This document provides an overview of network naming protocols, including DNS and WINS. It describes:
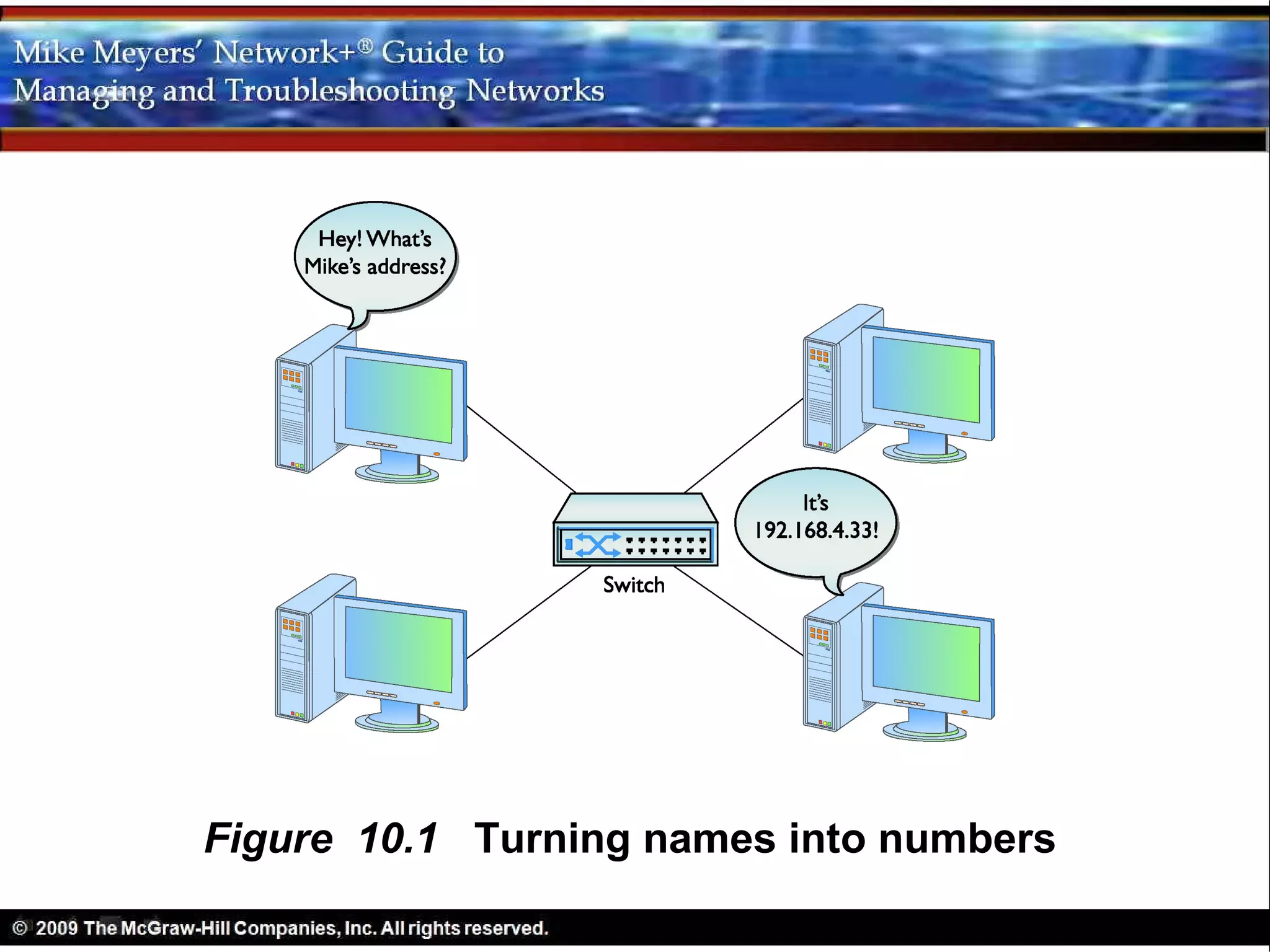
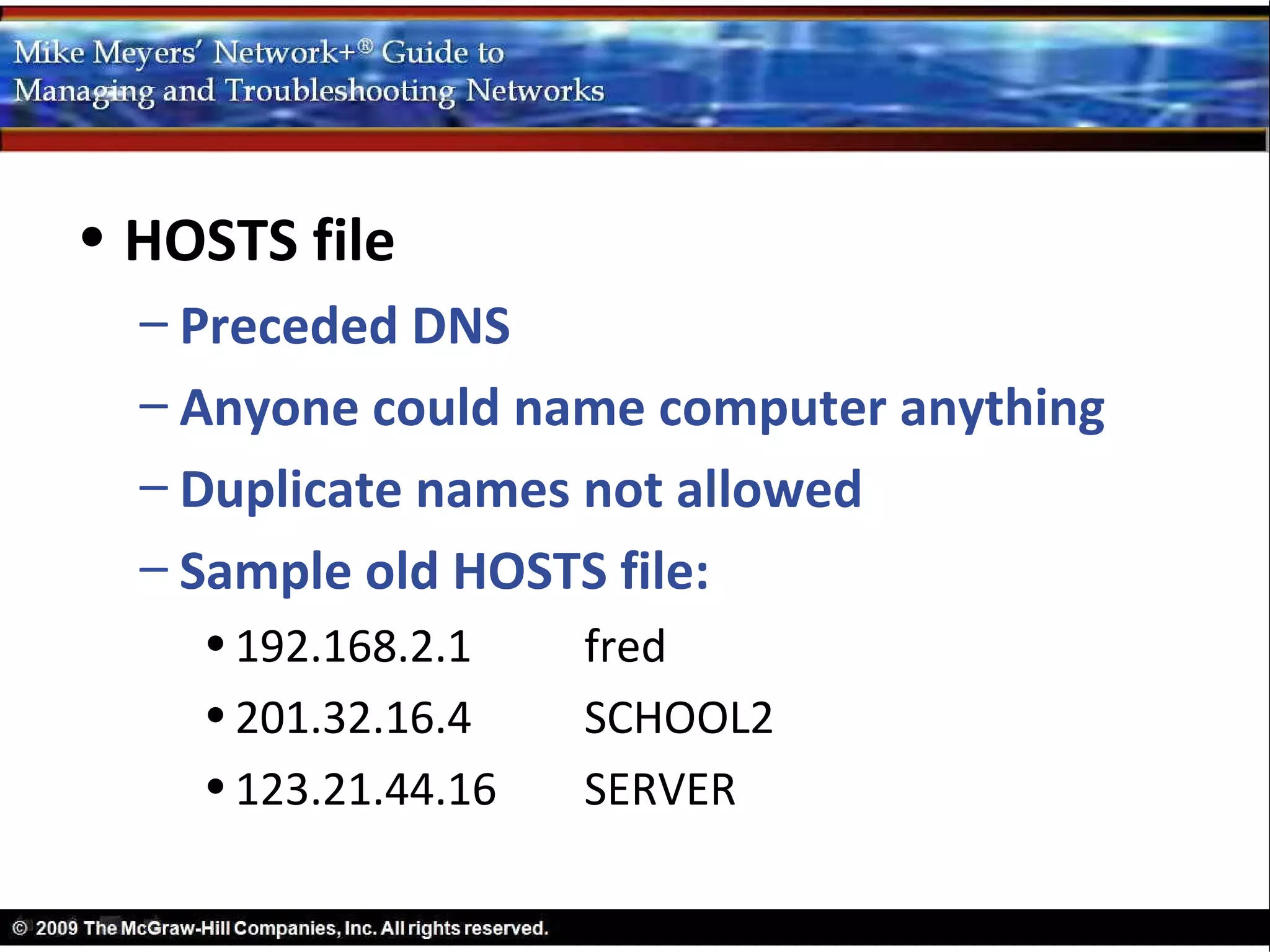
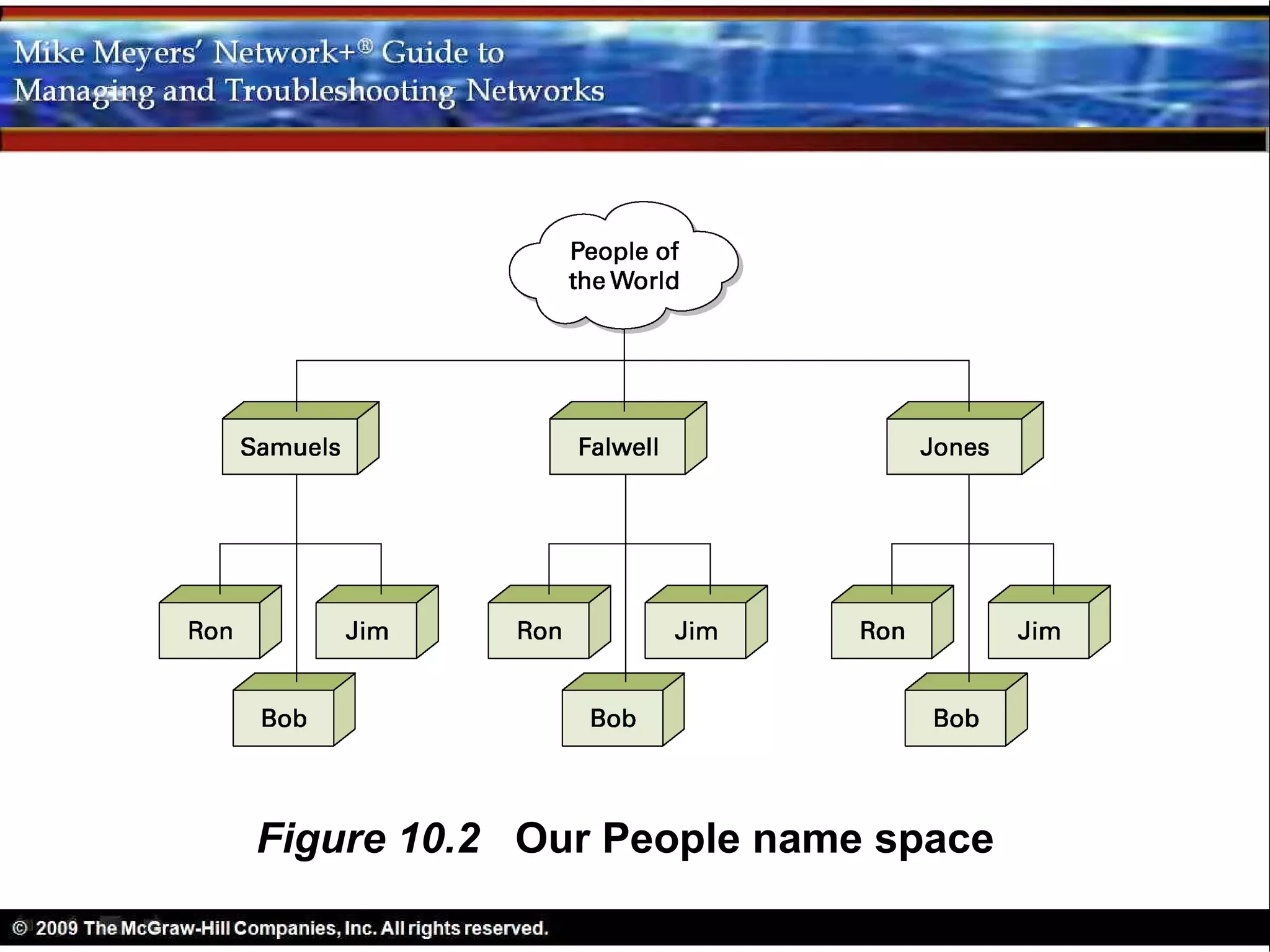
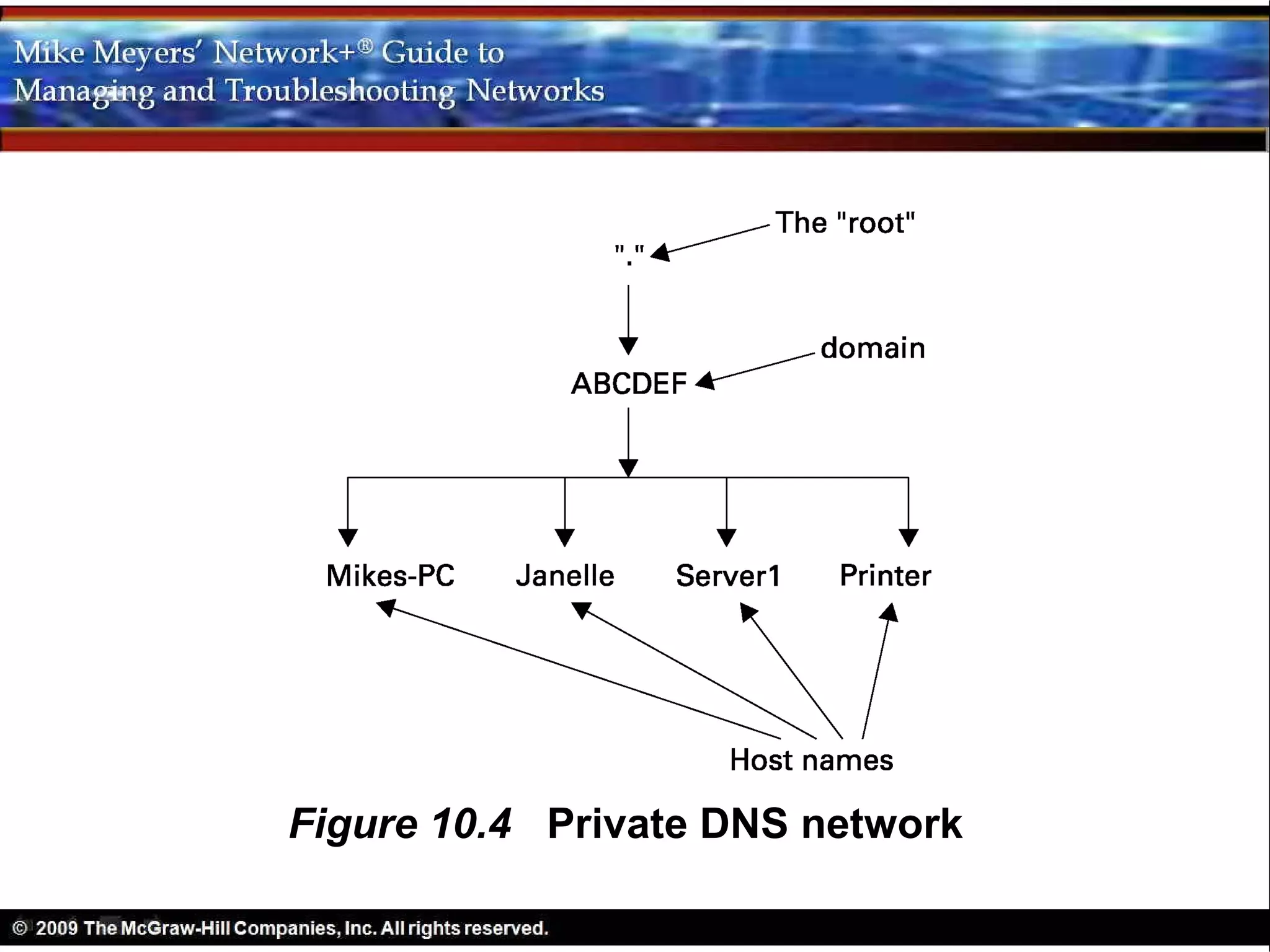
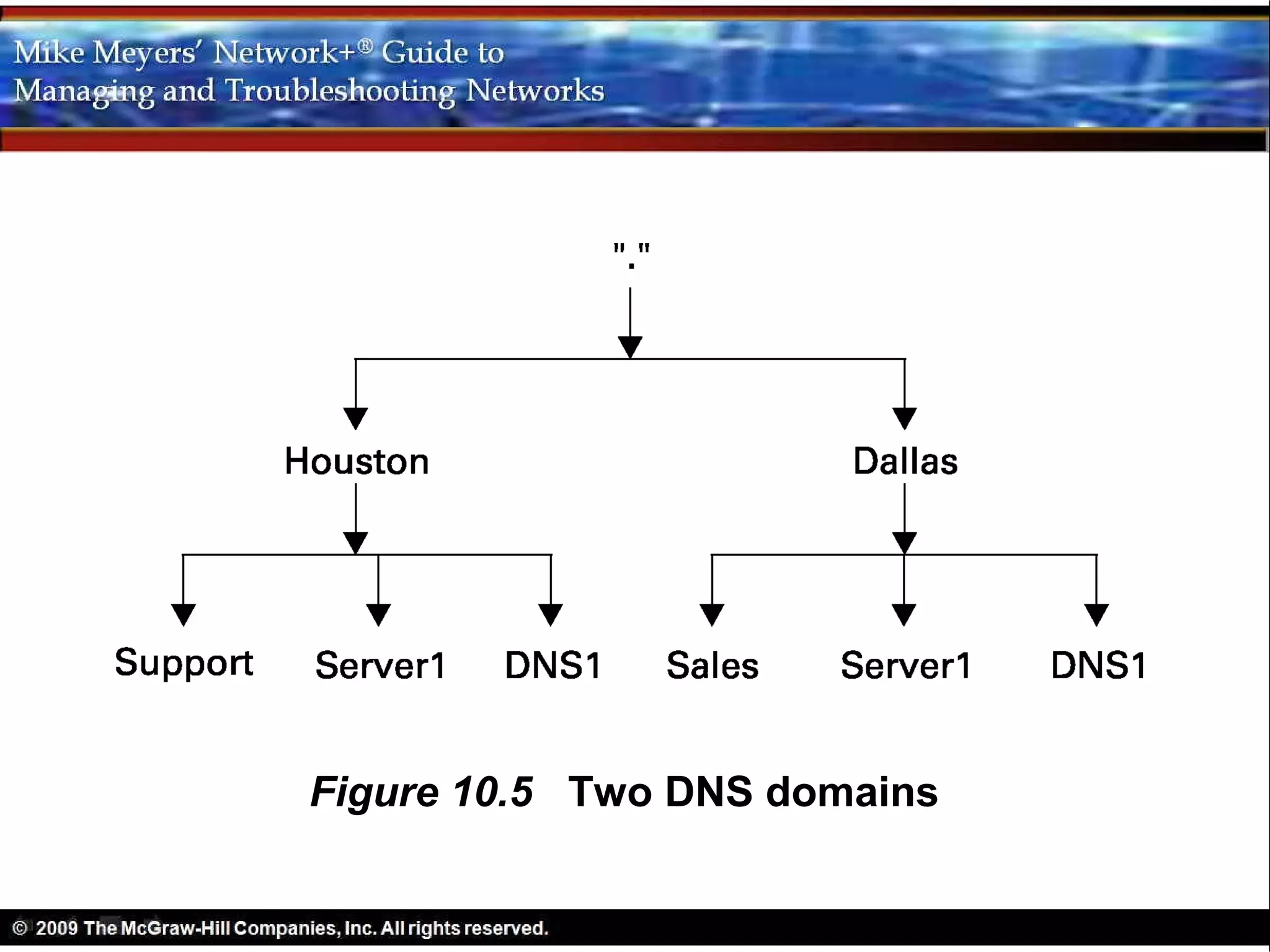
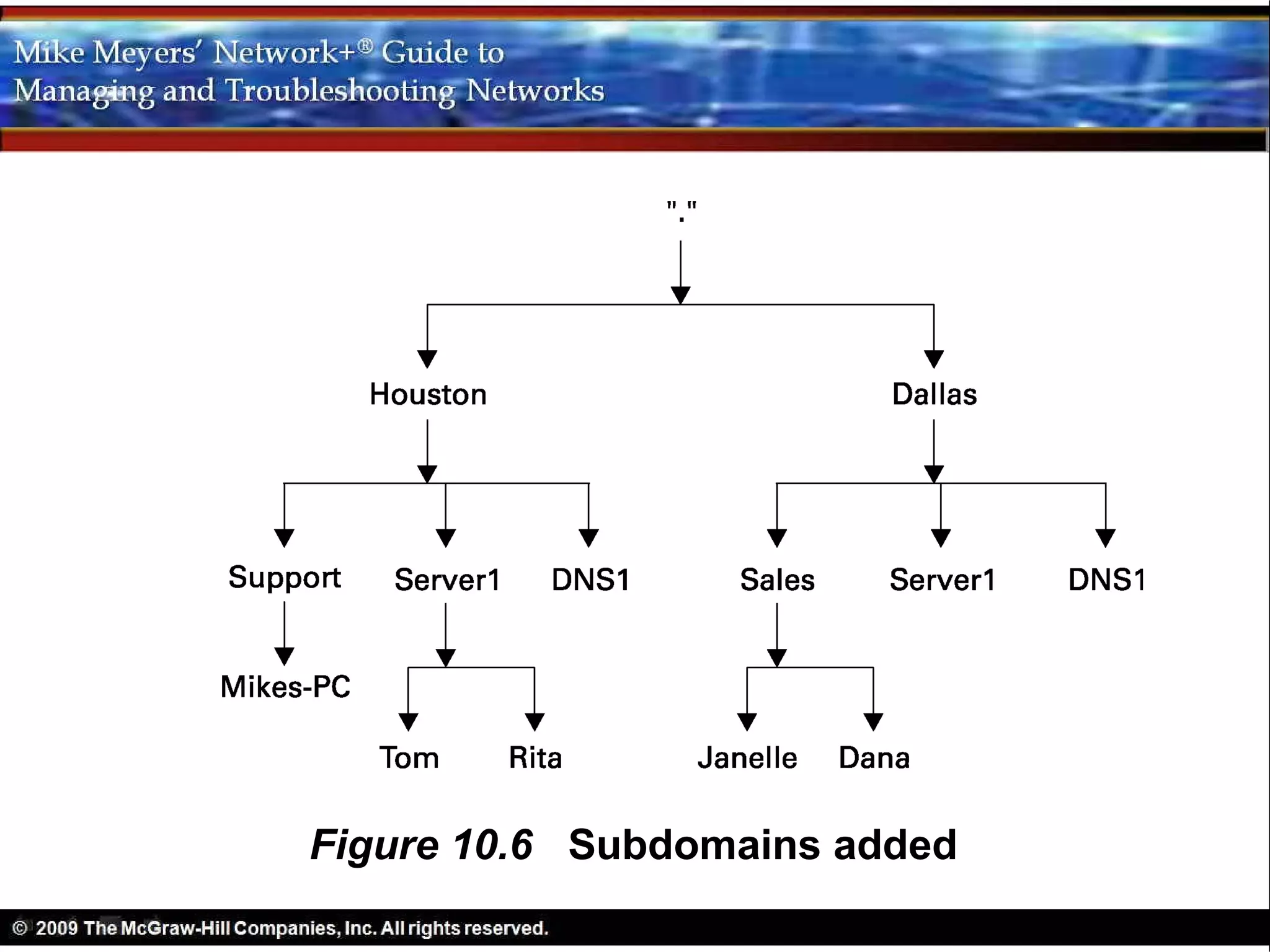
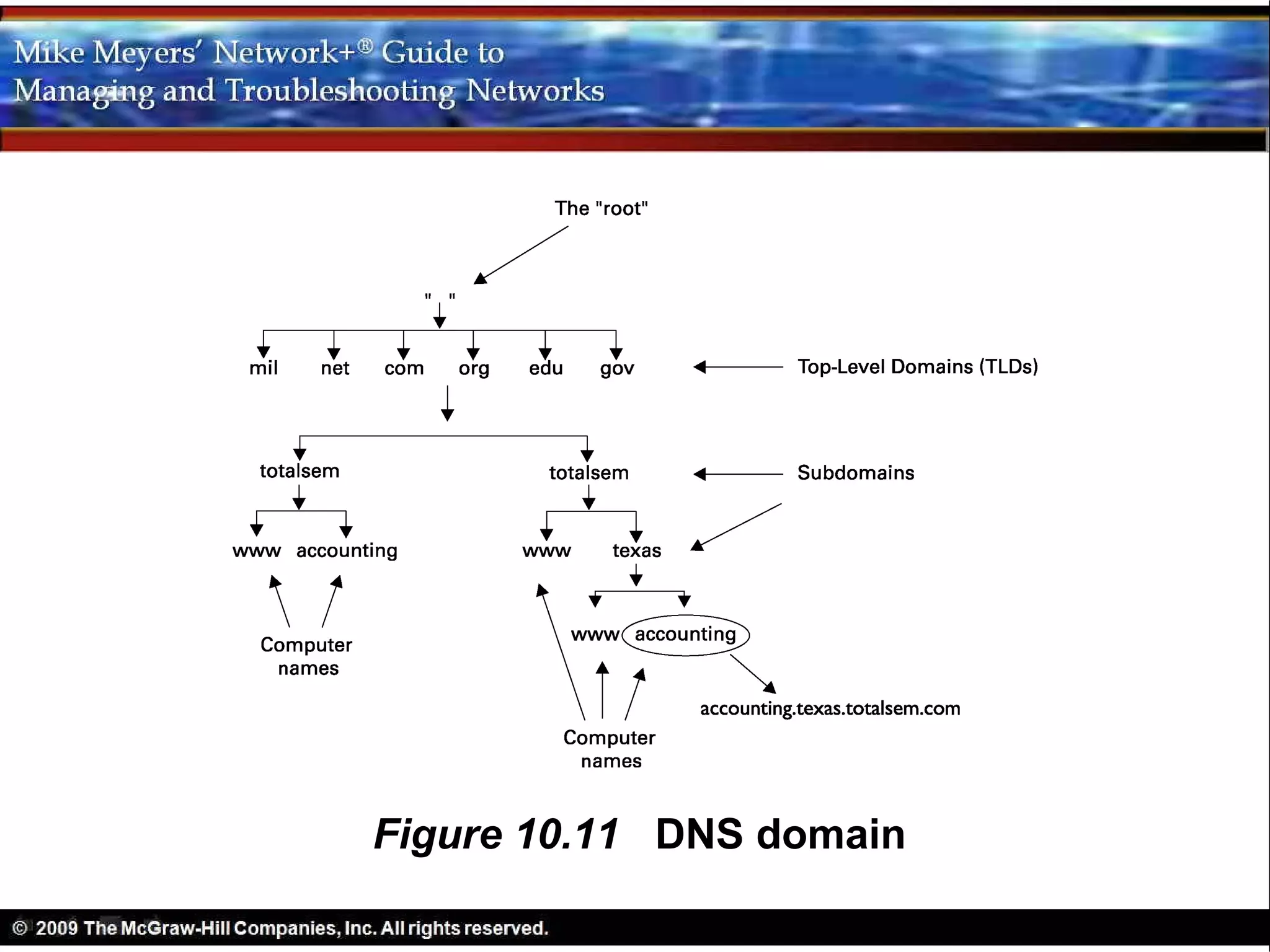
