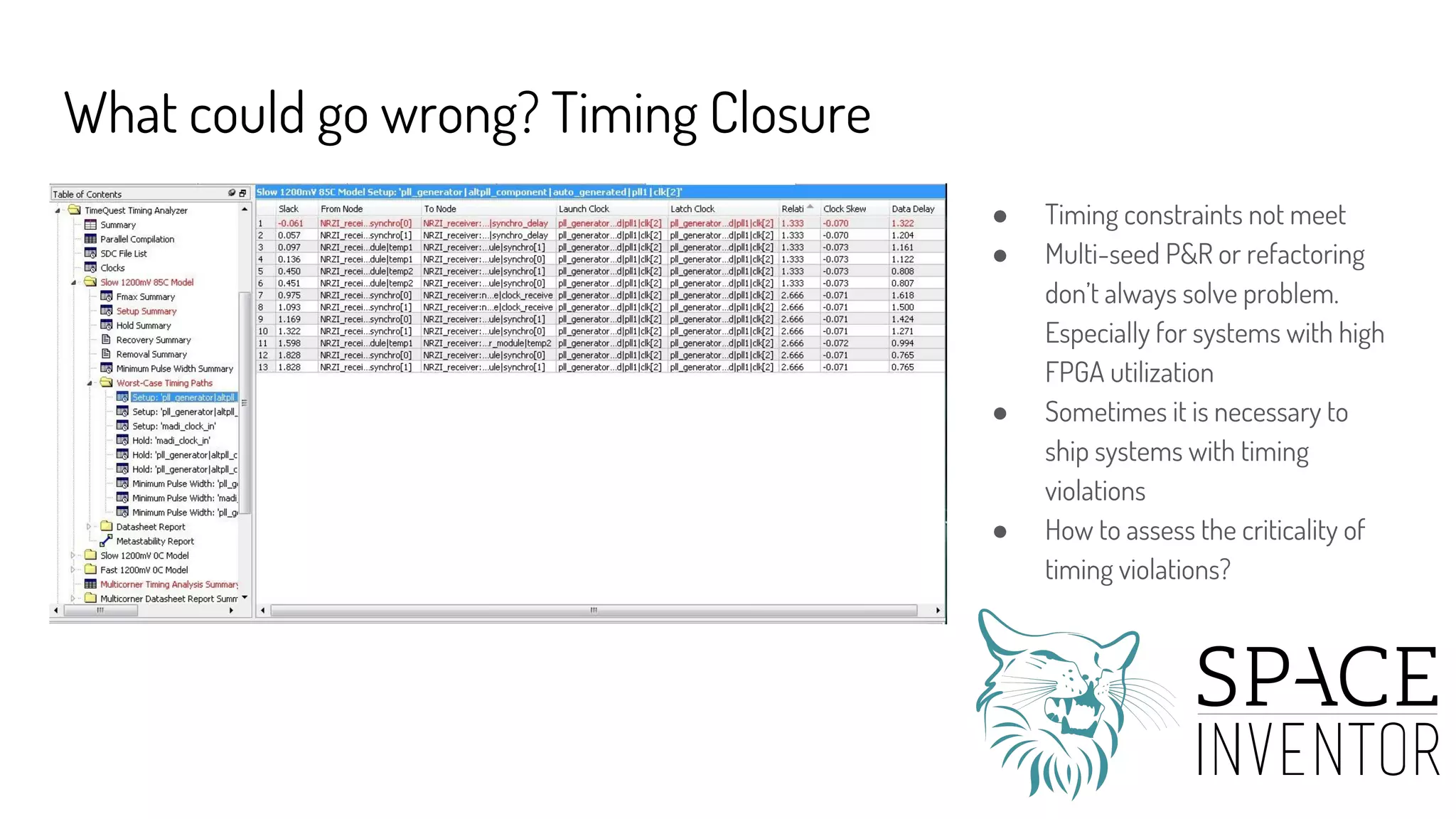
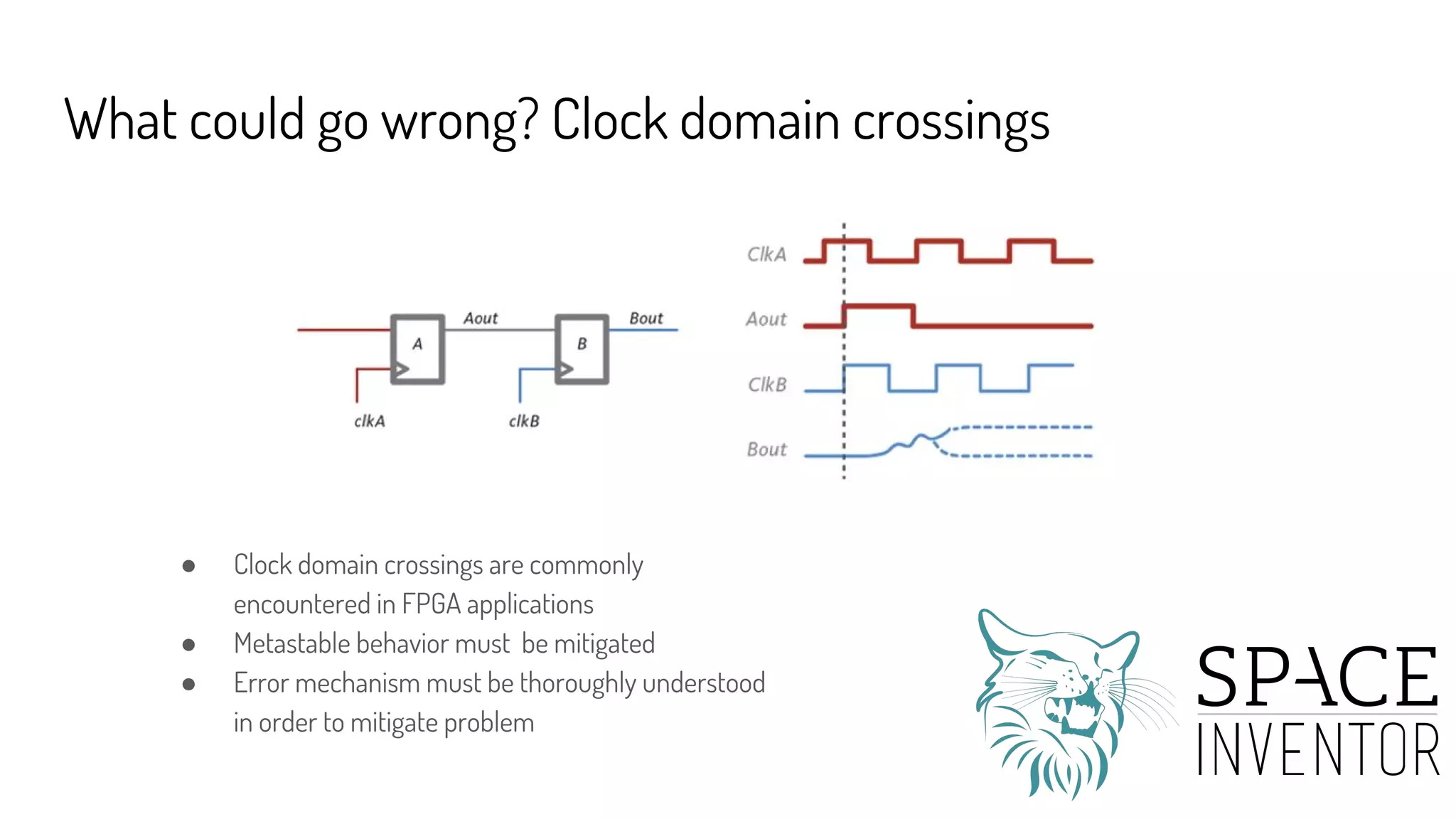
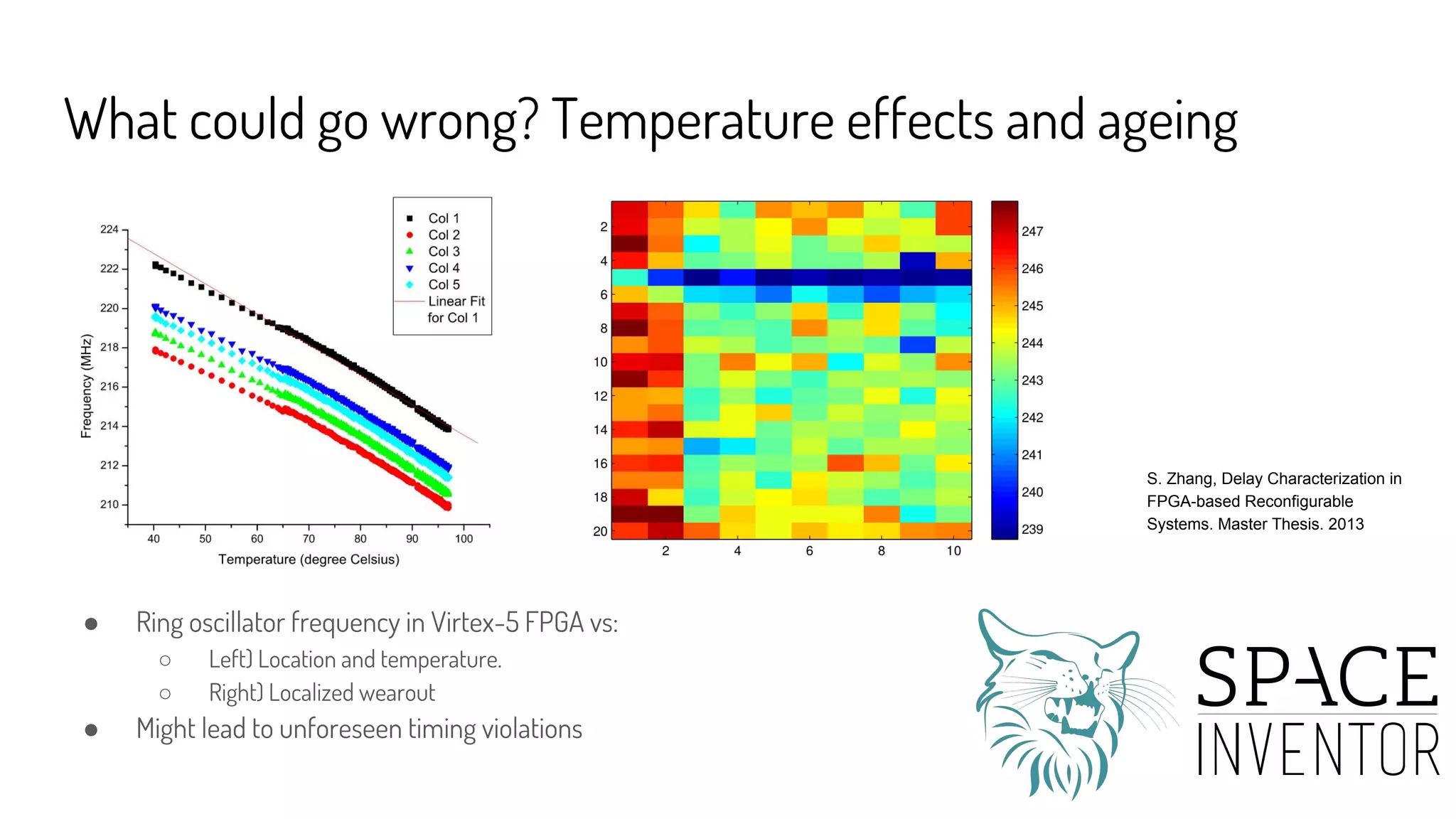
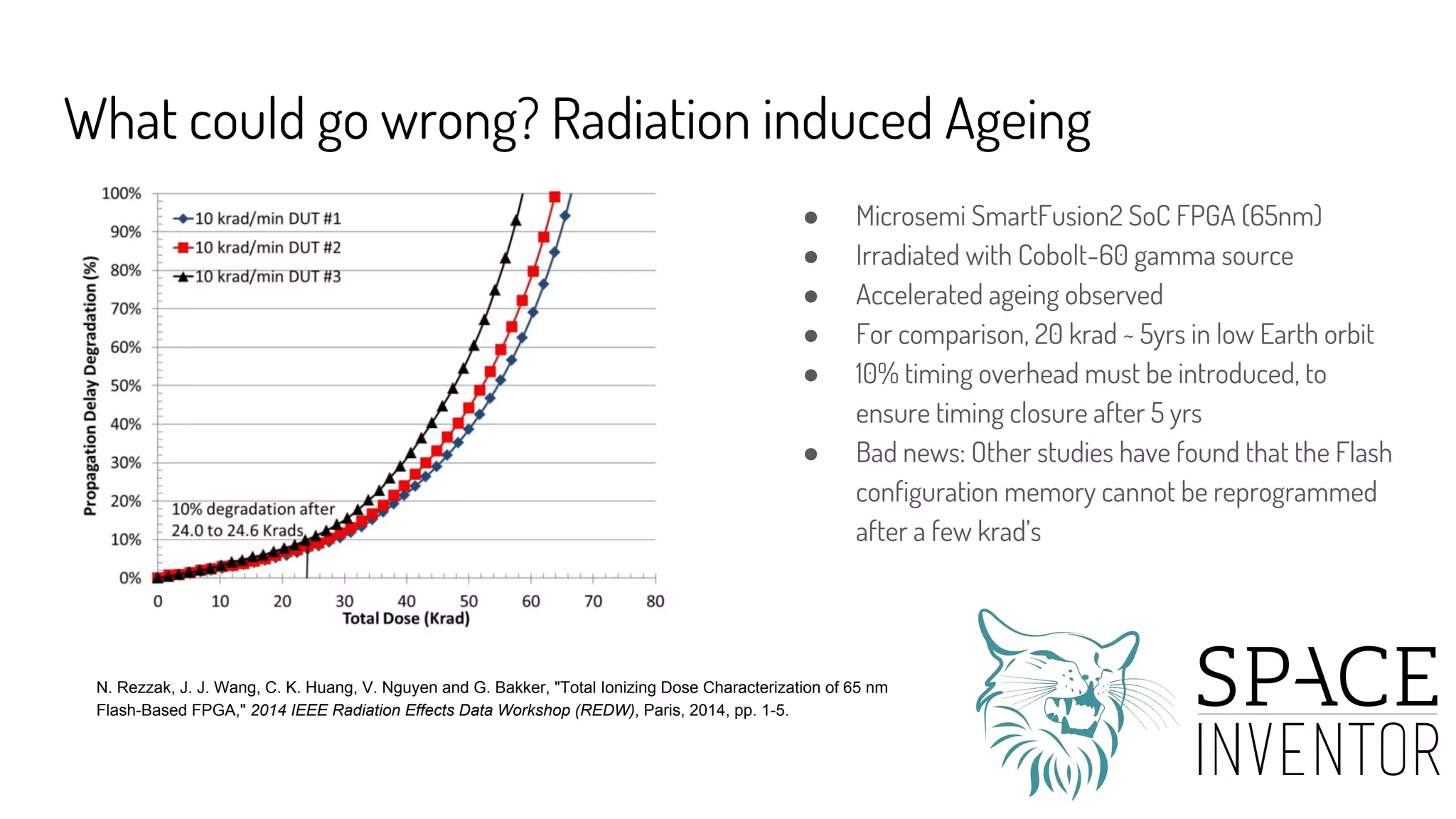
