypervisor developers realize areas of improvement for their hypervisors, and to help users make informed decisions
about their choice of hypervisor.
Vulnerability Exploitation in Docker Container Environments

According to Forrester, 53% of IT respondents say their biggest concern about containers is security. Containerization is not only prevalent in browsers (Google Chrome), desktop applications (Adobe Reader X), and mobile operating systems (Apple iOS), but is also invading the data center via Docker. Docker and other LXC-based containerization solutions provide isolation via Linux control groups (cgroups). However, containers can still be exploited and even with kernel-level isolation, critical data can be stolen. In this presentation, the FlawCheck team will exploit real-world Docker implementations and show what can be done to mitigate the risk.
More Related Content
What's hot
Dockersh and a brief intro to the docker internals

Dockersh is a new tool to give a login shell into per-user Docker containers. (https://github.com/Yelp/dockersh) This talk will be an illustrated tour of what dockersh does, and why it might be useful to you. During this journey we’ll dive into the Go programming language, + libcontainer (the technologies Docker is built on) in addition to the facilities Docker uses in the kernel (Namespaces, Cgroups and Capabilities), how these work, and how normal mortals can (ab)use them for fun and profit
You Call that Micro, Mr. Docker? How OSv and Unikernels Help Micro-services S...

OSv is the new open source unikernel technology that combines the power of virtualization and micro-services architecture. This combination allows unmodified applications to be packaged just like Docker containers while at the same time outperform bare-metal deployments. Yes. You've heard it right: for the first time ever we can stop asking the question of how much performance would I lose if I virtualize. OSv lets you ask a different question: how much would my application gain in performance if I virtualize it. This talk will start by looking into the architecture of OSv and the kind of optimizations it makes possible for native, unmodified applications. We will then focus on JVM-specific optimizations and specifically on speedups available to micro-service oriented applications when they are being deployed on OSv.
runC: The little engine that could (run Docker containers) by Docker Captain ...

With the announcement of the OCI by Solomon Hykes at last summer's DockerCon, a Docker-contributed reference implementation of the OCI spec, called runC, was born. While some of you may have tried runC or have a history of poking at the OS layer integration library to Linux namespaces, cgroups and the like (known as libcontainer), many of you may not know what runC offers. In this talk Phil Estes, Docker engine maintainer who has also contributed to libcontainer and runC, will show what's possible using runC as a lightweight and fast runtime environment to experiment with lower-level features of the container runtime. Phil will introduce a conversion tool called "riddler", which can inspect and convert container configurations from Docker into the proper OCI configuration bundle for easy conversion between the two environments. He'll also demonstrate how to make custom configurations for trying out security features like user namespaces and seccomp profiles.
OpenNebulaConf 2016 - Measuring and tuning VM performance by Boyan Krosnov, S...

In this session we'll explore measuring VM performance and evaluating changes to settings or infrastructure which can affect performance positively. We'll also share the best current practice for architecture for high performance clouds from our experience.
XPDS14: Xen 4.5 Roadmap - Konrad Wilk, Oracle

Konrad Wilk is a Software Development Manager at Oracle. His group’s mission is to make Linux and Xen Project virtualization better and faster. As part of this work, Konrad has been the maintainer of the Xen Project subsystem in Linux, Xen Project maintainer and now also Release Manager for the 4.5 release of the Xen Project Hypervisor. Konrad has been active in the Linux and Xen Project communities for more than 6 years and was instrumental in adding Xen Project support to the Linux Kernel.
Project kronos open_stack_design_summit

http://blog.xen.org/index.php/2011/10/07/xen-openstack-design-summit/
Whats New in Havana--Nova

Part of Mirantis "What's New in Havana" Webinar, representing Nova features
Nexenta at VMworld Hands-on Lab

View the performance metrics that turned the heads of VMware, EMC, and NetApp at VMworld 2011.
See the reason why Nexenta is now the single biggest threat to legacy storage.
OpenNebulaConf 2016 - Hypervisors and Containers Hands-on Workshop by Jaime M...

In this 90-minute hands-on workshop, some of the key contributors to OpenNebula will walk attendees through the configuration and integration aspects of the computing subsystem in OpenNebula. The session will also include lightning talks by community members describing aspects related to Hypervisors and Containers with OpenNebula:
Deployment scenarios
Integration
Tuning & debugging
Best practices
OSv at Cassandra Summit

OSv is a new, high-performance OS for virtual machines in the cloud. Designed to run one application per guest with minimal overhead, OSv eliminates important bottlenecks for NoSQL applications through improvements in memory management, network I/O, and scheduling. And many important bottlenecks for NoSQL applications are tunable on a conventional OS, but do not require tuning in the OSv environment.
OSv is fully stateless and can be configured at runtime with cloud-init or through a REST API, with zero configuration files. OSv offers unified tracing from the application layer through the JVM and the OS kernel. Attendees will learn how to boot Cassandra in one second, and create a simple cluster in a minute.
OpenNebula Conf 2014: CentOS, QA an OpenNebula - Christoph Galuschka

