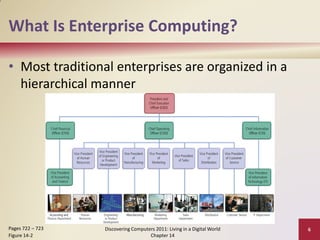
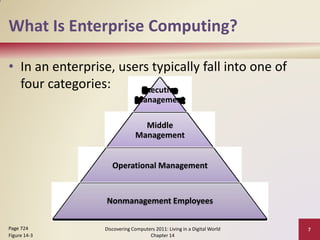
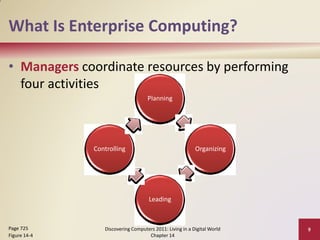
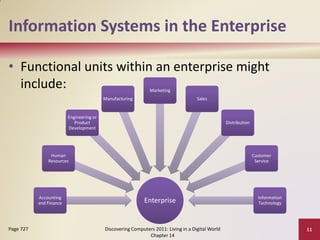
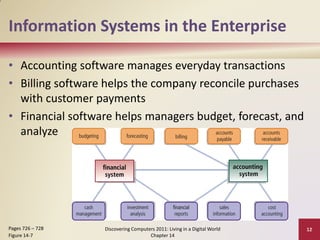
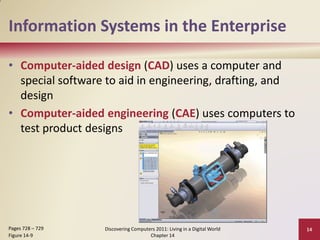
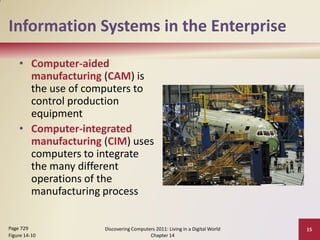
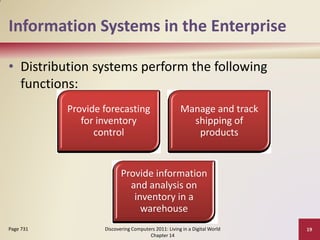
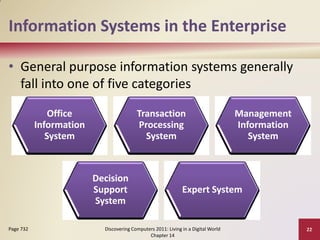
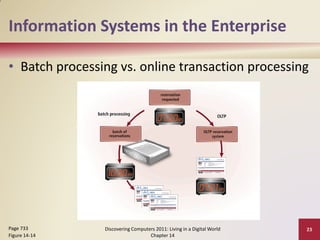
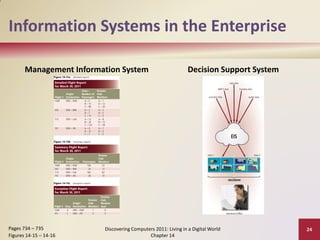
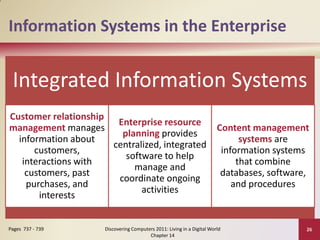
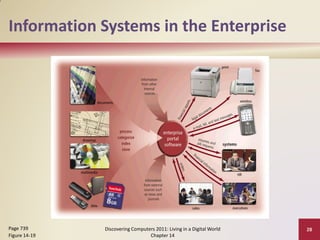
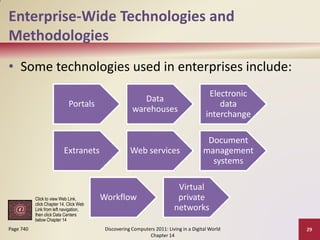
This document provides an overview of objectives and key concepts around enterprise computing. It discusses how enterprise computing involves using computers across interconnected networks to support large organizations. It describes the different functional units within enterprises and common information systems used, such as accounting, HR, manufacturing, and sales software. It also explains concepts like enterprise information, MRP, MRP II, and how information systems work together to support the needs of an enterprise.