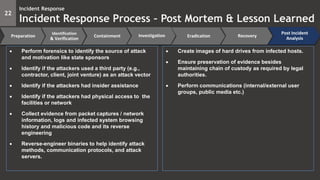
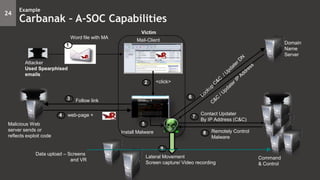
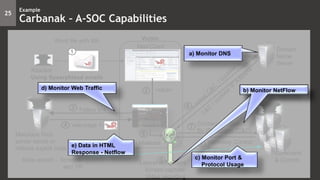
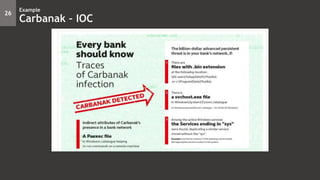
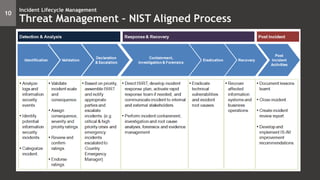
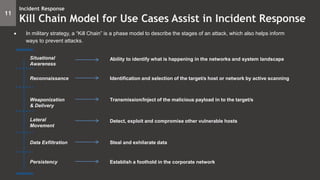
The document outlines an advanced Security Operations Center (SOC) framework focused on incident response and management, detailing the incident response lifecycle, including stages like reconnaissance, containment, eradication, recovery, and post-incident analysis. It emphasizes the importance of situational awareness and provides a structured kill chain model to identify threats and remediate incidents effectively. Additionally, the document discusses handling advanced persistent threats and offers specific procedures and rules for detecting and responding to various cyber threats.

![12
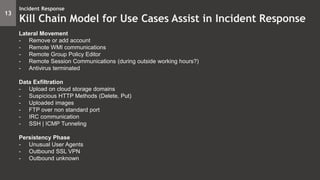
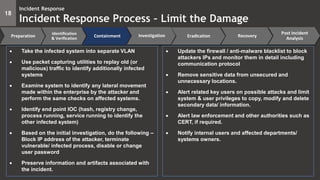
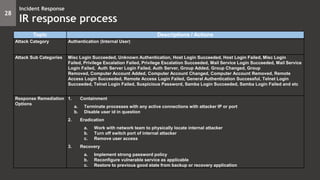
Incident Response
Kill Chain Model for Use Cases Assist in Incident Response
Situational Awareness
- Outbound Protocols
- Outbound protocols by size
- Top destination Countries
- Top destination Countries by size
Reconnaissance
- Port scan activity
- ICMP query
Weaponization and Delivery
- Injection
- Cross Site Scripting
- Cross Site Request Forgery
- Failure to Restrict URL
- Downloaded binaries
- Top email subjects
- Domains mismatching
- Malicious or anomalous Office/Java/Adobe files
- Suspicious Web pages (iframe + [pdf|html|js])](https://image.slidesharecdn.com/session8-a-socircase-2-170522123032/85/Incident-Response-Validation-Containment-Forensics-4-320.jpg)