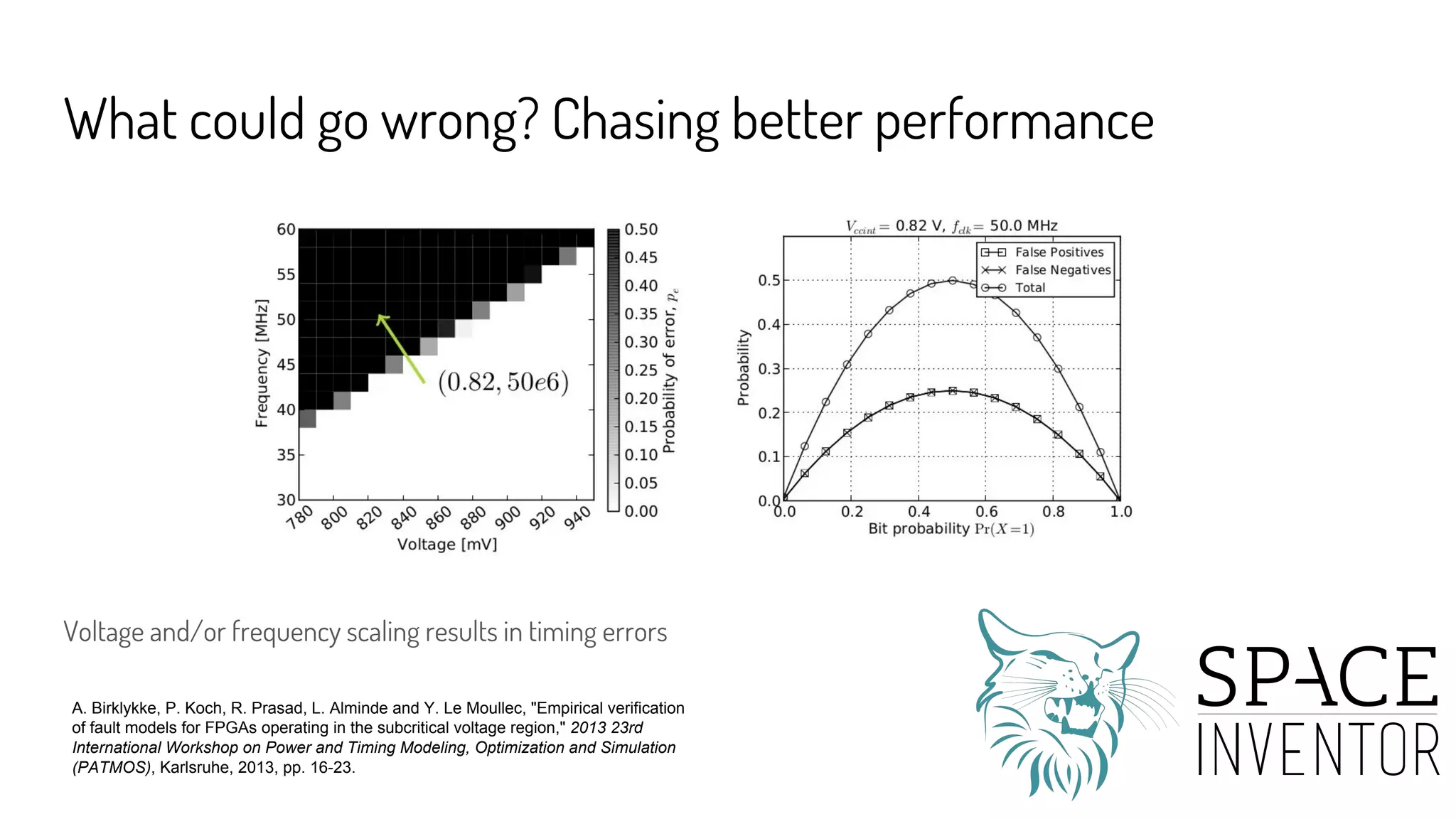
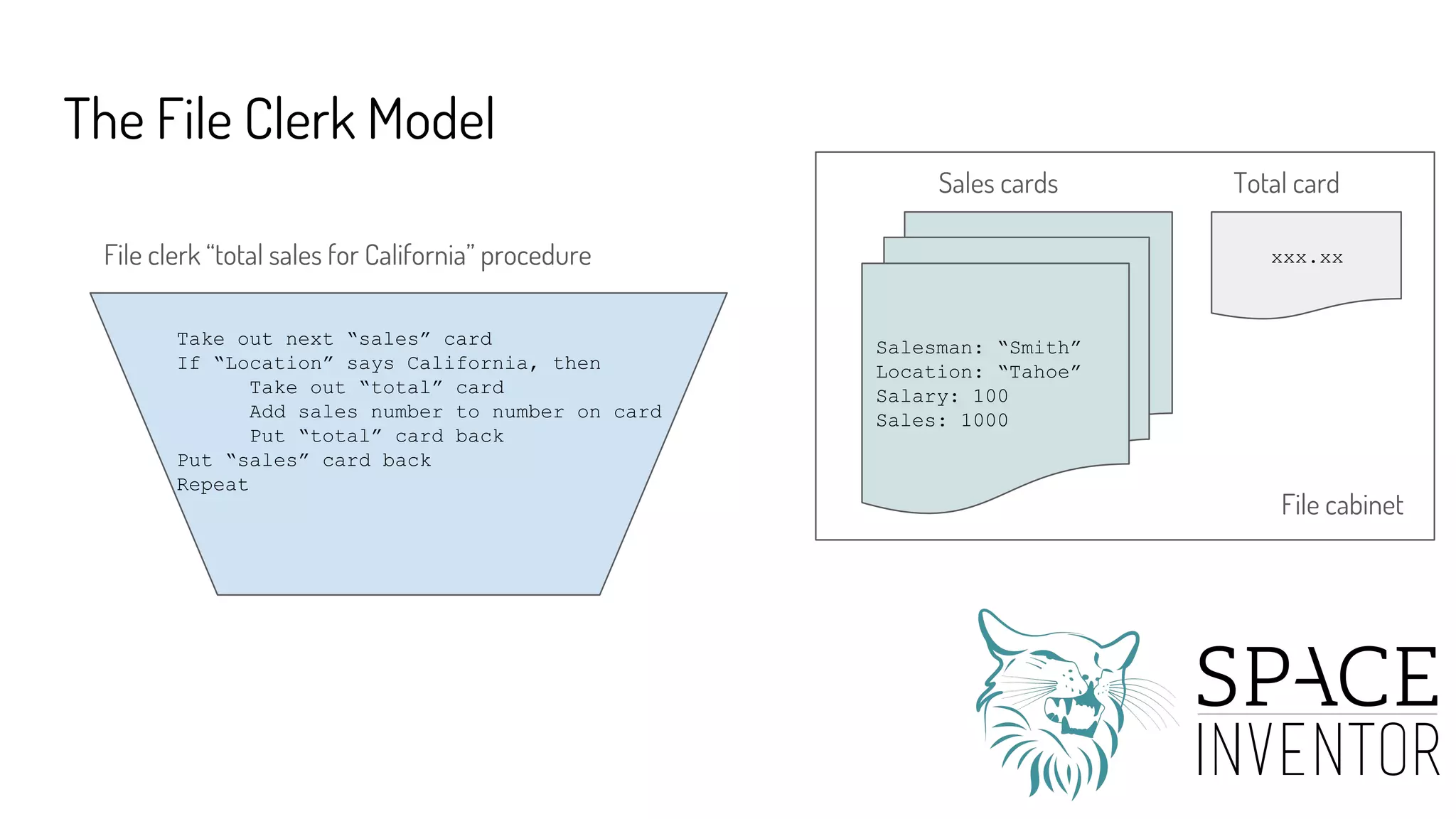
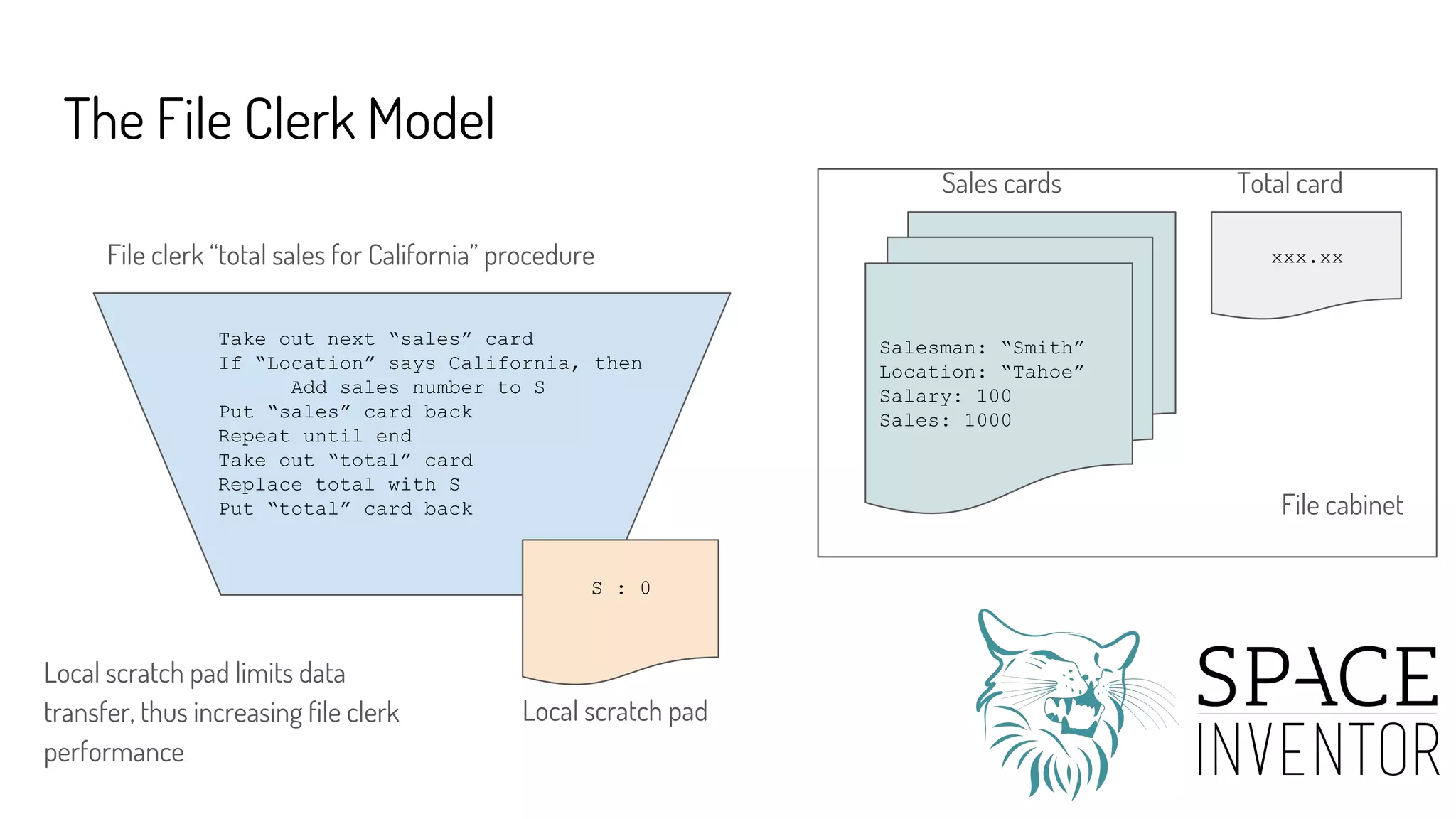
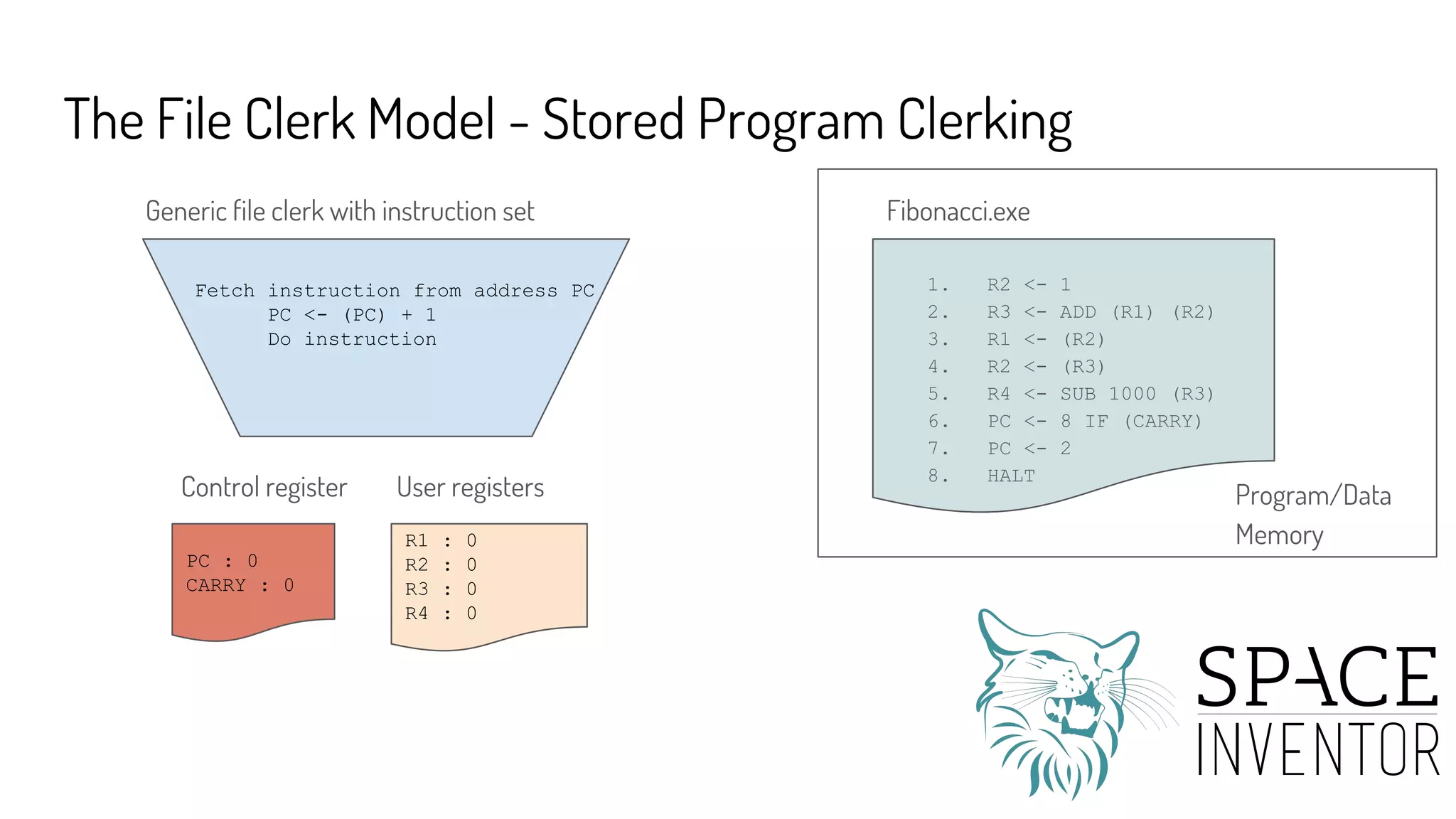