CentOS, the Community Enterprise OS, uses Opennebula as virtualization plattform for its automated QA-process. The opennebula setup consists of 3 nodes, all running CentOS-6, who handle the following tasks:
– sunstone as cloud controller
– local mirror/DNS-Server/http-Server for the VMs to pull in packages
– one VM to run a jenkins instance to launch the various tests (ci.de.centos.org)
– nginx on the cloud controller to forward http traffic to the jenkins VM
A public git repository (http://www.gitorious.org/testautomation) is used to allow whoever wants to contribute to pull the current test suite – t_functional, a series of bash scripts used to do funtional tests of various applications, binaries, configuration files and Trademark issues. As new tests are added to the repo via personal clones and merge requests, those tests first need to complete a test run via jenkins. Each test run currently consists of 4 VMs (one for each arch for C5 and C6 – C7 to come), which run the complete test suite. All VMs used for theses tests are instantiated and torn down on demand, whenever the call to testrun a personal clone is issued (via IRC).
Once completed successfully, the request is merged into the main repo. The jenkins node monitors this repository and which automatically triggers another complete test run.
Besides these triggered test runs, the test suite is automatically triggered daily to run. This is used to verify functionality of published updates – a handfull of failty updates have allready been discovered this way.
Besides t_functional, the Linux Test Project Suite of tests is also run on a daily basis, also to verify functionality of the OS and all updates.
The third setup is used to test the available and functional integrity of published docker images for CentOS.
All these tests are later – during the QA-phase of a point release – used to verify functionality of new packages inside the CentOS QA-Setup.
Gluster as Native Storage for Containers - past, present and future

Gluster as Native Storage for Containers - past, present and future
Michael Adam and Humble Devassy Chirammal
Gluster Summit, Prague
Civil War: LXD vs Docker

A review about the scenarios with most expectations always from an OpenNebula’s
integration point of view. What can we expect nowadays of both technologies and
what should they improve in the future.
Talk held at the OpenNebula Techday Barcelona 2017:
https://opennebula.org/community/techdays/techday-barcelona-2017/
What's hot (20)
Dockersh and a brief intro to the docker internals

Dockersh and a brief intro to the docker internals
You Call that Micro, Mr. Docker? How OSv and Unikernels Help Micro-services S...

You Call that Micro, Mr. Docker? How OSv and Unikernels Help Micro-services S...
runC: The little engine that could (run Docker containers) by Docker Captain ...

runC: The little engine that could (run Docker containers) by Docker Captain ...
OpenNebulaConf 2016 - Measuring and tuning VM performance by Boyan Krosnov, S...

OpenNebulaConf 2016 - Measuring and tuning VM performance by Boyan Krosnov, S...
OpenNebulaConf 2016 - Hypervisors and Containers Hands-on Workshop by Jaime M...

OpenNebulaConf 2016 - Hypervisors and Containers Hands-on Workshop by Jaime M...
OpenNebula Conf 2014: CentOS, QA an OpenNebula - Christoph Galuschka

OpenNebula Conf 2014: CentOS, QA an OpenNebula - Christoph Galuschka
Gluster as Native Storage for Containers - past, present and future

Gluster as Native Storage for Containers - past, present and future
Viewers also liked
Xen versus kvm_slides_20080623

We present initial results from and quantitative analysis of two leading open source hypervisors, Xen and KVM. This study focuses on the overall performance, performance isolation, and scalability of virtual machines running on these hypervisors. Our comparison was carried out using a benchmark suite that we developed to make the results easily repeatable. Our goals are to understand how the different architectural decisions taken by different hypervisor developers affect the resulting hypervisors, to help hypervisor developers realize areas of improvement for their hypervisors, and to help users make informed decisions
about their choice of hypervisor.
Vulnerability Exploitation in Docker Container Environments

According to Forrester, 53% of IT respondents say their biggest concern about containers is security. Containerization is not only prevalent in browsers (Google Chrome), desktop applications (Adobe Reader X), and mobile operating systems (Apple iOS), but is also invading the data center via Docker. Docker and other LXC-based containerization solutions provide isolation via Linux control groups (cgroups). However, containers can still be exploited and even with kernel-level isolation, critical data can be stolen. In this presentation, the FlawCheck team will exploit real-world Docker implementations and show what can be done to mitigate the risk.
Docker - Build, Ship and Run Any App, Anywhere Hollywood edition

Since I presented this inside a movie theater I reference a few movies. This talk covers the Why of Docker more business case relevant, the VM vs Containers argument and Swisscom use cases with Docker
Containers and microservices for realists

Talk for Oracle Code Conference- New York 2017. Container, Microservices, Serverless
What's Better than Microservices? Serverless Microservices.

Learn how Autodesk is transforming its services architecture to lightweight microservices using a combination of Amazon Web Services and Apigee. Topic include:
- real world microservices examples
- how to use AWS Lambda and Apigee to build serverless APIs
- how to manage microservices in the cloud
LCEU13: Securing your cloud with Xen's advanced security features - George Du...

LCEU13: Securing your cloud with Xen's advanced security features - George Du...The Linux Foundation
Xen is a mature enterprise-grade virtual machine with many advanced security features which are unique to Xen. For this reason it's the hypervisor of choice for the NSA, the DoD, and the new QubesOS Secure Desktop project. While much of the security of Xen is inherent in its design, many of the advanced security features, such as stub domains, driver domains, XSM, and so on are not enabled by default. This session will describe all of the advanced security features of Xen, and the best way to configure them for the Cloud environment. When the audience leaves, they should have a general framework to evaluate the security of their system, know the key security features of Xen, and have a basic framework of knowledge to help them make sense of the documentation. This talk will *not* go into mind-numbing detail about specific commands to type or configuration options.Infrastructure as code: running microservices on AWS using Docker, Terraform,...

