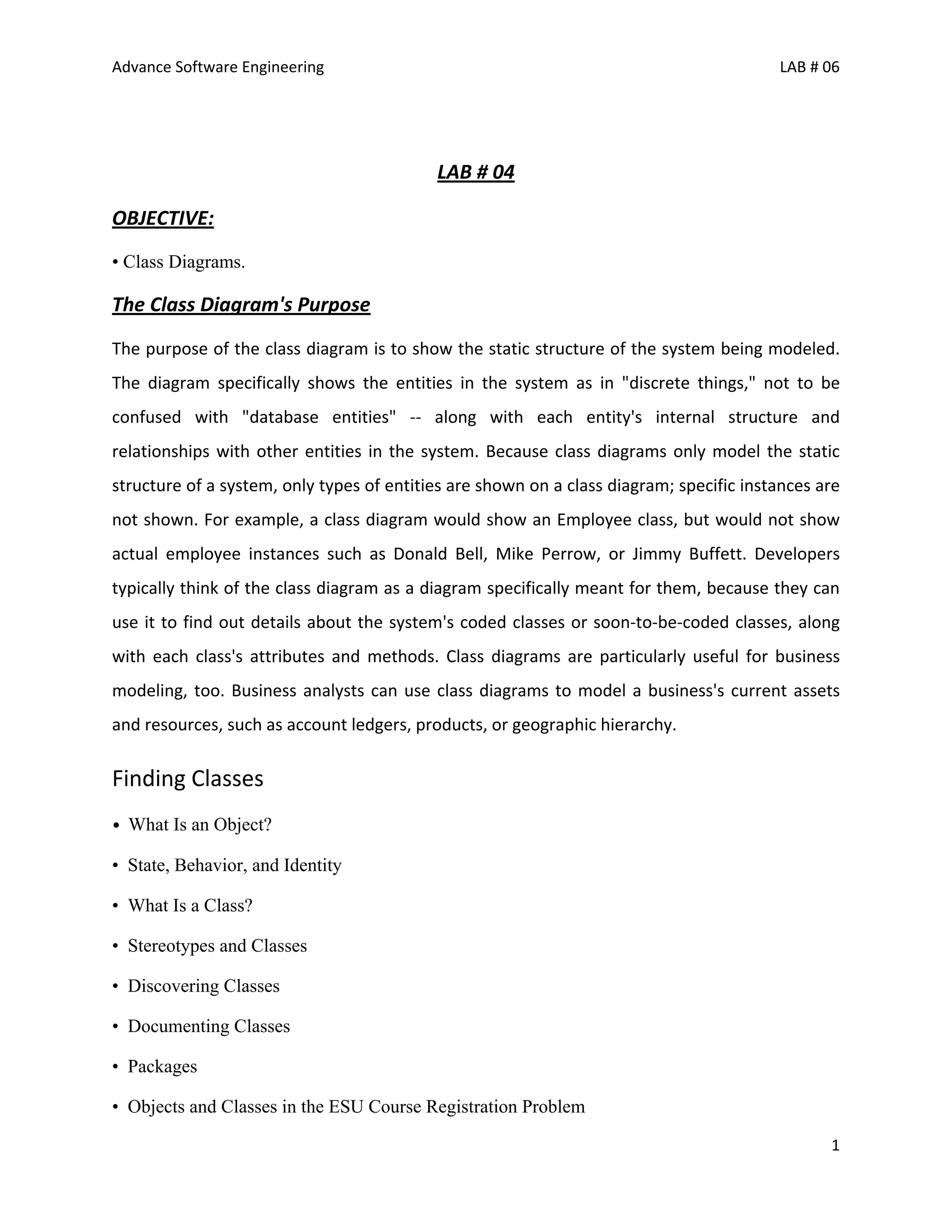
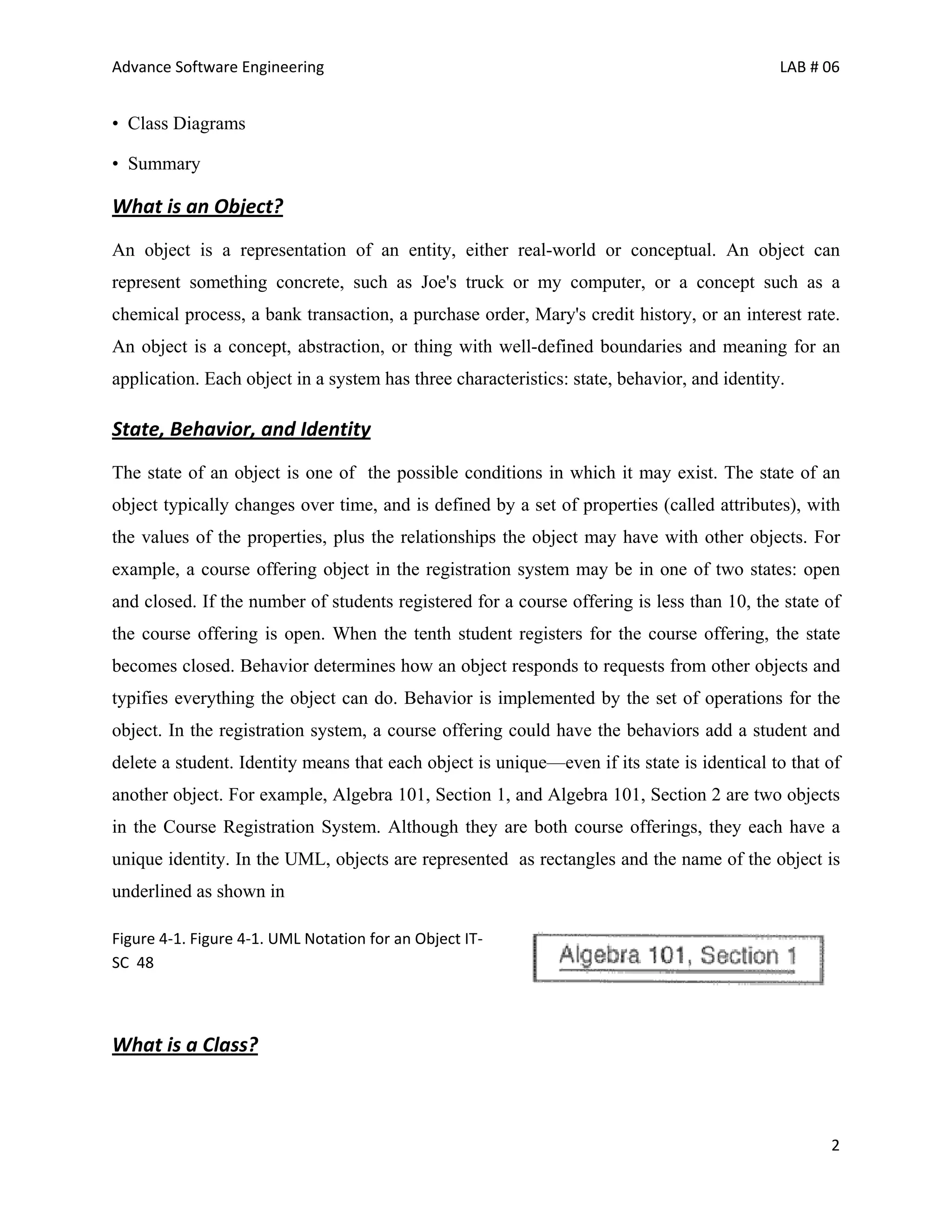
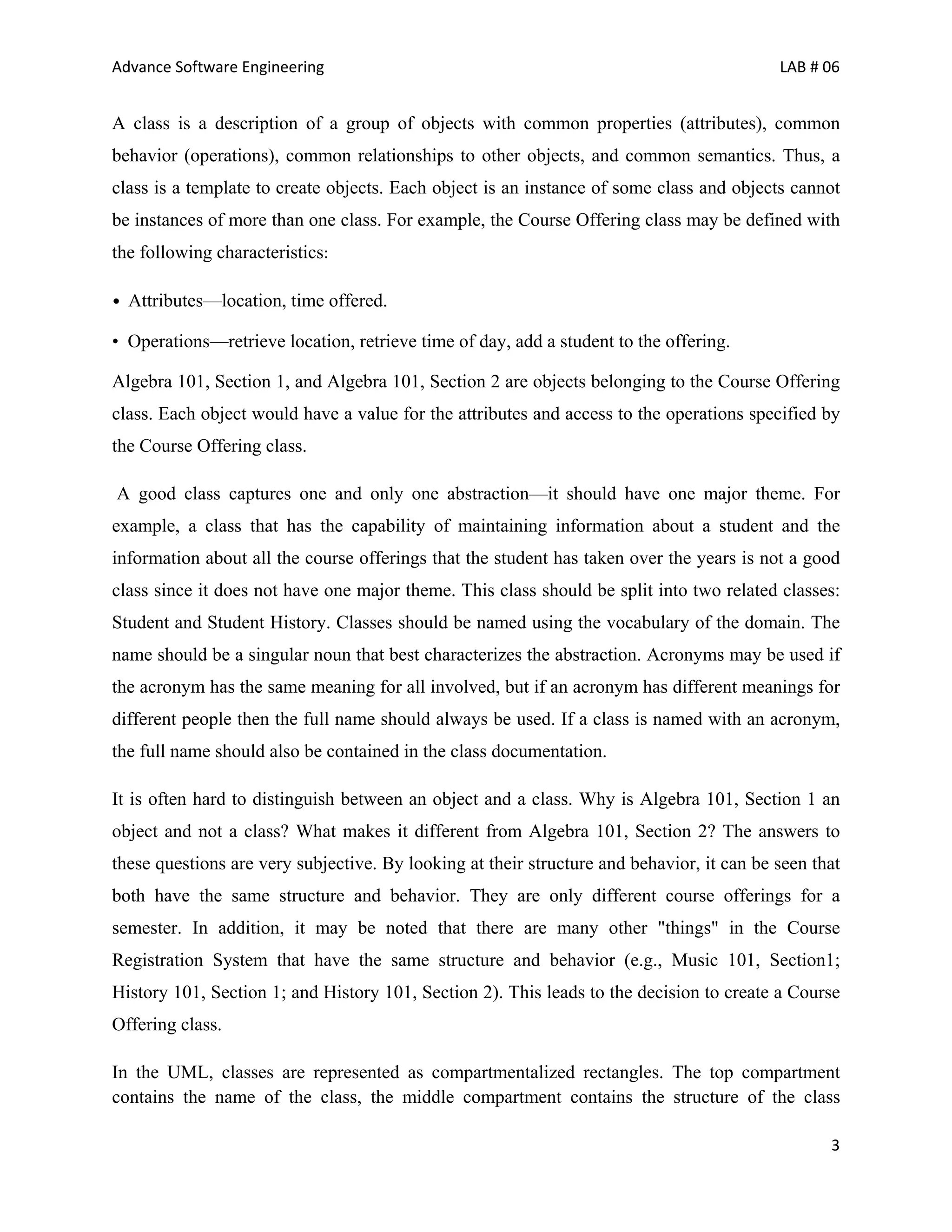