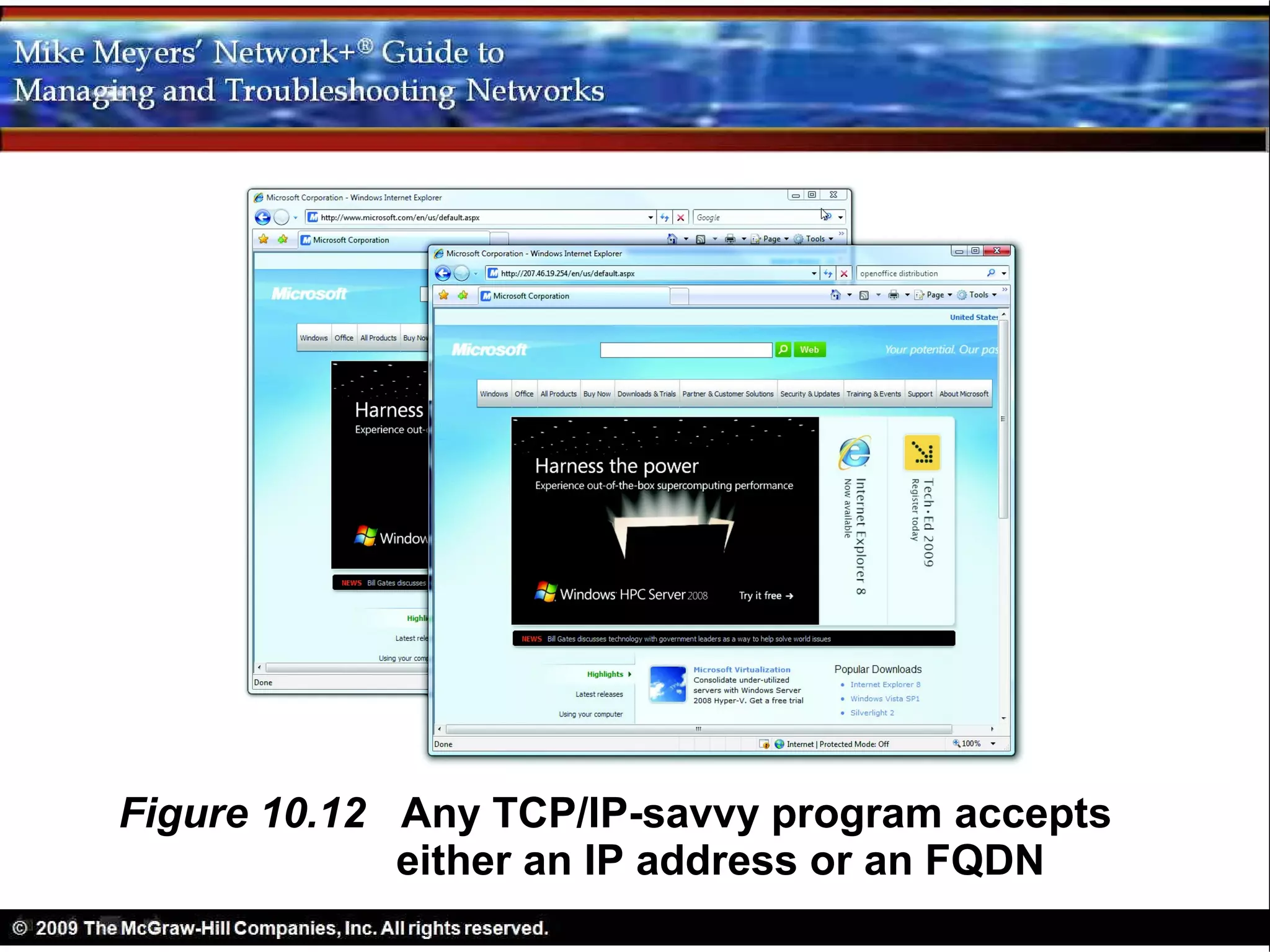
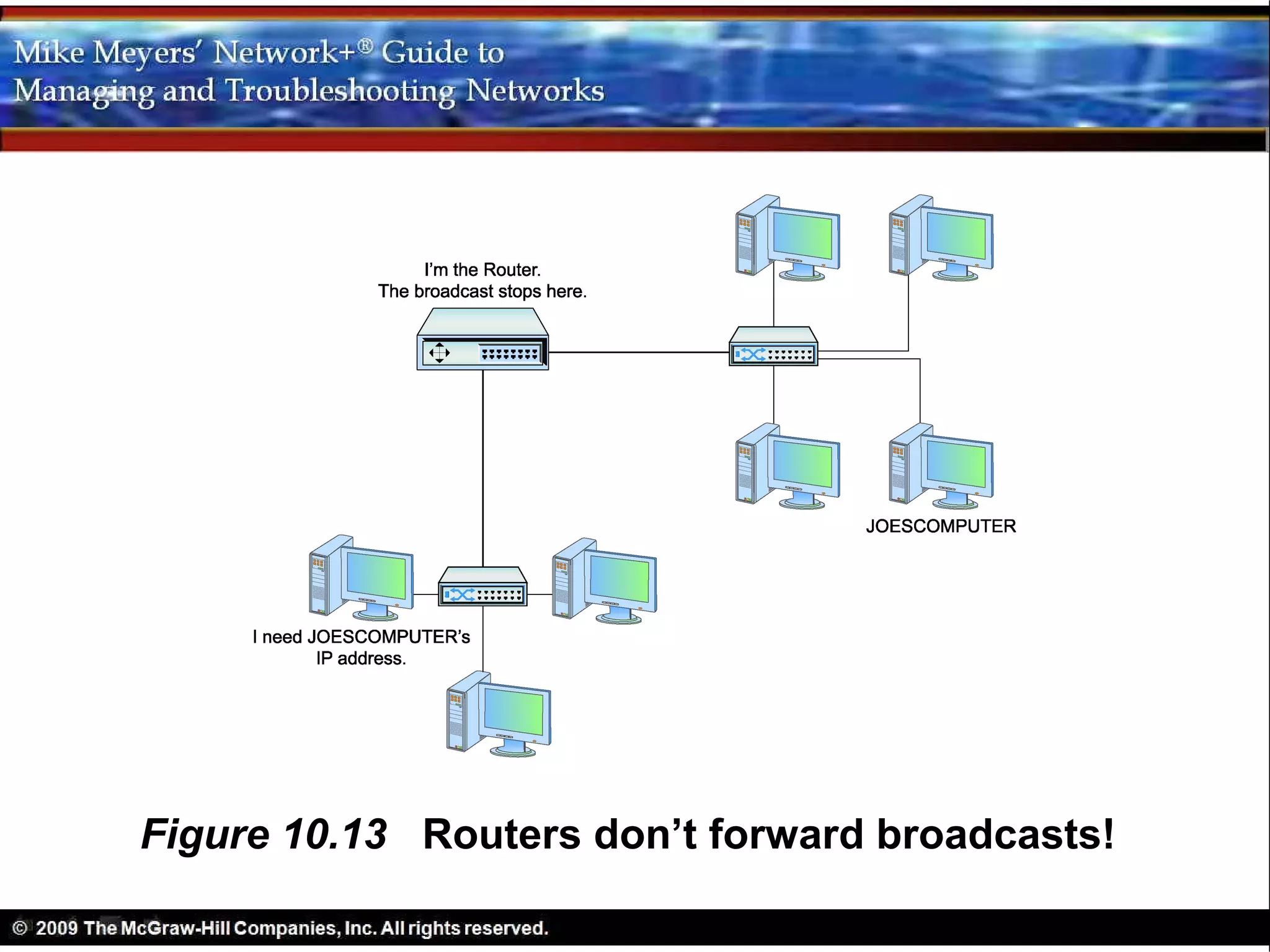
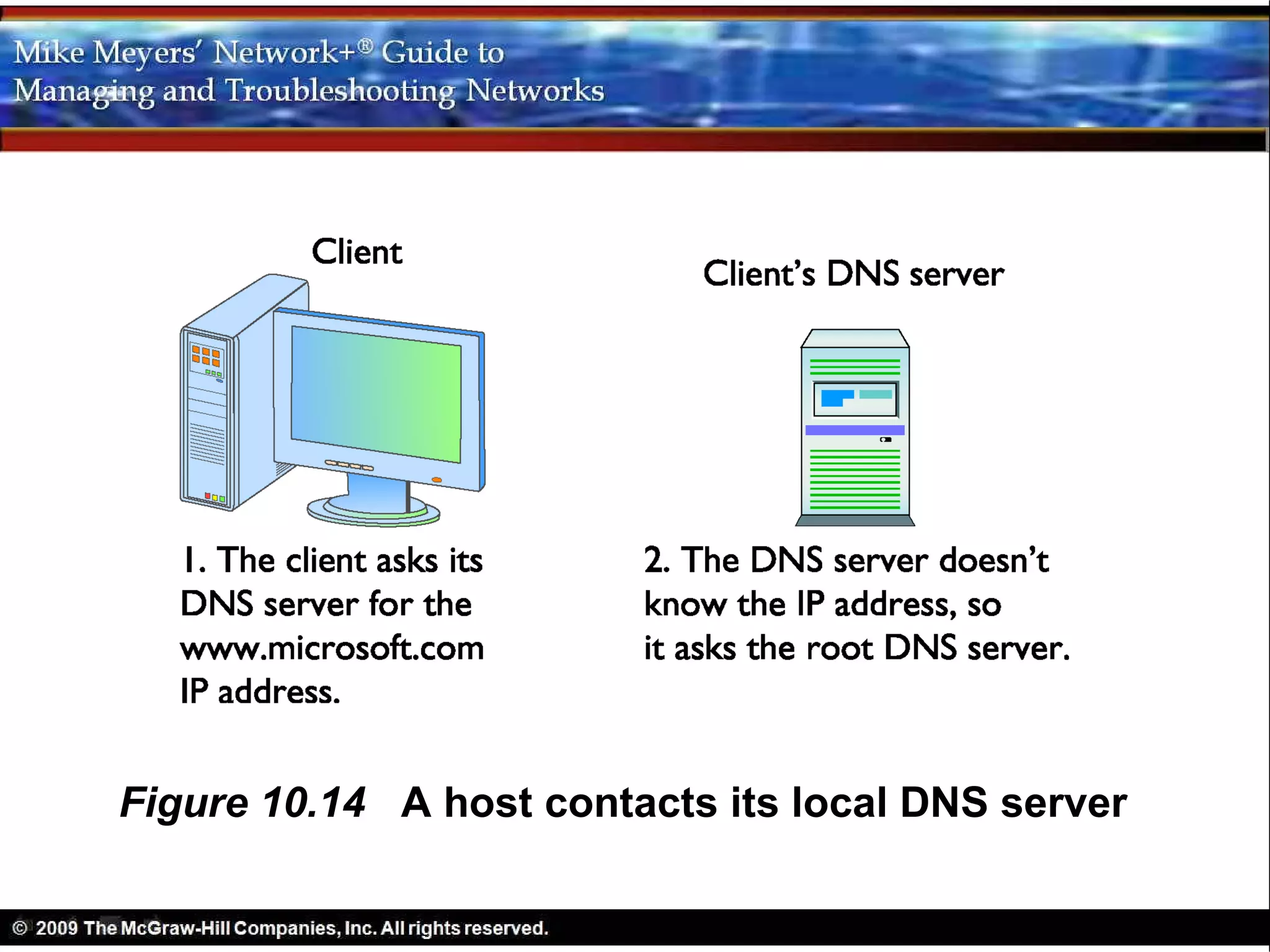
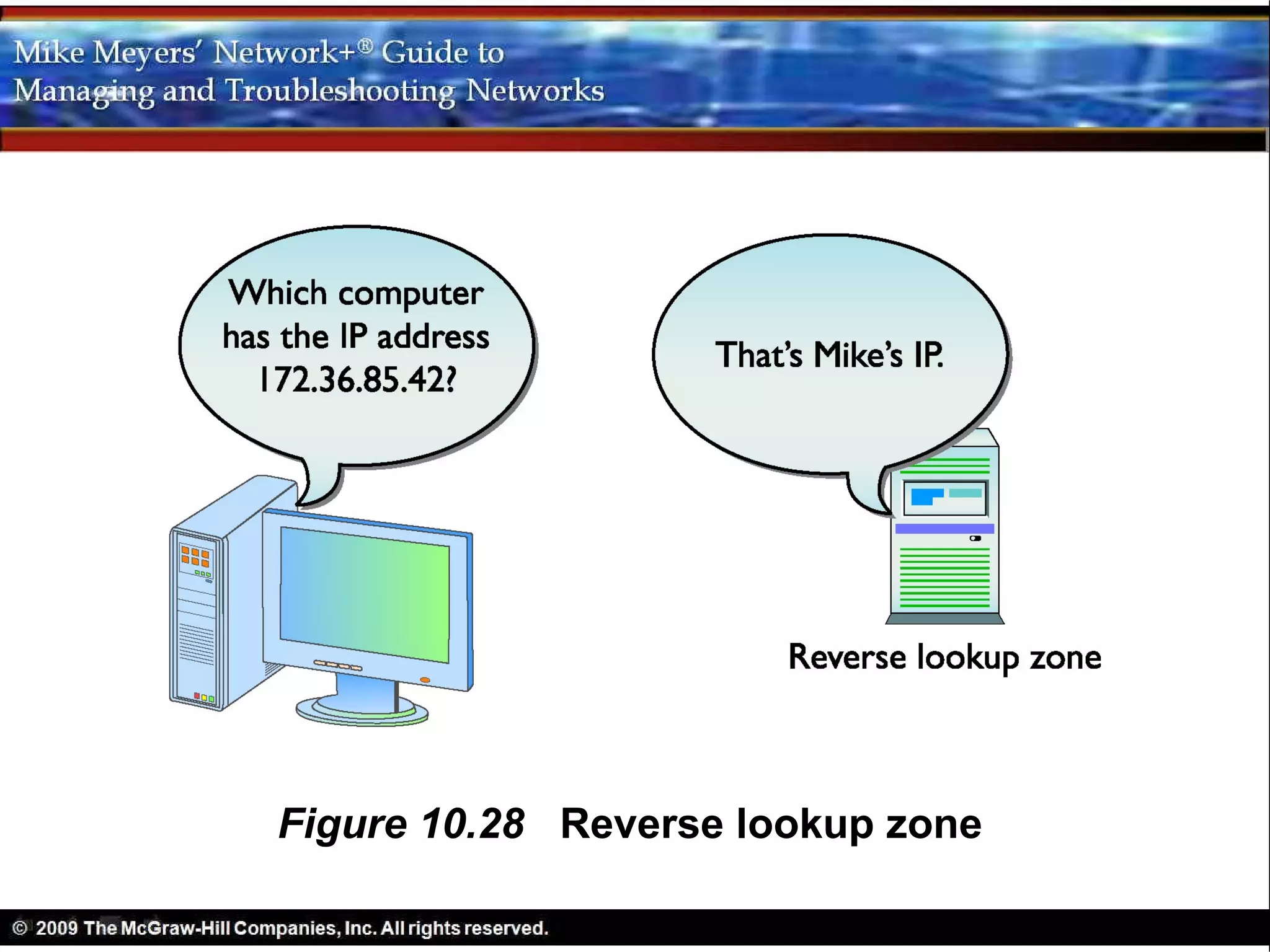
1) How DNS evolved from the HOSTS file to become the main name resolution protocol on the internet, allowing names to be converted to IP addresses and vice versa in a hierarchical naming structure.
