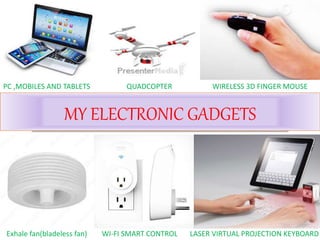
My electronic gadget
•Download as PPTX, PDF•
4 likes•1,395 views
This document discusses selecting and protecting electronic gadgets. It provides tips for choosing a good gadget, mobile, and laptop by considering factors like the operating system, processor, RAM, hard disk size, and battery life. It also discusses the top mobile operating systems and lists the best laptops under 35,000 rupees. Finally, it covers protecting devices from viruses by using antivirus software and cleaning temporary files.
Report
Share
Report
Share
Recommended
Gadgets

This presentation discusses gadgets for the beginner, including phones, eBooks, portable music devices, tablets and portable storage.
Laptops of 2018 ppt

This is an interpretation of an article from PCWorld. It is based on the fact that the seeping in of mobile technological devices like touch screen phones, etc have threatened the existence of PCs and laptops.
Effect of using mobile phone

What is a Mobile phone?
History and Evolution of Mobile
Main Source Of Using Mobile Phone
Effects of Mobile Phone
Effect on nature
Tips for reducing potential harmful
effects of mobile phone radiation
References
Evolution of laptops

This presentation is based on how laptops are evolved from olden days to present days. This presentation includes the History, Advantages, Disadvantages of laptops.
Recommended
Gadgets

This presentation discusses gadgets for the beginner, including phones, eBooks, portable music devices, tablets and portable storage.
Laptops of 2018 ppt

This is an interpretation of an article from PCWorld. It is based on the fact that the seeping in of mobile technological devices like touch screen phones, etc have threatened the existence of PCs and laptops.
Effect of using mobile phone

What is a Mobile phone?
History and Evolution of Mobile
Main Source Of Using Mobile Phone
Effects of Mobile Phone
Effect on nature
Tips for reducing potential harmful
effects of mobile phone radiation
References
Evolution of laptops

This presentation is based on how laptops are evolved from olden days to present days. This presentation includes the History, Advantages, Disadvantages of laptops.
Power Bank

Uimi India is have its creative business policy to serve the customers & corporate at better way. We are in the retail market as well as in online market with the broad visibility of our products & after sales services.
For more information, Visit: www.uimitech.com
SOLID-STATE BATTERY PERFORMANCE FOR THE EV INDUSTRY - COMMERCIAL TO PASSENGER

Adrian Tylim
Blue Solutions
Apple Inc. Life History

Whole Life history of Inc. from its born till 2017. From RNB Global University
Roll Laptop

Roll Laptop presentation presented by Khan Kashifa, Kazi Tanveen, Khan Fatima and Khan Faimin from M. H. Saboo Siddik Polytechnic
Rechargeable Sodium-ion Battery - The Future of Battery Development

Rechargeable Sodium-ion Battery - The Future of Battery Development
Uses and Abuses of Mobile Phone

This slide was used as a part of my English101 course at the first semester of United International University. Our focus was to describe the uses and abuses of mobile phone in the context of Bangladesh.
Gadget bazaar

Created by Vandan Kothari, IIT Roorkee, during a marketing internship by Prof. Sameer Mathur, IIM Lucknow
More Related Content
What's hot
Power Bank

Uimi India is have its creative business policy to serve the customers & corporate at better way. We are in the retail market as well as in online market with the broad visibility of our products & after sales services.
For more information, Visit: www.uimitech.com
SOLID-STATE BATTERY PERFORMANCE FOR THE EV INDUSTRY - COMMERCIAL TO PASSENGER

Adrian Tylim
Blue Solutions
Apple Inc. Life History

Whole Life history of Inc. from its born till 2017. From RNB Global University
Roll Laptop

Roll Laptop presentation presented by Khan Kashifa, Kazi Tanveen, Khan Fatima and Khan Faimin from M. H. Saboo Siddik Polytechnic
Rechargeable Sodium-ion Battery - The Future of Battery Development

Rechargeable Sodium-ion Battery - The Future of Battery Development
Uses and Abuses of Mobile Phone

This slide was used as a part of my English101 course at the first semester of United International University. Our focus was to describe the uses and abuses of mobile phone in the context of Bangladesh.
What's hot (20)
SOLID-STATE BATTERY PERFORMANCE FOR THE EV INDUSTRY - COMMERCIAL TO PASSENGER

SOLID-STATE BATTERY PERFORMANCE FOR THE EV INDUSTRY - COMMERCIAL TO PASSENGER
How Information Communication Technology used in Manufacturing Industry.

