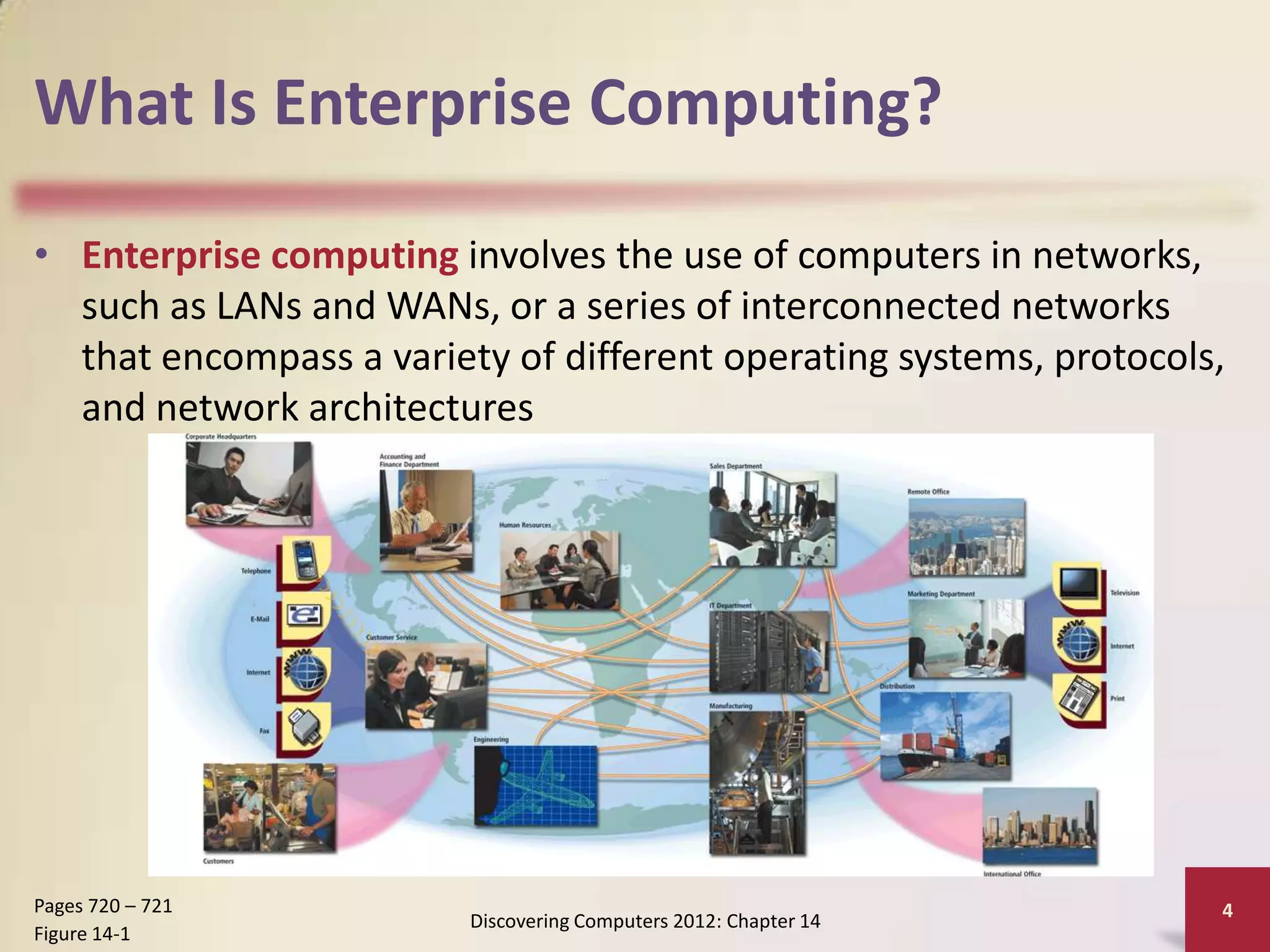
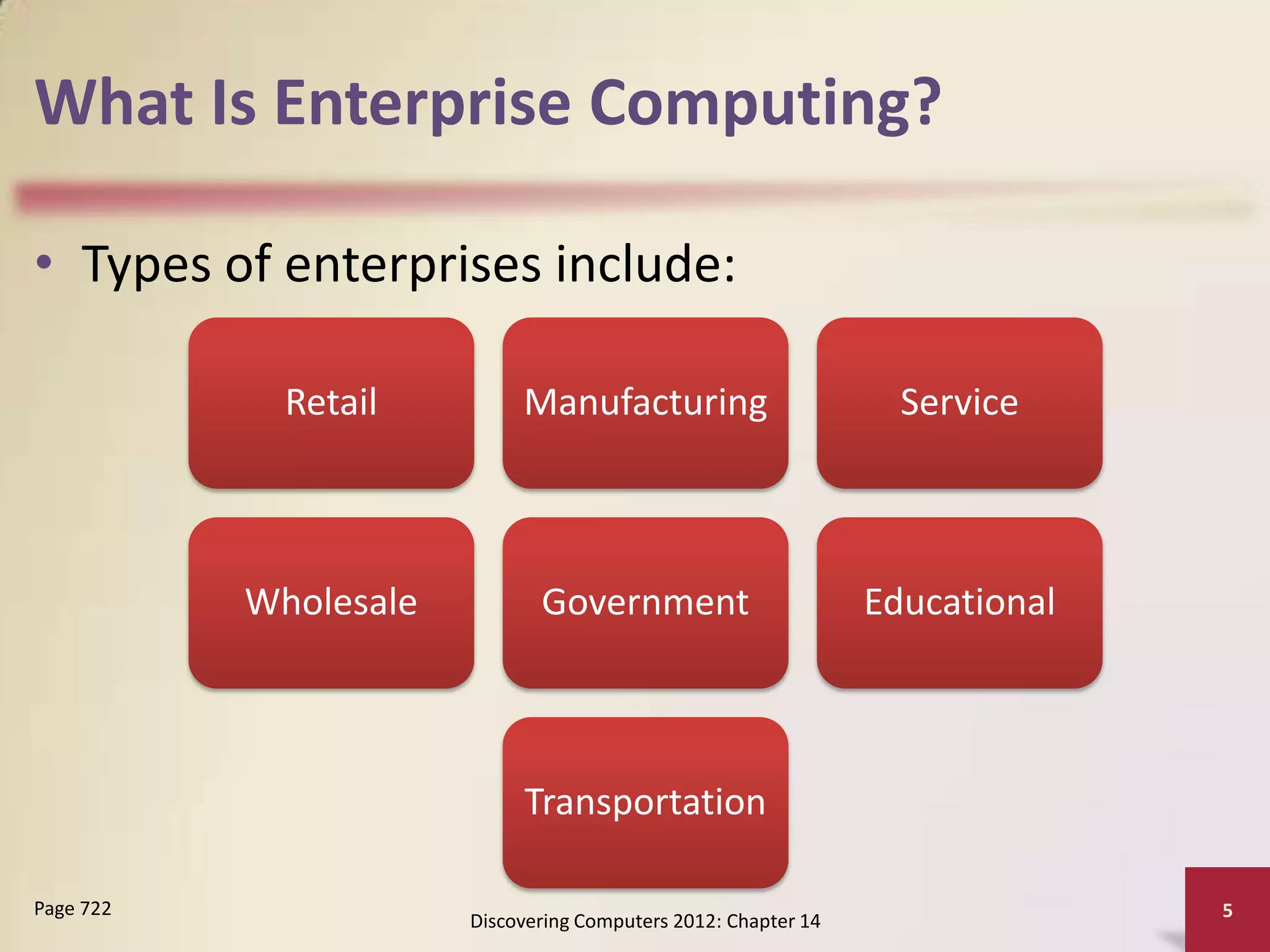
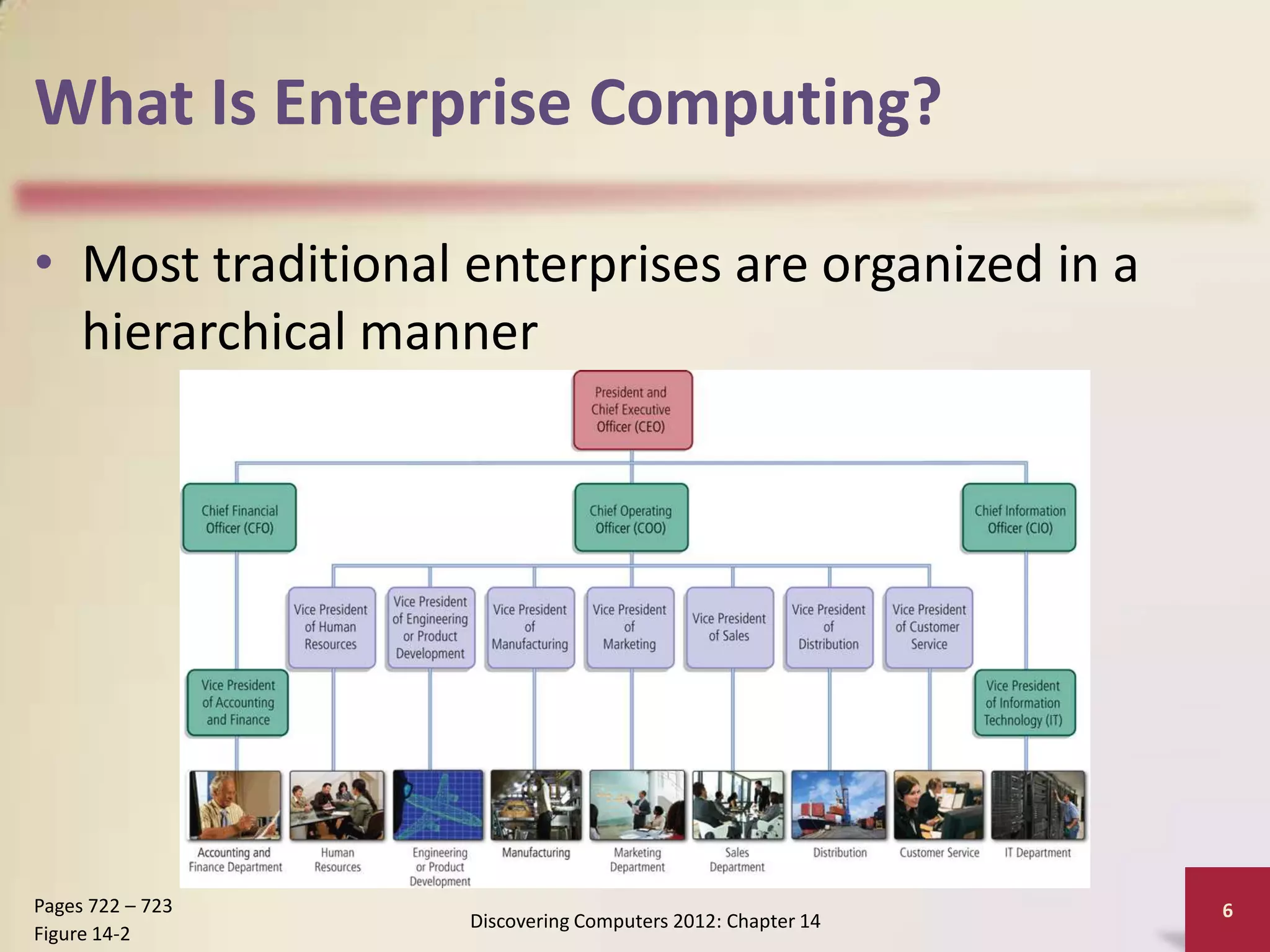
