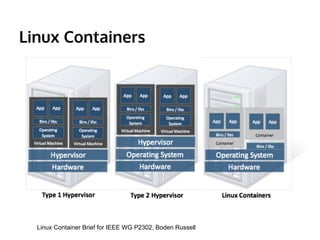
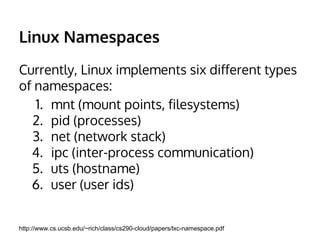
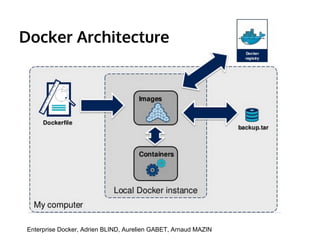
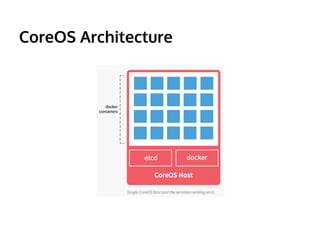
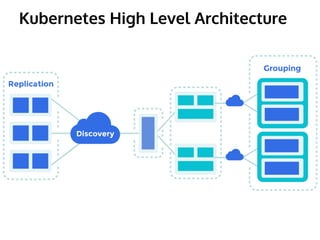
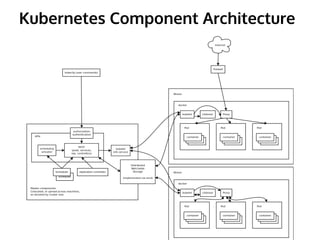
The document provides an overview of the evolution of Linux container virtualization, covering key concepts like virtualization, Linux containers, and associated technologies such as Docker, CoreOS, and Kubernetes. It elaborates on critical Linux kernel features including namespaces, cgroups, AppArmor, SELinux, seccomp, and chroot, which enable the creation and management of containers. Additionally, the document discusses the architecture and functionalities of Docker and Kubernetes in container management and deployment.