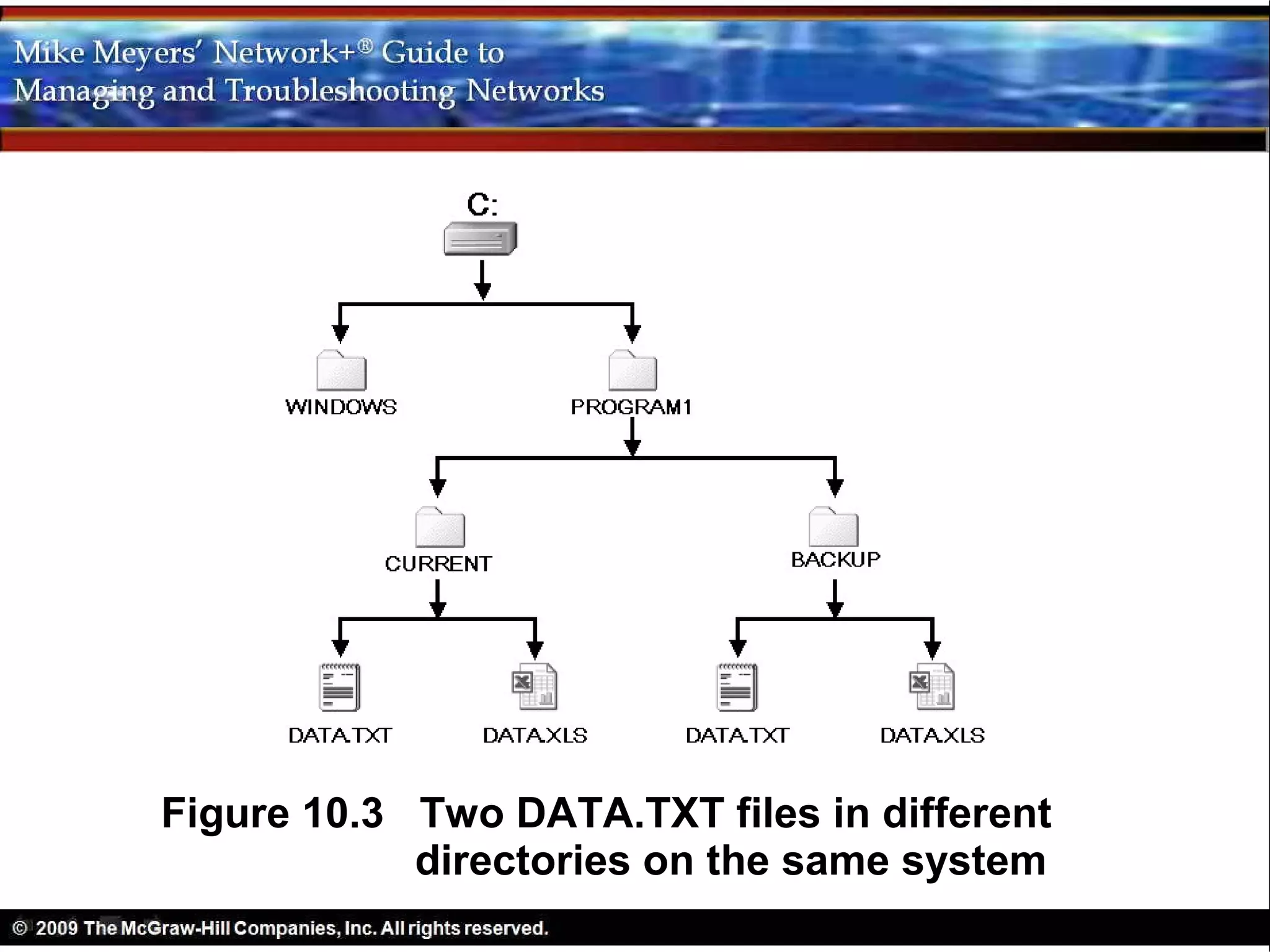
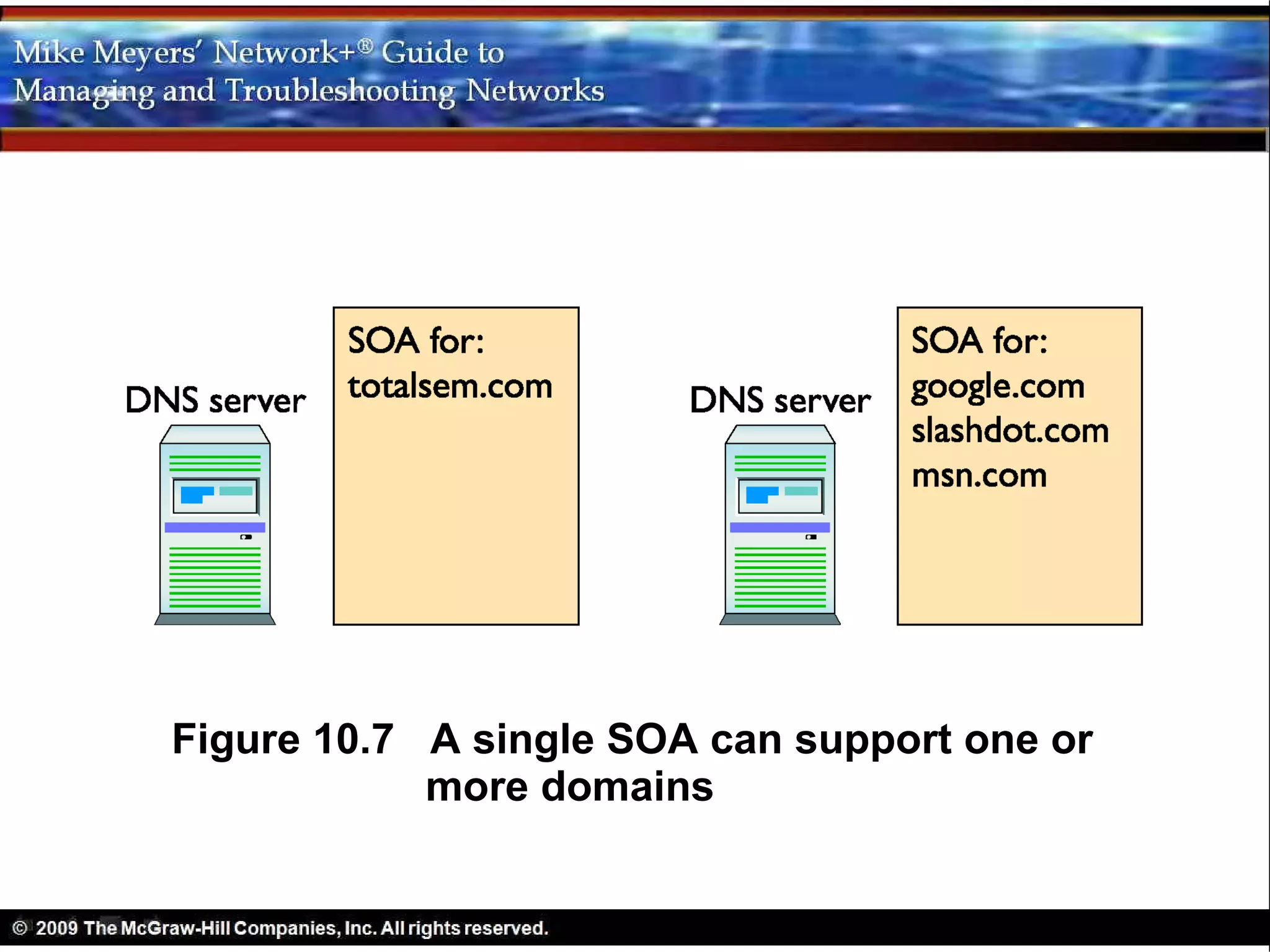
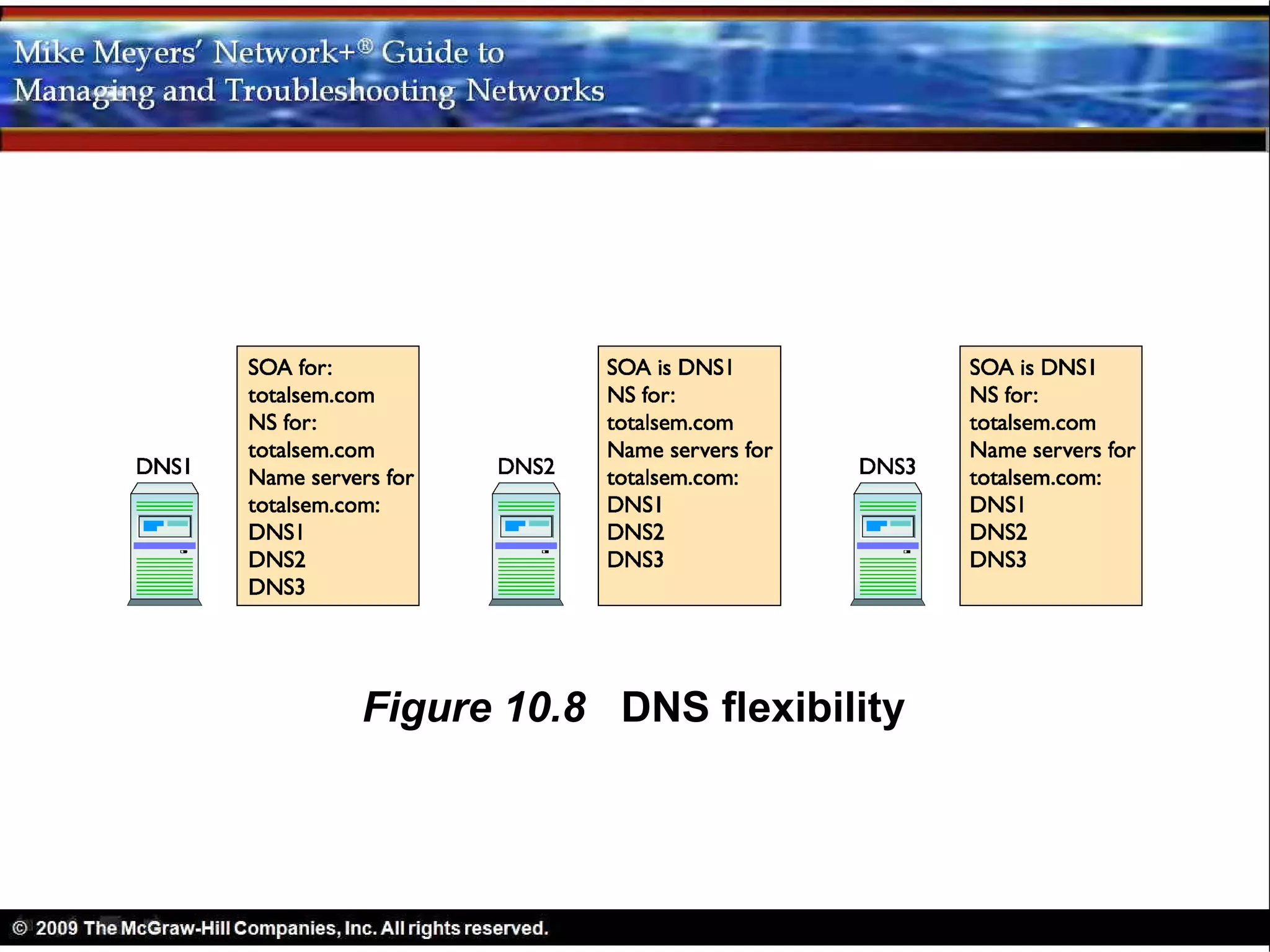
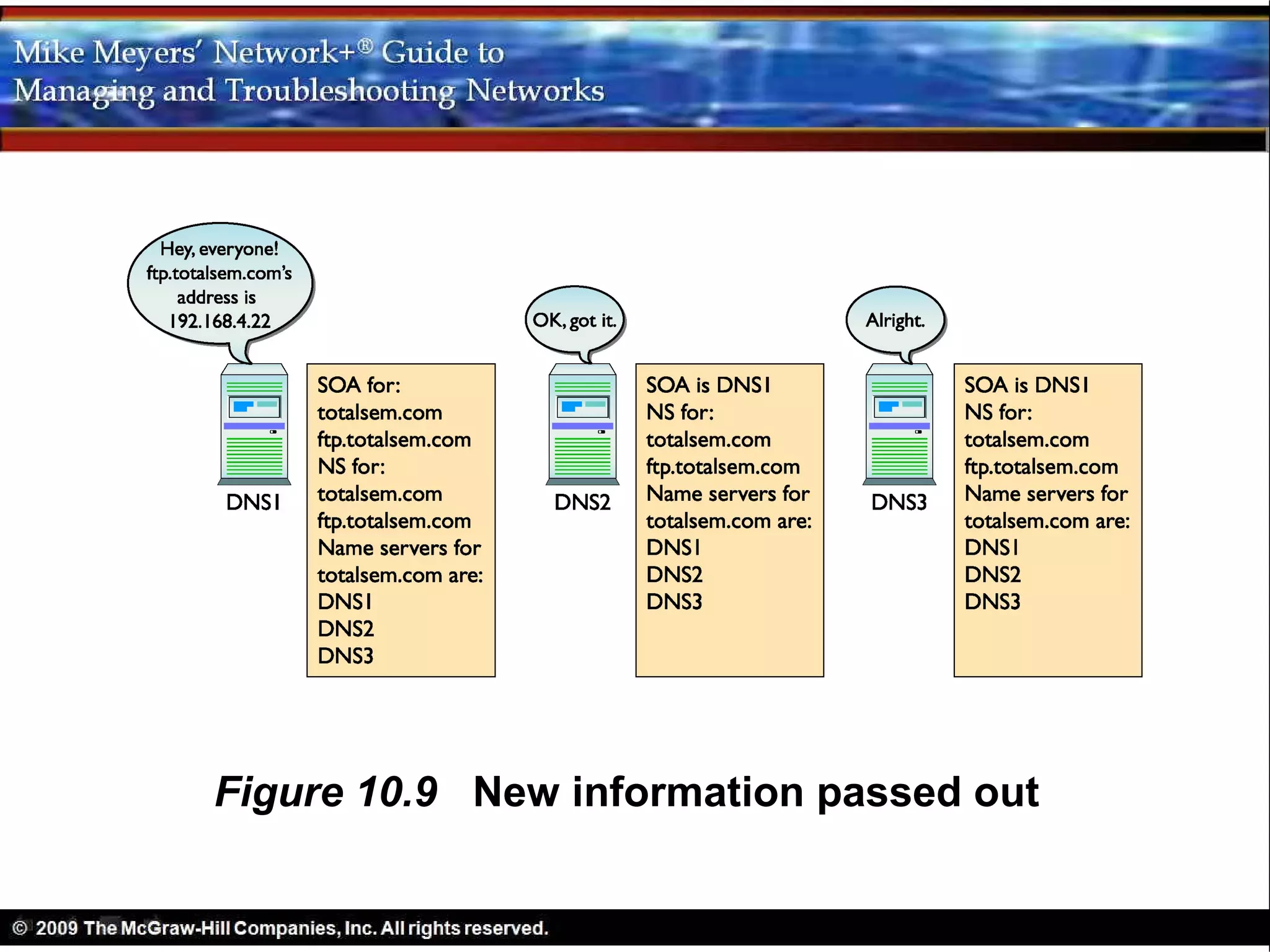
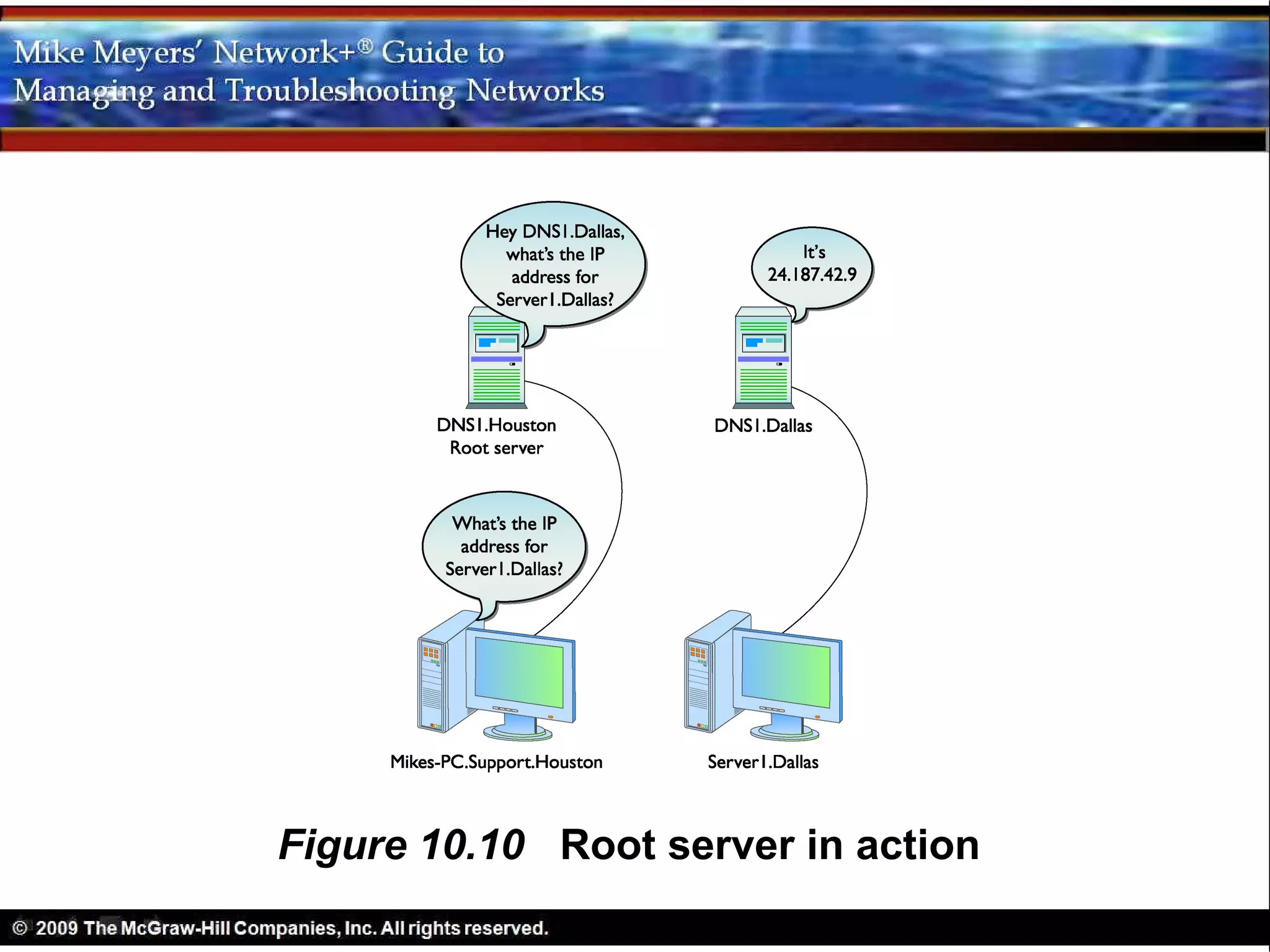