This is a talk about managing your software and infrastructure-as-code that walks through a real-world example of deploying microservices on AWS using Docker, Terraform, and ECS.
Hype vs. Reality: The AI Explainer

Artificial intelligence (AI) is everywhere, promising self-driving cars, medical breakthroughs, and new ways of working. But how do you separate hype from reality? How can your company apply AI to solve real business problems?
Here’s what AI learnings your business should keep in mind for 2017.
Viewers also liked (12)
Vulnerability Exploitation in Docker Container Environments

Vulnerability Exploitation in Docker Container Environments
Docker - Build, Ship and Run Any App, Anywhere Hollywood edition

Docker - Build, Ship and Run Any App, Anywhere Hollywood edition
What's Better than Microservices? Serverless Microservices.

What's Better than Microservices? Serverless Microservices.
LCEU13: Securing your cloud with Xen's advanced security features - George Du...

LCEU13: Securing your cloud with Xen's advanced security features - George Du...
Infrastructure as code: running microservices on AWS using Docker, Terraform,...

Infrastructure as code: running microservices on AWS using Docker, Terraform,...
Similar to Openvz booth
OpenVZ Linux Containers

The talk is about operating system virtualization technology known as OpenVZ. This is an effective way of partitioning a Linux machine into multiple isolated Linux containers. All containers are running on top of one single Linux kernel, which results in excellent density, performance and manageability. The talk gives an overall description of OpenVZ building blocks, such as namespaces, cgroups and various resource controllers. A few features, notably live migration and virtual swap, are described in greater details. Results of some performance measurements against VMware, Xen and KVM are given. Finally, we will provide a status update on merging bits and pieces of OpenVZ kernel to upstream Linux kernel, and share our plans for the future.
Oscon 2012 : From Datacenter to the Cloud - Featuring Xen and XCP

Do you dream of being able to spin up ten or twenty (or a thousand) virtual machines in an instant? Discover and repair resource bottlenecks without moving a finger? Dodge the loss of an entire storage array with no-one noticing? Span across data centers with a fleet of virtual machines? This is no sales pitch; during this tutorial, we’ll demonstrate how to leverage truly FOSS tools to build a powerful, scalable cloud that easily competes with those proprietary solutions!
This deep-dive into Xen, Xen Cloud Platform, and other FOSS cloud tools and concepts is intended both for those ready to wholeheartedly embrace virtualization and for those already seasoned in general virtualization practices. You’ll leave with a collection of pre-made tools that you can use right out of the box or modify to your liking. You’ll also leave with immediately useful knowledge on best practices and common pitfalls, presented by actual FOSS practitioners like you.
We begin this tutorial by discussing Xen, Xen Cloud Platform (XCP), and XCP cloud concepts (pools, hosts, storage, networks, etc.). We then explore in detail the API that makes Xen so useful for building a cloud, explore provisioning of hosts and guests using PXE, and discuss templating and installing guest virtual machines. Critical to understanding potential bottlenecks, identifying tuning opportunities and planning for the future, we will discuss performance monitoring and methodologies. Next, we teach you how to make the most of your new FOSS cloud capabilities and discuss in detail high availability infrastructure for storage and networking, advanced networking capabilities like bonding/VLANs, and the cloud orchestration tools that save you time and money. All of this with a focus on XCP in enterprise environments. Tools discussed include DRBD, Pacemaker, Open vSwitch, Cloudstack, Openstack, and more.
We conclude by shedding light on exciting developments: Xen 4.2 has recently been released, with just over a year of development time and nearly 3,000 changesets. We will discuss many of the new features introduced in 4.2, as well as what changes we have in store for the 4.3 release as well as other exciting developments.
2. Vagin. Linux containers. June 01, 2013

Fedora Virtualization Day 2013. Moscow.
June 01, 2013.
Andrey Vagin (Андрей Вагин).
Language: russian.
Введение в технологию Linux Containers.
https://www.youtube.com/watch?v=N7if7aJcnkg&index=3&list=PLTWTWm0uA2fLok6RlpJYy350FDQiRXYbS
Практические применения контайнеров (vzctl, Lxcl, systemd, unshare).
https://www.youtube.com/watch?v=ghlyp8JnR50&index=4&list=PLTWTWm0uA2fLok6RlpJYy350FDQiRXYbS
Testing kubernetes and_open_shift_at_scale_20170209

Slides from 9 February, 2017 Triangle Kubernetes and OpenShift meetup
N problems of Linux Containers

Over the years our engineers faced some complex technical problems. This talk is an overview of some of those problems, as well as solutions we came up with.
Let's Try Every CRI Runtime Available for Kubernetes

A talk given at KubeCon/CloudNativeCon EU in Barcelona, Spain on May 23, 2019. In this talk Phil presented the explosion of OCI-compliant CRI-enabled runtimes that can be used underneath Kubernetes, and demonstrated several of them live.
Containers: from development to production at DevNation 2015