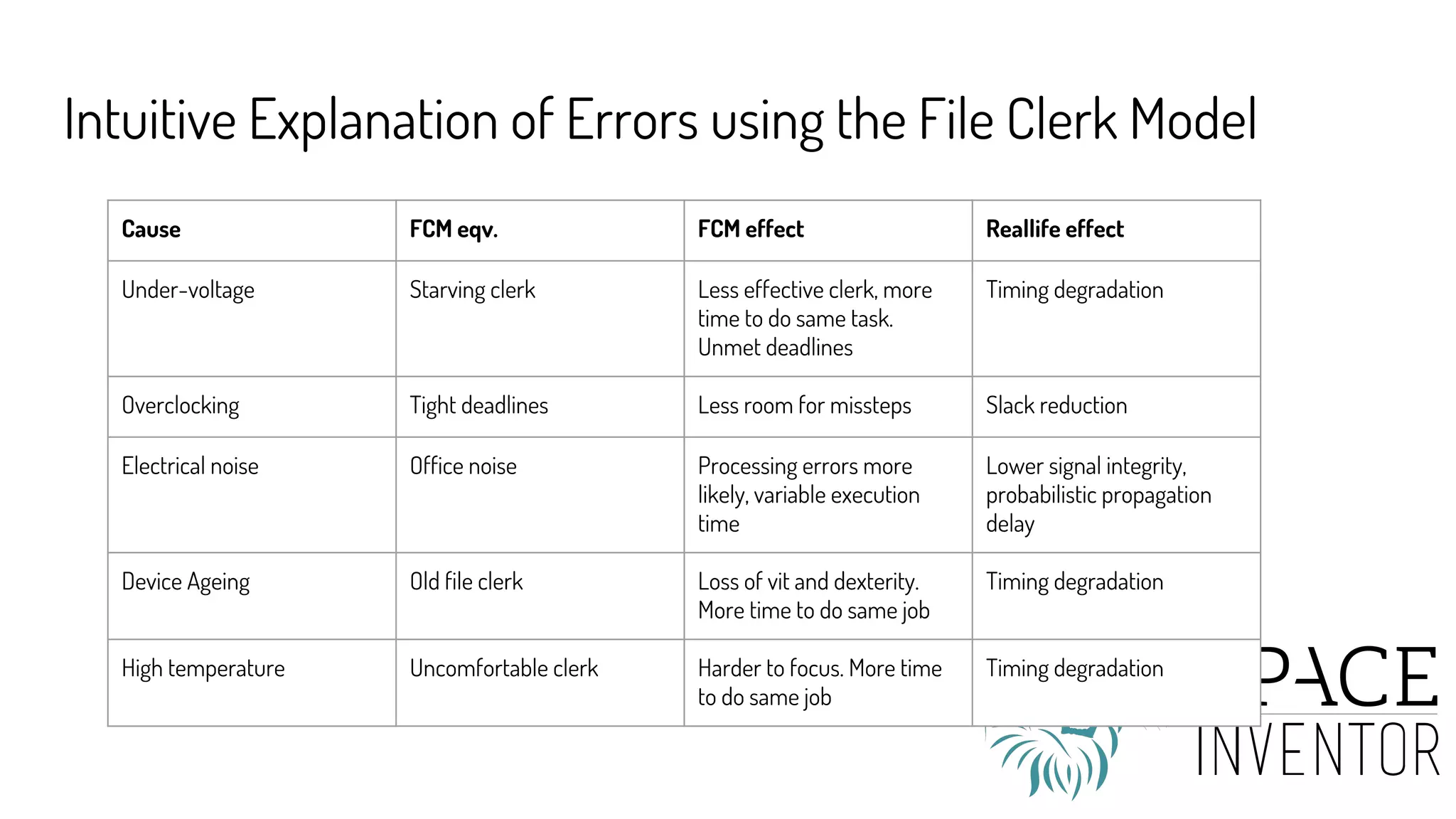
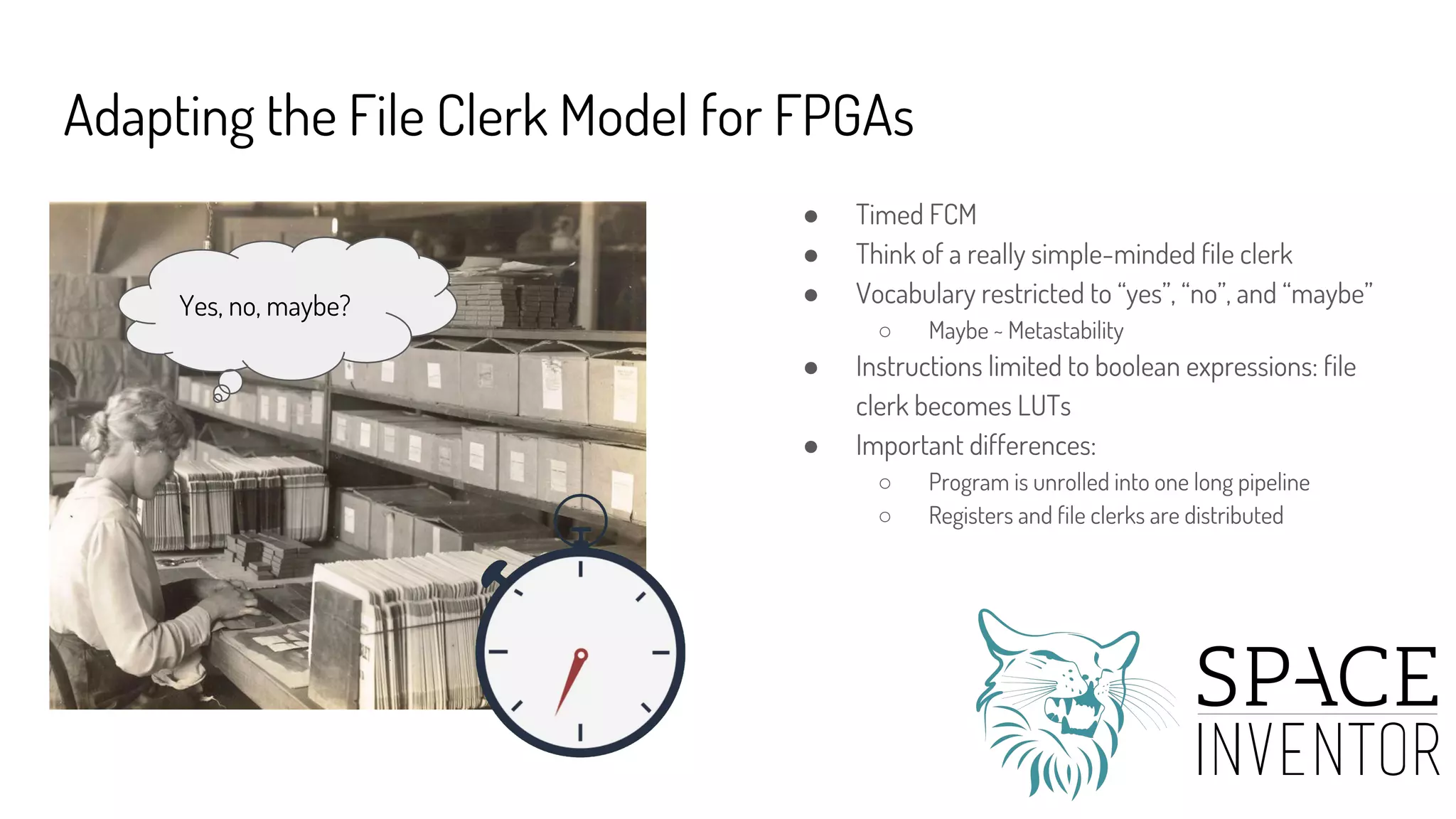
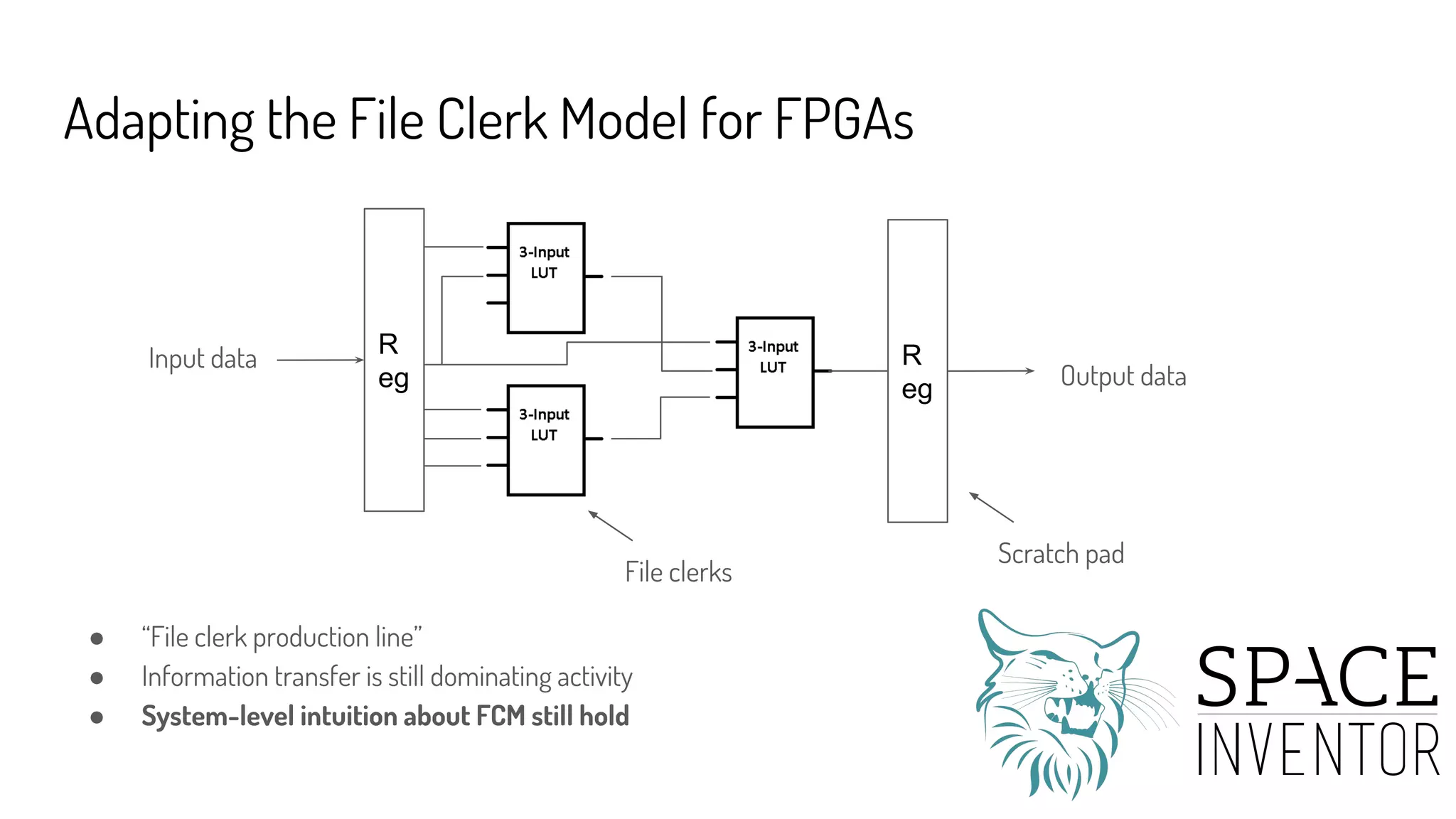
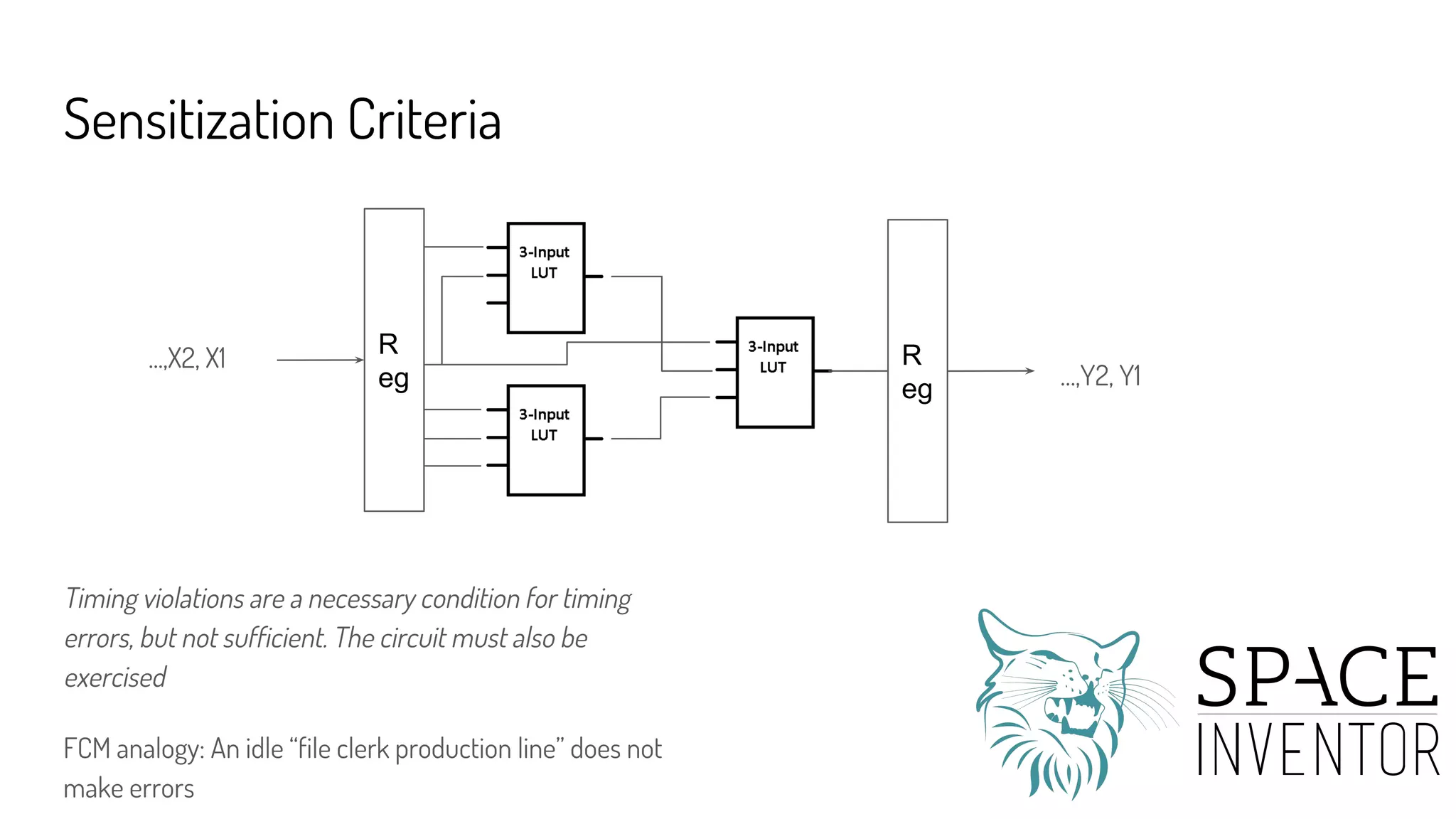
