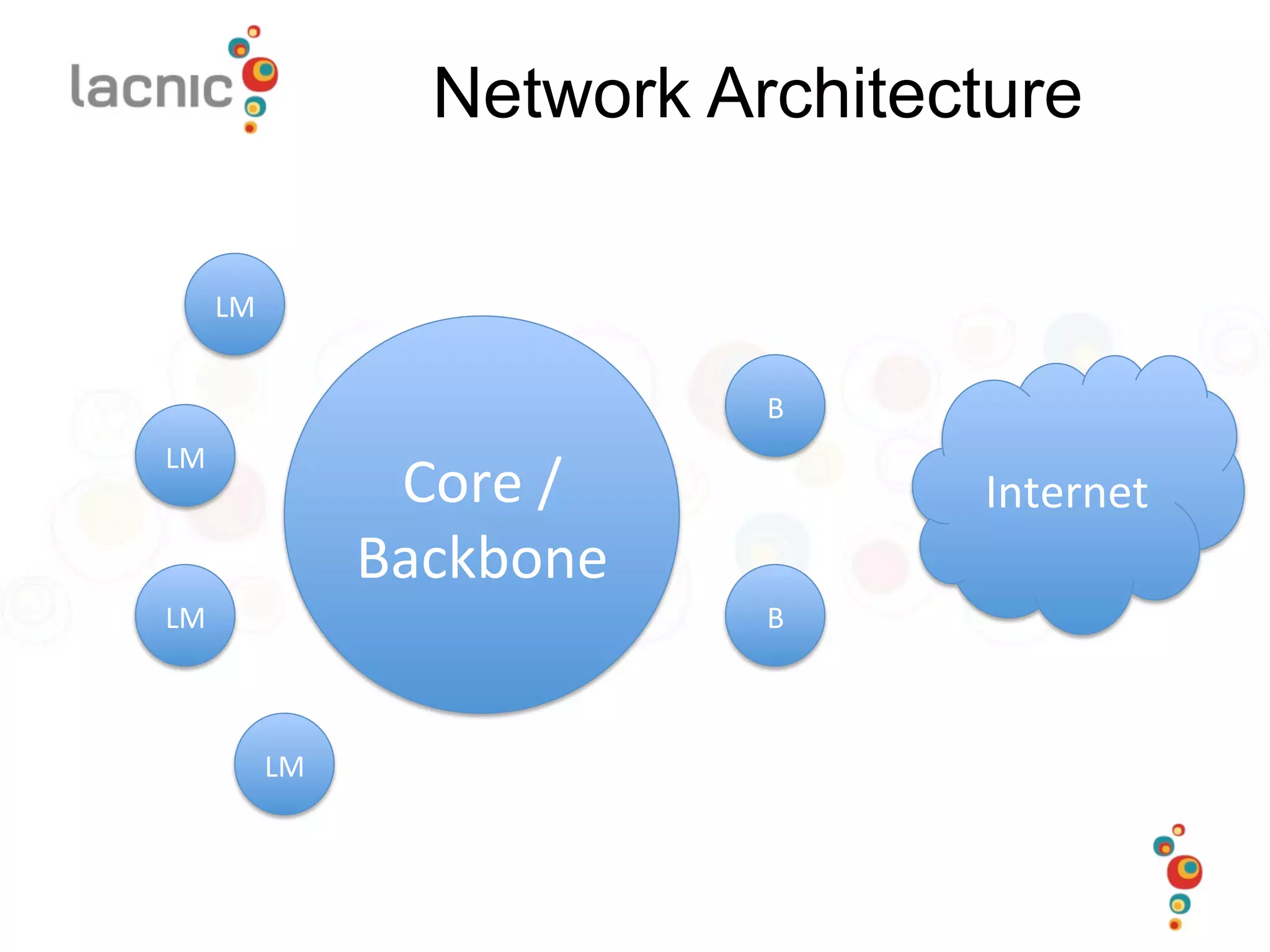
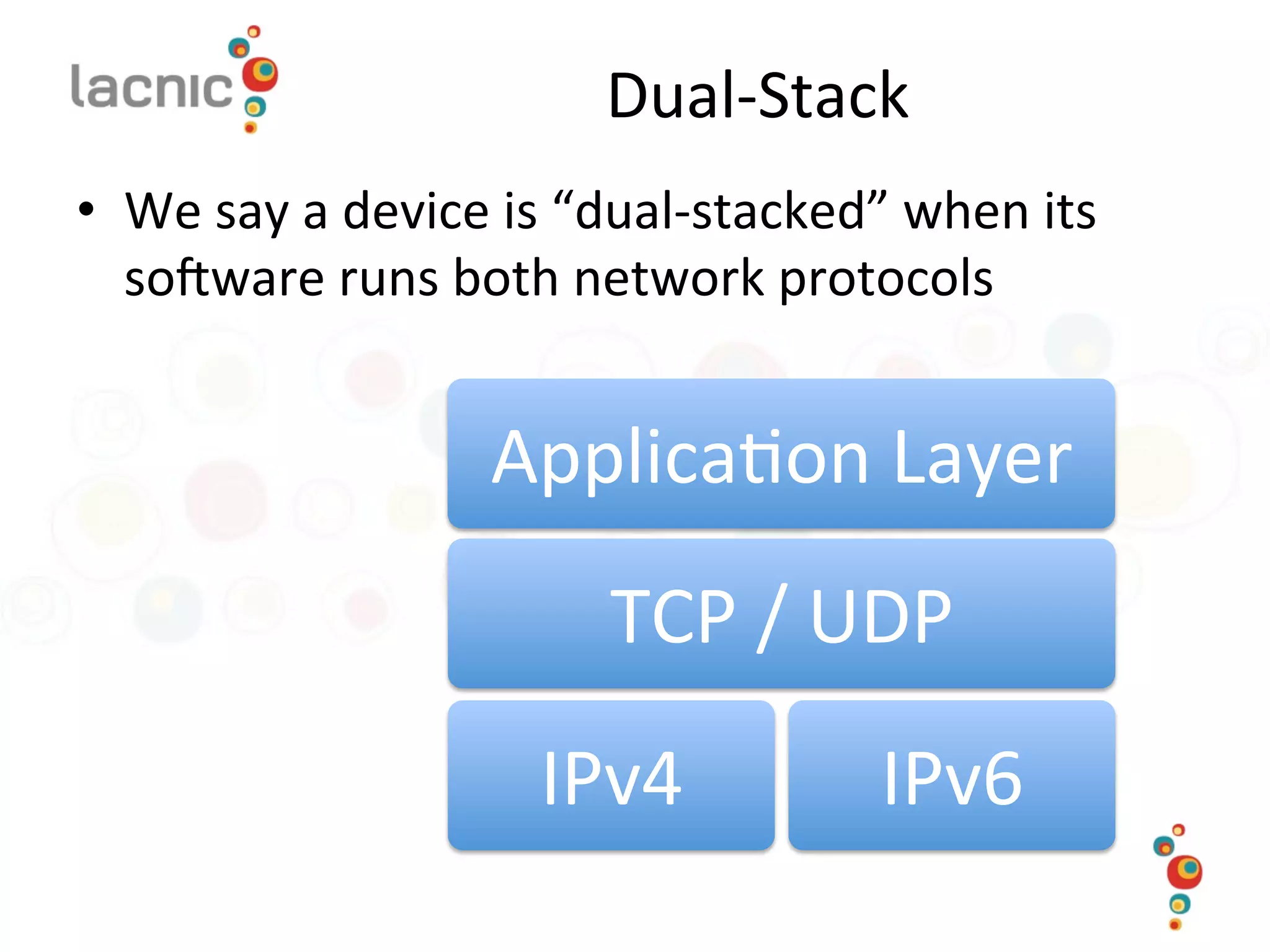
This document discusses considerations for internet service providers transitioning to IPv6. It covers common network architectural patterns like core/backbone, last mile, and border networks. It also discusses transition approaches like dual-stack and tunneling. The document outlines a multi-phase transition plan including obtaining IPv6 address space, setting up a testbed, enabling IPv6 routing and services, and addressing security considerations during the rollout.