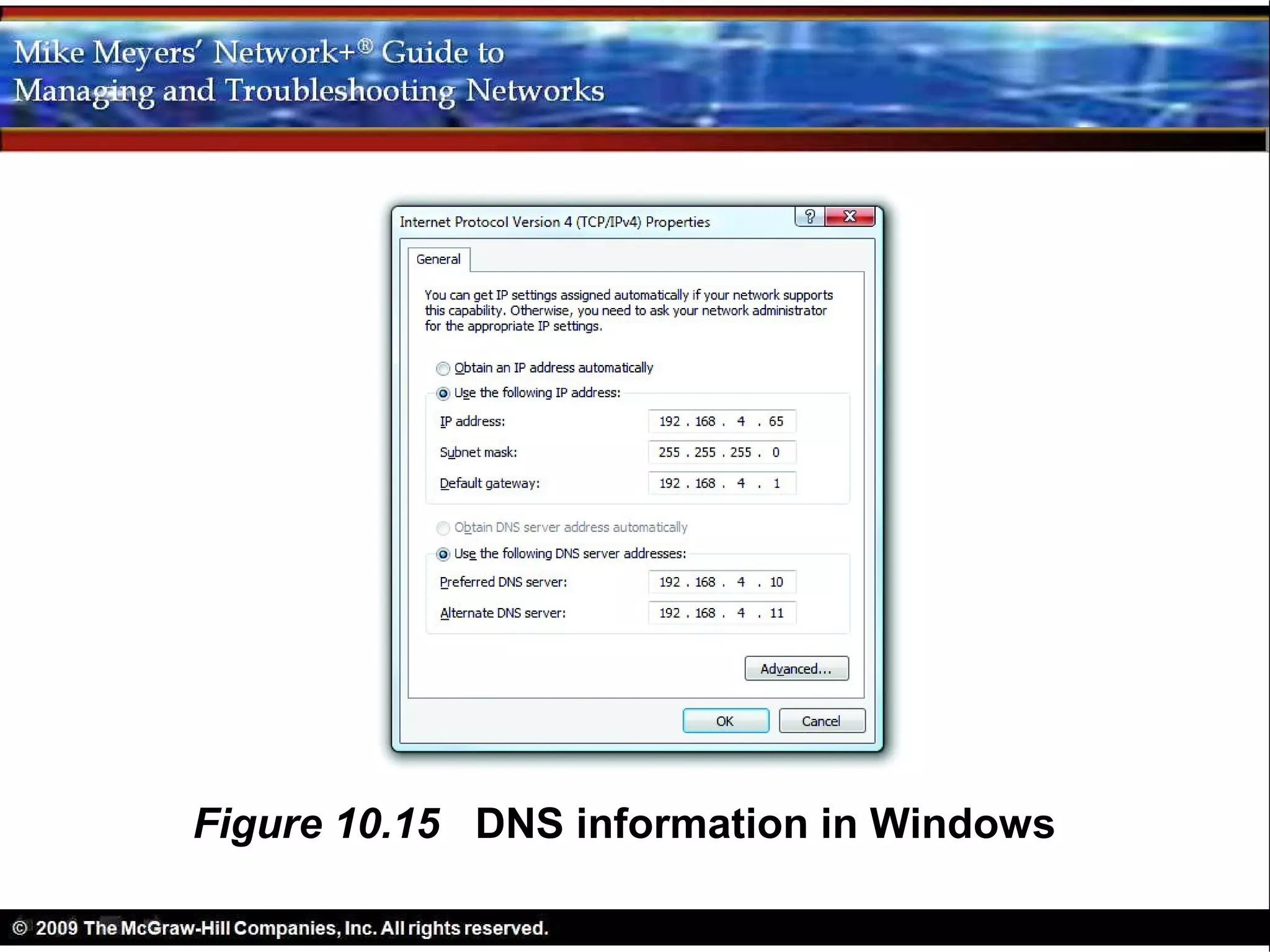
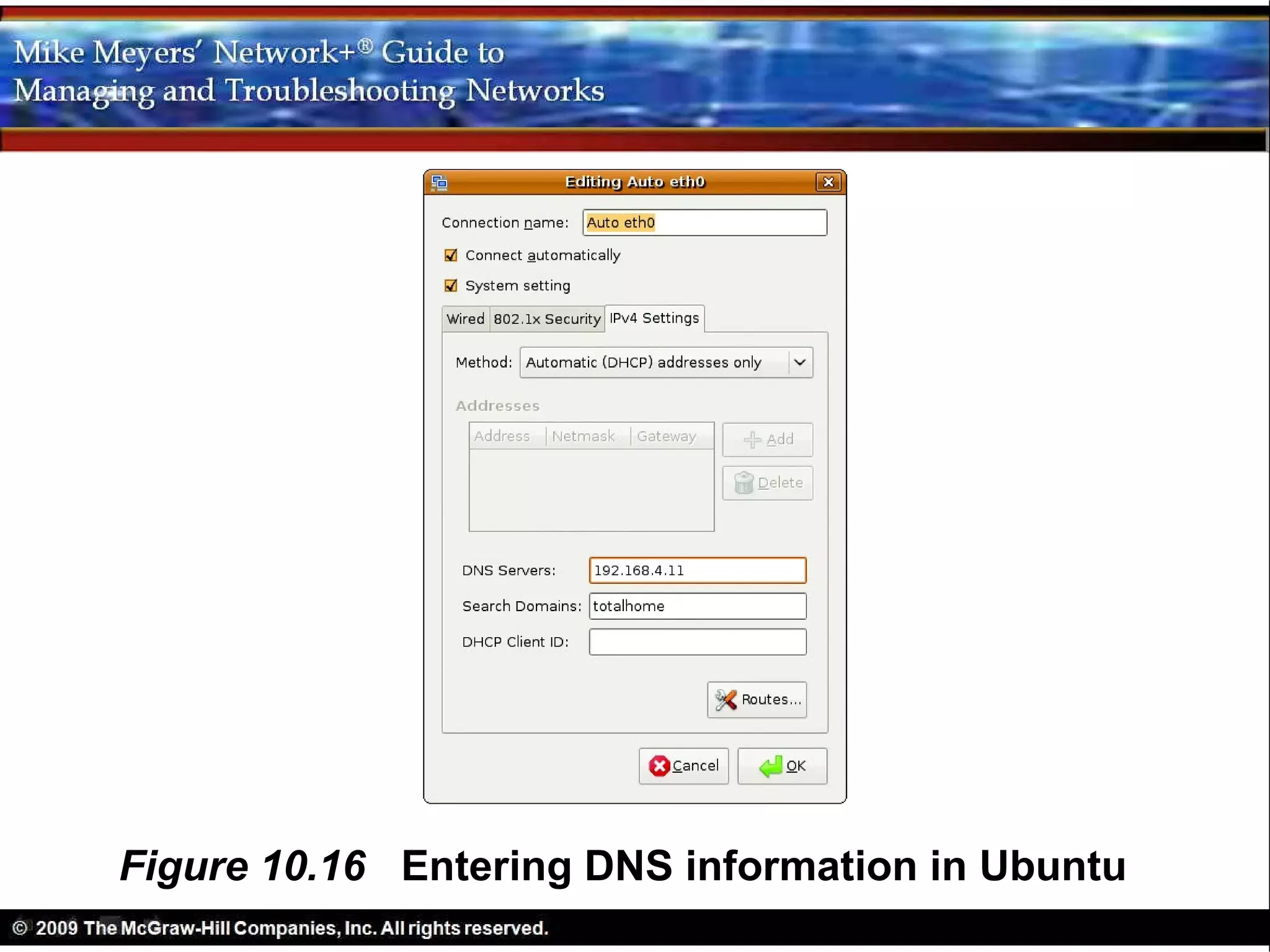
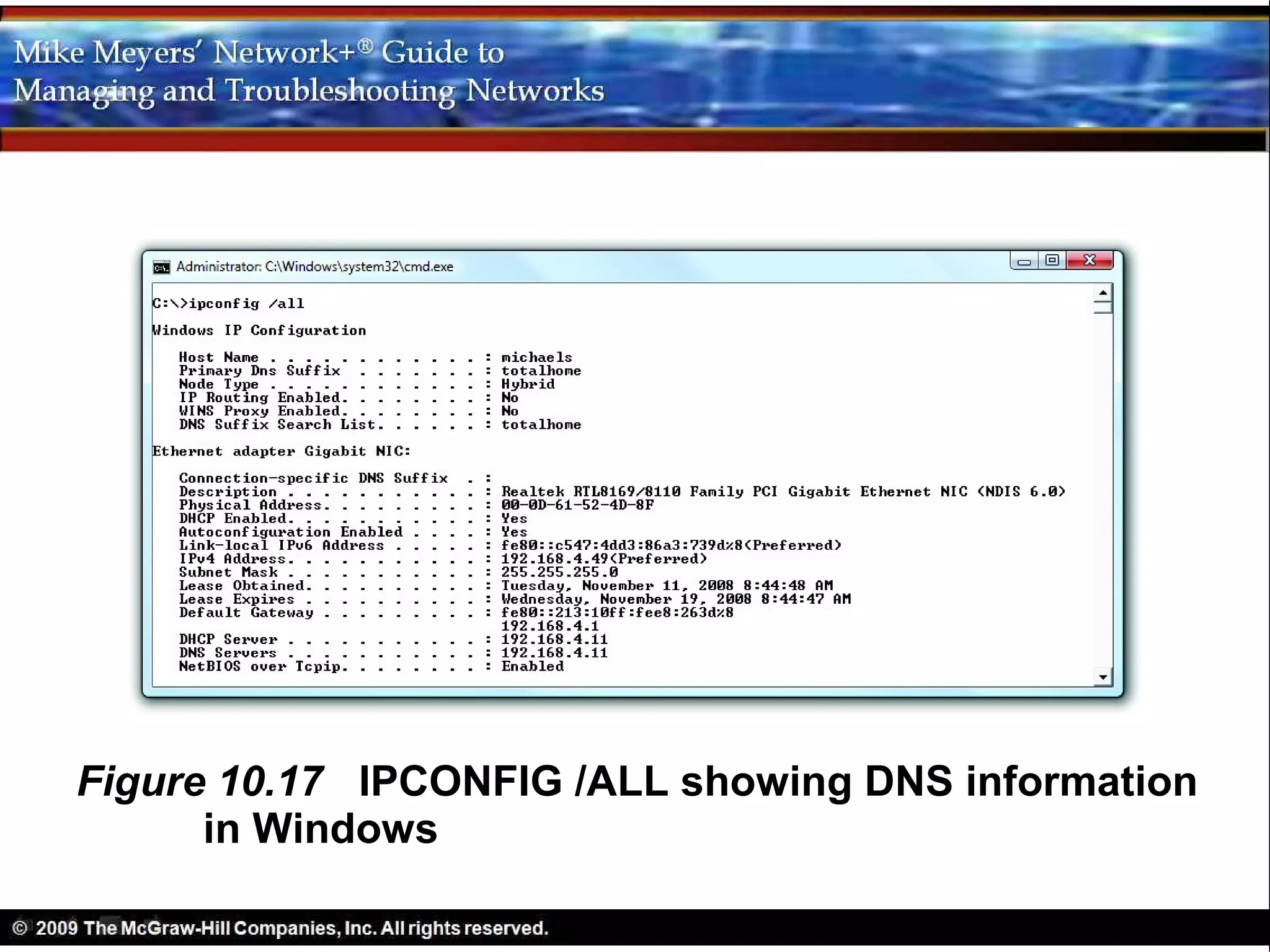
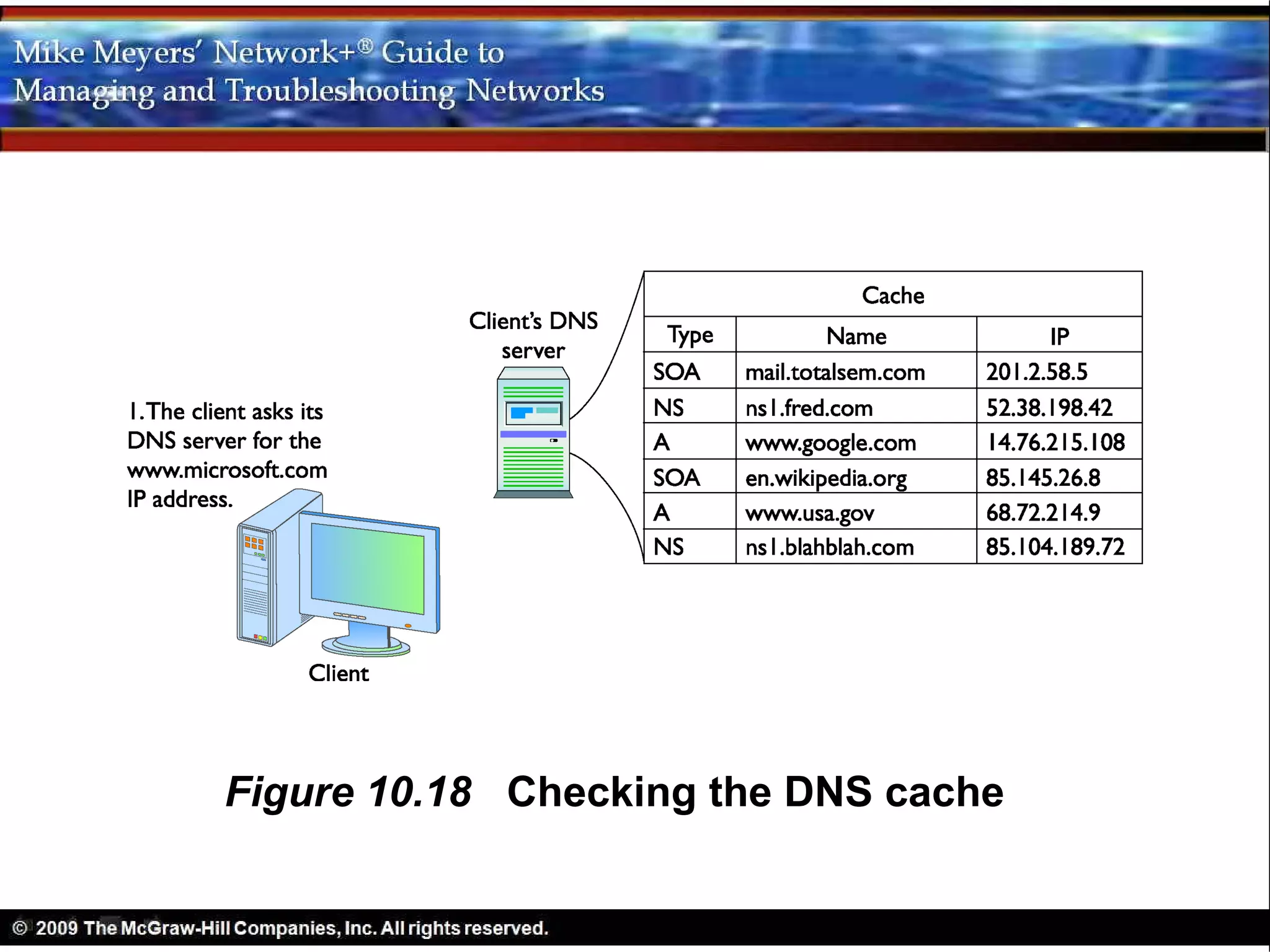
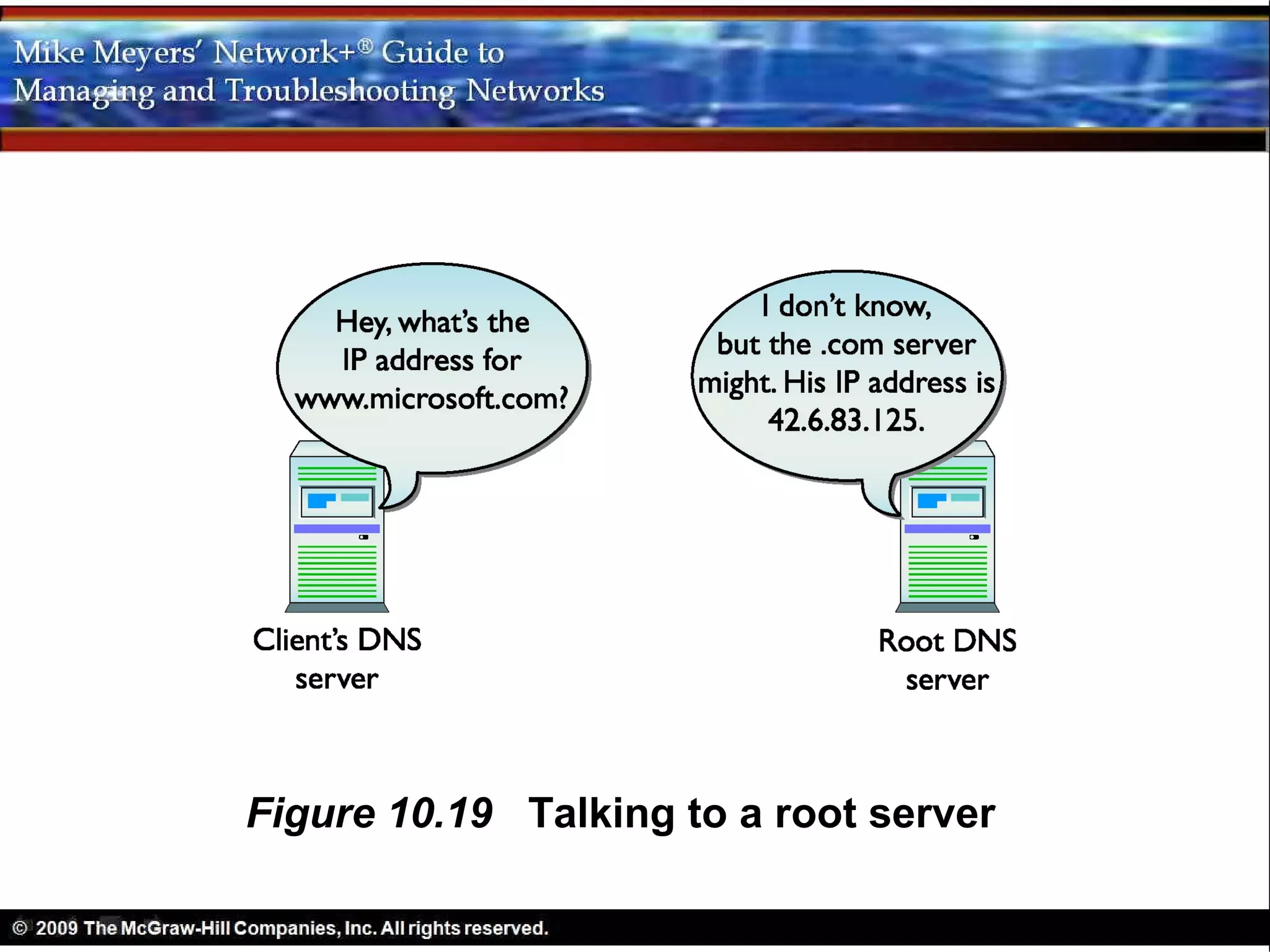
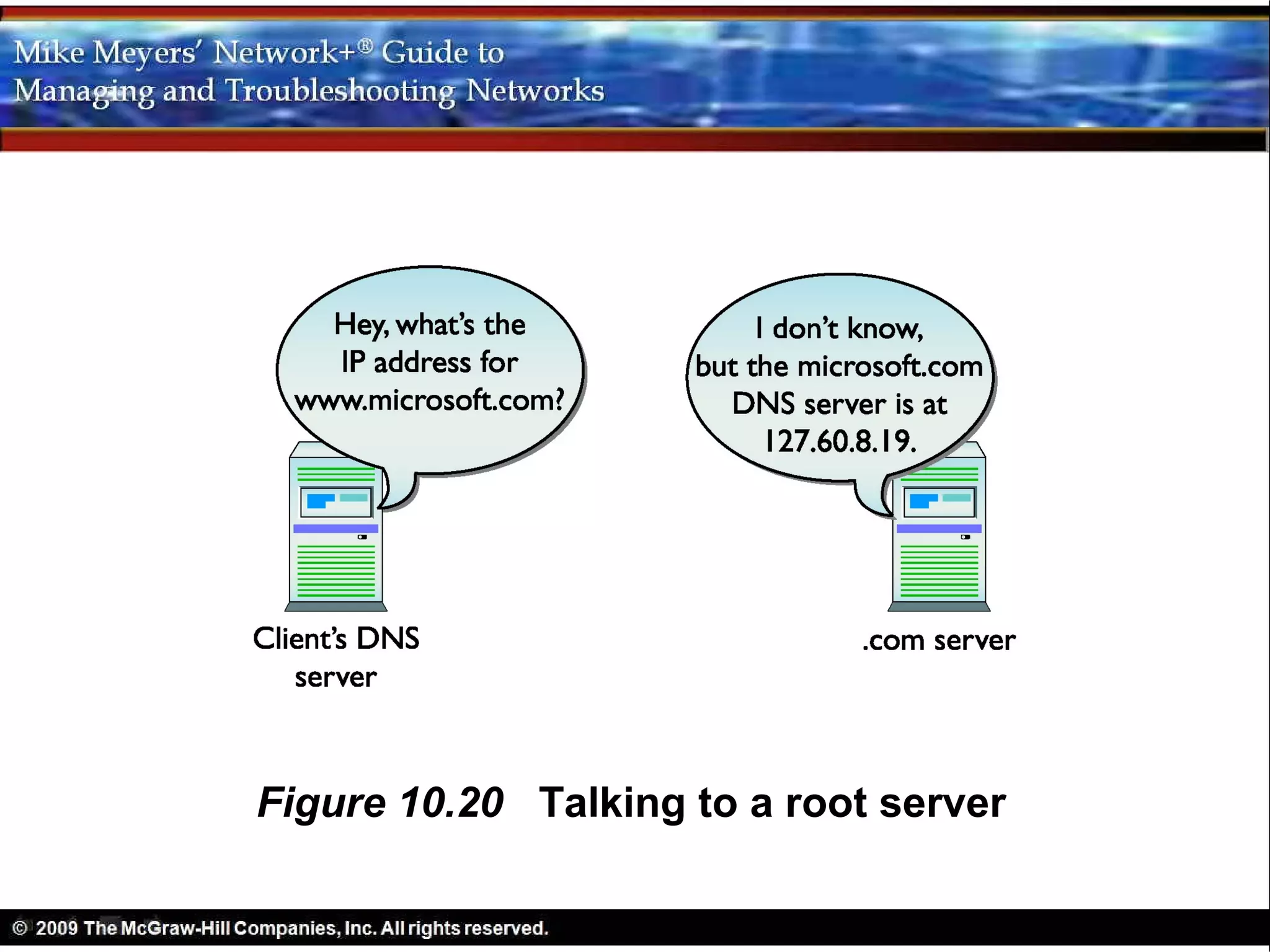
