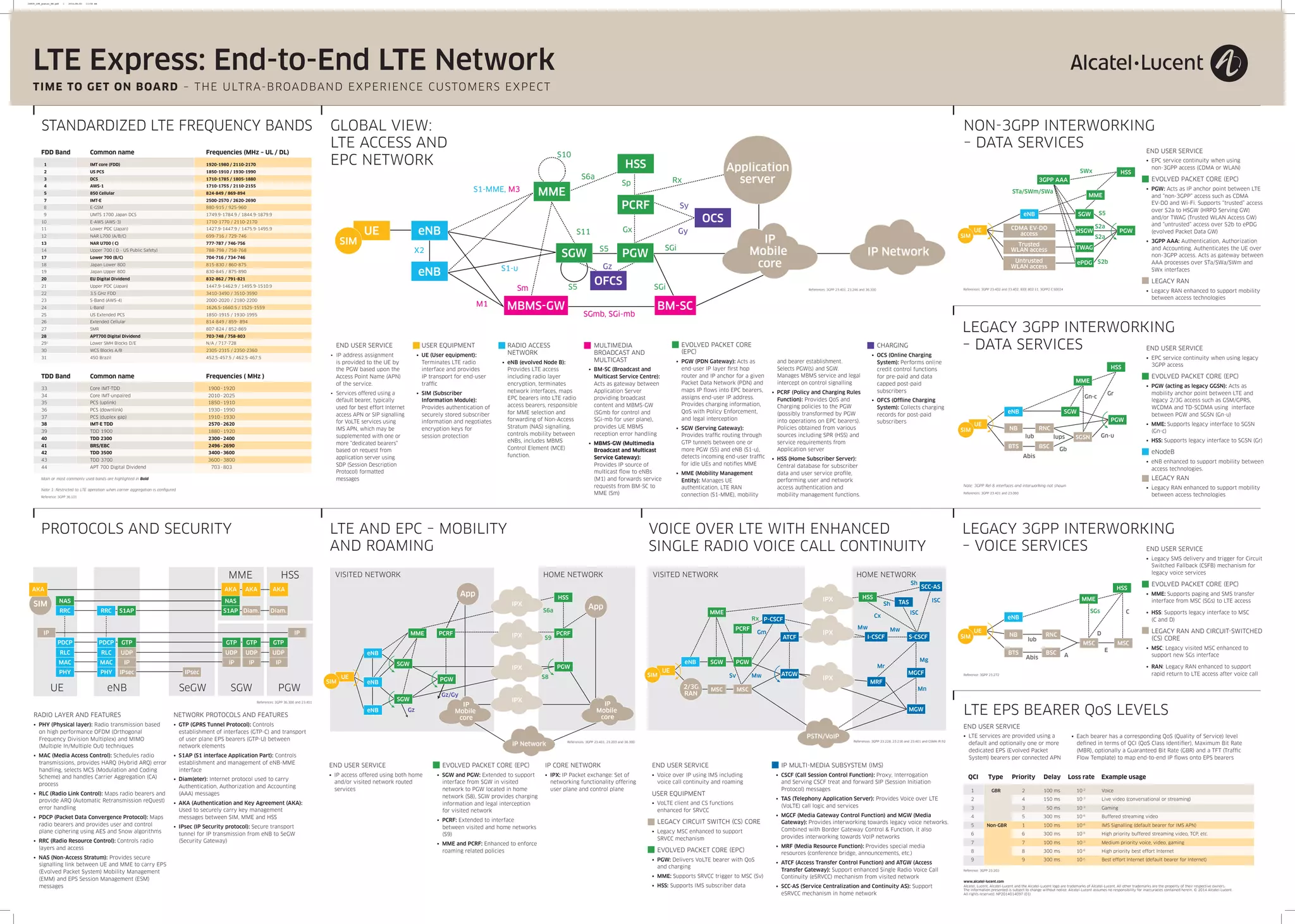
The document provides an overview of an LTE network including:
1) The key components of an LTE network including the Evolved Packet Core (EPC), radio access network (eNodeB), and user equipment (UE).
2) Protocols and functions used within the LTE network for mobility, authentication, quality of service, charging, and multimedia services.
3) Interworking of the LTE network with external networks including legacy 3G networks, non-3GPP access like WiFi, IP Multimedia Subsystem (IMS) for voice, and IPX networks for roaming.