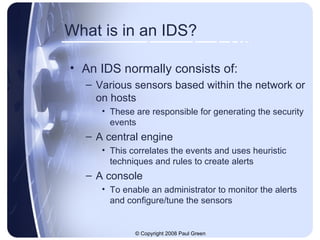
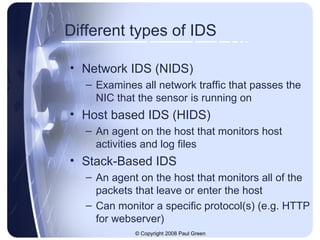
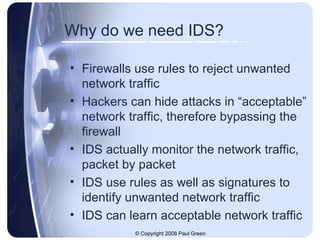
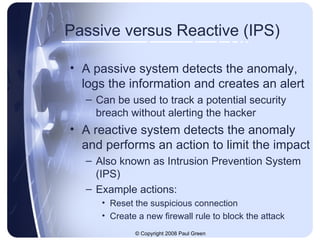
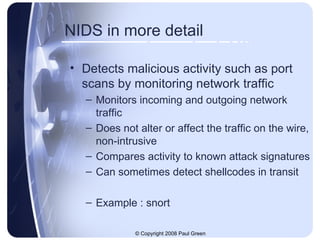
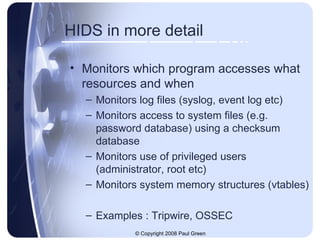
An intrusion detection system (IDS) monitors network traffic and system activities for malicious activities or policy violations. An IDS typically consists of sensors to generate security events, a central engine to correlate events and generate alerts, and a console for administrators to monitor alerts. There are different types of IDS, including network IDS that monitor network traffic, and host-based IDS that monitor activities on individual hosts. While firewalls block unwanted traffic using rules, IDS are needed to monitor for attacks hidden in acceptable traffic and help identify unwanted network traffic using signatures and anomaly detection. IDS can operate passively by detecting anomalies and logging or actively by performing actions like blocking traffic (intrusion prevention system).

![Paul Green CISSP, MACS Paul is an information security practitioner, currently residing in Brisbane, Queensland. He has worked with government and financial institutions to help them understand their information security risks and identify suitable process and technical solutions to mitigate those risks. He has experience working with authentication and access control; network security; and monitoring solutions, as well as performing information security reviews and creation of security policies. Paul may be contacted through LinkedIN or via personal email : [email_address]](https://image.slidesharecdn.com/introduction-to-intrusion-detection-systems-1229416178037248-2/85/Introduction-To-Intrusion-Detection-Systems-16-320.jpg)