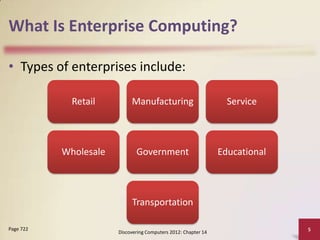
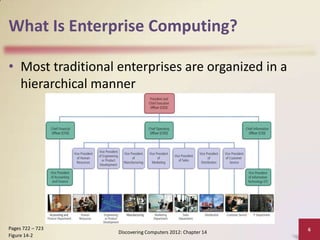
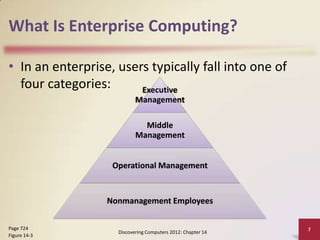
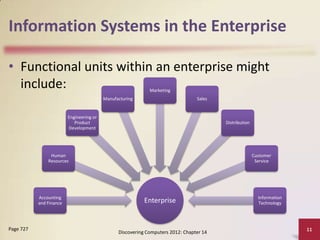
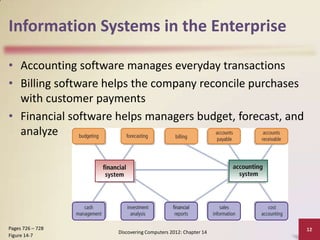
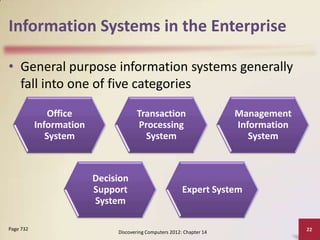
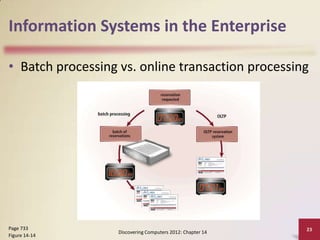
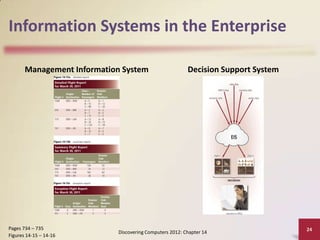
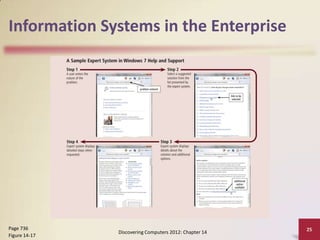
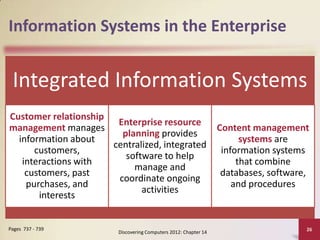
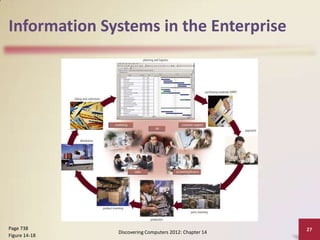
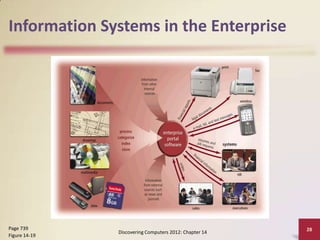
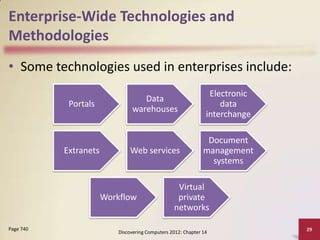
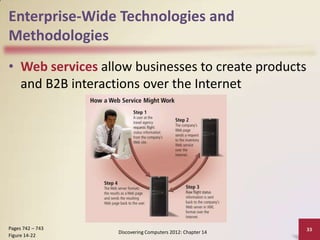
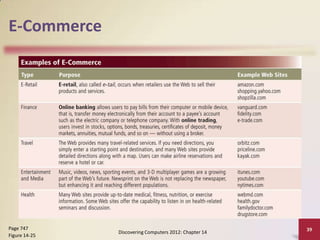
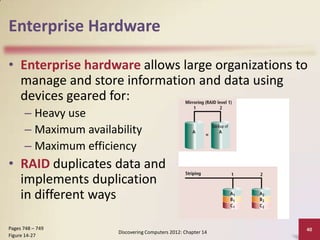
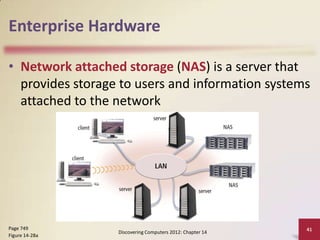
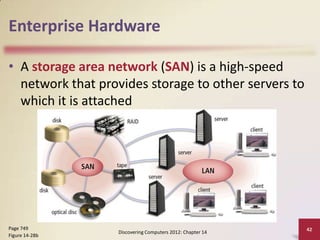
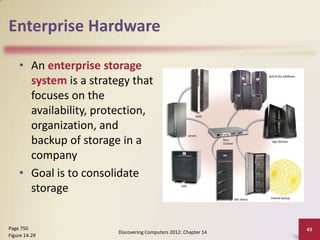
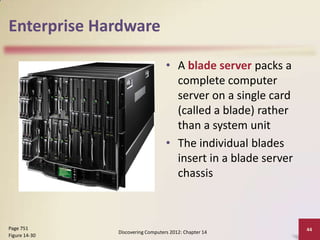
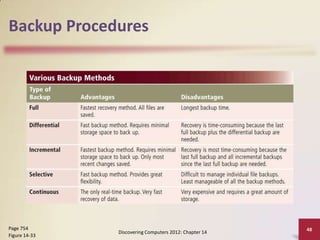
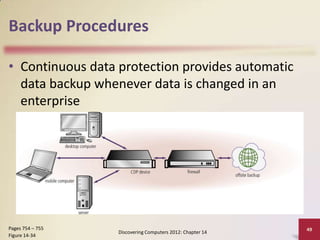
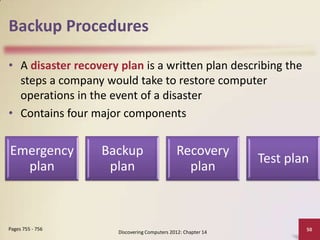
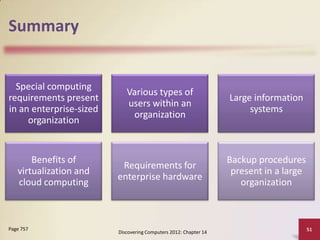
The document discusses enterprise computing and information systems. It describes the various functional units within an enterprise like accounting, human resources, engineering and how they utilize different information systems. It also summarizes the different types of general purpose information systems used across enterprises as well as key enterprise-wide technologies. The document concludes with discussing hardware requirements, high availability, scalability, interoperability, backup procedures and disaster recovery plans for large enterprises.