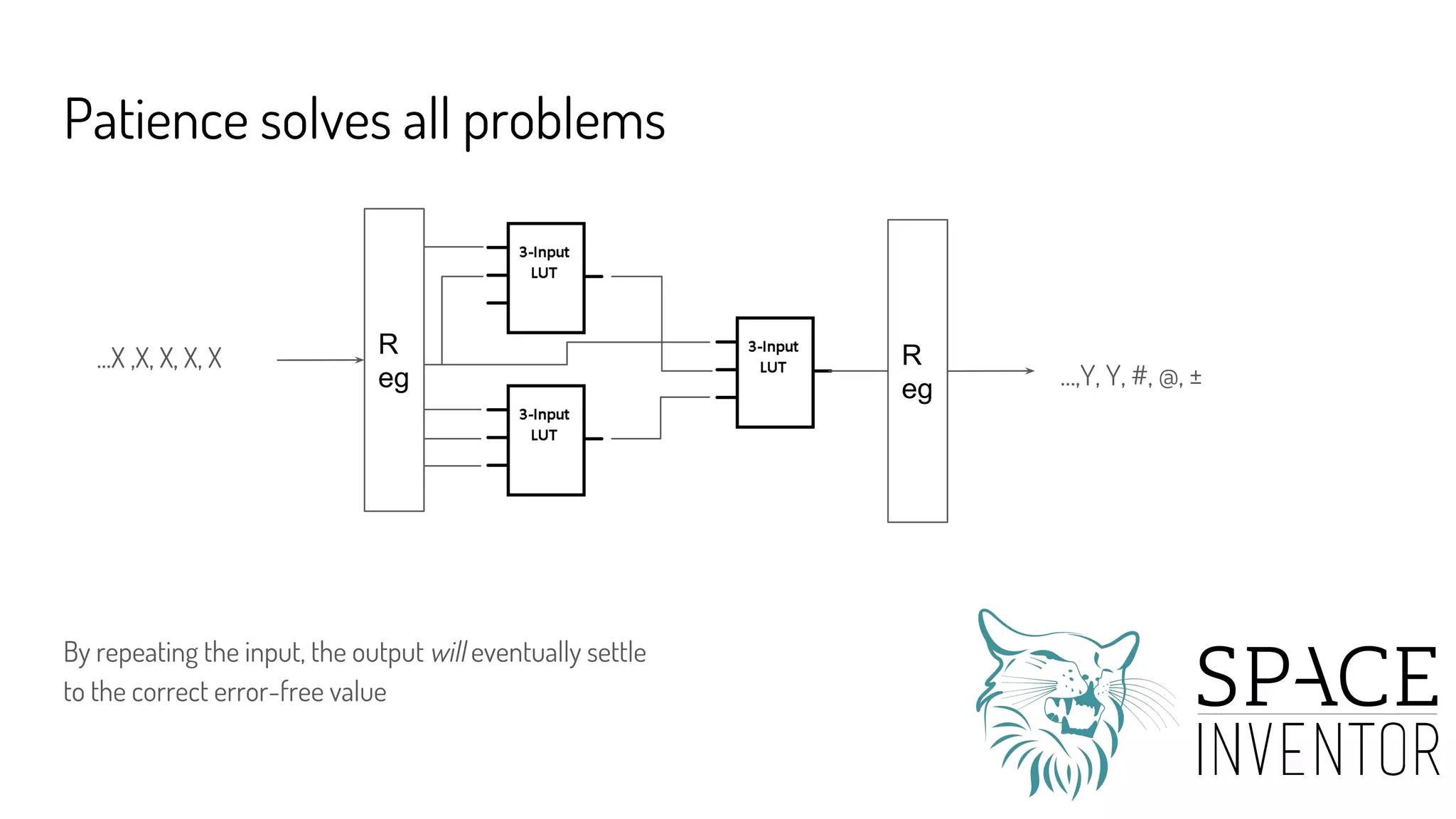
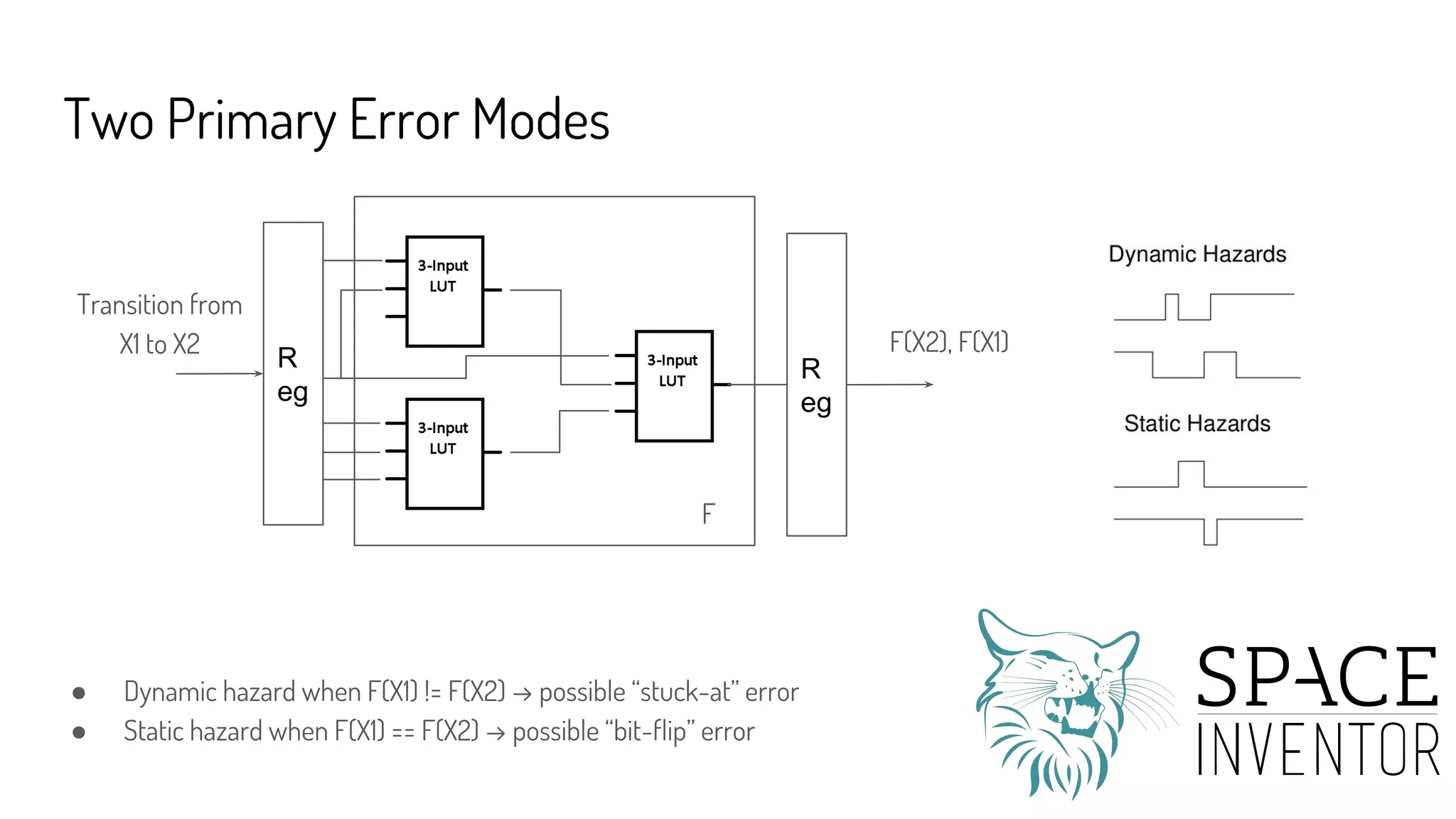
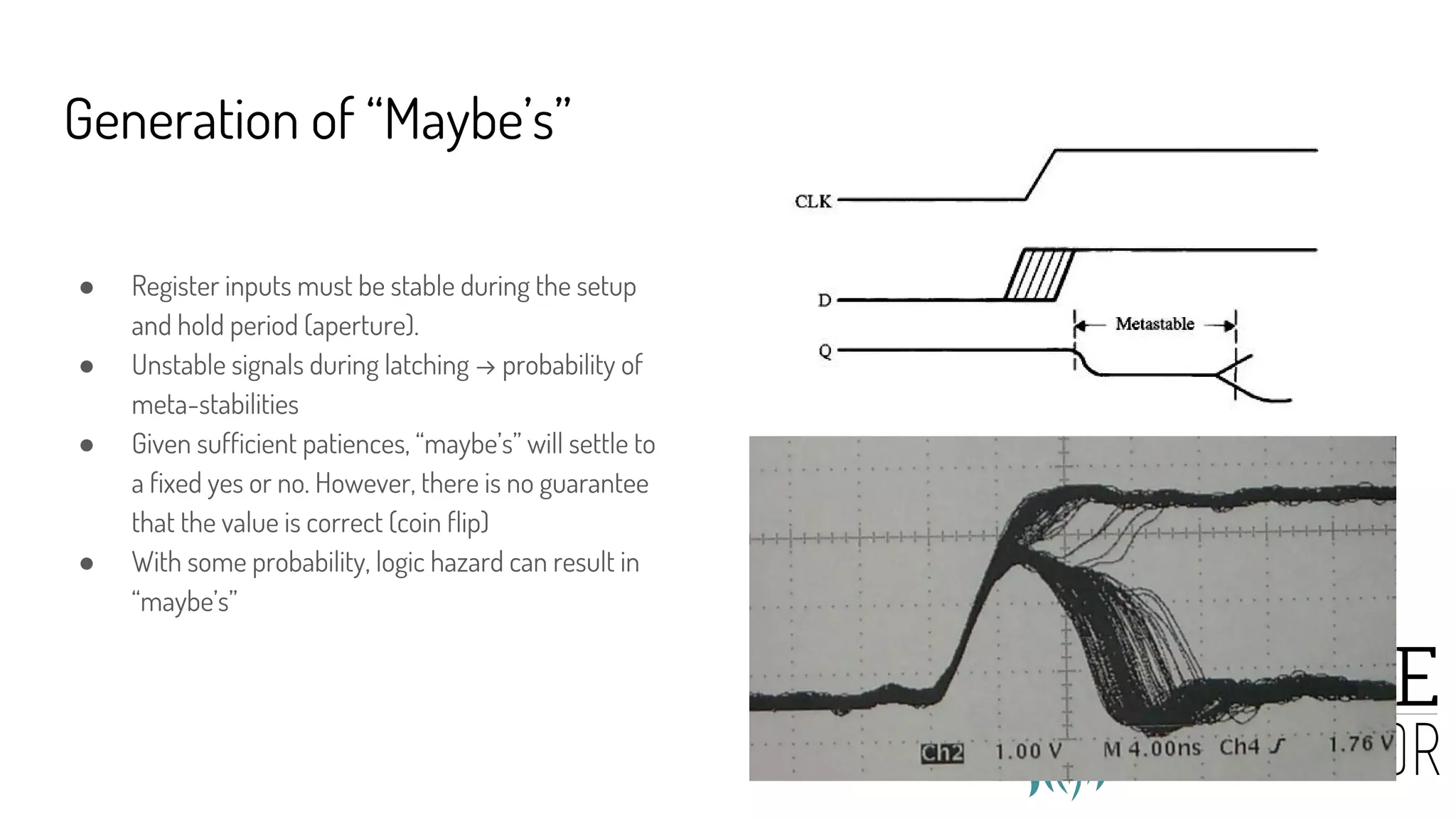
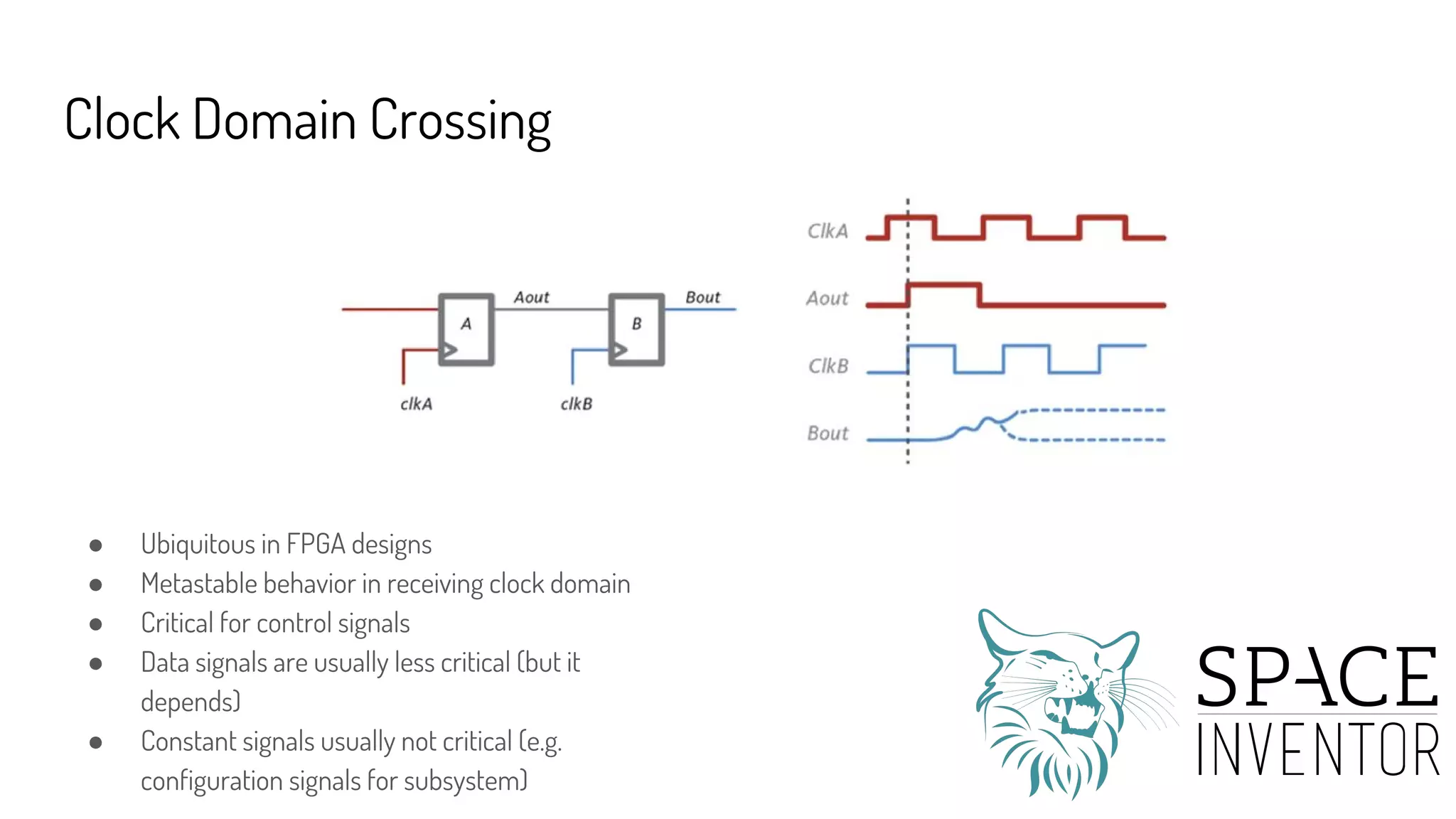