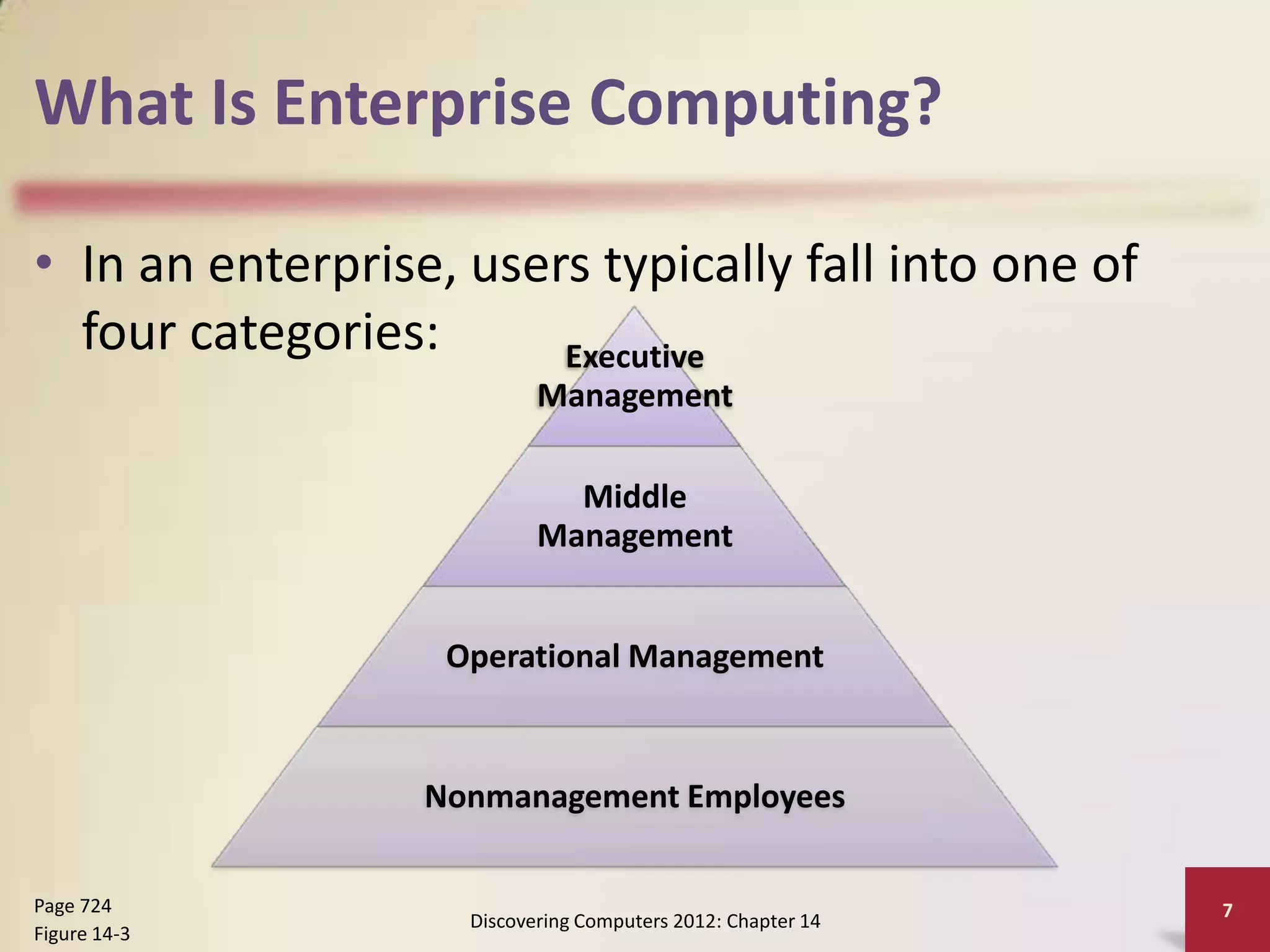
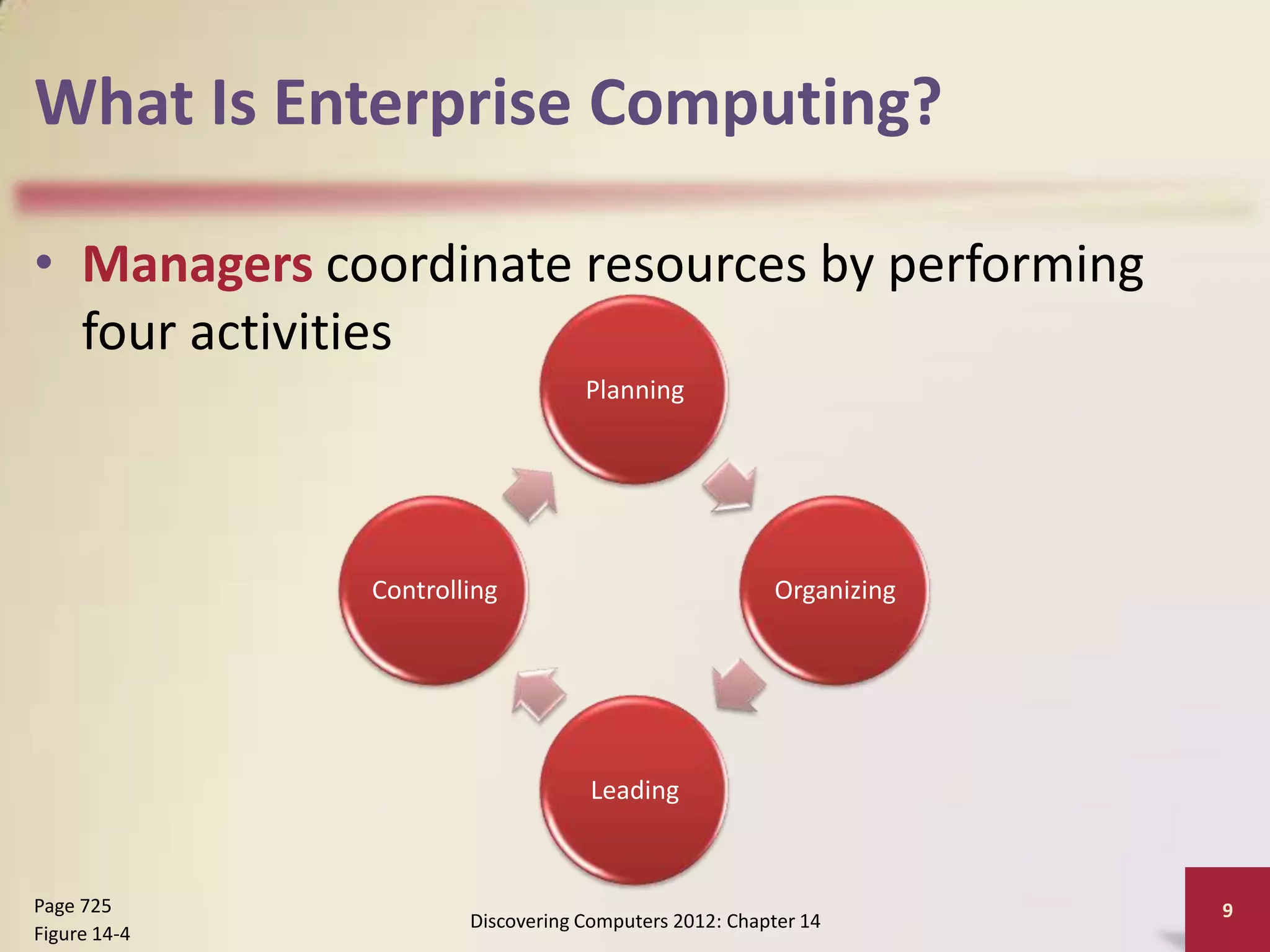
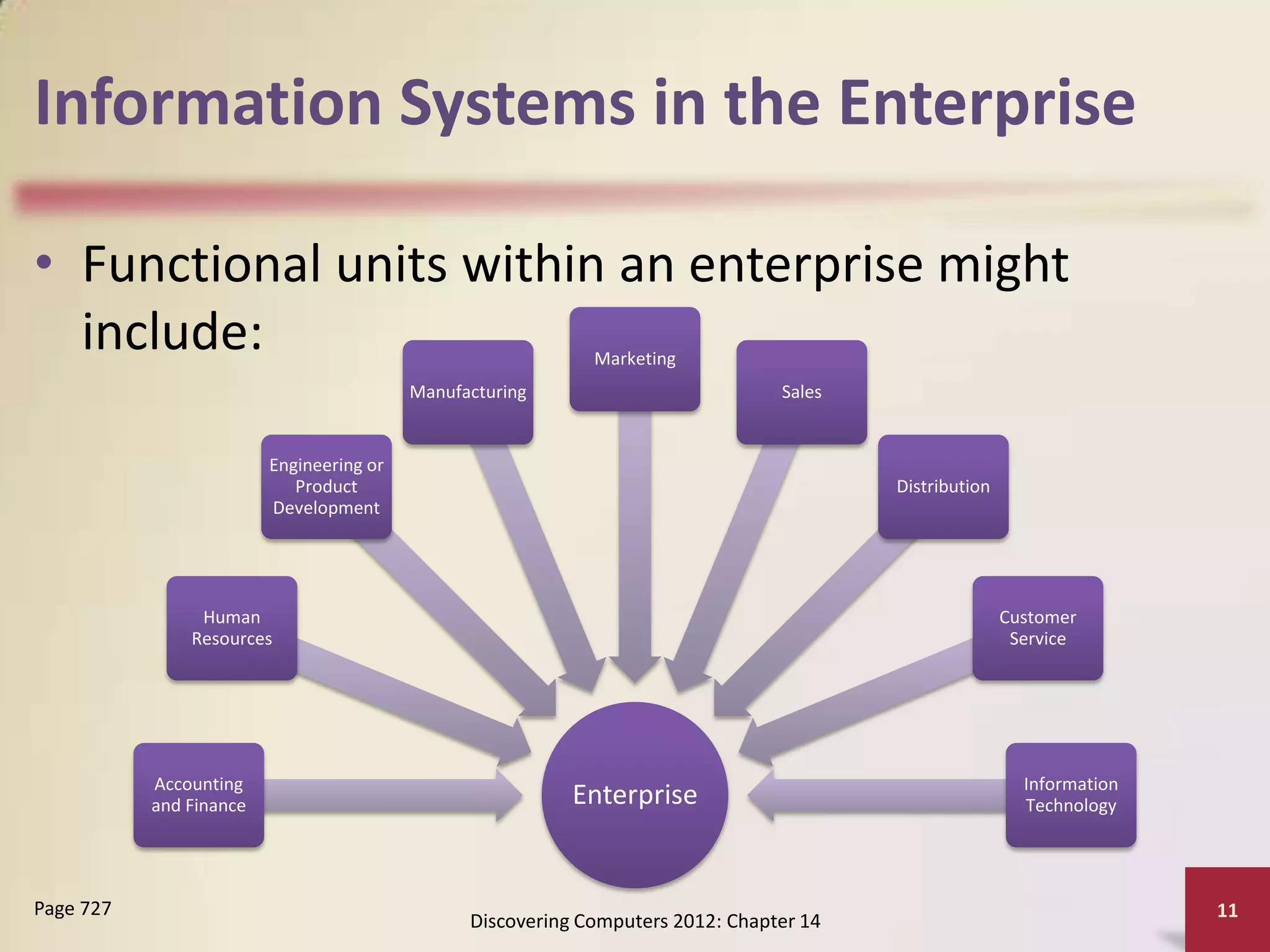
