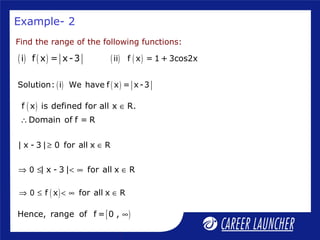
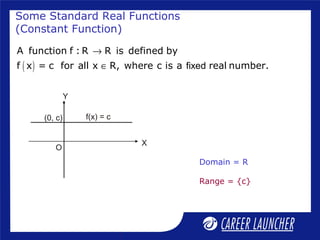
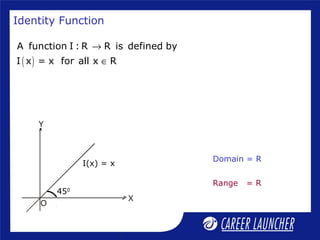
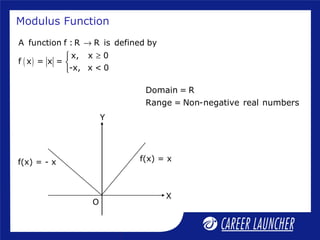
This document discusses functions, limits, and continuity. It begins by defining functions, domains, ranges, and some standard real functions like constant, identity, modulus, and greatest integer functions. It then covers limits of functions including one-sided limits and properties of limits. Examples are provided to illustrate evaluating limits using substitution and factorization methods. The overall objectives are to understand functions, domains, ranges, limits of functions and methods to evaluate limits.
![Example– 1
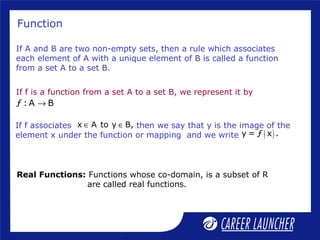
Find the domain of the following functions:
( ) ( ) 2
i f x = 9- x ( ) 2
x
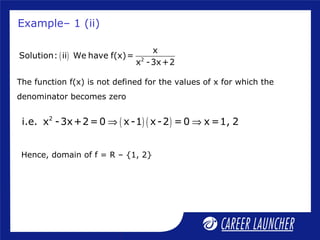
ii f(x)=
x -3x+2
( ) 2
Solution: We have f x = 9- x
( )The function f x is defined for
[ ]-3 x 3 x -3, 3⇒ ≤ ≤ ⇒ ∈
( ) ( )2 2
9- x 0 x -9 0 x-3 x+3 0≥ ⇒ ≤ ⇒ ≤
Domain of f = -3, 3∴ ](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-7-320.jpg)
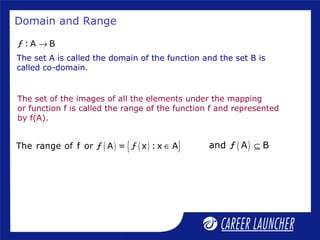
![-1 ≤ cos2x ≤ 1 for all x∈R
⇒-3 ≤ 3cos2x ≤ 3 for all x∈R
⇒-2 ≤ 1 + 3cos2x ≤ 4 for all x∈R
⇒ -2 ≤ f(x) ≤ 4
Hence , range of f = [-2, 4]
Example – 2(ii)
( ) ( )Solution : ii We have f x = 1 + 3cos2x
( )Domain of cosx is R. f x is defined for all x R
Domain of f = R
∴ ∈
∴
Q](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-10-320.jpg)
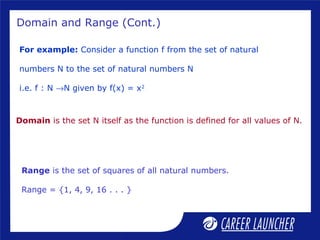
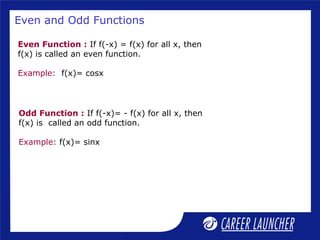
![Find fog and gof if f : R → R such that f(x) = [x]
and g : R → [-1, 1] such that g(x) = sinx.