In Docker, applications are shipped using a lightweight format, managed with a high-level API, and run within software containers which abstract the host environment. Operating details like distributions, versions, and network setup no longer matter to the application developer.
Thanks to this abstraction level, we can use the same container across all steps of the life cycle of an application, from development to production. This eliminates problems stemming from discrepancies between those environments.
Even so, these environments will always have different requirements. If our quality assurance (QA) and production systems use different logging systems, how can we still ship the same container to both? How can we satisfy the backup and security requirements of our production stack without bloating our development stack?
In this sess, you will learn about the unique features in containers that allow you to cleanly decouple system administrator tasks from the core of your application. We’ll show you how this decoupling results in smaller, simpler containers, and gives you more flexibility when building, managing, and evolving your application stacks.
Containers > VMs

Historically, sharing a Linux server entailed all kinds of untenable compromises. In addition to the security concerns, there was simply no good way to keep one application from hogging resources and messing with the others. The classic “noisy neighbor” problem made shared systems the bargain-basement slums of the Internet, suitable only for small or throwaway projects.
Serious use-cases traditionally demanded dedicated systems. Over the past decade virtualization (in conjunction with Moore’s law) has democratized the availability of what amount to dedicated systems, and the result is hundreds of thousands of websites and applications deployed into VPS or cloud instances. It’s a step in the right direction, but still has glaring flaws.
Most of these websites are just piles of code sitting on a server somewhere. How did that code got there? How can it can be scaled? Secured? Maintained? It’s anybody’s guess. There simply isn’t enough SysAdmin talent in the world to meet the demands of managing all these apps with anything close to best practices without a better model.
Containers are a whole new ballgame. Unlike VMs, you skip the overhead of running an entire OS for every application environment. There’s also no need to provision a whole new machine to have a place to deploy, meaning you can spin up or scale your application with orders of magnitude more speed and accuracy.
Containerization & Docker - Under the Hood

This presentation looks deep into the concept of containerization. What is containerization, how is it different from VMs, how containerization is achieved using Linux containers (LXC), control groups (cgroups) and copy on write file systems and current trends in containerization/docker are described.
Containers and Namespaces in the Linux Kernel

Containers and Namespaces in the Linux Kernel, Kir Kolyshkin
XPDS14 - OSv - A Modern Semi-POSIX LibraryOS - Glauber Costa, Cloudius Systems

During last year, we have seen the rise of LibraryOSes in the hypervisor world. Fast, scalable and light, they bring to hypervisors the resource efficiency of Containers while maintaining many of its well known isolation and manageability advantages.
While most LibraryOSes are niche in what they do, OSv is designed to run almost any POSIX compliant application and just have a slight focus in the Java application. Which applications can we run? And why? What's the story with Java and what can users gain from it? And more importantly: How can Xen users and the Xen community at large benefit from OSv? Those are some of the questions that I intend to cover in this presentation.
Similar to Openvz booth (20)
Oscon 2012 : From Datacenter to the Cloud - Featuring Xen and XCP

Oscon 2012 : From Datacenter to the Cloud - Featuring Xen and XCP
Fedora Virtualization Day: Linux Containers & CRIU

Fedora Virtualization Day: Linux Containers & CRIU
Testing kubernetes and_open_shift_at_scale_20170209

Testing kubernetes and_open_shift_at_scale_20170209
Let's Try Every CRI Runtime Available for Kubernetes

Let's Try Every CRI Runtime Available for Kubernetes
Containers: from development to production at DevNation 2015

Containers: from development to production at DevNation 2015
XPDS14 - OSv - A Modern Semi-POSIX LibraryOS - Glauber Costa, Cloudius Systems

XPDS14 - OSv - A Modern Semi-POSIX LibraryOS - Glauber Costa, Cloudius Systems
More from OpenVZ
Live migrating a container: pros, cons and gotchas -- Pavel Emelyanov

Live migrating a container: pros, cons and gotchas
Monday, November 16 • 17:20 - 18:05
Pavel Emelyanov
Principal Engineer, Odin
Principal engineer at Odin Server Virtualization team, creator and maintainer of the CRIU project. Joined Parallels in 2004 as junior Linux kernel developer, later became kernel team leader. Now works on architecture of the Odin Server products. | | Pavel tweets at @xemulp.
http://dockerconeu2015.sched.org/event/62e6d2ea7380442a48fafaeee26c9842
CRIU: time and space travel for Linux containers -- Kir Kolyshkin

CRIU: time and space travel for Linux containers
Kirill Kolyshkin, ContainerDays NYC, 30 Oct 2015
http://www.youtube.com/watch?v=0y7a3_Nn2hI
Тестирование ПО, основанного на сторонних компонентах - Денис Силаков, SECR 2015

В своей презентации мы на примере дистрибутива Linux расскажем об опыте организации процесса тестирования продукта, существенная часть (более 90%) кода которого создается независимыми от компании разработчиками.
https://www.youtube.com/watch?v=AstgrnE7_dI
Живая миграция: плюсы, минусы и подводные камни - Павел Емельянов

Двенадцатая конференция разработчиков свободных программ #OSDEVCONF 2015
http://www.altlinux.ru/news/archive/2015/08/item/743/
What's missing from upstream kernel containers? - Sergey Bronnikov

Двенадцатая конференция разработчиков свободных программ #OSDEVCONF 2015
http://www.altlinux.ru/news/archive/2015/08/item/743/
Проблема фрагментации виртуальных дисков и способы её решения -- Дмитрий Монахов

