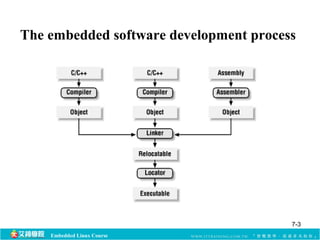
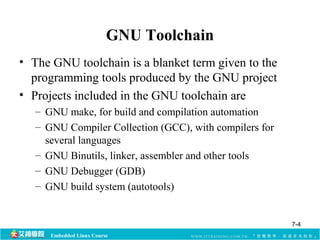
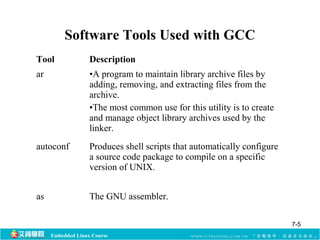
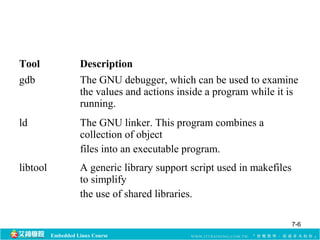
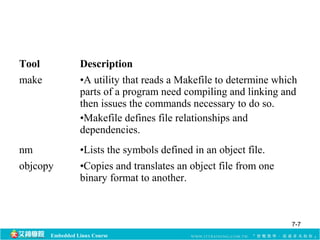
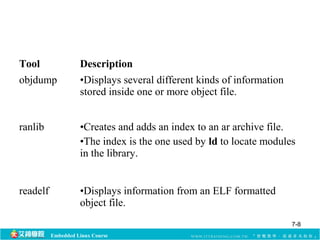
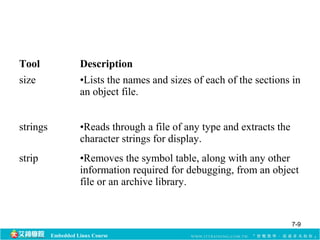
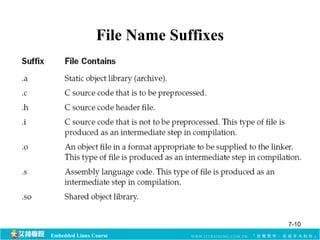
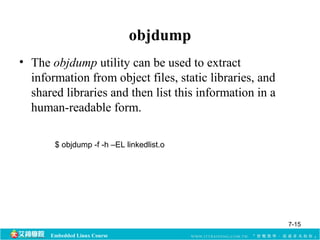
The document discusses various tools that are part of the GNU toolchain used for embedded software development. It provides descriptions of common tools used with the GNU Compiler Collection (GCC) such as ar, autoconf, as, gdb, ld, libtool, make, nm, objcopy, objdump, ranlib, readelf, size, strings and strip. It also covers topics like the preprocessor, compiler options, anonymous unions, arrays of zero length, and using attributes with GCC.
![Embedded Linux Course
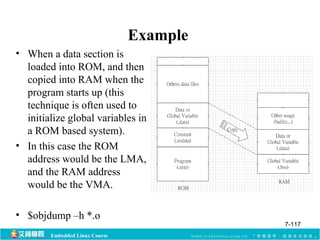
Example
Version 1: largearrayinit.c
int myarray[50000] = {1, 2, 3, 4};
int main(void) {
myarray[0] = 3;
return 0;
}
Version 2: largearray.c
int myarray[50000]={0};
int main(void) {
myarray[0] = 3;
return 0;
}
gcc -c largearrayinit.c
size largearrayinit.o
ls –l largearrayinit.o
gcc -c largearray.c
size largearray.o
ls –l largearray.o
7-13](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-13-320.jpg)
![Embedded Linux Course
Example
struct command
{
char *name;
void (*function) ();
};
#define COMMAND(NAME) { #NAME, NAME ## _command }
struct command commands[] =
{
COMMAND (quit),
COMMAND (help),
...
};
struct command commands[] =
{
{ "quit", quit_command},
{ "help", help_command},
...
};
7-34](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-34-320.jpg)

