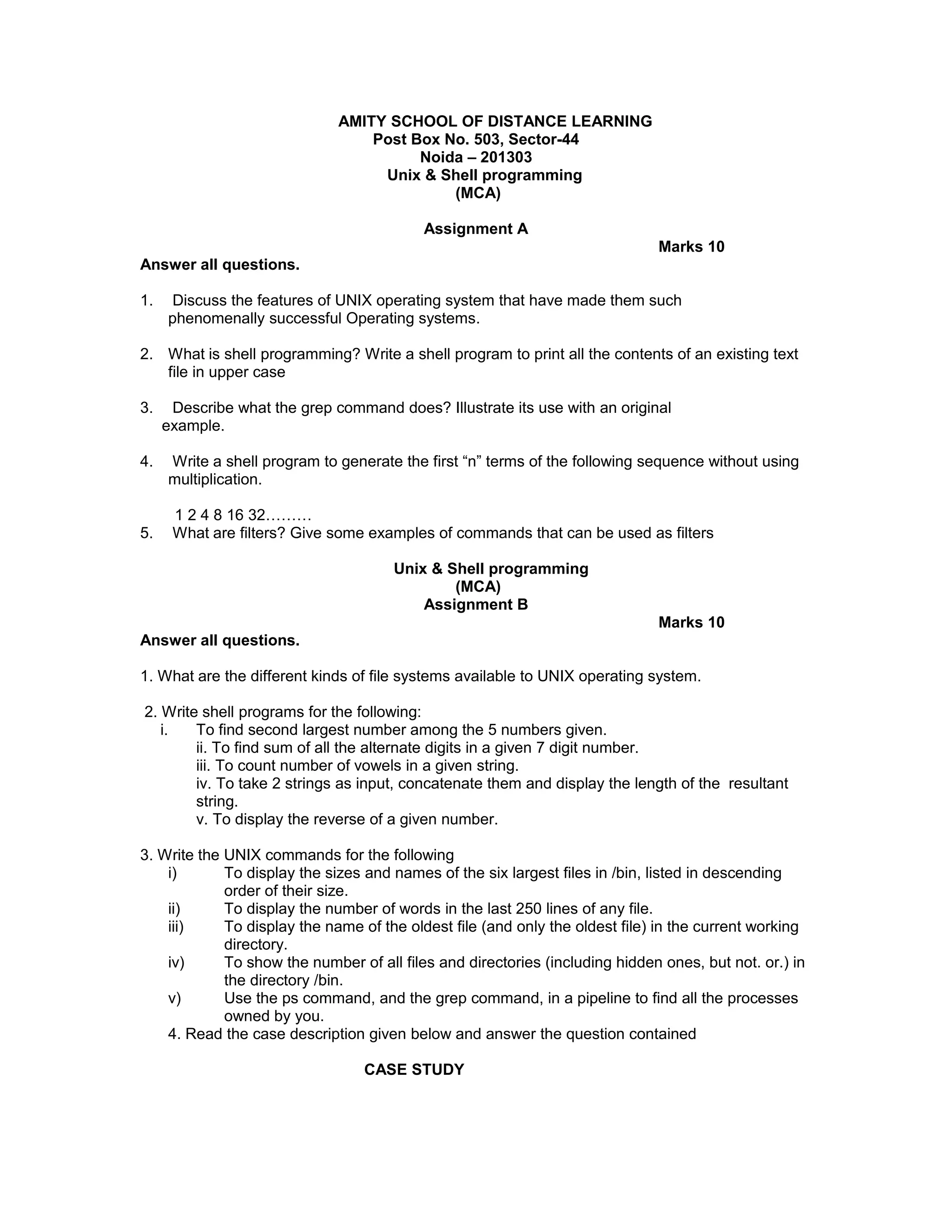
The document contains three assignments related to Unix and shell programming. Assignment A contains questions about features of Unix, shell programming, the grep command, writing a shell program to generate terms of a sequence, and examples of filter commands. Assignment B contains questions about Unix file systems, writing shell programs to perform various tasks, and Unix commands. Assignment C contains multiple choice questions testing knowledge of Unix commands, file concepts, shell programming, and operating system concepts.