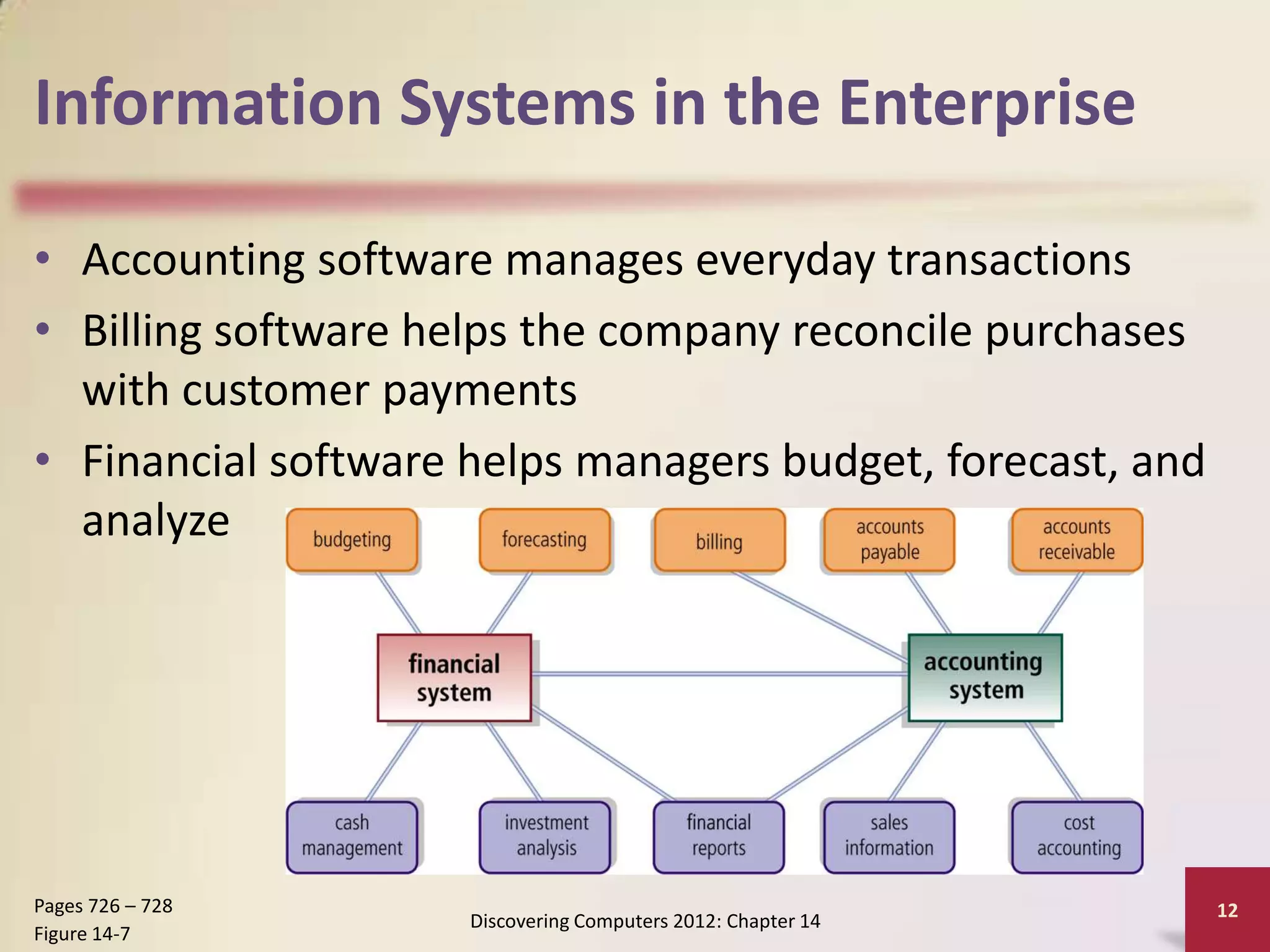
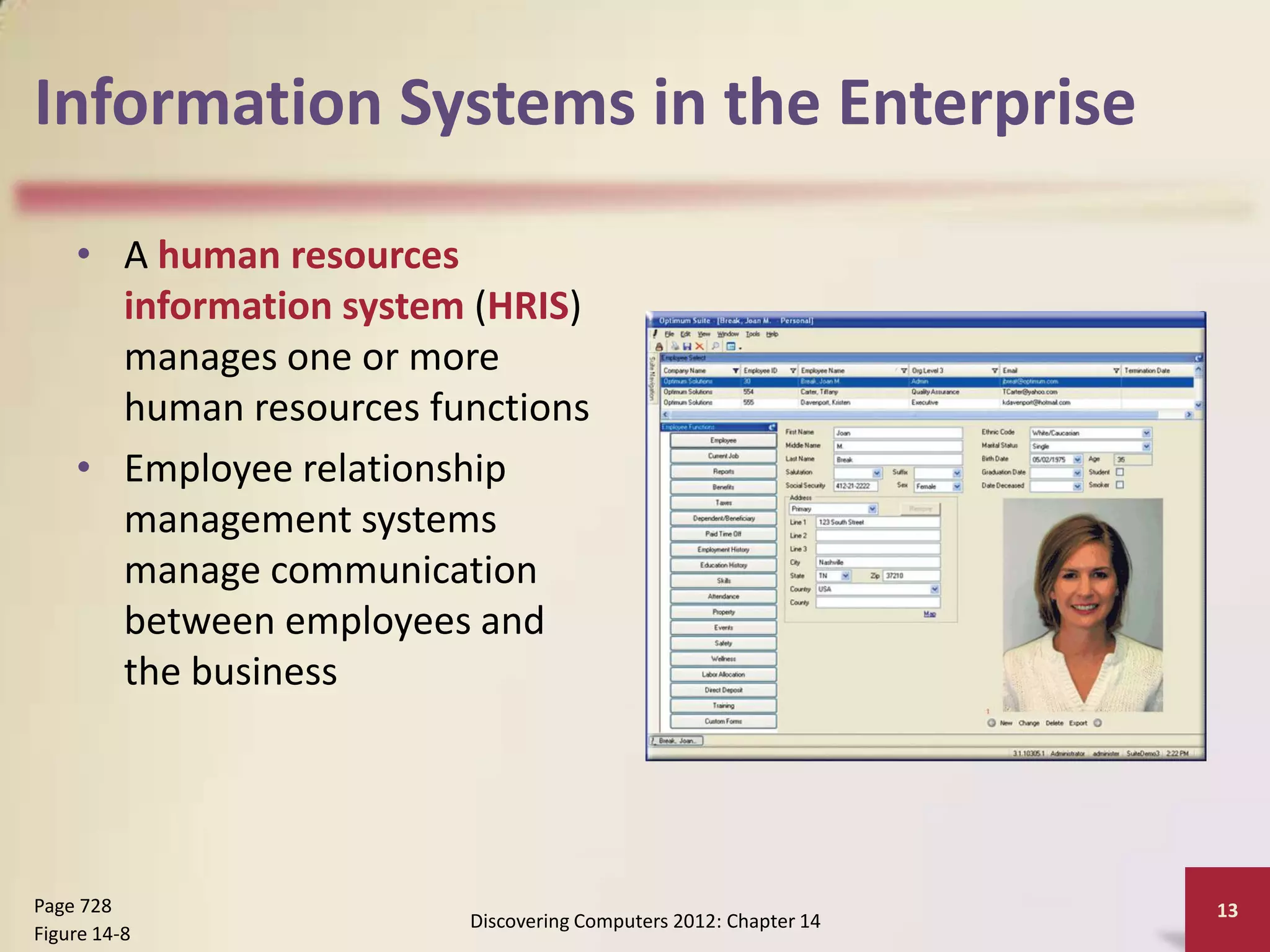
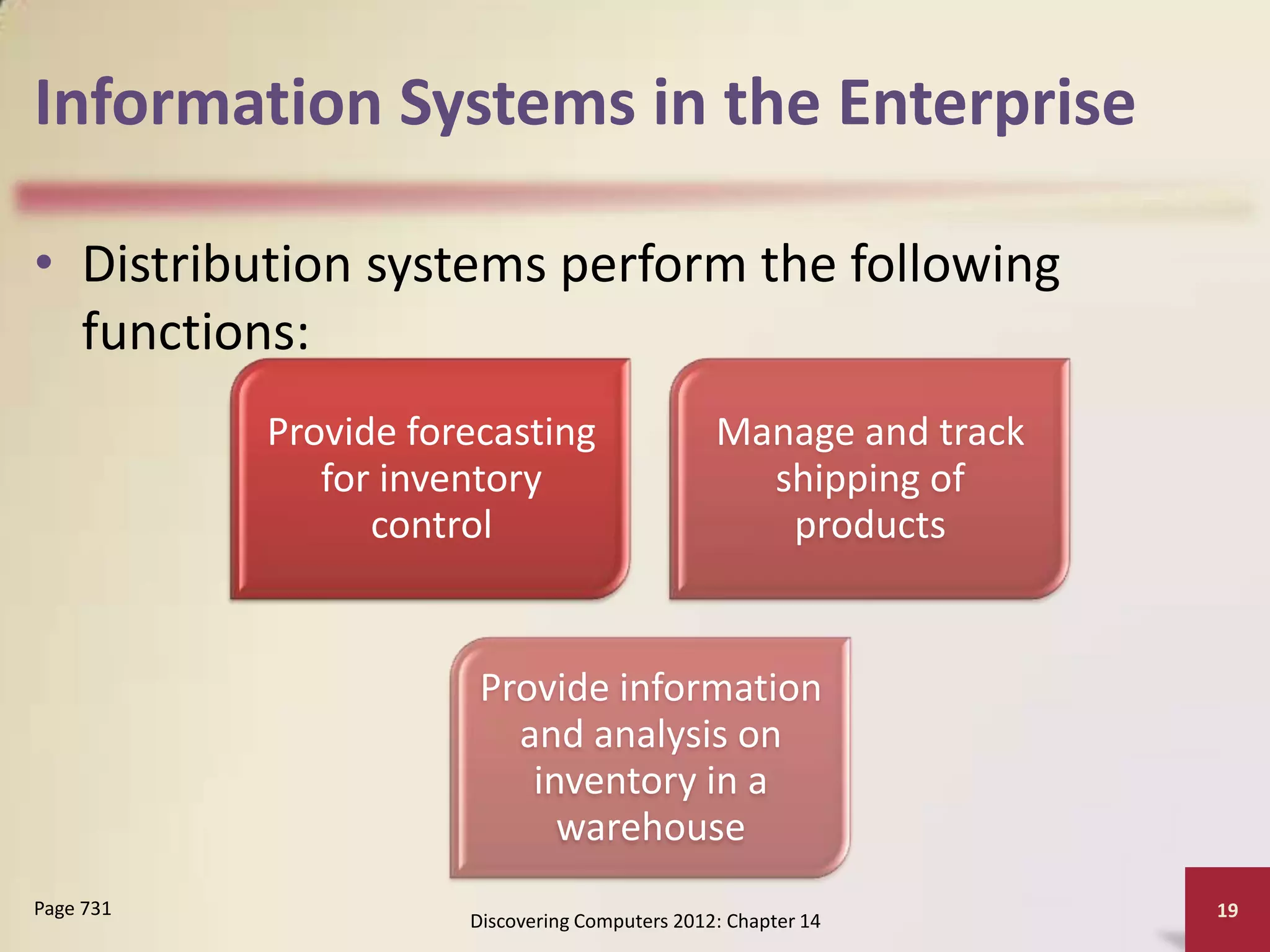