Проблема фрагментации виртуальных дисков и способы её решения Дмитрий Монахов
https://events.yandex.ru/events/yagosti/19-september-2015-linux/
Развёртывание приложений Docker в контейнерах Virtuozzo -- Павел Тихомиров

Развёртывание приложений Docker в контейнерах Virtuozzo
Павел Тихомиров
https://events.yandex.ru/events/yagosti/19-september-2015-linux/
CRIU: ускорение запуска PHP в CloudLinux OS -- Руслан Купреев

CRIU: ускорение запуска PHP в CloudLinux OS -- Руслан Купреев
https://events.yandex.ru/events/yagosti/19-september-2015-linux/
LibCT и контейнеры на уровне приложений -- Александр Бурлука

LibCT и контейнеры на уровне приложений -- Александр Бурлука
https://events.yandex.ru/events/yagosti/19-september-2015-linux/
Управление памятью контейнеров в проекте OpenVZ -- Владимир Давыдов

Управление памятью контейнеров в проекте OpenVZ
Владимир Давыдов
https://events.yandex.ru/events/yagosti/19-september-2015-linux/
Живая миграция контейнеров: плюсы, минусы, подводные камни -- Павел Емельянов

Живая миграция контейнеров: плюсы, минусы, подводные камни -- Павел Емельянов
https://events.yandex.ru/events/yagosti/19-september-2015-linux/
LibCT: one lib to rule them all -- Andrey Vagin

LibCT: one lib to rule them all -- Andrey Vagin
LinuxCon 2015, Seattle
Denser containers with PF cache - Pavel Emelyanov

Denser containers with PF cache - Pavel Emelyanov
LinuxCon 2015
CGroups kernel memory controller -- Pavel Emelyanov

CGroups kernel memory controller -- Pavel Emelyanov
Linux Plumbers 2015, Containers MC
Notes - https://etherpad.openstack.org/p/LPC2015_Containers
What's missing from upstream kernel containers? - Kir Kolyshkin, Sergey Bronn...

What's missing from upstream kernel containers? - Kir Kolyshkin, Linux Plumbers 2015
Not so brief history of Linux Containers - Kir Kolyshkin

Not so brief history of Linux Containers - Kir Kolyshkin, ContainerCon 2015
https://openvz.org/
Управление ресурсами в Linux и OpenVZ 

Управление ресурсами в Linux и OpenVZ Кирилл Колышкин kir@openvz.org http://openvz.org/
Отчет - http://yourcmc.ru/wiki/RootConf_2009:_%D0%9E%D1%82%D1%87%D1%91%D1%82_%D0%92%D0%B8%D1%82%D0%B0%D0%BB%D0%B8%D1%8F_%D0%A4%D0%B8%D0%BB%D0%B8%D0%BF%D0%BF%D0%BE%D0%B2%D0%B0#.D0.A3.D0.BF.D1.80.D0.B0.D0.B2.D0.BB.D0.B5.D0.BD.D0.B8.D0.B5_.D1.80.D0.B5.D1.81.D1.83.D1.80.D1.81.D0.B0.D0.BC.D0.B8_.D0.B2_Linux_.D0.B8_OpenVZ_.28.D0.B7.D0.B0.D1.87.D1.91.D1.82.21.29
More from OpenVZ (20)
Live migration: pros, cons and gotchas -- Pavel Emelyanov

Live migration: pros, cons and gotchas -- Pavel Emelyanov
Live migrating a container: pros, cons and gotchas -- Pavel Emelyanov

Live migrating a container: pros, cons and gotchas -- Pavel Emelyanov
CRIU: time and space travel for Linux containers -- Kir Kolyshkin

CRIU: time and space travel for Linux containers -- Kir Kolyshkin
Тестирование ПО, основанного на сторонних компонентах - Денис Силаков, SECR 2015

Тестирование ПО, основанного на сторонних компонентах - Денис Силаков, SECR 2015
Живая миграция: плюсы, минусы и подводные камни - Павел Емельянов

Живая миграция: плюсы, минусы и подводные камни - Павел Емельянов
What's missing from upstream kernel containers? - Sergey Bronnikov

What's missing from upstream kernel containers? - Sergey Bronnikov
Проблема фрагментации виртуальных дисков и способы её решения -- Дмитрий Монахов

Проблема фрагментации виртуальных дисков и способы её решения -- Дмитрий Монахов
Развёртывание приложений Docker в контейнерах Virtuozzo -- Павел Тихомиров

Развёртывание приложений Docker в контейнерах Virtuozzo -- Павел Тихомиров
CRIU: ускорение запуска PHP в CloudLinux OS -- Руслан Купреев

CRIU: ускорение запуска PHP в CloudLinux OS -- Руслан Купреев
LibCT и контейнеры на уровне приложений -- Александр Бурлука

LibCT и контейнеры на уровне приложений -- Александр Бурлука
Управление памятью контейнеров в проекте OpenVZ -- Владимир Давыдов

Управление памятью контейнеров в проекте OpenVZ -- Владимир Давыдов
Живая миграция контейнеров: плюсы, минусы, подводные камни -- Павел Емельянов

Живая миграция контейнеров: плюсы, минусы, подводные камни -- Павел Емельянов
CGroups kernel memory controller -- Pavel Emelyanov

CGroups kernel memory controller -- Pavel Emelyanov
What's missing from upstream kernel containers? - Kir Kolyshkin, Sergey Bronn...