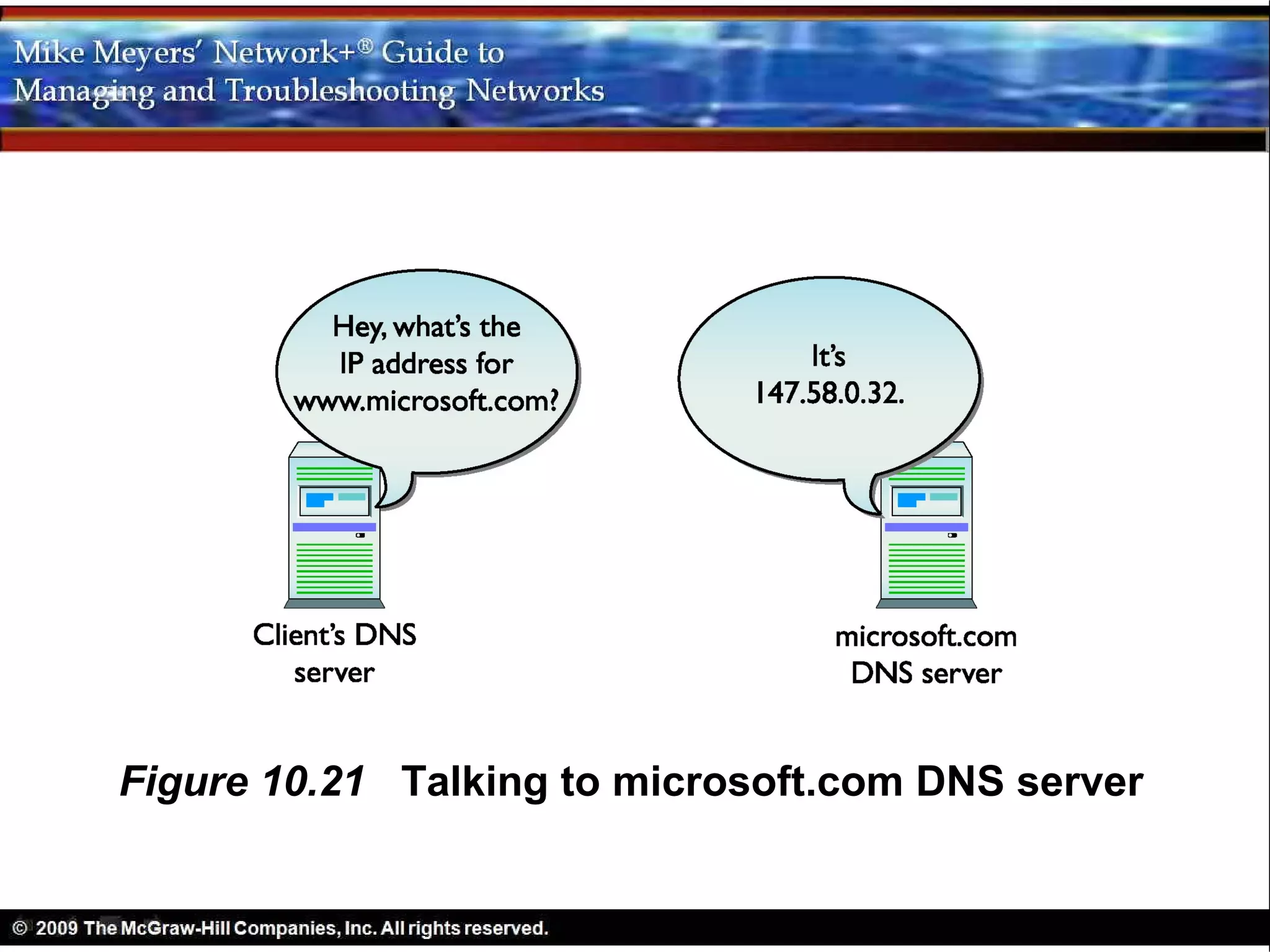
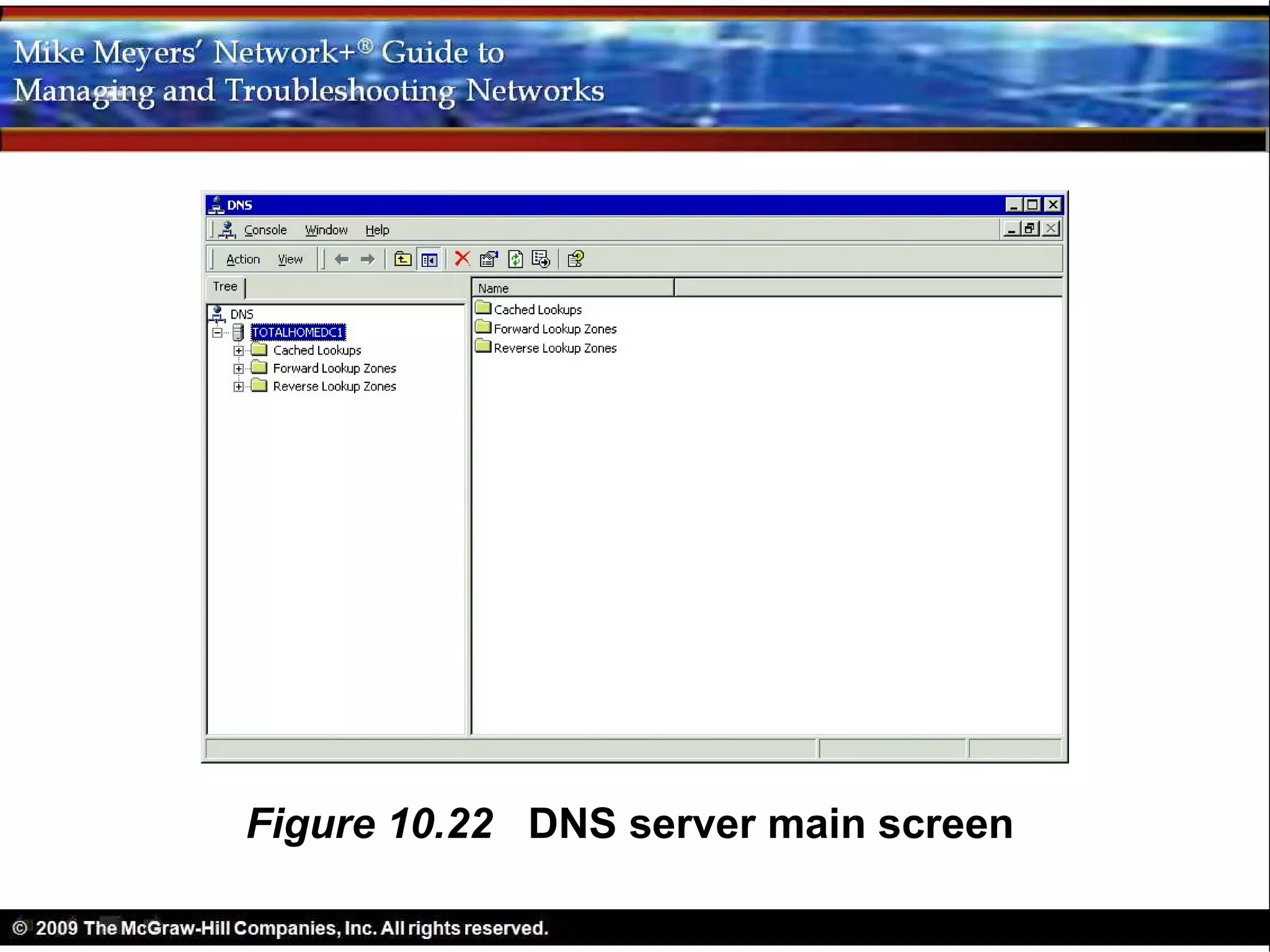
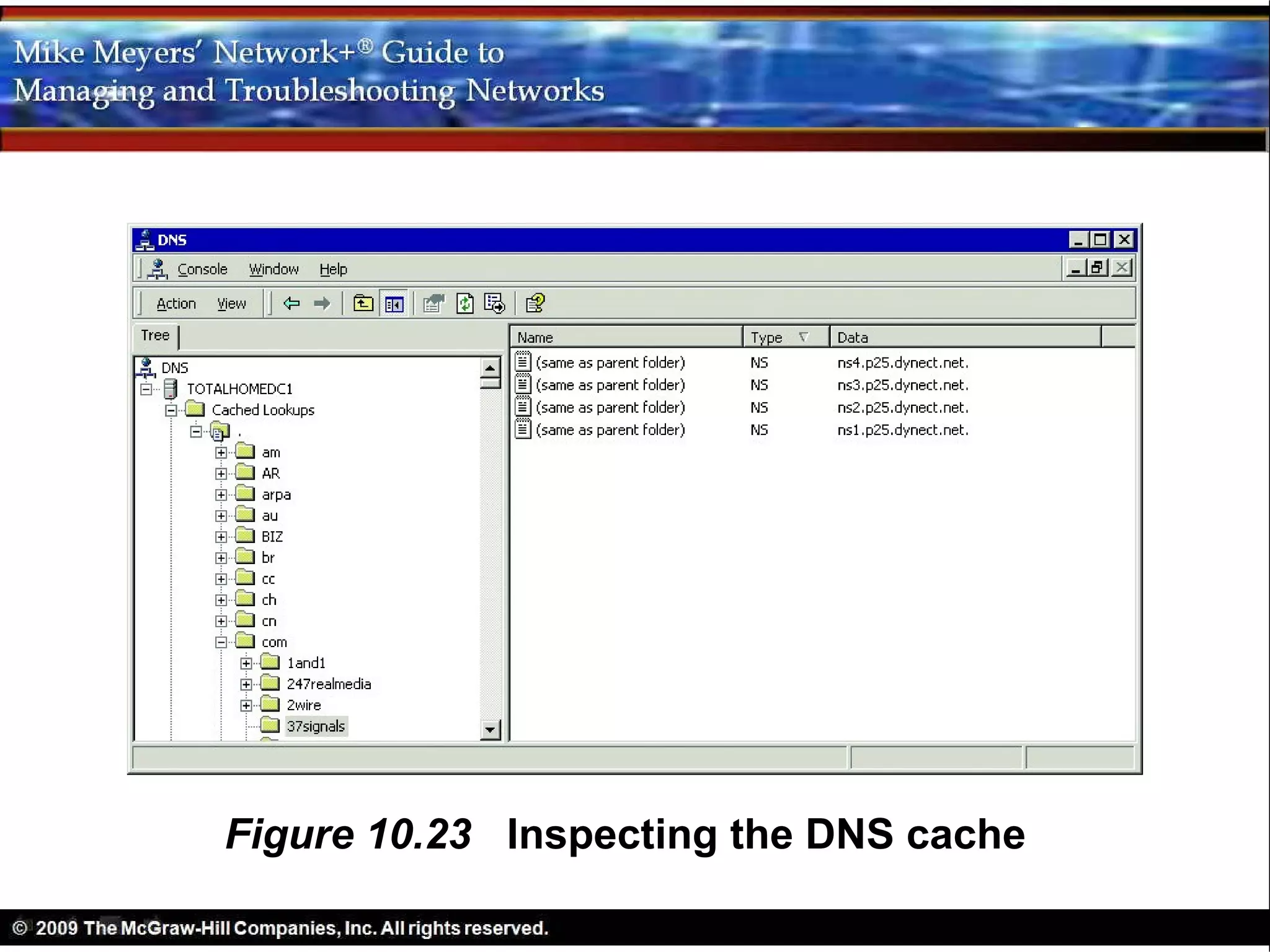
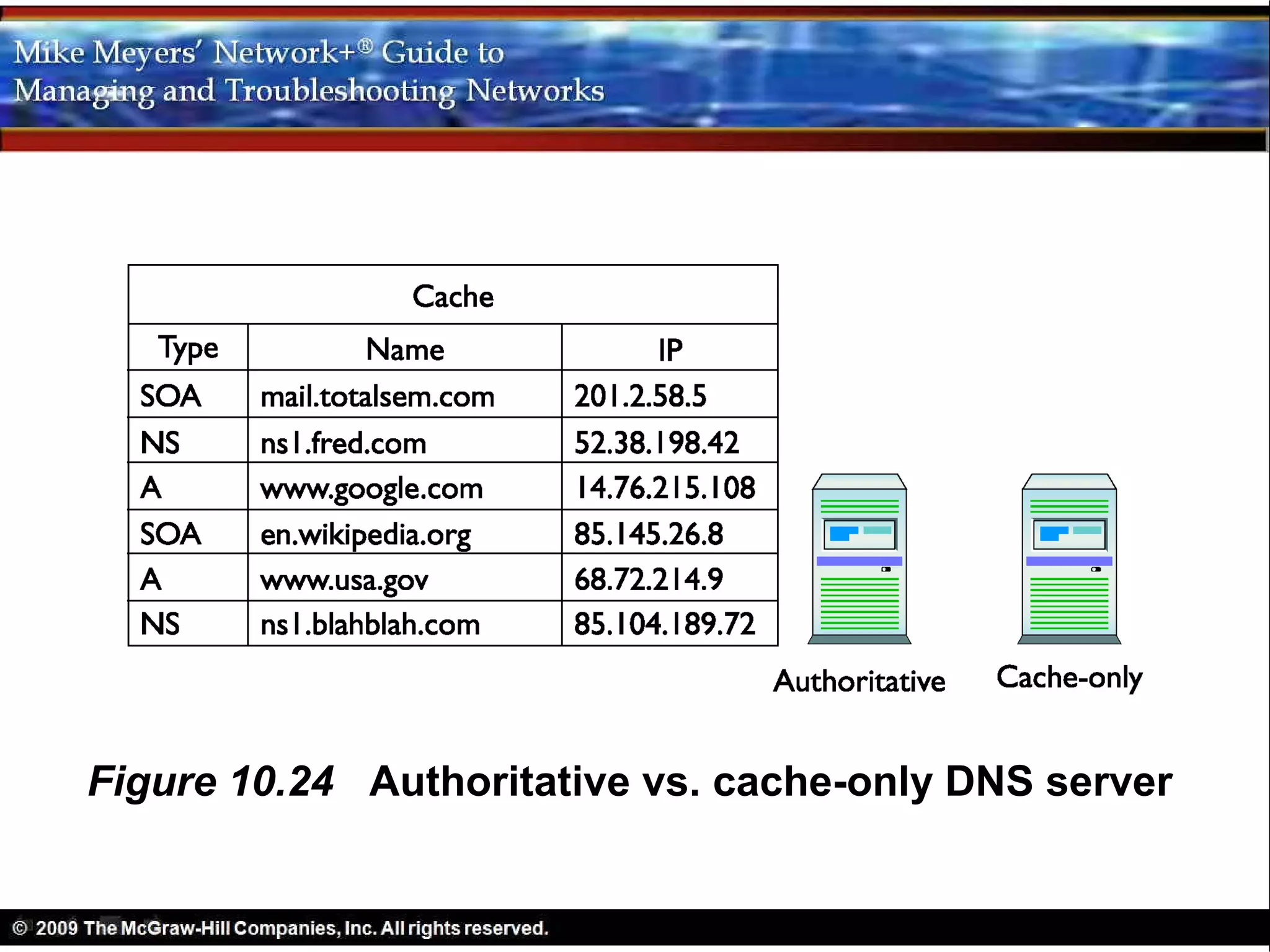
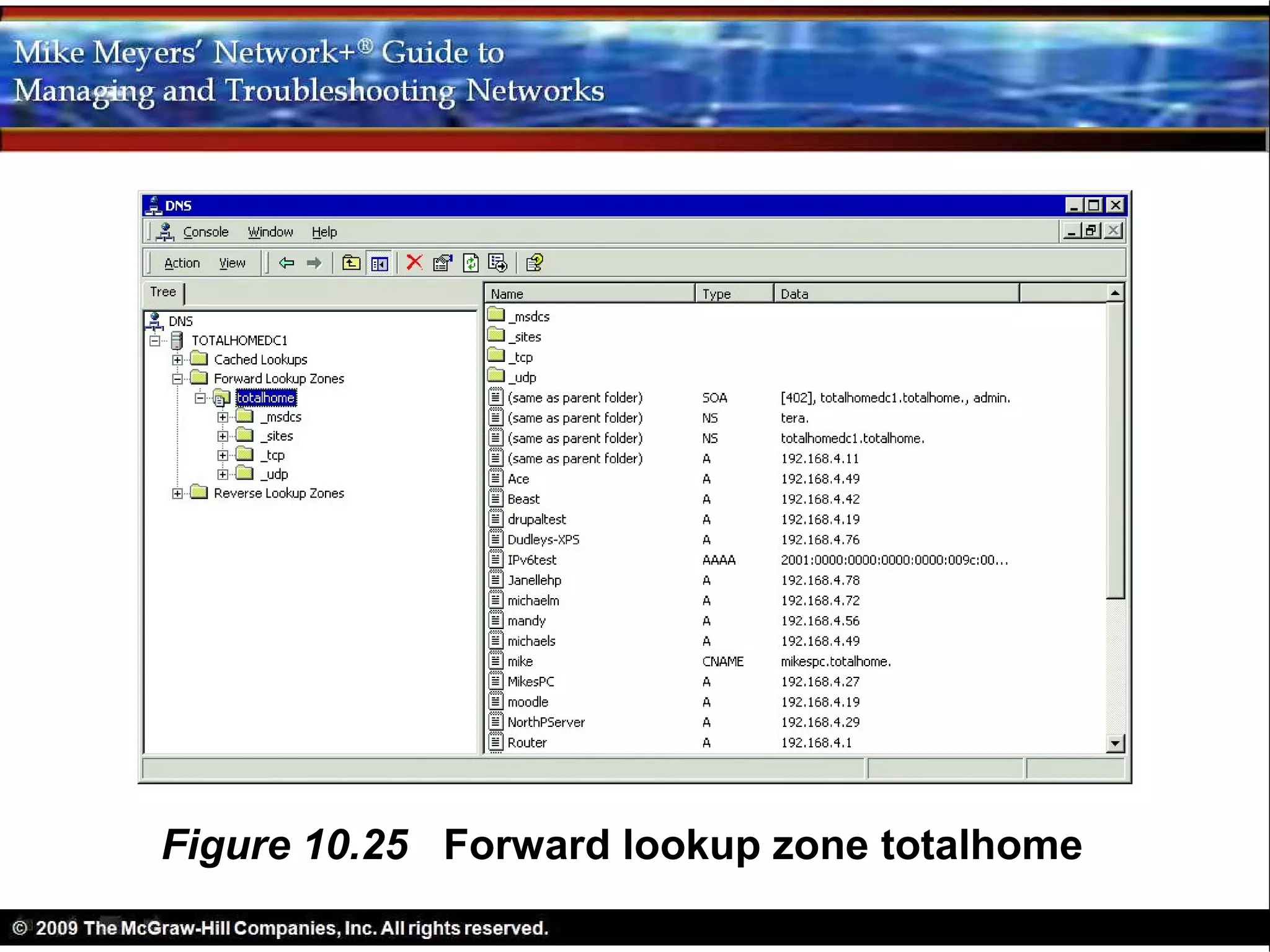