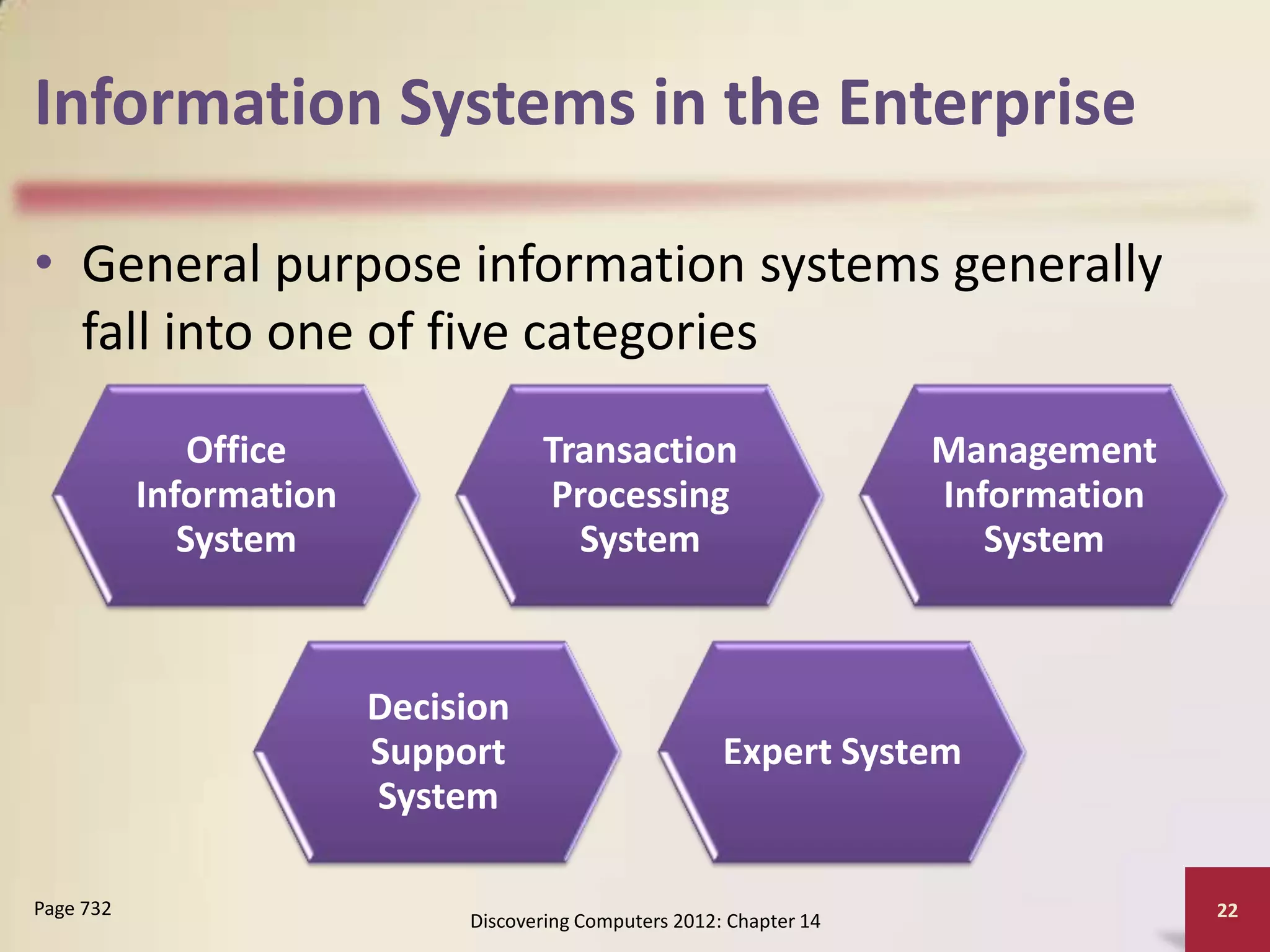
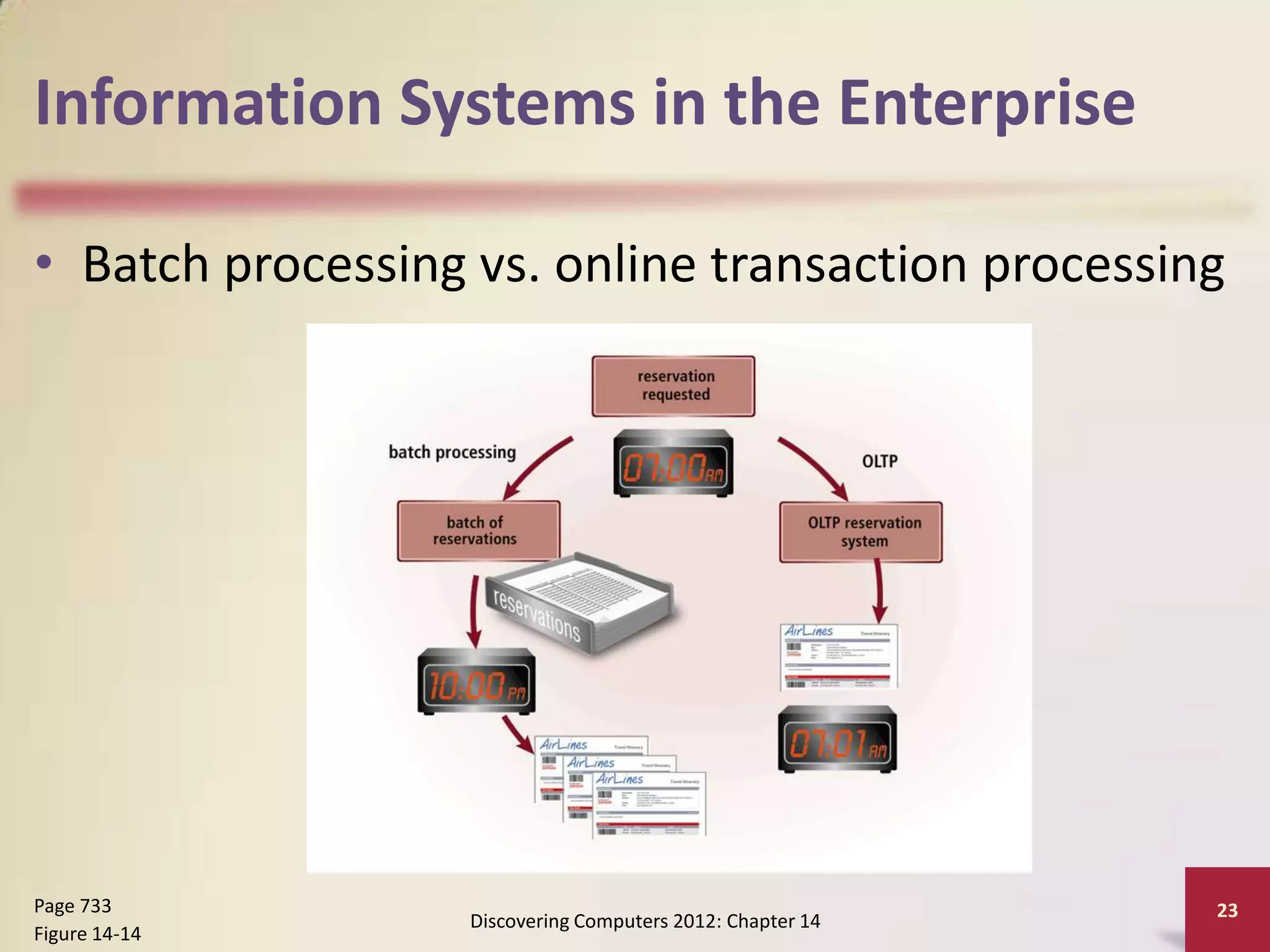
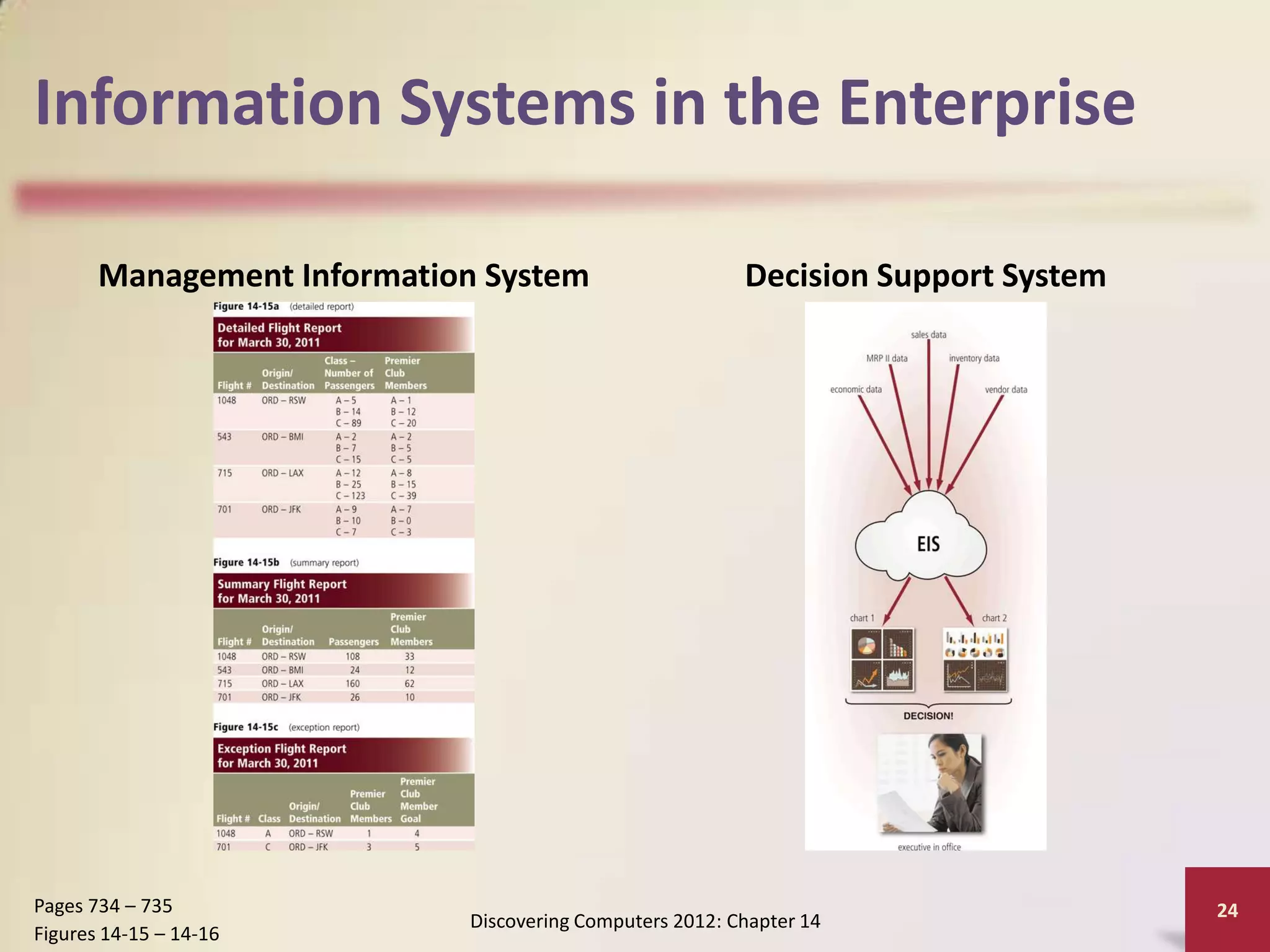