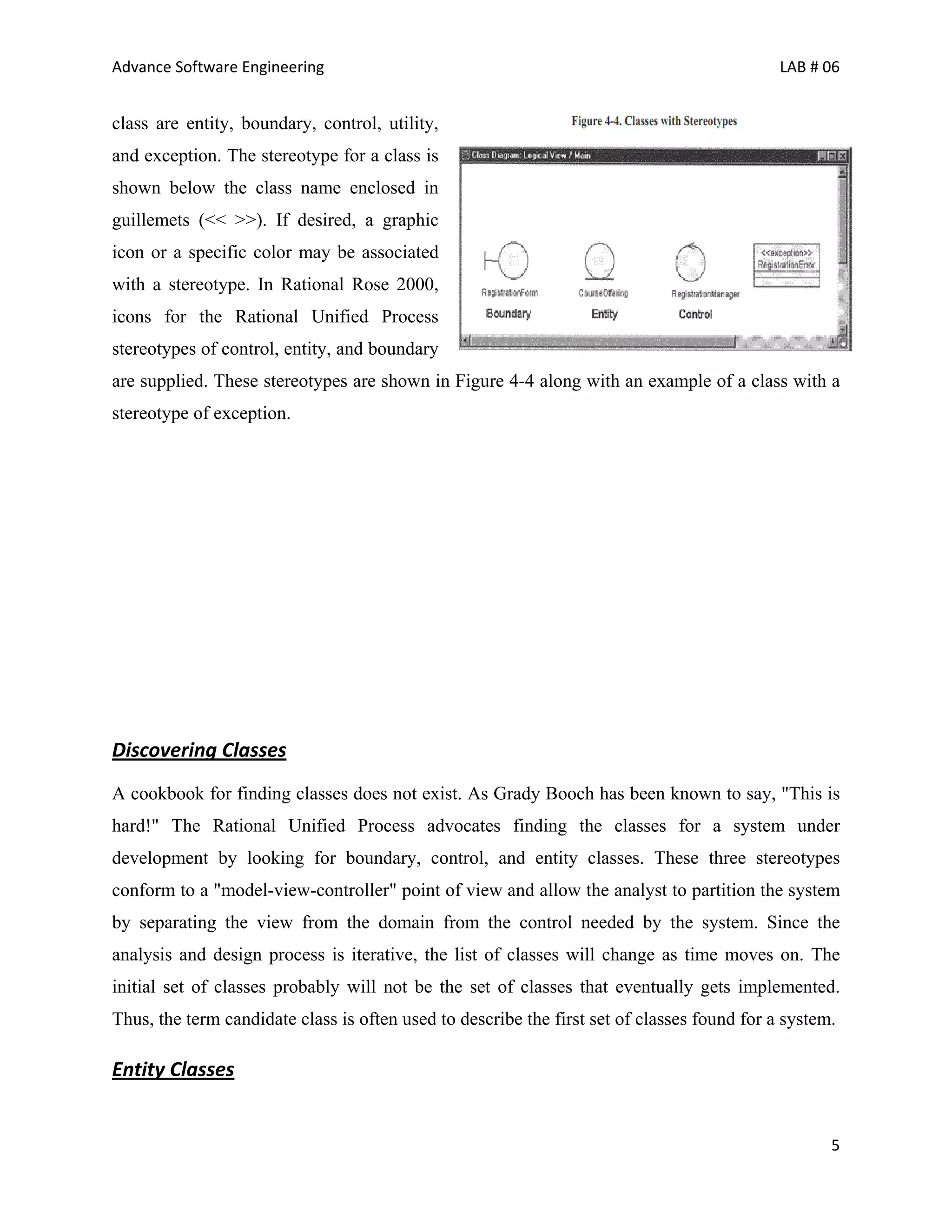
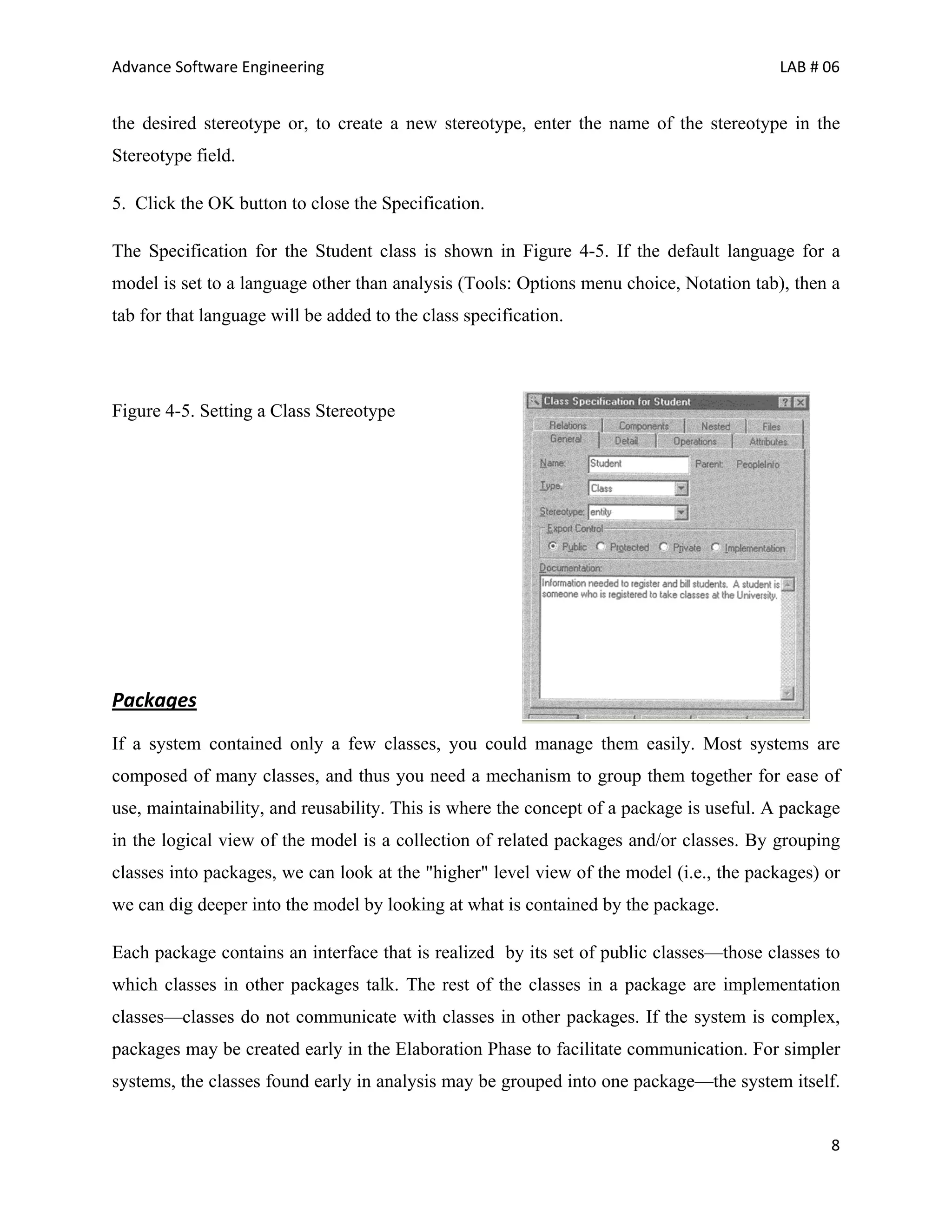
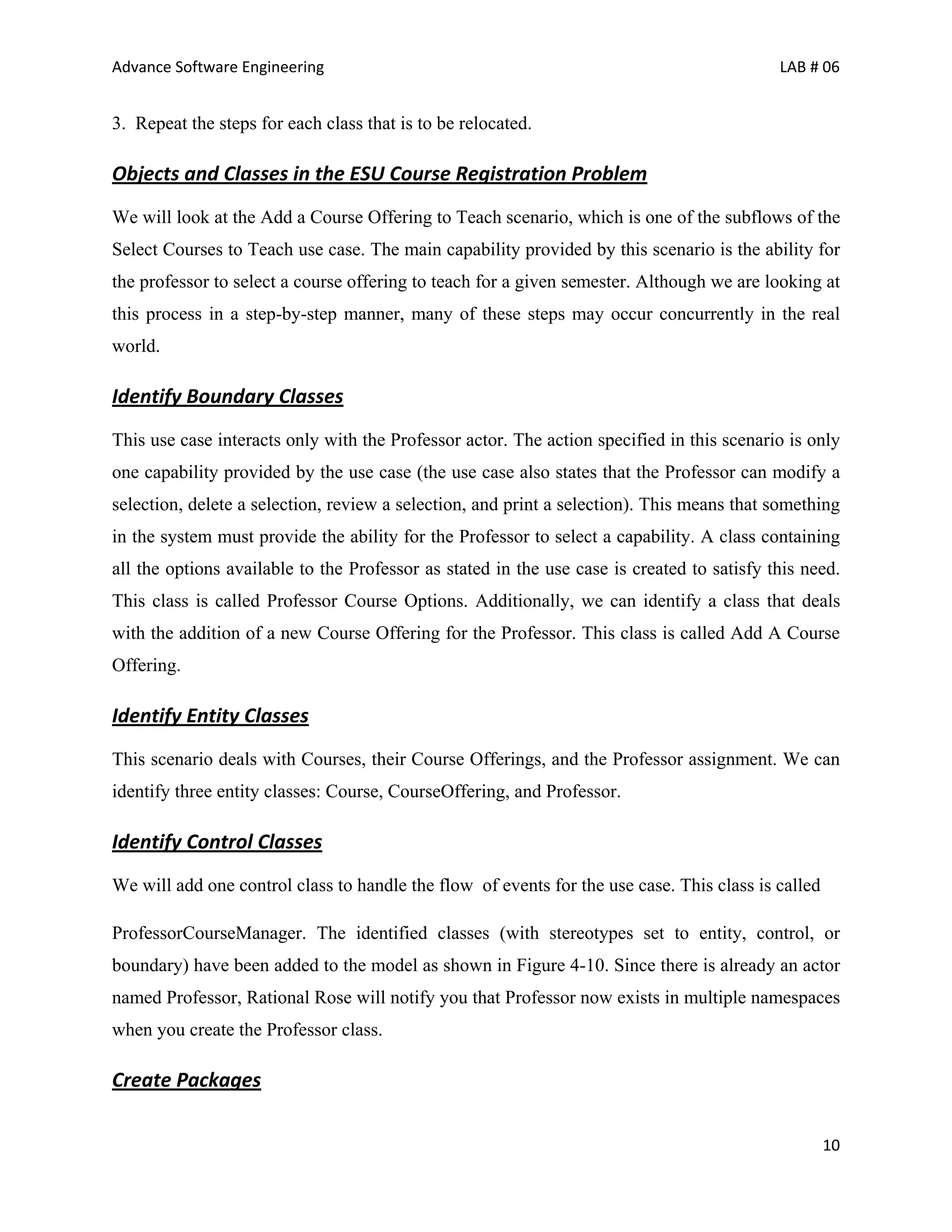