What's missing from upstream kernel containers? - Kir Kolyshkin, Sergey Bronn...
Not so brief history of Linux Containers - Kir Kolyshkin

Not so brief history of Linux Containers - Kir Kolyshkin
Recently uploaded
SOCRadar Research Team: Latest Activities of IntelBroker

The European Union Agency for Law Enforcement Cooperation (Europol) has suffered an alleged data breach after a notorious threat actor claimed to have exfiltrated data from its systems. Infamous data leaker IntelBroker posted on the even more infamous BreachForums hacking forum, saying that Europol suffered a data breach this month.
The alleged breach affected Europol agencies CCSE, EC3, Europol Platform for Experts, Law Enforcement Forum, and SIRIUS. Infiltration of these entities can disrupt ongoing investigations and compromise sensitive intelligence shared among international law enforcement agencies.
However, this is neither the first nor the last activity of IntekBroker. We have compiled for you what happened in the last few days. To track such hacker activities on dark web sources like hacker forums, private Telegram channels, and other hidden platforms where cyber threats often originate, you can check SOCRadar’s Dark Web News.
Stay Informed on Threat Actors’ Activity on the Dark Web with SOCRadar!
Quarkus Hidden and Forbidden Extensions

Quarkus has a vast extension ecosystem and is known for its subsonic and subatomic feature set. Some of these features are not as well known, and some extensions are less talked about, but that does not make them less interesting - quite the opposite.
Come join this talk to see some tips and tricks for using Quarkus and some of the lesser known features, extensions and development techniques.
Understanding Globus Data Transfers with NetSage

NetSage is an open privacy-aware network measurement, analysis, and visualization service designed to help end-users visualize and reason about large data transfers. NetSage traditionally has used a combination of passive measurements, including SNMP and flow data, as well as active measurements, mainly perfSONAR, to provide longitudinal network performance data visualization. It has been deployed by dozens of networks world wide, and is supported domestically by the Engagement and Performance Operations Center (EPOC), NSF #2328479. We have recently expanded the NetSage data sources to include logs for Globus data transfers, following the same privacy-preserving approach as for Flow data. Using the logs for the Texas Advanced Computing Center (TACC) as an example, this talk will walk through several different example use cases that NetSage can answer, including: Who is using Globus to share data with my institution, and what kind of performance are they able to achieve? How many transfers has Globus supported for us? Which sites are we sharing the most data with, and how is that changing over time? How is my site using Globus to move data internally, and what kind of performance do we see for those transfers? What percentage of data transfers at my institution used Globus, and how did the overall data transfer performance compare to the Globus users?
Exploring Innovations in Data Repository Solutions - Insights from the U.S. G...

The U.S. Geological Survey (USGS) has made substantial investments in meeting evolving scientific, technical, and policy driven demands on storing, managing, and delivering data. As these demands continue to grow in complexity and scale, the USGS must continue to explore innovative solutions to improve its management, curation, sharing, delivering, and preservation approaches for large-scale research data. Supporting these needs, the USGS has partnered with the University of Chicago-Globus to research and develop advanced repository components and workflows leveraging its current investment in Globus. The primary outcome of this partnership includes the development of a prototype enterprise repository, driven by USGS Data Release requirements, through exploration and implementation of the entire suite of the Globus platform offerings, including Globus Flow, Globus Auth, Globus Transfer, and Globus Search. This presentation will provide insights into this research partnership, introduce the unique requirements and challenges being addressed and provide relevant project progress.
Accelerate Enterprise Software Engineering with Platformless

Key takeaways:
Challenges of building platforms and the benefits of platformless.
Key principles of platformless, including API-first, cloud-native middleware, platform engineering, and developer experience.
How Choreo enables the platformless experience.
How key concepts like application architecture, domain-driven design, zero trust, and cell-based architecture are inherently a part of Choreo.
Demo of an end-to-end app built and deployed on Choreo.
Globus Compute Introduction - GlobusWorld 2024

We describe the deployment and use of Globus Compute for remote computation. This content is aimed at researchers who wish to compute on remote resources using a unified programming interface, as well as system administrators who will deploy and operate Globus Compute services on their research computing infrastructure.
Field Employee Tracking System| MiTrack App| Best Employee Tracking Solution|...

Field Employee Tracking System| MiTrack App| Best Employee Tracking Solution|...informapgpstrackings
Keep tabs on your field staff effortlessly with Informap Technology Centre LLC. Real-time tracking, task assignment, and smart features for efficient management. Request a live demo today!
For more details, visit us : https://informapuae.com/field-staff-tracking/Gamify Your Mind; The Secret Sauce to Delivering Success, Continuously Improv...