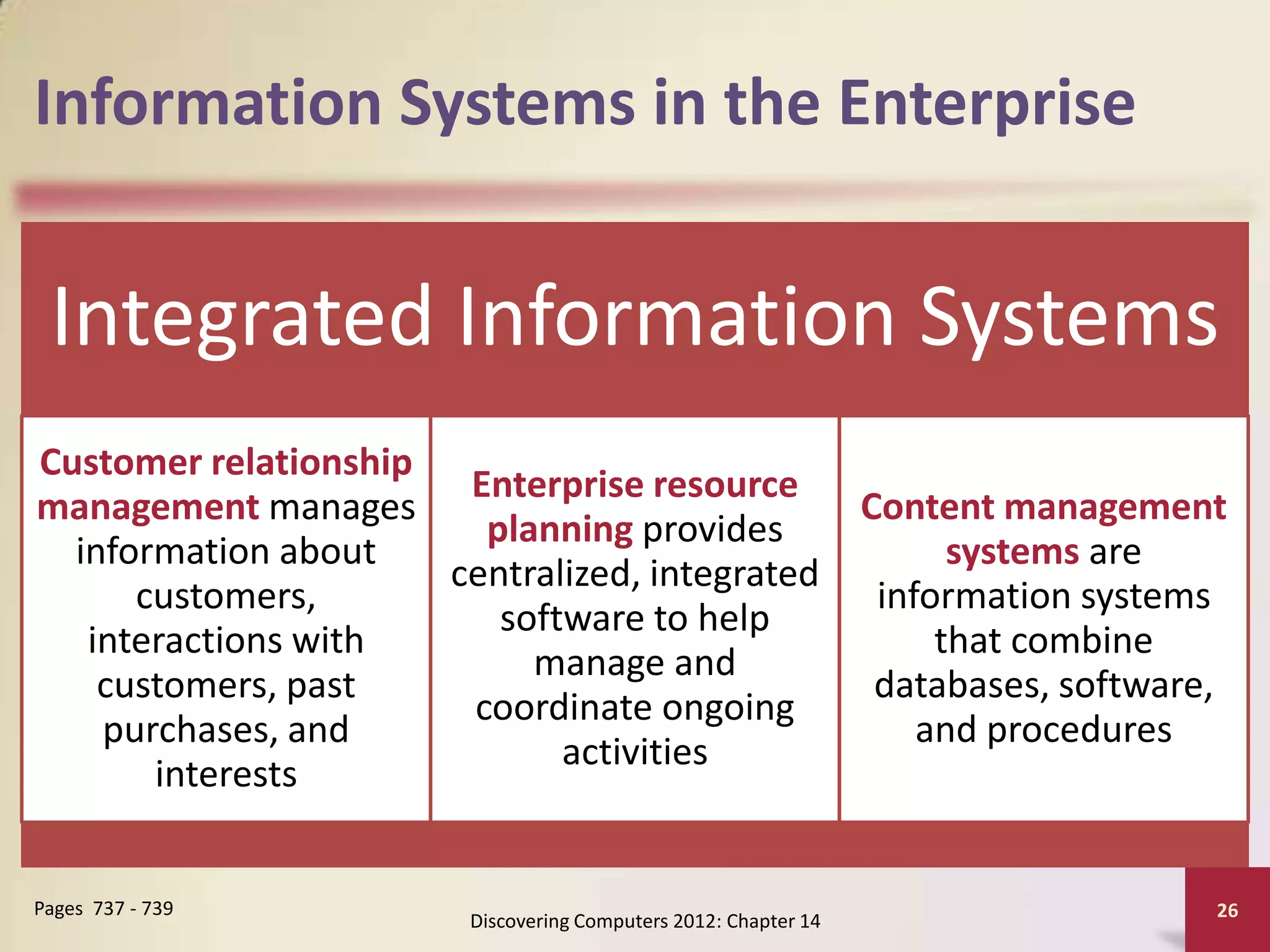
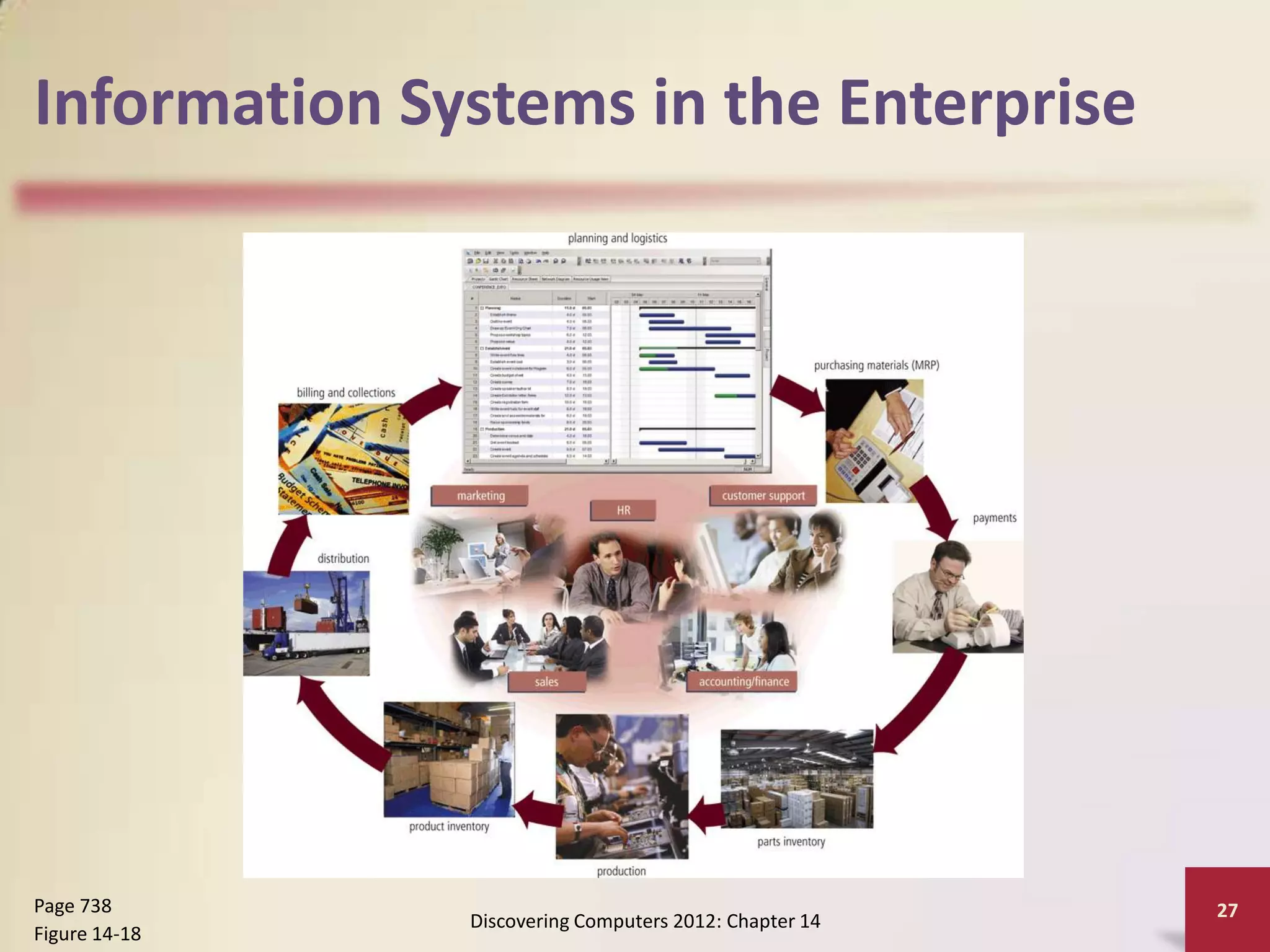