Solution: We have f(x)= [x] and g(x) = sinx
fog(x) = f(g(x)) = f(sinx) = [sin x]
gof(x) = g(f(x)) = g ([x]) = sin [x]
Example – 4](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-20-320.jpg)
![Example – 7
Which of the following limits exist:
( ) x 0
x
i lim
x→
[ ]5
x
2
(ii) lim x
→
( ) ( )
x
Solution : i Let f x =
x
( ) ( ) ( )- h 0 h 0 h 0x 0
0 - h -h
LHL at x = 0 = lim f x = limf 0 - h =lim =lim = -1
0 - h h→ → →→
( ) ( ) ( )+ h 0 h 0 h 0x 0
0 + h h
RHL at x = 0 = lim f x = limf 0 + h =lim =lim = 1
0 + h h→ → →→
( ) ( )- +
x 0 x 0
lim f x lim f x
→ →
≠Q x 0
x
lim does not exist.
x→
∴](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-29-320.jpg)
![Example - 7 (ii)
( ) [ ]Solution:(ii) Let f x = x
( ) h 0 h 05
x
2
5 5 5
LHL at x = = lim f x =limf -h =lim -h =2
2 2 2− → →
→
÷ ÷
( ) h 0 h 05
x
2
5 5 5
RHL at x = = lim f x =limf +h =lim +h =2
2 2 2+ → →
→
÷ ÷
( ) ( )5 5
x x
2 2
lim f x lim f x− +
→ →
=Q [ ]5
x
2
lim x exists.
→
∴](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-30-320.jpg)
![Properties of Limits
( )
x a x a x a
i lim [f(x) g(x)]= lim f(x) lim g(x) = m n
→ → →
± ± ±
( )
x a x a
ii lim [cf(x)]= c. lim f(x) = c.m
→ →
( ) ( )
x a x a x a
iii lim f(x). g(x) = lim f(x) . lim g(x) = m.n
→ → →
( )
x a
x a
x a
lim f(x)
f(x) m
iv lim = = , provided n 0
g(x) lim g(x) n
→
→
→
≠
If and
where ‘m’ and ‘n’ are real and finite then
x a
lim g(x)= n
→x a
lim f(x)= m
→](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-31-320.jpg)
![Algebraic Limits (Rationalization Method)
When we substitute the value of x in the rational expression it
takes the form
0
, etc.
0
∞
∞
[ ]
2 2
2 2x 4
x -16 ( x +9 +5)
=lim × Rationalizing the denominator
( x +9 -5) ( x +9 +5)→
2
2
2x 4
x -16
=lim ×( x +9 +5)
(x +9-25)→
2
2
2x 4
x -16
=lim ×( x +9 +5)
x -16→
2 2
x 4
=lim( x +9 +5) = 4 +9 +5 = 5+5=10
→
2
2x 4
x -16 0
For example: lim form
0x +9 -5→
](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-34-320.jpg)
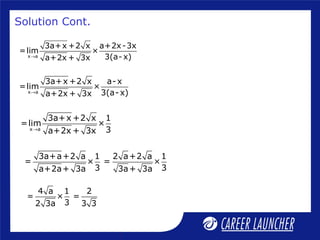
![x a
a+2x - 3x
Evaluate:lim
3a+x -2 x→
x a
a+2x - 3x
Solution: lim
3a+x -2 x→
[ ]x a
a+2x - 3x 3a+x +2 x
=lim × Rationalizing the denominator
3a+x -2 x 3a+x +2 x→
Example – 8 (iii)
x a
a+2x - 3x
=lim × 3a+x +2 x
3a+x- 4x→
[ ]x a
3a+x +2 x a+2x + 3x
=lim × a+2x - 3x× Rationalizing thenumerator
3(a- x) a+2x + 3x→](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-38-320.jpg)
![2x 1
3+x - 5- x
Evaluate: lim
x -1→
2x 1
3+x - 5- x
Solution: lim
x -1→
[ ]2x 1
3+x - 5- x 3+x + 5- x
=lim × Rationalizing the numerator
x -1 3+x + 5- x→
Example – 8 (iv)
2x 1
3+x-5+x 1
=lim ×
x -1 3+x + 5-x→ x 1
2(x-1) 1
=lim ×
(x-1)(x+1) 3+x + 5- x→
( ) ( )x 1
2
=lim
x+1 3+x + 5- x→
2 1
= =
42( 4 + 4)
( ) ( )
2
=
1+1 3+1+ 5-1](https://image.slidesharecdn.com/functionslimitsandcontinuity-130909092441-/85/Functions-limits-and-continuity-40-320.jpg)