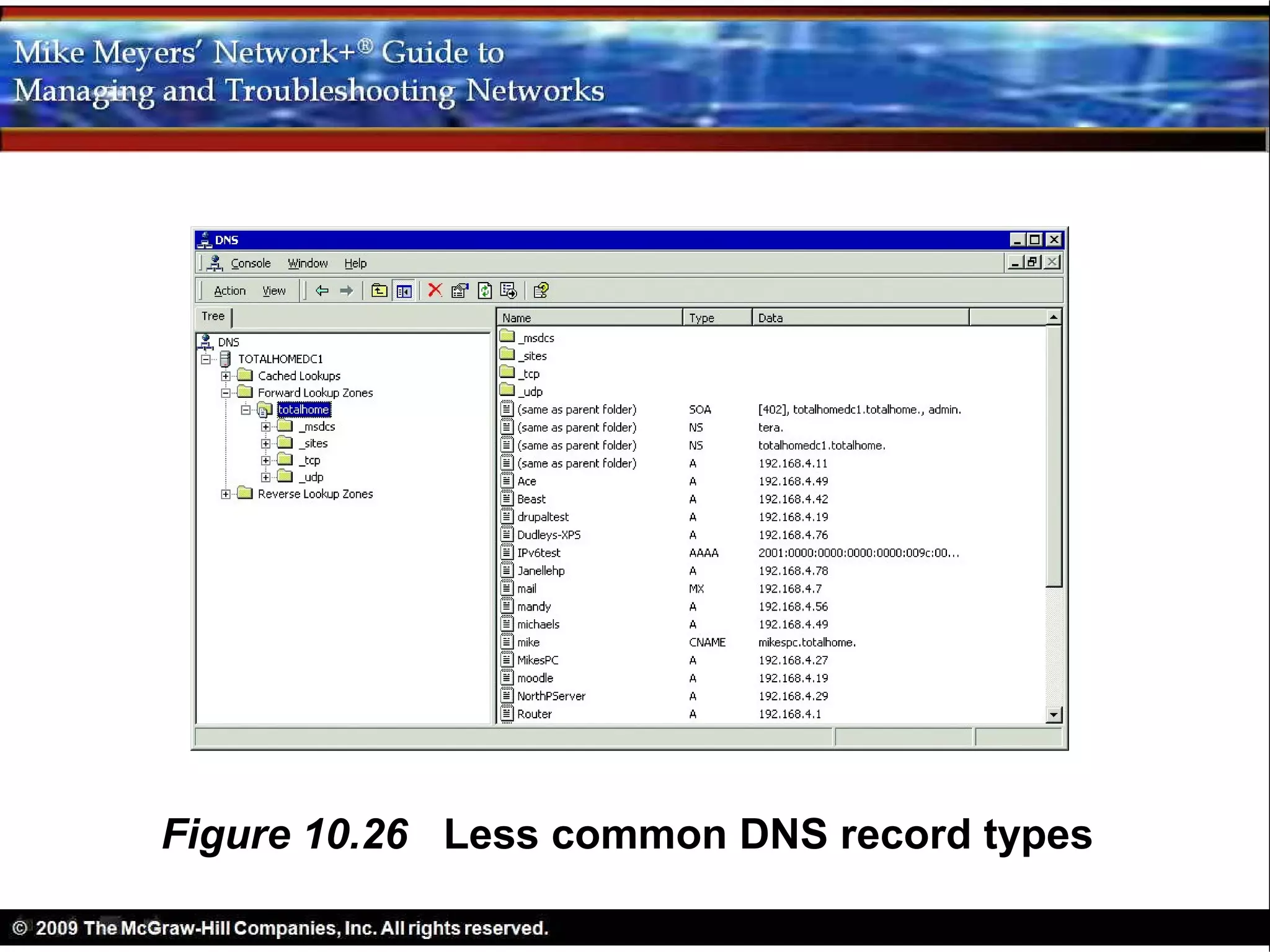
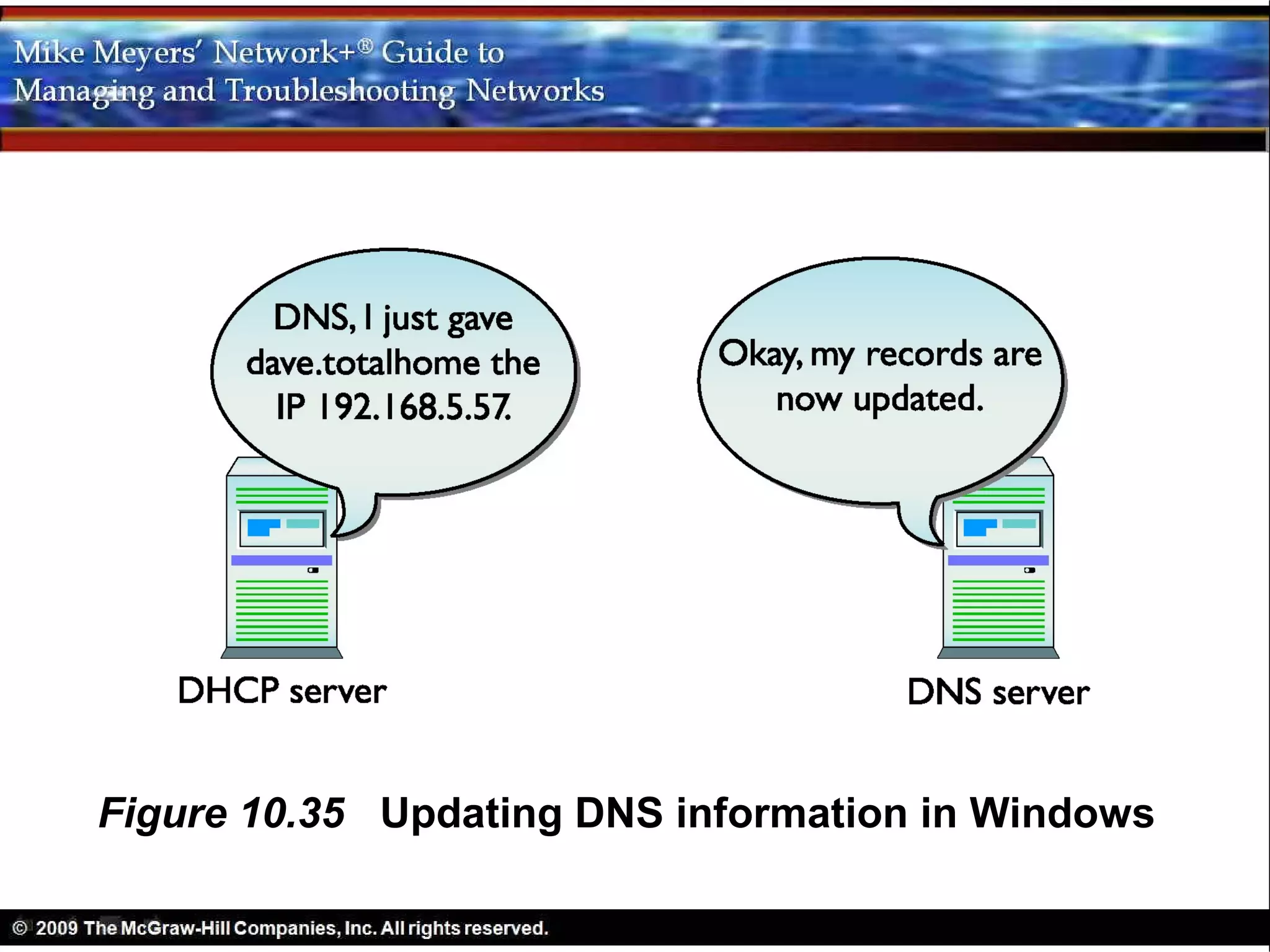
2) Additional details on how DNS works, including name spaces, name servers, name resolution, and examples of DNS configurations.