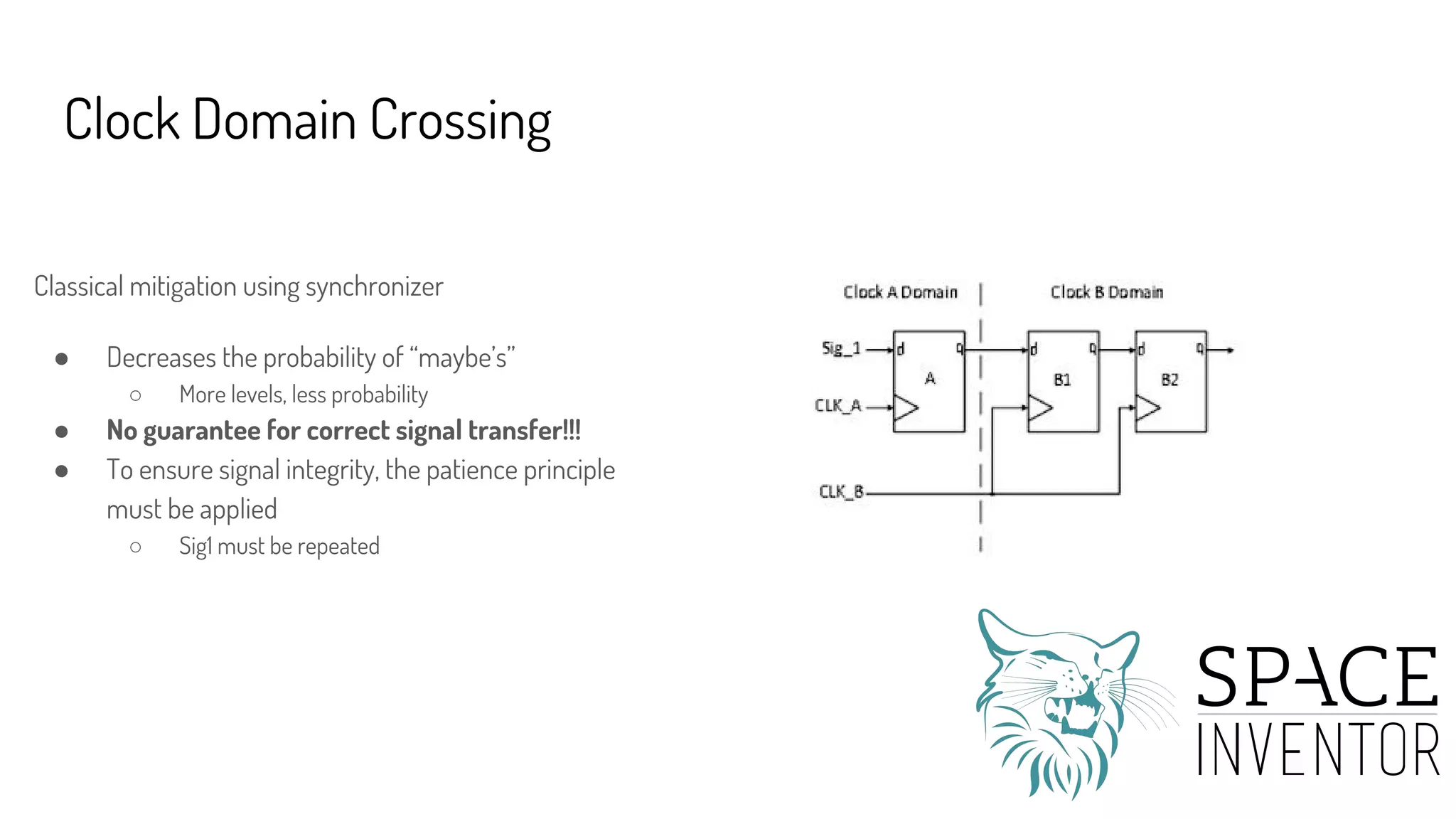
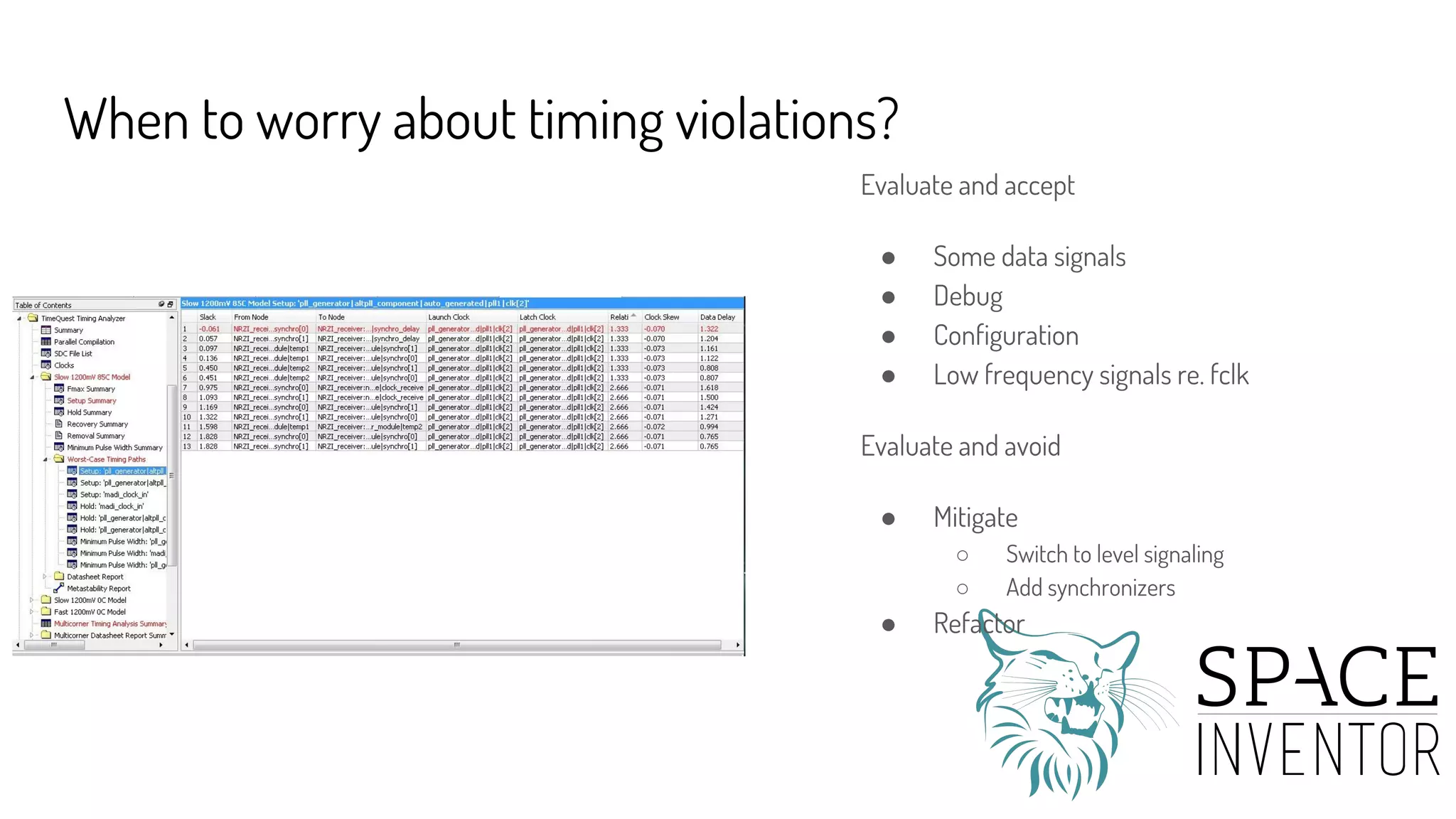
The document discusses how FPGAs can fail due to timing violations even when programmed correctly. It introduces Richard Feynman's "File Clerk Model" (FCM) as an intuitive way to understand these failures. Using the FCM analogy, the presentation explains how timing violations can cause errors by sensitizing logic and generating transient "maybe" states. It also discusses specific error cases like clock domain crossing and radiation-induced aging. The overall message is that timing constraints are crucial for reliable FPGA operation, and the FCM provides system-level insights into how timing errors can occur.