How Information Communication Technology used in Manufacturing Industry.
Rechargeable Sodium-ion Battery - The Future of Battery Development

Rechargeable Sodium-ion Battery - The Future of Battery Development
Viewers also liked
Gadget bazaar

Created by Vandan Kothari, IIT Roorkee, during a marketing internship by Prof. Sameer Mathur, IIM Lucknow
How To Use Facebook To Get Referrals From Past Clients

During this event you get to learn the three profit activators in your mortgage business. Then we go in depth into a simple strategy to help you generate an immediate influx of new referrals.
Cover & Carry - Internet Business Marketing Plan

Cover & Carry is a one-stop shop for protective coverings fit for any electronic device. We offer customized cases from preselected materials and designs, our company stands out by allowing
customers to create new products from their personal belongings.
A pure play business, Cover & Carry will have no bricks-and-mortar storefront and our manufacturer-direct model will focus on creating one-to-one relationships with customers. Our target is composed of heavy electronics users, from the young adults entering college or the workforce to the middle-aged professionals with multiple gadgets they want to cover. We hope to position Cover & Carry as as a high-quality, high-value brand, distinguishing ourselves through our personalized shopping experience and devotion to customer
service.
Use of Electronic Devices for National License Examination Self-Study among R...

Use of Electronic Devices for National License Examination Self-Study among R...Nawanan Theera-Ampornpunt
Abstract for poster presentation at the 16th National Medical Education Conference of Thailand in August 2015Powerful Real Estate Business Plans

Presentation to Florida REALTORS Annual Conference 2015 on 3 Steps to a Powerful Real Estate Business Plan
Simple, proven real estate business plan 

If your real estate business is not what you want it to be, this for your.
A few phone calls to the proper target audience along with a continuous, repetitive direct mail campaign and the profit rocks.
IT Quiz Final @ eRz eRDeN 15, IT Fest, ITM Mayyil

IT-Tech quiz @ eRz eRDen Annual IT Fest conducted by Dept of Computer Application, ITM
Business Plan Poultry Industry

This is an actual report on Poultry farming of the earlier uploaded presentation http://www.slideshare.net/HariyoKakro/rato-bhale
Digital Marketing Plan for Real Estate Business

Its a complete step by step digital marketing plan and strategy for real estate business. Follow these actionable steps to increase your business online reputation, sales, leads and ranking. Wanna know how you can increase leads for your real estate business? Check this detailed Digital Marketing Plan
Business Plan for Arya Travel Agency

This slide show is a business plan. The bullet points which are underline have some excel sheets, contained detais in numbers. It can be furnished on demand.
Digital Marketing Plan For Real Estate

Digital Marketing Plan For Real Estate.
Running a business is hard with lots of moving parts, Technologies and demands on your time. One important task is marketing, especially digital marketing For Branding & Lead generation. Mostly business's & clients require only two things from the digital marketing-Brand awareness & Business Leads.
Viewers also liked (20)
How To Use Facebook To Get Referrals From Past Clients

How To Use Facebook To Get Referrals From Past Clients
Use of Electronic Devices for National License Examination Self-Study among R...

Use of Electronic Devices for National License Examination Self-Study among R...
Similar to My electronic gadget
Computer Basics and Hardware

Computer Basics and HardwareAmity University | FMS - DU | IMT | Stratford University | KKMI International Institute | AIMA | DTU
Computer Basics and HardwareHardware & networking

IT IS MORE USEFUL FOR KNOWING ABOUT HARDWARE AND NETWORK IN COMPUTER FOR NON TECHNICAL PEOPLE WHO WANT TO KNOW ABOUT IT.
Similar to My electronic gadget (20)
Computer hardware Created By :- king parmeshwar pawar

Computer hardware Created By :- king parmeshwar pawar
Introduction to Computing not in 2022 - Presentation