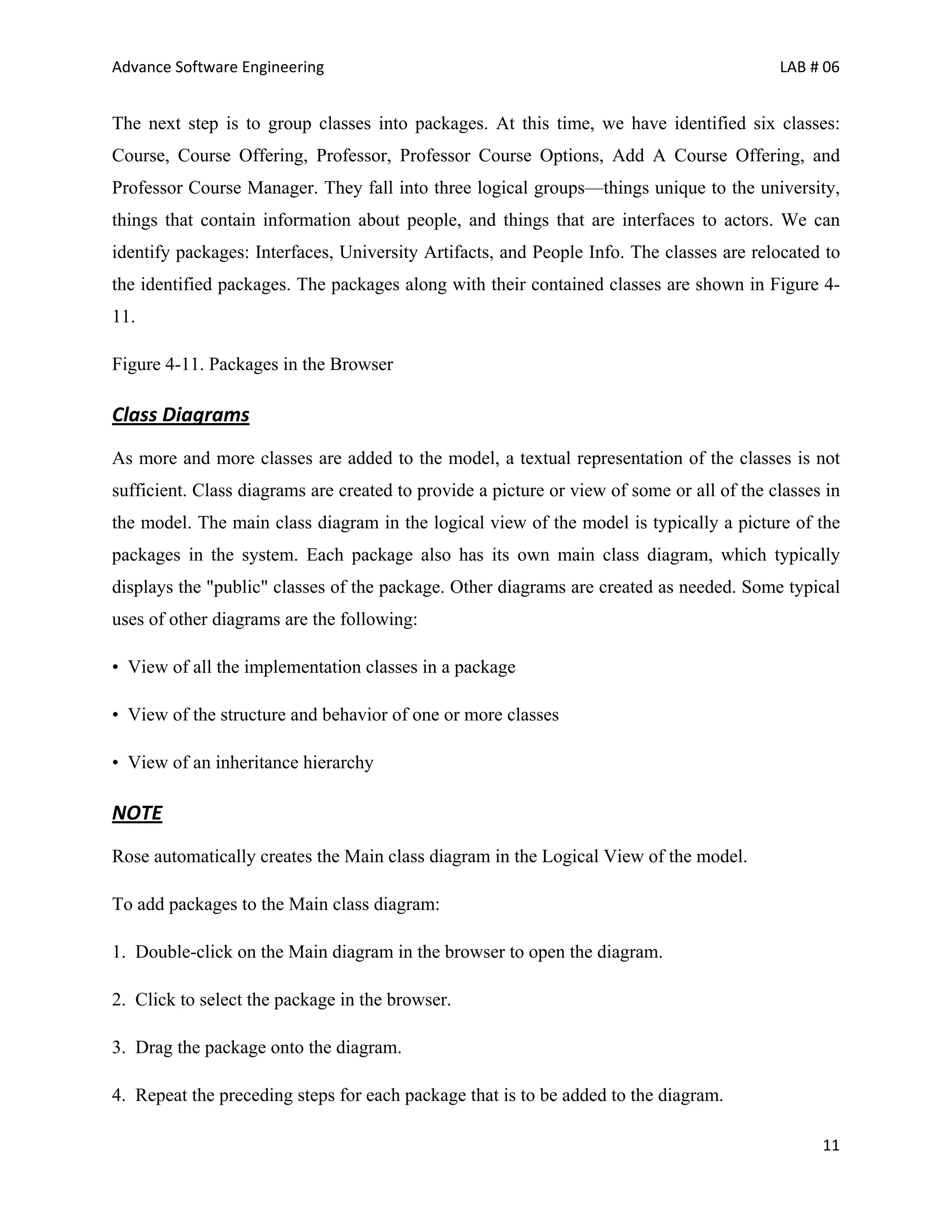
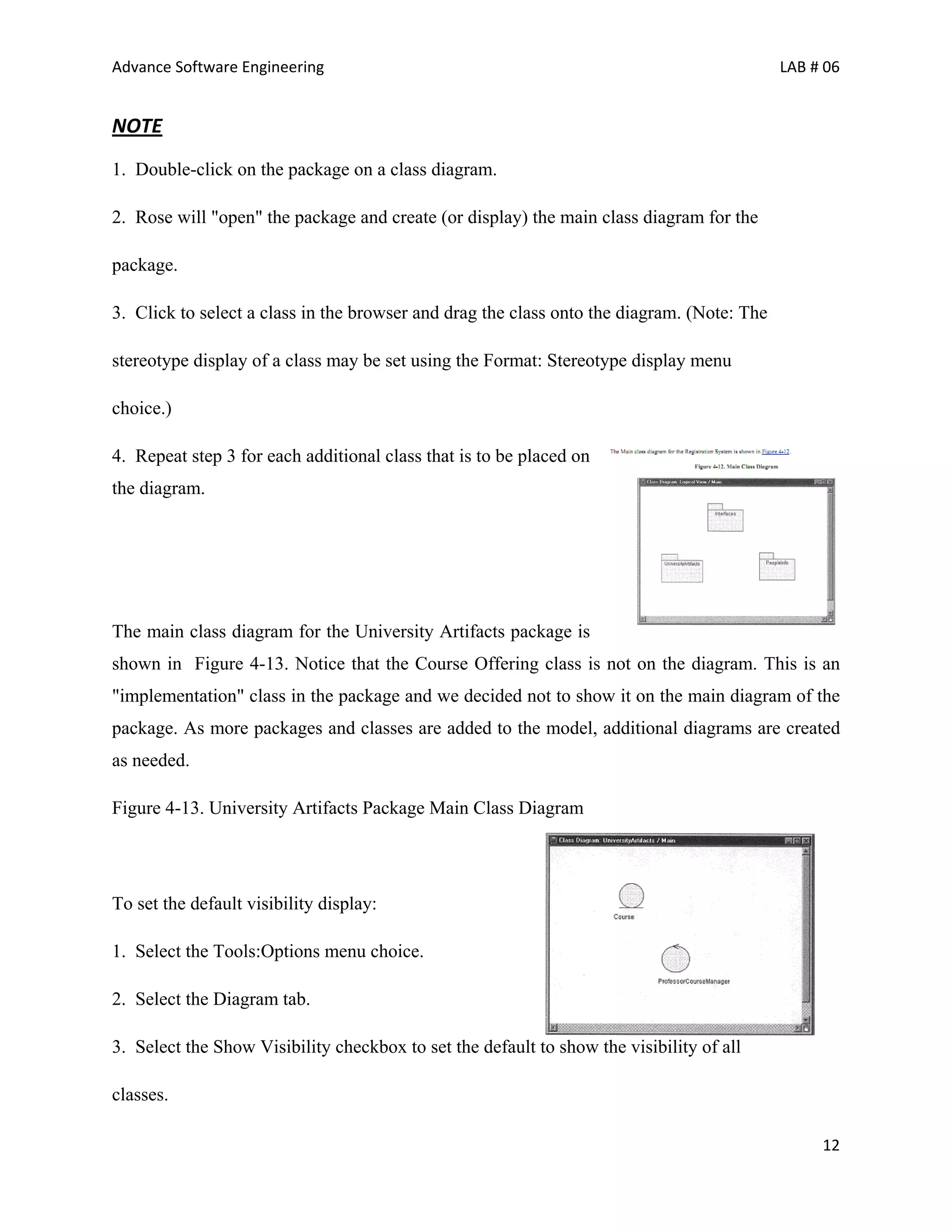
The document discusses class diagrams and how to identify classes in object-oriented analysis and design. It defines key concepts like objects, classes, state, behavior, and identity. It explains that a class is a template for creating objects that share attributes and behaviors. The document provides guidelines for discovering different types of classes, specifically entity classes, boundary classes, and control classes. It also discusses stereotypes that can be applied to classes.