Games are powerful teaching tools, fostering hands-on engagement and fun. But they require careful consideration to succeed. Join me to explore factors in running and selecting games, ensuring they serve as effective teaching tools. Learn to maintain focus on learning objectives while playing, and how to measure the ROI of gaming in education. Discover strategies for pitching gaming to leadership. This session offers insights, tips, and examples for coaches, team leads, and enterprise leaders seeking to teach from simple to complex concepts.
GlobusWorld 2024 Opening Keynote session

Listen to the keynote address and hear about the latest developments from Rachana Ananthakrishnan and Ian Foster who review the updates to the Globus Platform and Service, and the relevance of Globus to the scientific community as an automation platform to accelerate scientific discovery.
Cracking the code review at SpringIO 2024

Code reviews are vital for ensuring good code quality. They serve as one of our last lines of defense against bugs and subpar code reaching production.
Yet, they often turn into annoying tasks riddled with frustration, hostility, unclear feedback and lack of standards. How can we improve this crucial process?
In this session we will cover:
- The Art of Effective Code Reviews
- Streamlining the Review Process
- Elevating Reviews with Automated Tools
By the end of this presentation, you'll have the knowledge on how to organize and improve your code review proces
Globus Connect Server Deep Dive - GlobusWorld 2024

We explore the Globus Connect Server (GCS) architecture and experiment with advanced configuration options and use cases. This content is targeted at system administrators who are familiar with GCS and currently operate—or are planning to operate—broader deployments at their institution.
Into the Box 2024 - Keynote Day 2 Slides.pdf

Into the Box Keynote Day 2: Unveiling amazing updates and announcements for modern CFML developers! Get ready for exciting releases and updates on Ortus tools and products. Stay tuned for cutting-edge innovations designed to boost your productivity.
Large Language Models and the End of Programming

Talk by Matt Welsh at Craft Conference 2024 on the impact that Large Language Models will have on the future of software development. In this talk, I discuss the ways in which LLMs will impact the software industry, from replacing human software developers with AI, to replacing conventional software with models that perform reasoning, computation, and problem-solving.
Paketo Buildpacks : la meilleure façon de construire des images OCI? DevopsDa...

Les Buildpacks existent depuis plus de 10 ans ! D’abord, ils étaient utilisés pour détecter et construire une application avant de la déployer sur certains PaaS. Ensuite, nous avons pu créer des images Docker (OCI) avec leur dernière génération, les Cloud Native Buildpacks (CNCF en incubation). Sont-ils une bonne alternative au Dockerfile ? Que sont les buildpacks Paketo ? Quelles communautés les soutiennent et comment ?
Venez le découvrir lors de cette session ignite
Strategies for Successful Data Migration Tools.pptx

Data migration is a complex but essential task for organizations aiming to modernize their IT infrastructure and leverage new technologies. By understanding common challenges and implementing these strategies, businesses can achieve a successful migration with minimal disruption. Data Migration Tool like Ask On Data play a pivotal role in this journey, offering features that streamline the process, ensure data integrity, and maintain security. With the right approach and tools, organizations can turn the challenge of data migration into an opportunity for growth and innovation.
Cyaniclab : Software Development Agency Portfolio.pdf

CyanicLab, an offshore custom software development company based in Sweden,India, Finland, is your go-to partner for startup development and innovative web design solutions. Our expert team specializes in crafting cutting-edge software tailored to meet the unique needs of startups and established enterprises alike. From conceptualization to execution, we offer comprehensive services including web and mobile app development, UI/UX design, and ongoing software maintenance. Ready to elevate your business? Contact CyanicLab today and let us propel your vision to success with our top-notch IT solutions.
Designing for Privacy in Amazon Web Services

Data privacy is one of the most critical issues that businesses face. This presentation shares insights on the principles and best practices for ensuring the resilience and security of your workload.
Drawing on a real-life project from the HR industry, the various challenges will be demonstrated: data protection, self-healing, business continuity, security, and transparency of data processing. This systematized approach allowed to create a secure AWS cloud infrastructure that not only met strict compliance rules but also exceeded the client's expectations.
TROUBLESHOOTING 9 TYPES OF OUTOFMEMORYERROR

Even though at surface level ‘java.lang.OutOfMemoryError’ appears as one single error; underlyingly there are 9 types of OutOfMemoryError. Each type of OutOfMemoryError has different causes, diagnosis approaches and solutions. This session equips you with the knowledge, tools, and techniques needed to troubleshoot and conquer OutOfMemoryError in all its forms, ensuring smoother, more efficient Java applications.
Multiple Your Crypto Portfolio with the Innovative Features of Advanced Crypt...

Multiple Your Crypto Portfolio with the Innovative Features of Advanced Crypt...Hivelance Technology
Cryptocurrency trading bots are computer programs designed to automate buying, selling, and managing cryptocurrency transactions. These bots utilize advanced algorithms and machine learning techniques to analyze market data, identify trading opportunities, and execute trades on behalf of their users. By automating the decision-making process, crypto trading bots can react to market changes faster than human traders
Hivelance, a leading provider of cryptocurrency trading bot development services, stands out as the premier choice for crypto traders and developers. Hivelance boasts a team of seasoned cryptocurrency experts and software engineers who deeply understand the crypto market and the latest trends in automated trading, Hivelance leverages the latest technologies and tools in the industry, including advanced AI and machine learning algorithms, to create highly efficient and adaptable crypto trading botsFirst Steps with Globus Compute Multi-User Endpoints

In this presentation we will share our experiences around getting started with the Globus Compute multi-user endpoint. Working with the Pharmacology group at the University of Auckland, we have previously written an application using Globus Compute that can offload computationally expensive steps in the researcher's workflows, which they wish to manage from their familiar Windows environments, onto the NeSI (New Zealand eScience Infrastructure) cluster. Some of the challenges we have encountered were that each researcher had to set up and manage their own single-user globus compute endpoint and that the workloads had varying resource requirements (CPUs, memory and wall time) between different runs. We hope that the multi-user endpoint will help to address these challenges and share an update on our progress here.
Recently uploaded (20)
SOCRadar Research Team: Latest Activities of IntelBroker

SOCRadar Research Team: Latest Activities of IntelBroker
Exploring Innovations in Data Repository Solutions - Insights from the U.S. G...