Introduction to Computing not in 2022 - Presentation
More from Madugula Kumar (13)
Recently uploaded
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Recently uploaded (20)
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
My electronic gadget
- 1. MY ELECTRONIC GADGETS PC ,MOBILES AND TABLETS QUADCOPTER WIRELESS 3D FINGER MOUSE Exhale fan(bladeless fan) WI-FI SMART CONTROL LASER VIRTUAL PROJECTION KEYBOARD
- 2. How to opt a good electronic gadget ? How to opt a better mobile ? How to opt a best laptop ? Best laptop under 35000 /- Protecting your gadget from virus Main objectives :
- 3. OPTING A GOOD ELECTRONIC GADGET 5 Things that to be observed while opting an electronic gadget 1. Check the Calendar 2. Check Reviews 3. Life expectancy (efficiency) 4. Beware of Online Scammers 5. Re-check
- 4. Opting a better mobile 1. Operating system 2. Ram 3. External memory ( SD/DDR CARD) 4. mAh (milli amp-hour)
- 5. Best operating system 9 Popular Mobile Operating Systems : • Android OS (Google Inc.) • Bada (Samsung Electronics) • BlackBerry OS (Research In Motion) • iPhone OS / iOS (Apple) • MeeGo OS (Nokia and Intel) • Palm OS (Garnet OS) • Windows Mobile (Windows Phone 7)
- 7. How to opt a best laptop ??? 1. Operating system 2. Processor 3. Ram size 4. Hard disk size 5. Battery life (mAh)
- 8. Operating system a collection of programs which control the resources of a computer system written in low-level languages (i.e. machine- dependent) an interface between the users and the hardware when the computer is on, OS will first load into the main memory
- 9. processor Definition : A machine that processes something (DATA) BEST PROCESSORS Platform Google Chrome OS Windows 10 Processor Name Intel Celeron N3160 Intel Core i5- 6200U Processor Speed 1.6 GHz 2.3 GHz RAM 4 GB 8 GB Graphics Card Intel GMA HD 3150 Intel HD Graphics 520
- 10. RAM RAM : RAM (pronounced ramm) is an acronym for random access memory, a type of computer memory that can be accessed randomly Robert Dennard was the inventor of ram: random access memory, the device was patented in 1968 by Dennard. Jay Forrester was a pioneer in early digital computer development and invented random-access, coincident-current magnetic storage Robert Dennard Dennard. Jay Forrester
- 11. HARD DISK DEFINITION : A hard disk drive (HDD), hard disk, hard drive or fixed disk is a data storage device used for storing and retrieving digital information using one or more rigid ("hard") rapidly rotating disks (platters) coated with magnetic material. The IBM 350 Disk File, invented by Reynold Johnson, was introduced in 1956 with the IBM 305 RAMAC computer. This drive had fifty 24- inch (0.6 m) platters, with a total capacity of five million 6-bit characters (3.75 megabytes) A partially disassembled IBM 350 Reynold Johnson,
- 12. 10 Best Laptop Under 35000/- Specifications : Intel core i5 processor 1TeraByte hard drive 4GB RAM 2GB graphics card and operating system HP 15-AC120TX Laptop Acer Aspire E5 Laptop Under 35000 with i5 Processor Lenovo G50-45 Laptop Acer Aspire E5 E5- 573-587Q Notebook
- 13. Protecting laptop from virus virus : A computer virus is a type of malicious software program ("malware") that, when executed, replicates by reproducing itself (copying its own source code) or infecting other computer programs by modifying them. Infecting computer programs can include as well, data files, or the "boot" sector of the hard drive. How does a computer get infected with a virus or spyware? • Accepting without reading • Downloading any infected software• Inserting or connecting an infected disk, disc, or drive • Not running the latest updates • Pirating software, music, or movies • No antivirus spyware scanner
- 14. Best Anti-virus software 2016 Free anti-virus • Avira Free Antivirus • Bitdefender Antivirus Free Edition • AVG AntiVirus Free 2016 Paid anti-virus • Bit defender Antivirus • Kaspersky antivirus • Norton antivirus
- 15. Cleaning temp. files in p.c Press + R Type • temp • %temp% • prefetch • Cookies • Cleanmgr.exe And press