This document discusses HTML forms, including:
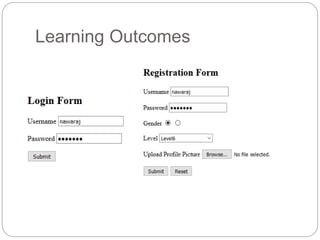
- HTML forms allow users to enter and submit data through text boxes, buttons, checkboxes, radio buttons, and other controls.
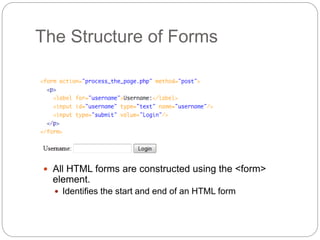
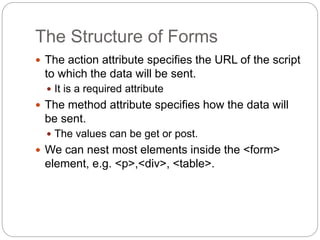
- Forms are defined using <form> tags which specify an action and method for submitting data.
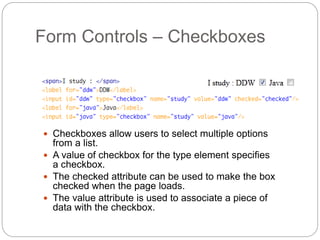
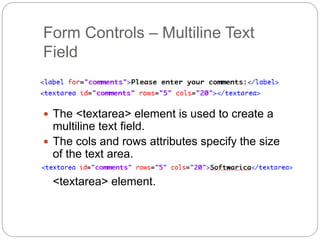
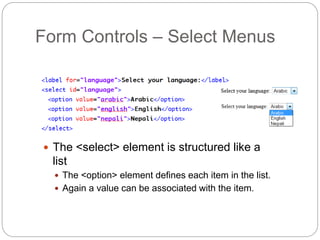
- Common form controls include text fields, passwords, checkboxes, radio buttons, buttons, textareas, and select menus.
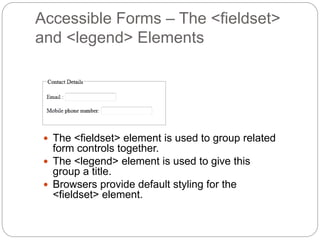
- Accessible forms should use <label> tags, <fieldset> and <legend> elements to organize groups of controls.
- CSS can style forms and individual controls using properties like :focus and outline.
- Form layout can be controlled through <br>, tables, or CSS float and clear properties.