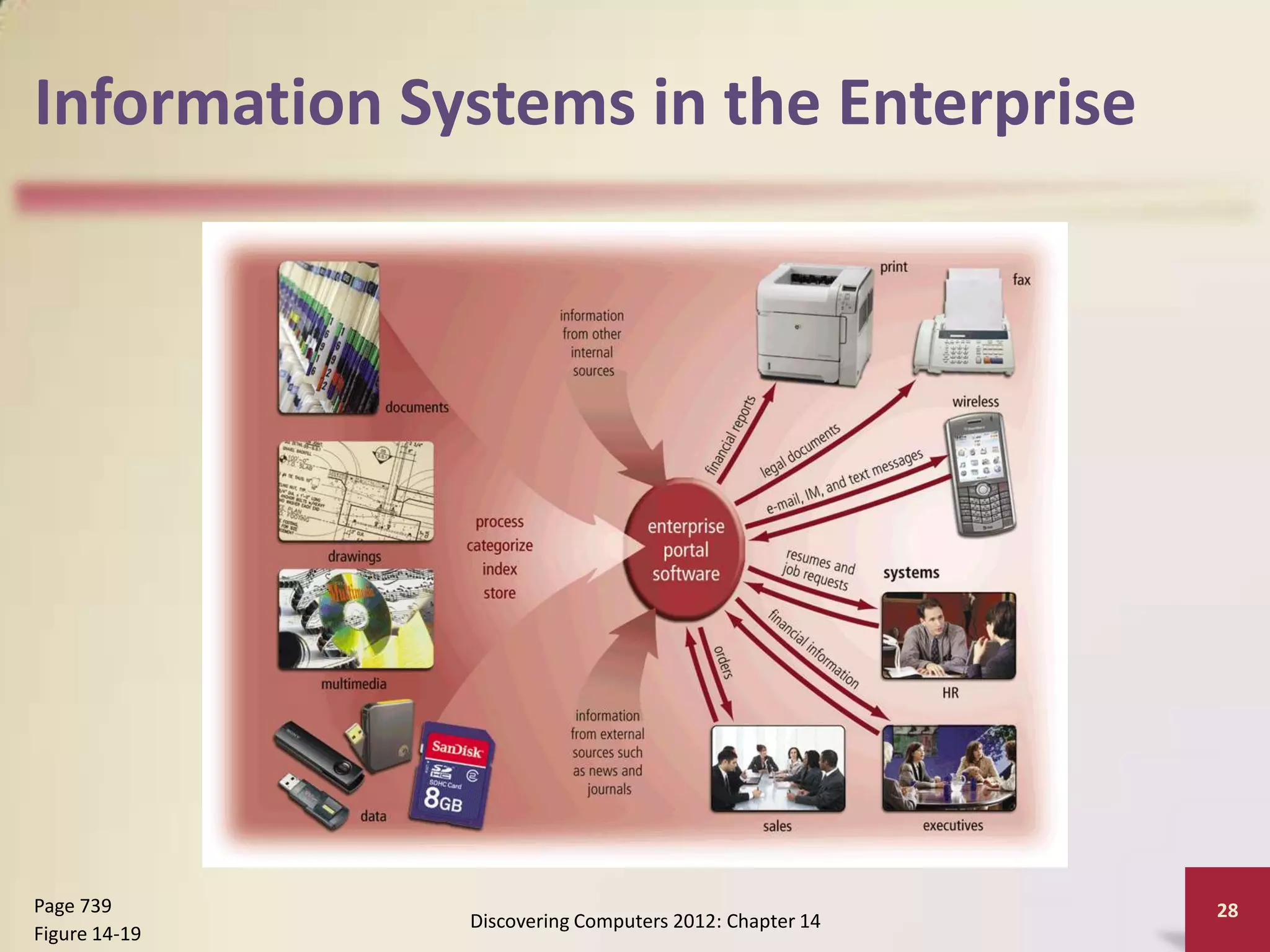
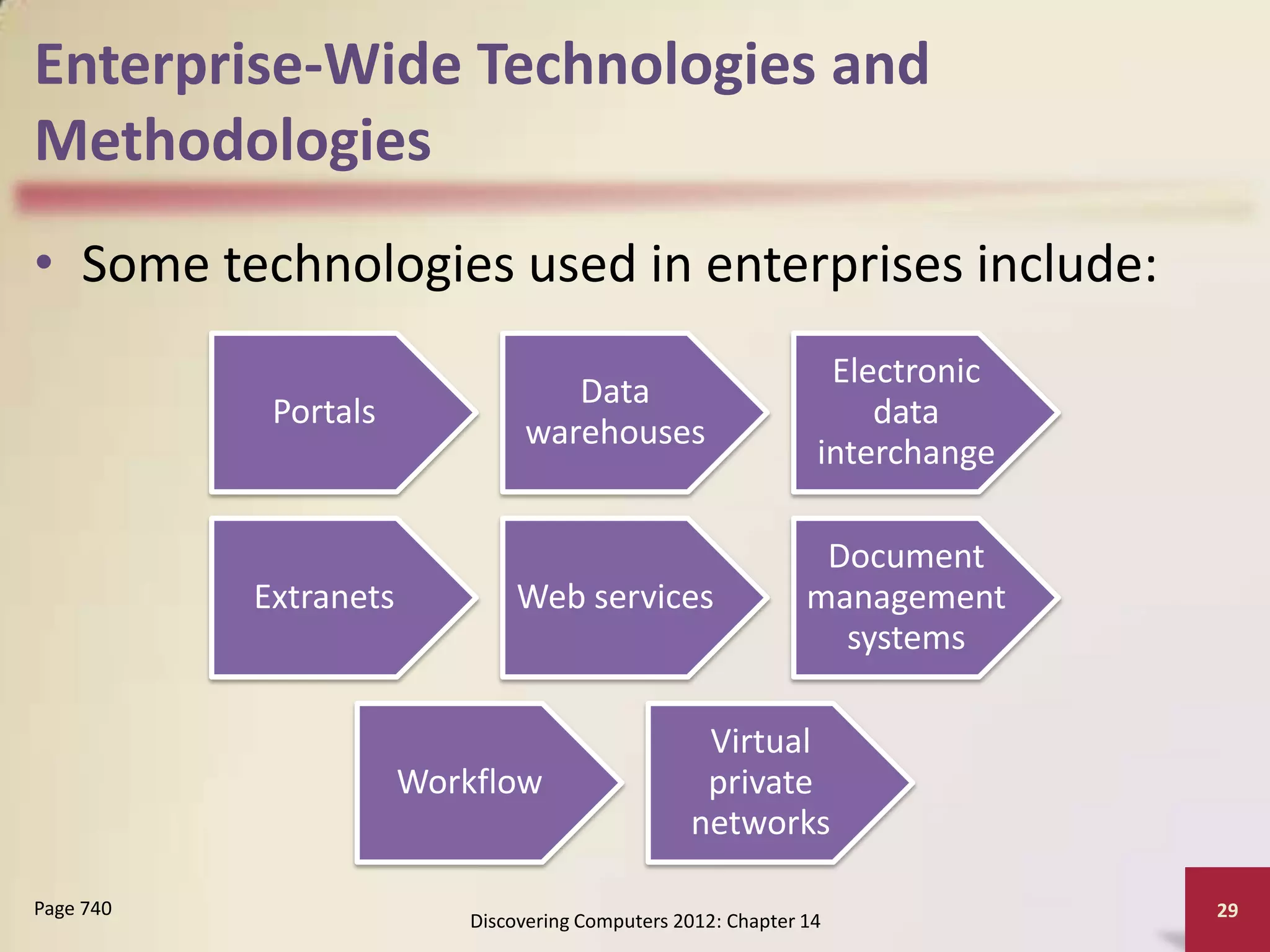
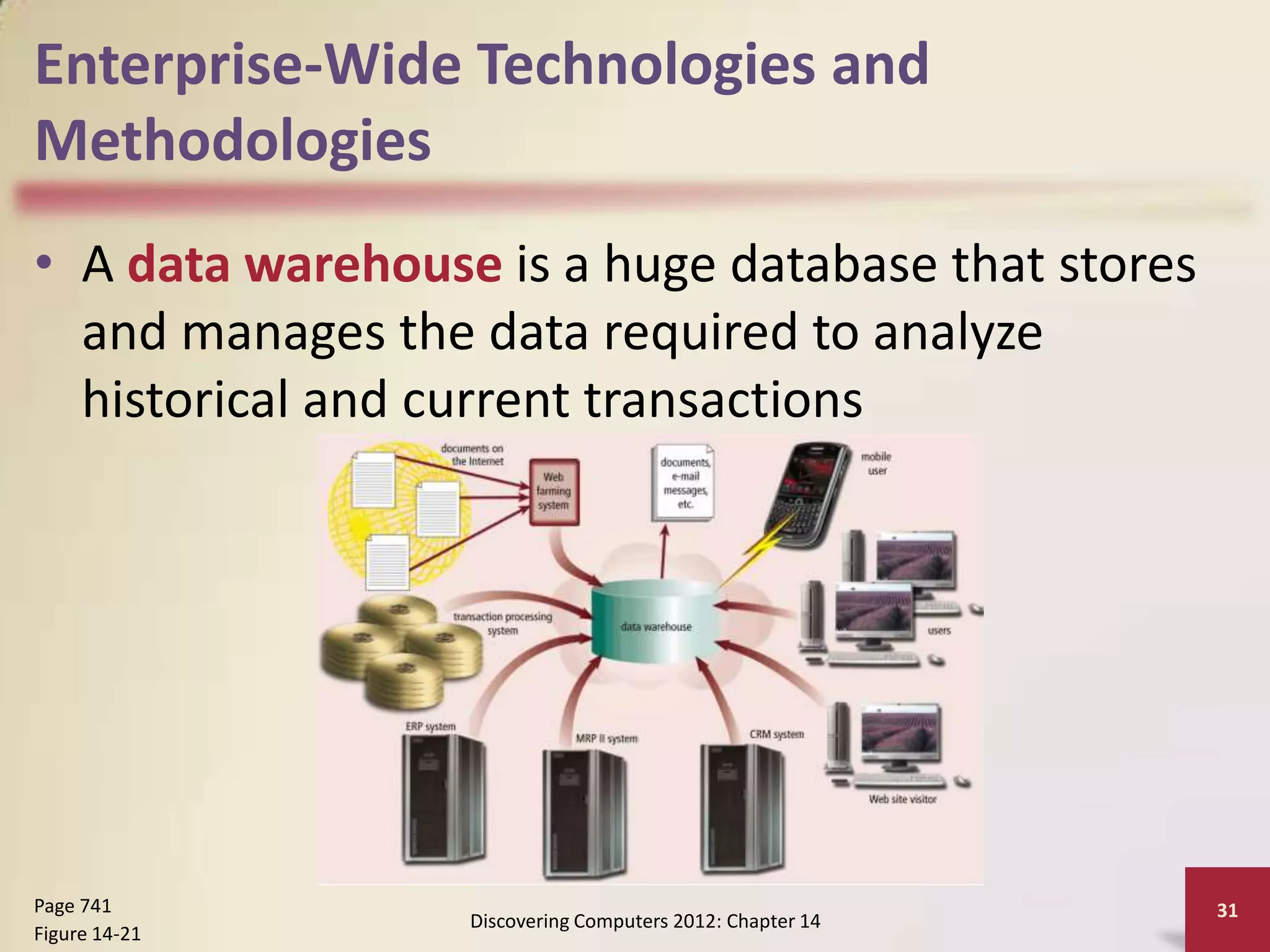