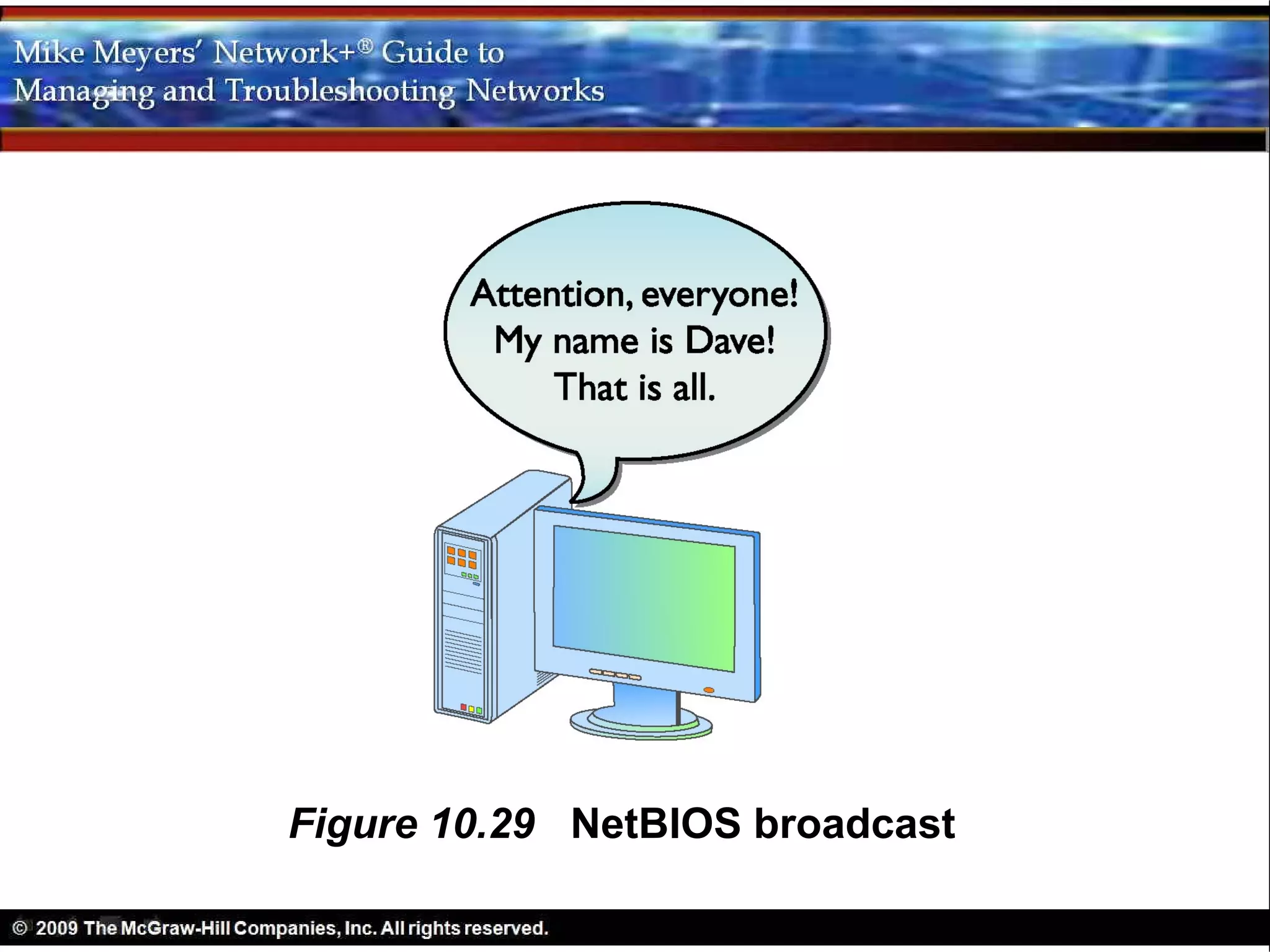
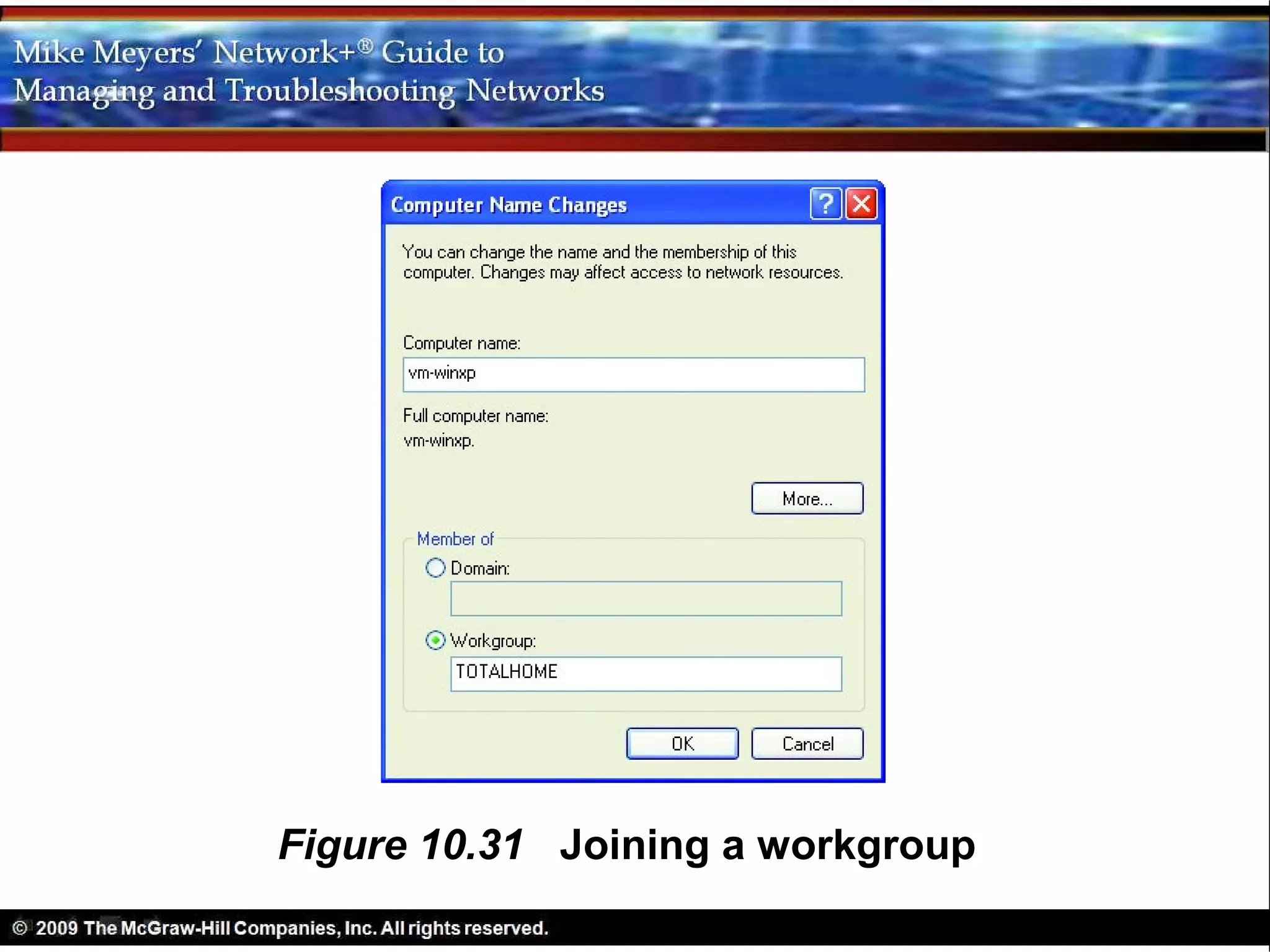
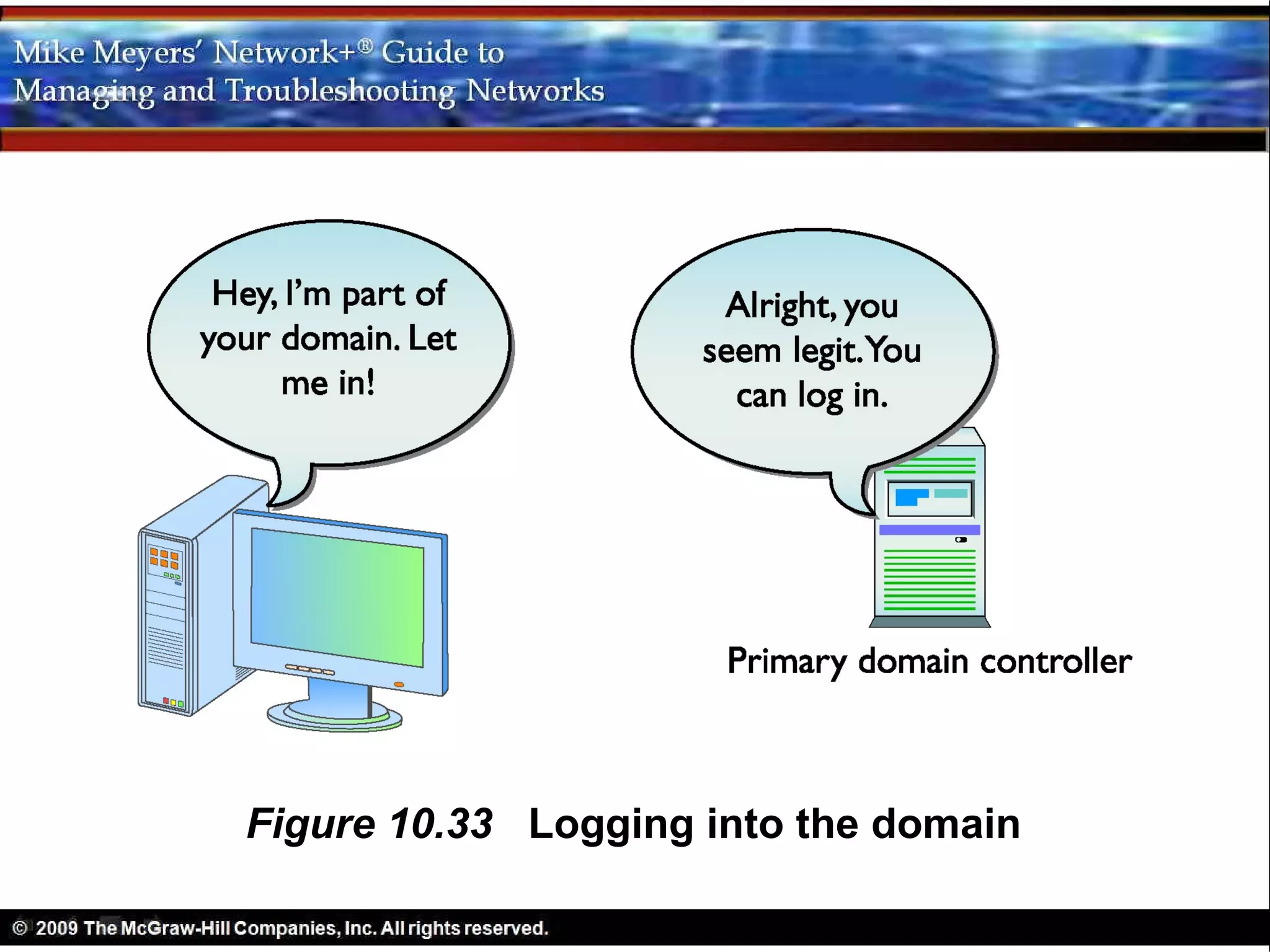
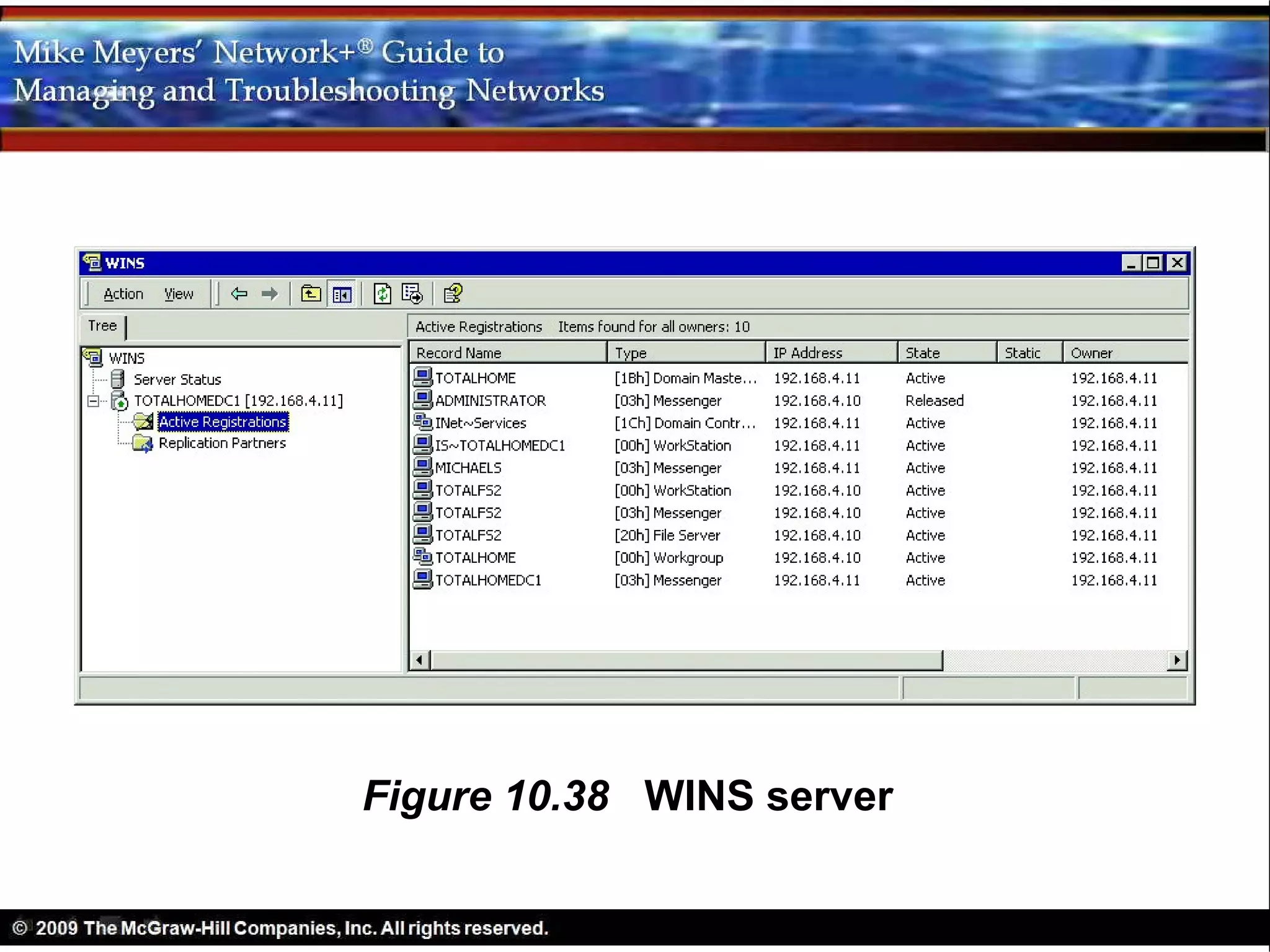
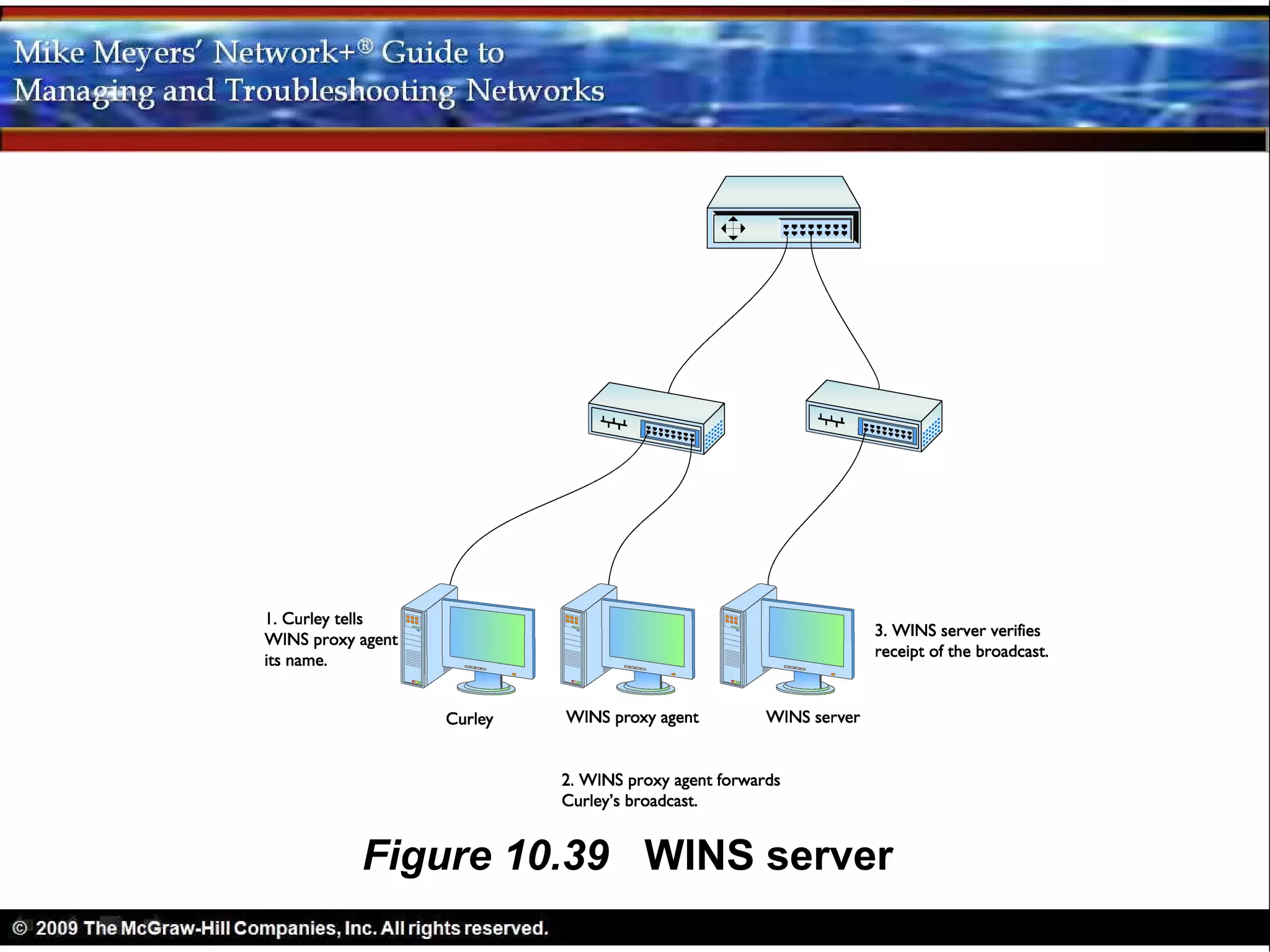
3) A brief introduction to WINS, which provides name resolution for legacy NetBIOS names to support backward compatibility in Windows networks.