Exploring Innovations in Data Repository Solutions - Insights from the U.S. G...
Accelerate Enterprise Software Engineering with Platformless

Accelerate Enterprise Software Engineering with Platformless
Field Employee Tracking System| MiTrack App| Best Employee Tracking Solution|...

Field Employee Tracking System| MiTrack App| Best Employee Tracking Solution|...
Gamify Your Mind; The Secret Sauce to Delivering Success, Continuously Improv...

Gamify Your Mind; The Secret Sauce to Delivering Success, Continuously Improv...
Globus Connect Server Deep Dive - GlobusWorld 2024

Globus Connect Server Deep Dive - GlobusWorld 2024
Paketo Buildpacks : la meilleure façon de construire des images OCI? DevopsDa...

Paketo Buildpacks : la meilleure façon de construire des images OCI? DevopsDa...
Strategies for Successful Data Migration Tools.pptx

Strategies for Successful Data Migration Tools.pptx
Cyaniclab : Software Development Agency Portfolio.pdf

Cyaniclab : Software Development Agency Portfolio.pdf
Multiple Your Crypto Portfolio with the Innovative Features of Advanced Crypt...

Multiple Your Crypto Portfolio with the Innovative Features of Advanced Crypt...
First Steps with Globus Compute Multi-User Endpoints

First Steps with Globus Compute Multi-User Endpoints
Openvz booth
- 1. VM vs Container Xen, KVM, VMware, etc. ● Hardware emulation / paravirtualization ● Can run different OSs on the same box ● Dozens of instances ● OS sprawl problem ● Lower performance ● Chroot on steroids ● Single OS per box ● Hundred of instances ● Dynamic resource management, best scalability ● Trivial performance overhead
- 2. OpenVZ vs. Xen comparison by HP labs ● “For all the configurations and workloads we have tested, Xen incurs higher virtualization overhead than OpenVZ does.” ● “For all the cases tested, the virtualization overhead observed in OpenVZ is low, and can be neglected in many scenarios.” ● “The two nodes running Xen become overloaded when hosting four instances of RUBiS, whereas those using OpenVZ can host at least six without being overloaded.” From http://www.hpl.hp.com/techreports/2007/HPL-2007-59R1.pdf
- 3. New Stuff ● RHEL6 kernel port ● VSwap: easy management, RSS reclamation ● Containers CPU binding (cpumask) ● PCI device delegation ● NFS mounts migration ● Journaled quota ● ext4 safe writeback
- 4. Future directions ● Mainstream kernel integration ● Container in a file a.k.a. PLOOP – Come to see our talk! ● CRIU: checkpoint/restore in userspace ● Caching de-duplicating FS (pfscache)
- 5. Mainstream kernel integration ● OpenVZ project pioneers container technology – Developing new container technology since 1999. Features then ported from OpenVZ to upstream Linux “containers”. ● Already upstream (in Linux containers): – IPC namespace, utsname() virtualization, PID namespace, user namespace, cgroups (control groups), Memory controllers (RSS, page cache), Network namespace... – Collaborative community effort: IBM, Google, SGI, Parallels, and many others. ● It's still ongoing – In progress: NFS virtualization, network buffer accounting, Checkpoint/restart in userspace – TODO: Kernel memory accounting, ...
- 6. CT #1CT #1 Migration at a Glance Physical Server #1 Physical Server #2 CT Private Data CT Memory CT#1 • Container's file system transfer • Save full container's state to a file • Container is running on Server #1 Full State Dump Full State Dump • Restart container on Server #2 CT #1 CT Memory CT Private Data
- 7. To sum it up ● Containers scale as well as Linux does – Benefit from all Linux performance improvements – Native I/O speed, best possible performance – The more memory/CPUs the merrier ● Platform-independent – as long as Linux supports it, we support it – arm/mips/ppc no problem. ● Plays well with others (Xen, KVM, VMware) – VM and container technologies are orthogonal – run containers and VMs side by side
Editor's Notes
- In case we need to move a container from one physical server to another, this can be done with the following simple procedure: stop a container, copy its file system to another server and start it there. This is known as cold or offline migration. With a container it is easy because a container is not tied to any particular hardware – it doesn't know what NIC or SCSI controller do you have. Still, cold migration is usually not very convenient since you need to plan a downtime. Fortunately, there is a solution. Since a container is an isolated object not tied to a particular hardware, a closed set it opens up a possibility to move it from one server to another without a restart. So, how do we move a container without service downtime? At a glance it can be described in a following way: 1. Container's file system transfer to another computer 2. Complete state of container (all the processes and their resources) is saved to a file. 3. The file is copied to another server. 4. The container is restarted on another server from the file.