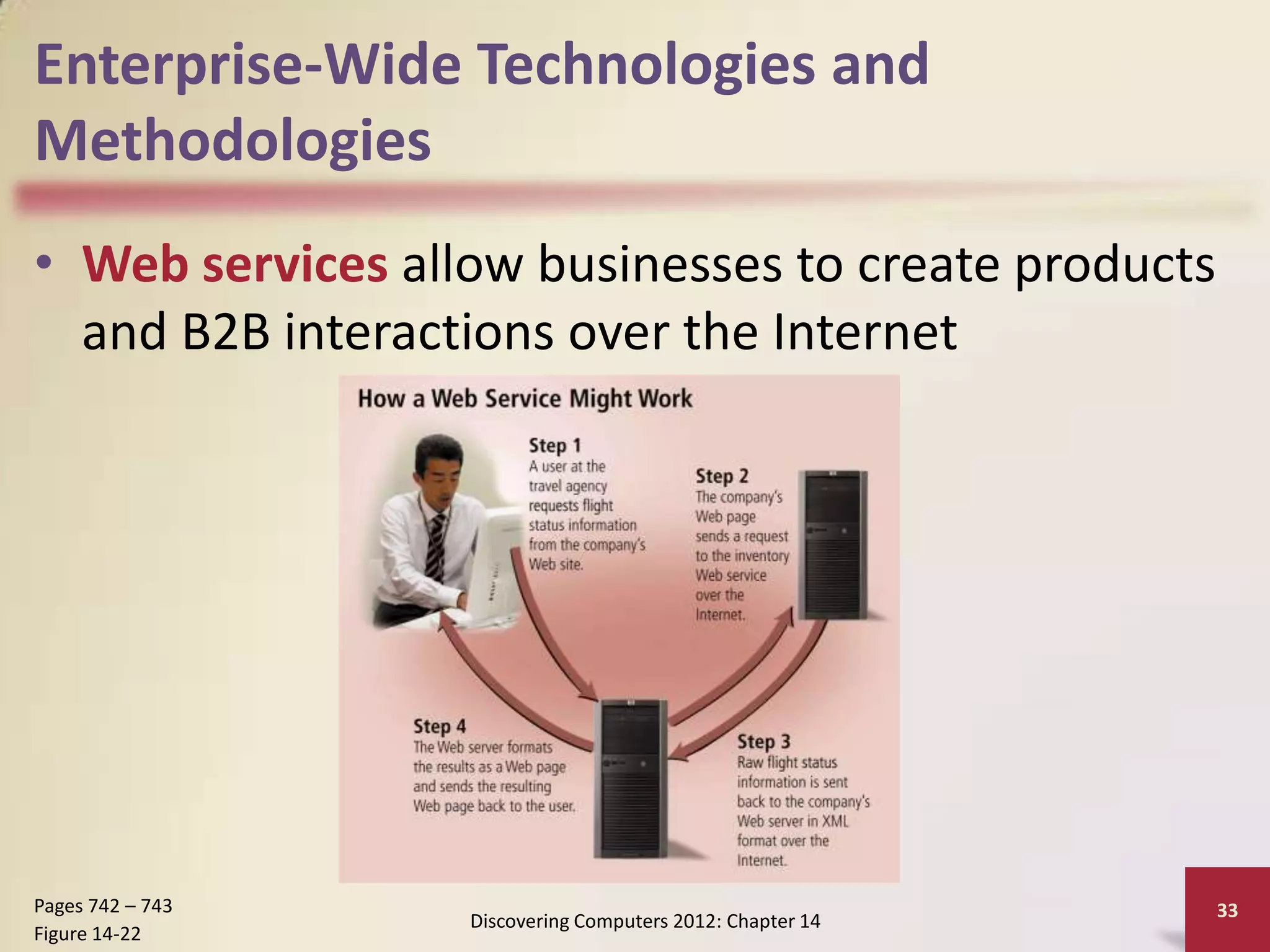
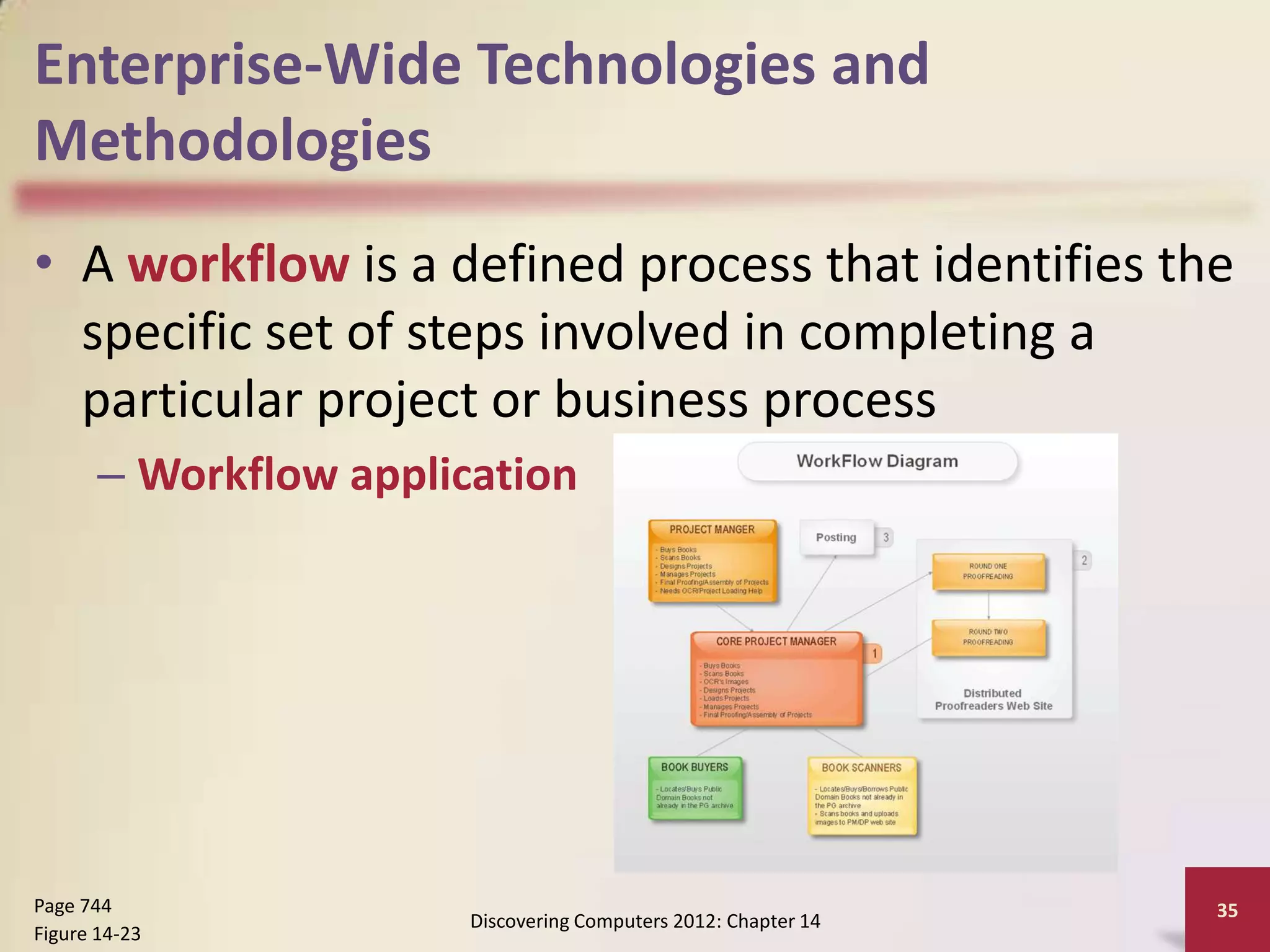
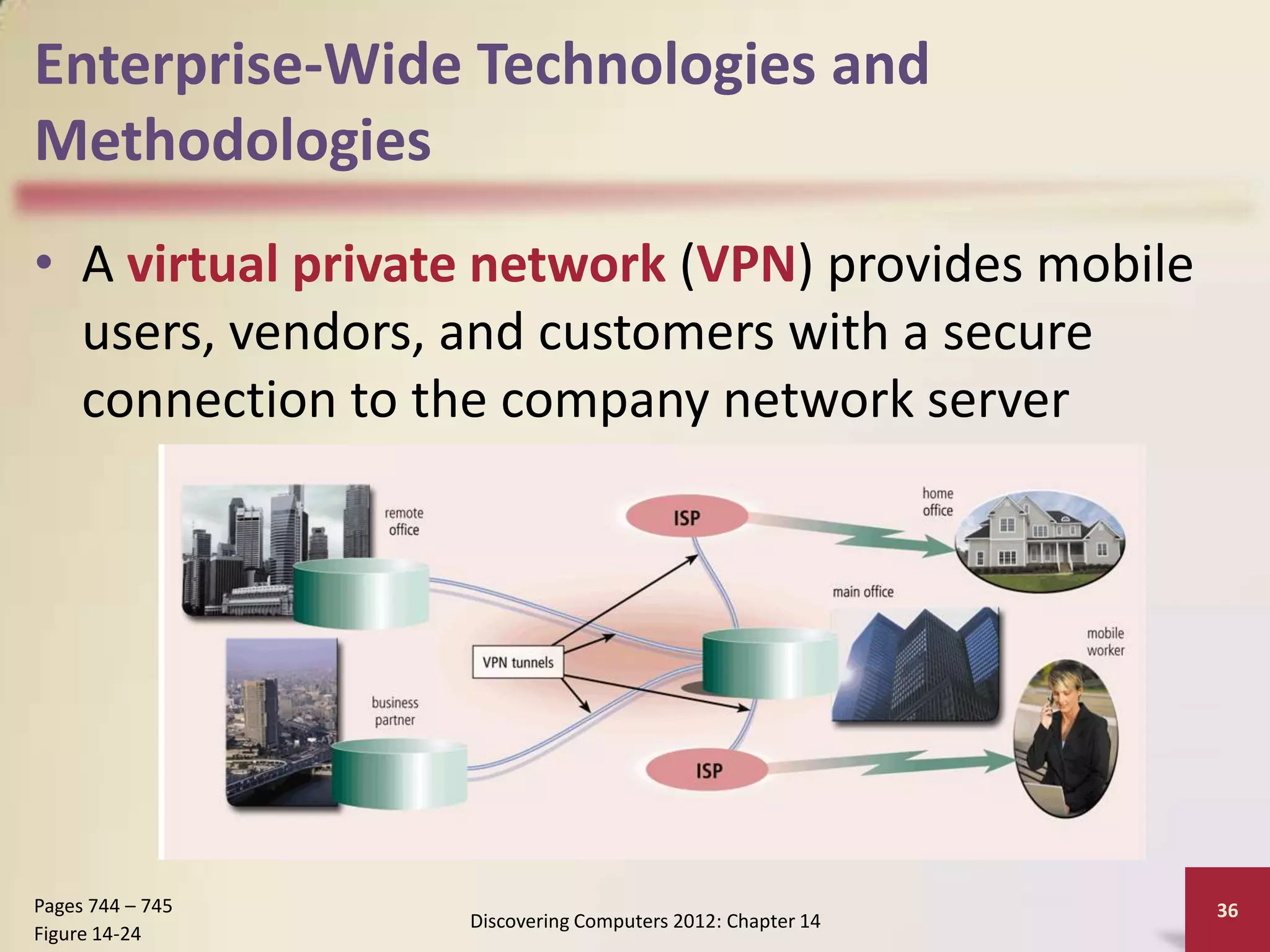