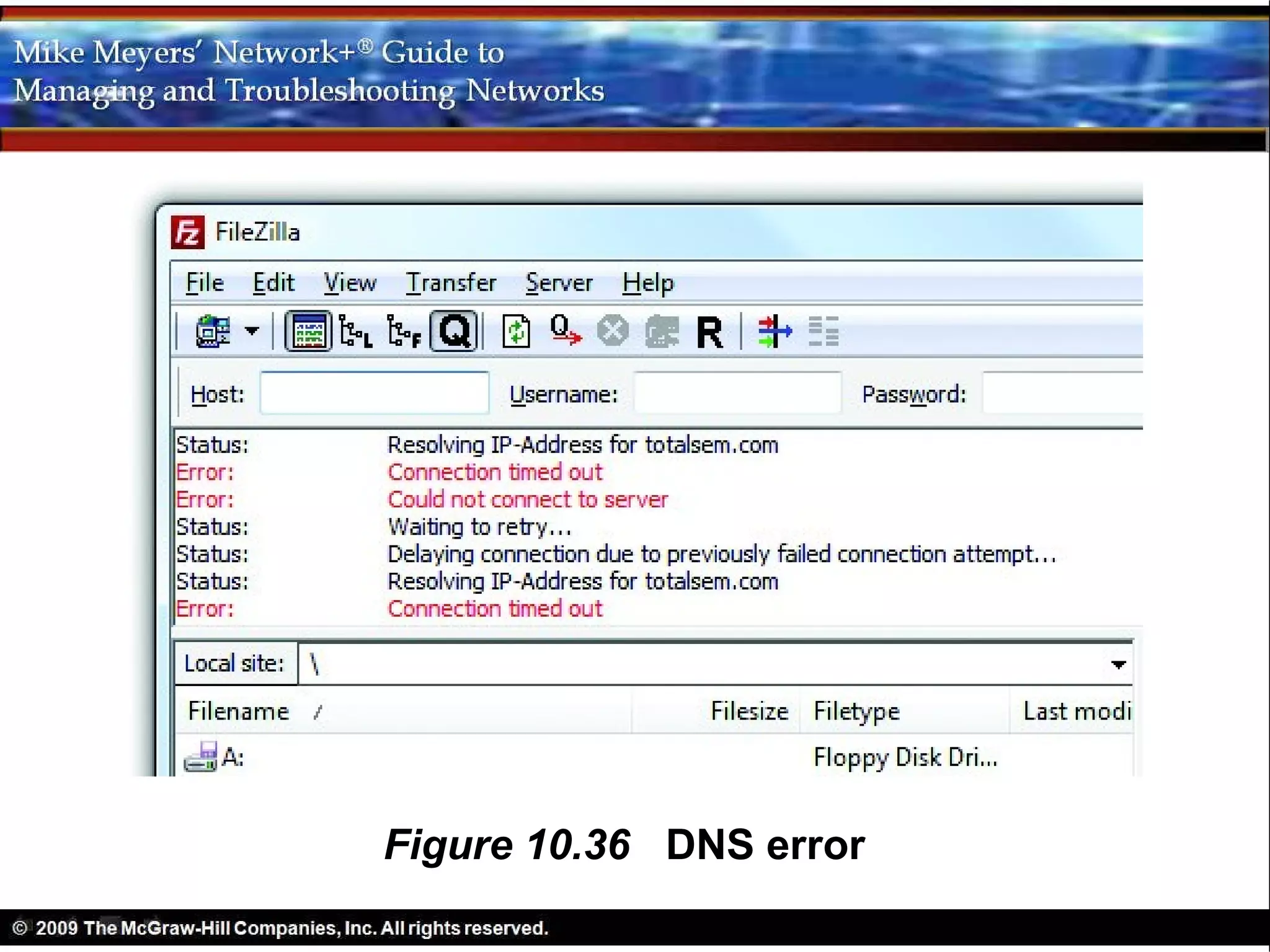
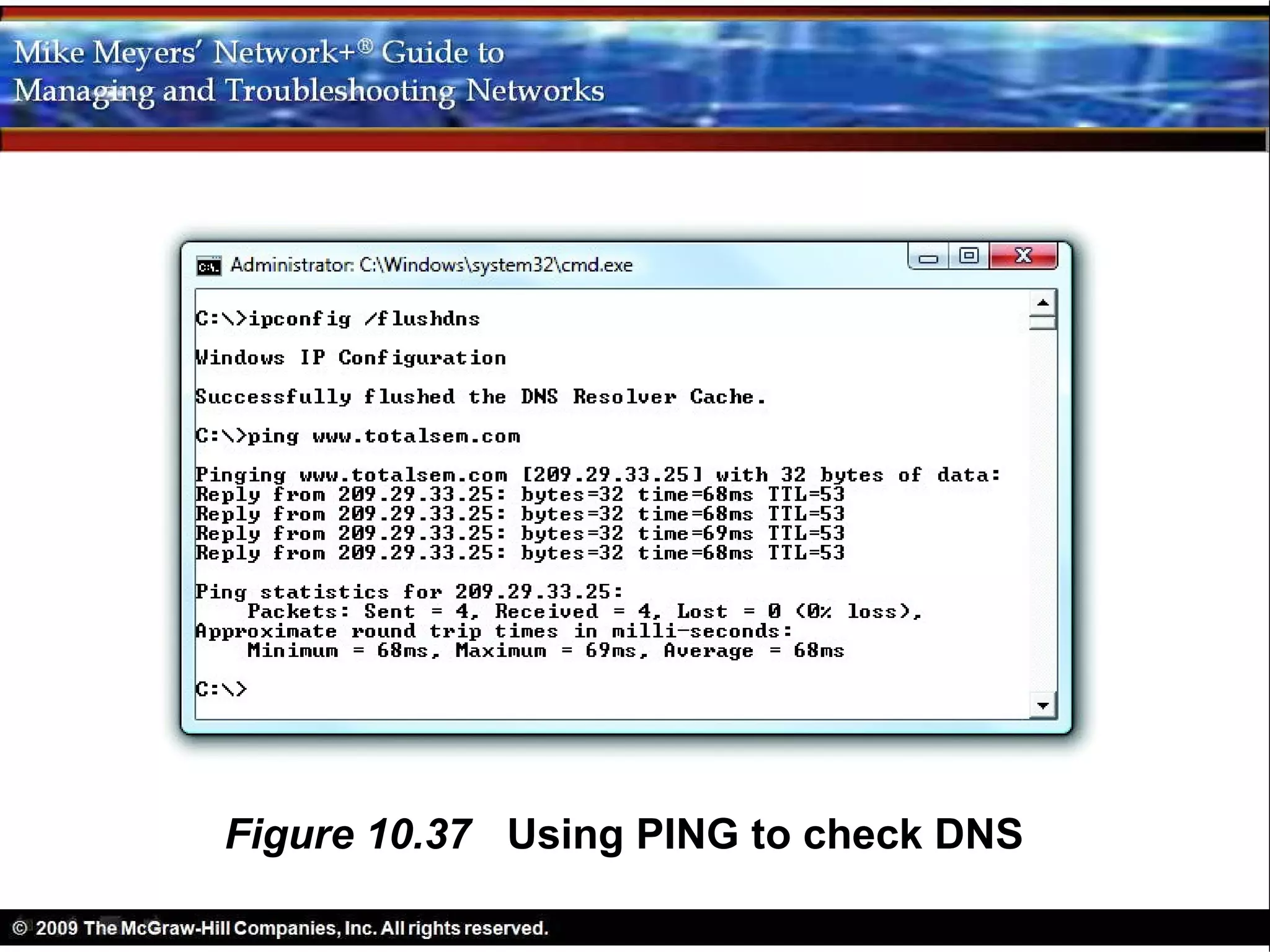
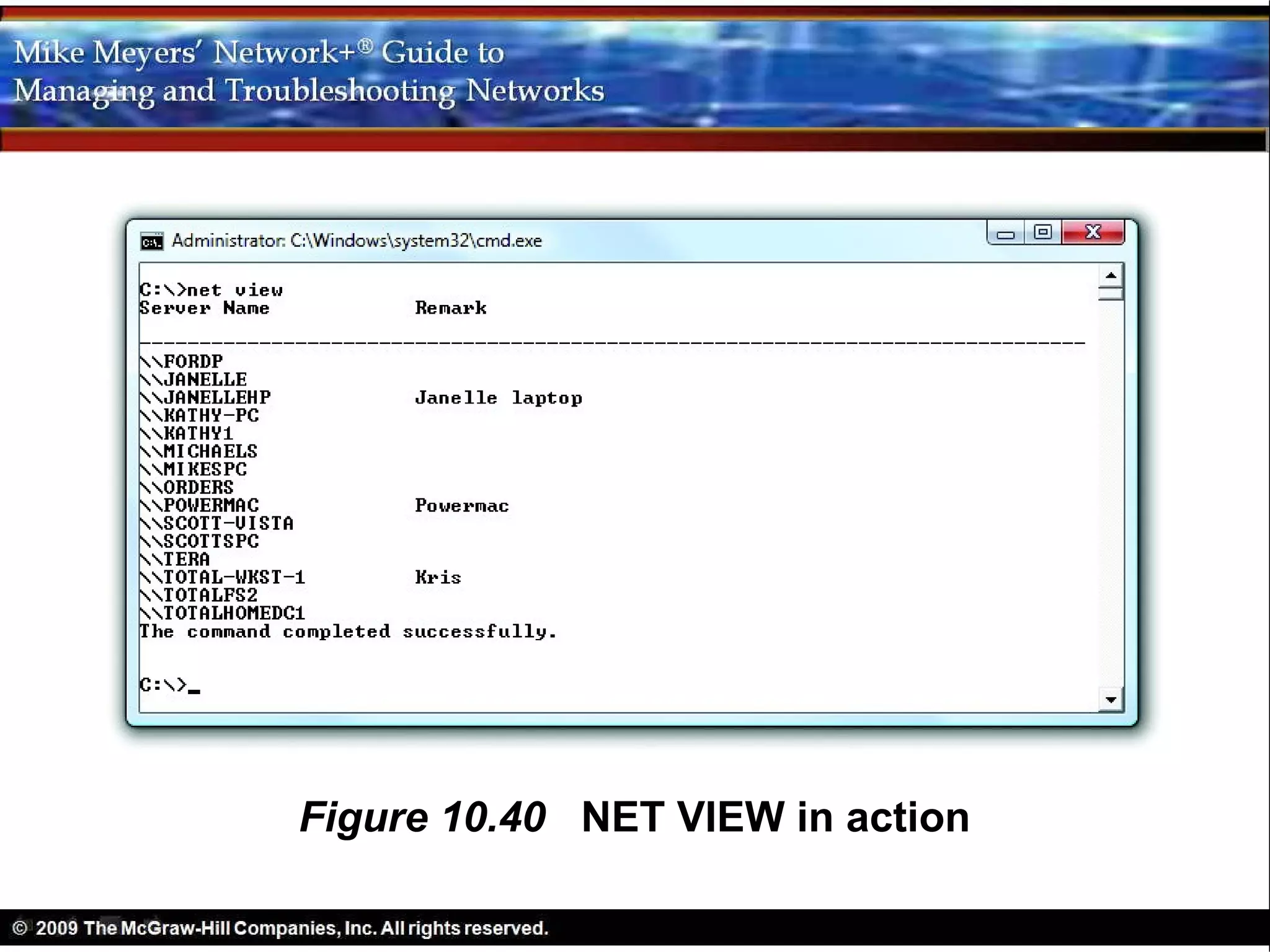
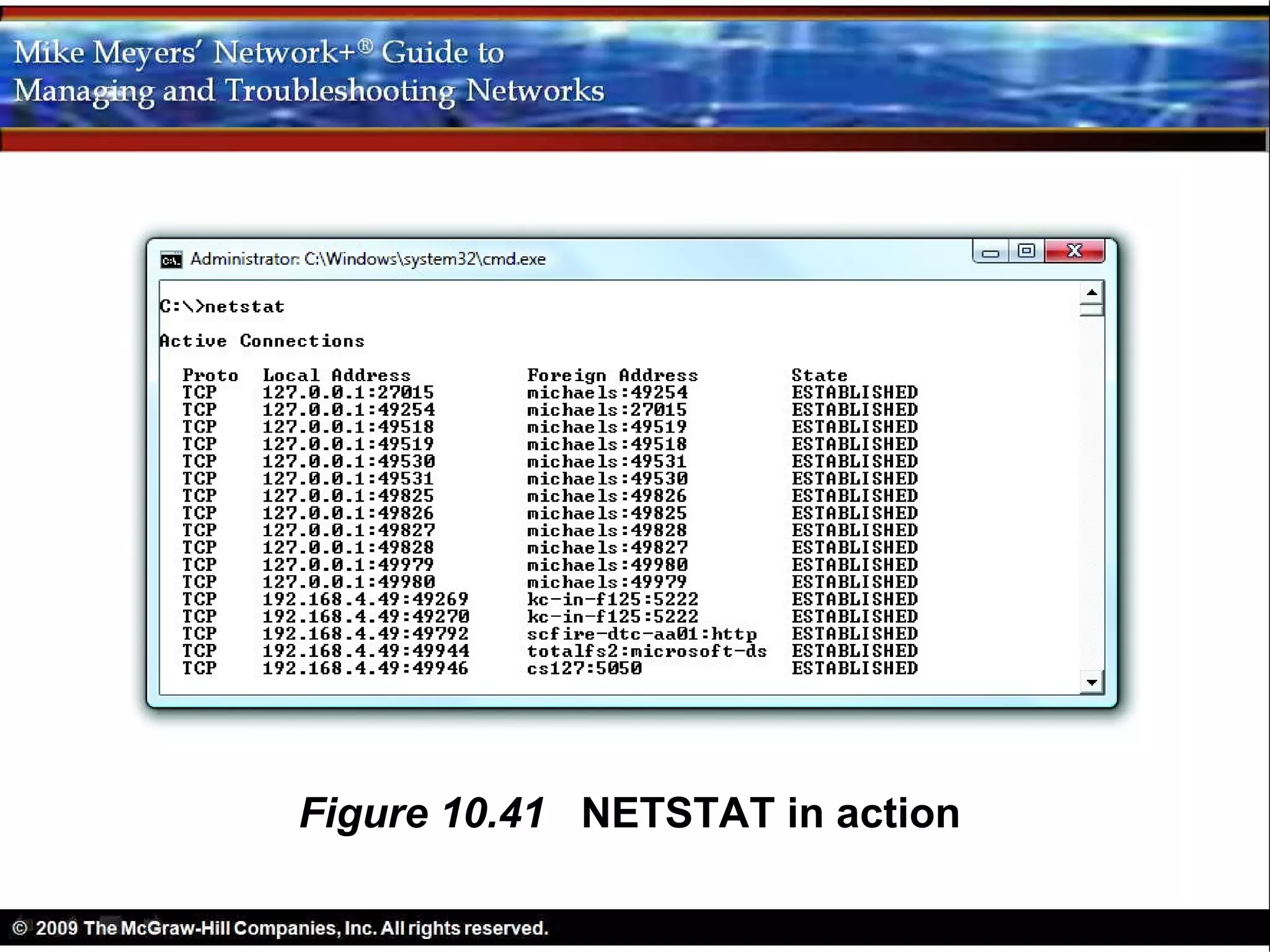
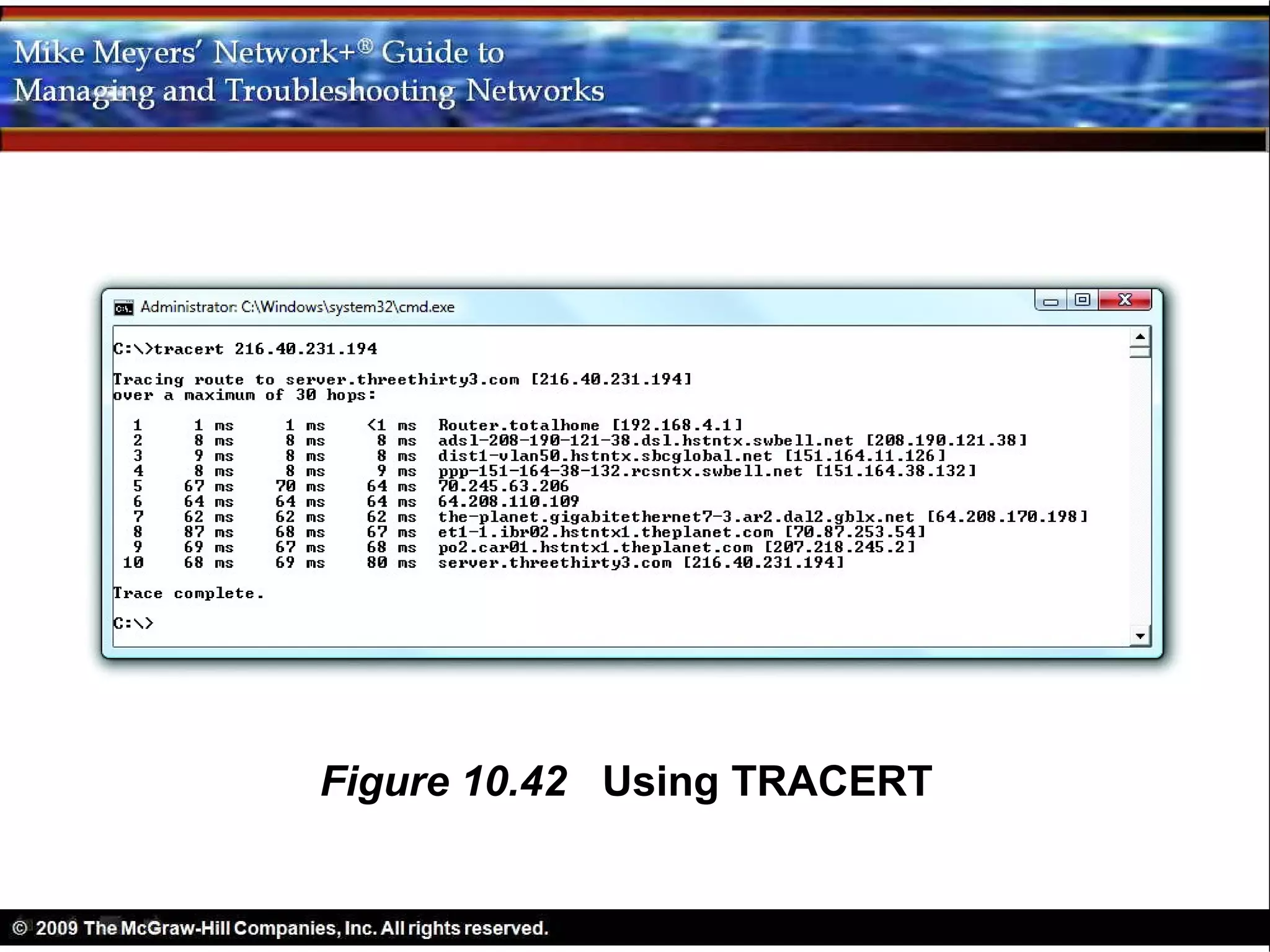
4) How DNS and WINS can be used together, as well as tools for diagnosing and troubleshooting TCP/IP networks.