![Anonymous Unions
• Within a struct, a union can be declared without a
name, making it possible to address the union
members directly, just as if they were members of the
struct.
struct {
char code;
Embedded Linux Course
union {
char chid[4];
int numid;
};
char *name;
} morx;
7-49](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-49-320.jpg)
![Arrays of Zero Length
• GNU C allows the declaration of arrays of zero length
to facilitate the creation of variable-length structures.
• This only makes sense if the zero-length array is the
last member of a struct.
• The size of the array can be specified by simply being
allocated the amount of space necessary.
typedef struct {
Embedded Linux Course
int size;
char string[0];
} vlen;
7-50](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-50-320.jpg)
![int main(int argc,char *argv[])
{
int i;
int count = 22;
char letter = 'a';
vlen *line = (vlen *)malloc(sizeof(vlen) + count);
line->size = count;
for(i=0; i<count; i++)
line->string[i] = letter++;
printf("sizeof(vlen)=%d, line->size=%d n",sizeof(vlen),line->size);
for(i=0; i<line->size; i++)
printf("%c ",line->string[i]);
printf("n");
return(0);
} 7-51
Embedded Linux Course](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-51-320.jpg)
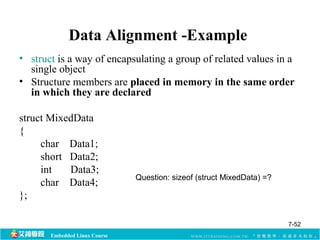
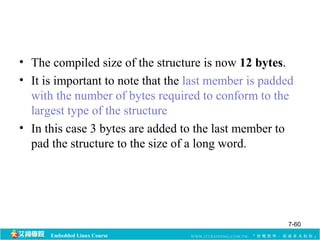
![• After compilation the data structure will be
supplemented with padding bytes to ensure a proper
alignment for each of its member:
struct MixedData (after compilation)
{
char Data1;
char Padding0[1];
short Data2;
int Data3;
char Data4;
char Padding1[3];
Embedded Linux Course
};
7-59](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-59-320.jpg)
![Attribute: packed
• A variable with this attribute has the smallest possible
alignment.
• A variable will be separated no more than one byte
from its predecessor field.
• In a struct, a field with this attribute will be allocated
with no space between it and the field before it.
struct zrecord {
char id;
int zar[32] __attribute__ ((packed));
};
Embedded Linux Course
7-64](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-64-320.jpg)

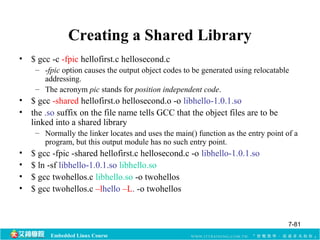
![$ gcc twohellos.c libhello.a -o twohellos
Embedded Linux Course
Cont.
/* twohellos.c */
void hellofirst(void);
void hellosecond(void);
int main(int argc,char *argv[])
{
hellofirst();
hellosecond();
return(0);
}
$ gcc twohellos.c –lhello –L. -o twohellos
7-79](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-79-320.jpg)
![Embedded Linux Course
ldd
[root@localhost 20071125]# ldd twohellos
linux-gate.so.1 => (0x00f30000)
libhello.so => not found
libc.so.6 => /lib/libc.so.6 (0x00781000)
/lib/ld-linux.so.2 (0x00764000)
[root@localhost 20071125]# ldd twohellos
linux-gate.so.1 => (0x00ea5000)
libhello.so => /lib/libhello.so (0x00eb4000)
libc.so.6 => /lib/libc.so.6 (0x00781000)
/lib/ld-linux.so.2 (0x00764000)
7-82](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-82-320.jpg)


![Embedded Linux Course
ldd
• The ldd utility reads through the object files in the
binary executable or shared library and lists all the
shared library dependencies.
– but toolchain doesn’t contain ldd utility, so we use readelf
• arm-linux-readelf –a <exe> | grep Shared
[root@localhost fbv-1.0b]# arm-linux-readelf -a fbv | grep Shared
0x00000001 (NEEDED) Shared library: [libpng12.so.0]
0x00000001 (NEEDED) Shared library: [libungif.so.4]
0x00000001 (NEEDED) Shared library: [libc.so.6]
7-89](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-89-320.jpg)
![Embedded Linux Course
handle = dlopen("libsayfn.so",RTLD_LAZY);
if(error = dlerror()) {
printf("%sn",error);
exit(1);
}
sayhello = dlsym(handle,"sayhello");
if(error = dlerror()) {
printf("%sn",error);
exit(1);
}
saysomething = dlsym(handle,"saysomething");
if(error = dlerror()) {
printf("%sn",error);
exit(1);
}
(*sayhello)();
saysomething("This is something");
dlclose(handle);
}
/* say.c */
#include <dlfcn.h>
#include <stdio.h>
#include <stdlib.h>
int main(int argc,char *argv[])
{
void *handle;
char *error;
void (*sayhello)(void);
void (*saysomething)(char *);
$ gcc say.c -ldl -o say
7-91](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-91-320.jpg)

![Output section description
SECTIONS [address] [(type)] : [AT(LMA)]
{
output-sections-command
output-sections-command
...
} [>region] [: phdr : phdr ...] [=fillexp]
Embedded Linux Course
7-108](https://image.slidesharecdn.com/ch7toolchain-140906211825-phpapp01/85/Linux-GNU-Toolchain-108-320.jpg)