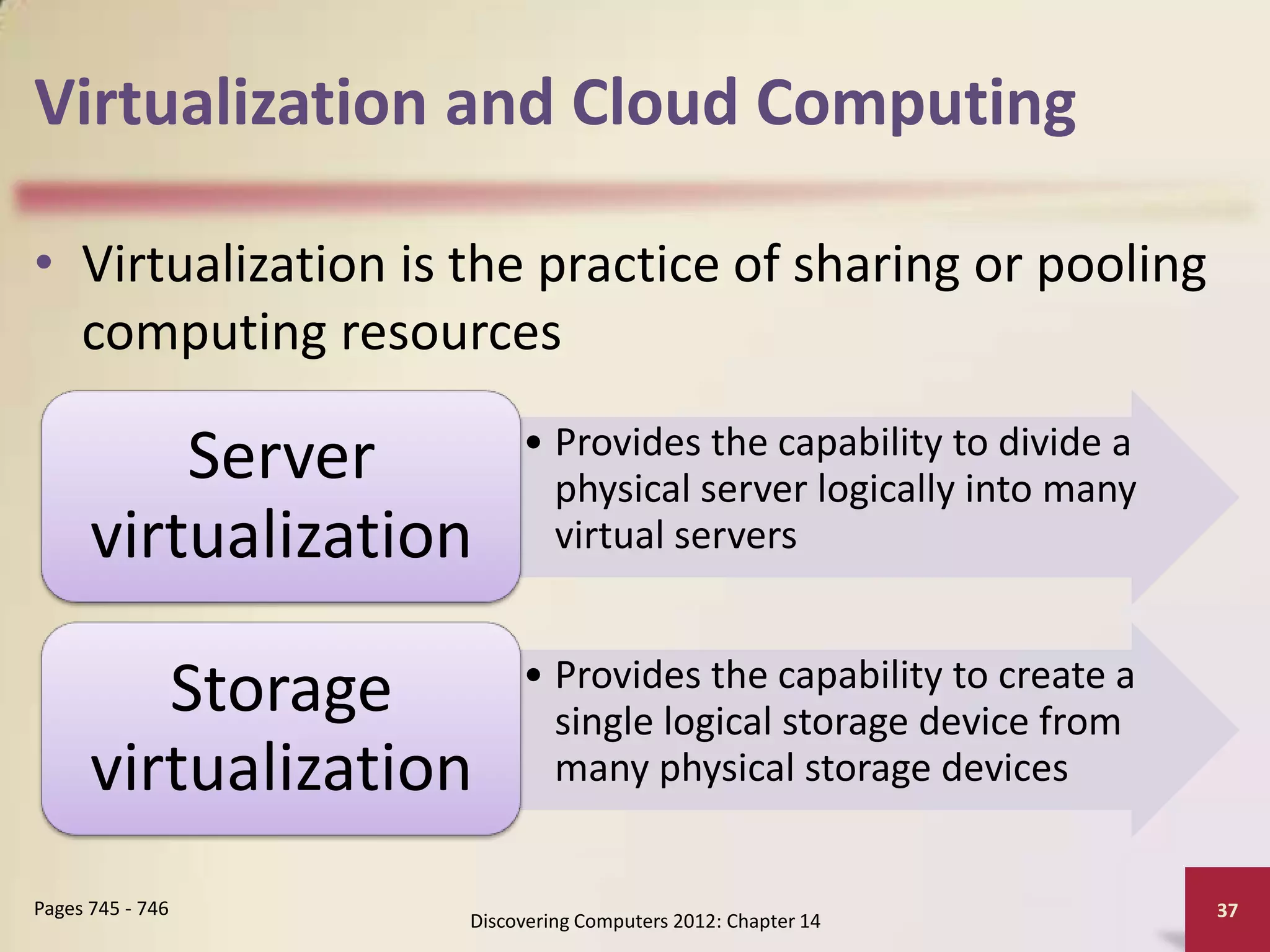
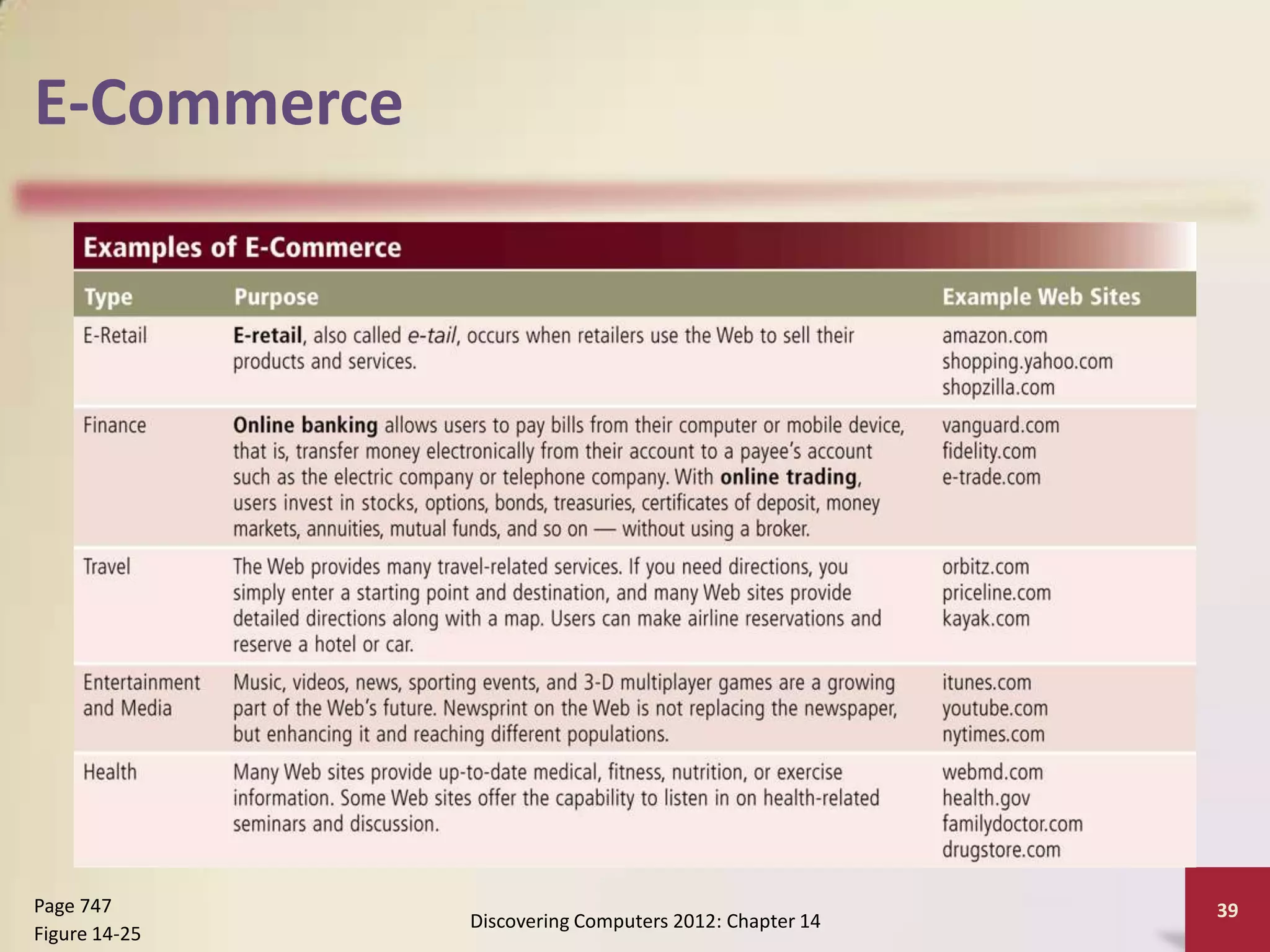
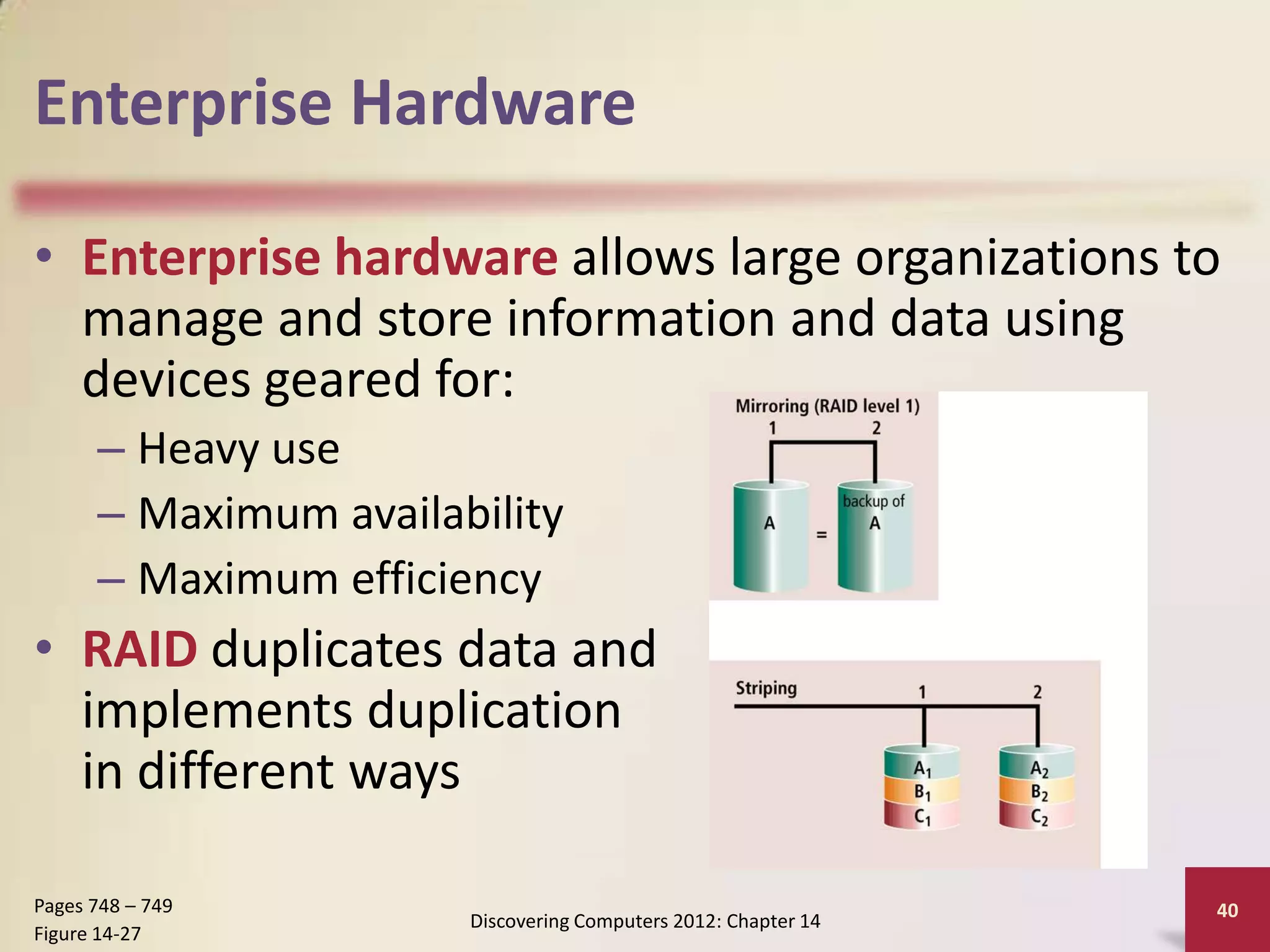
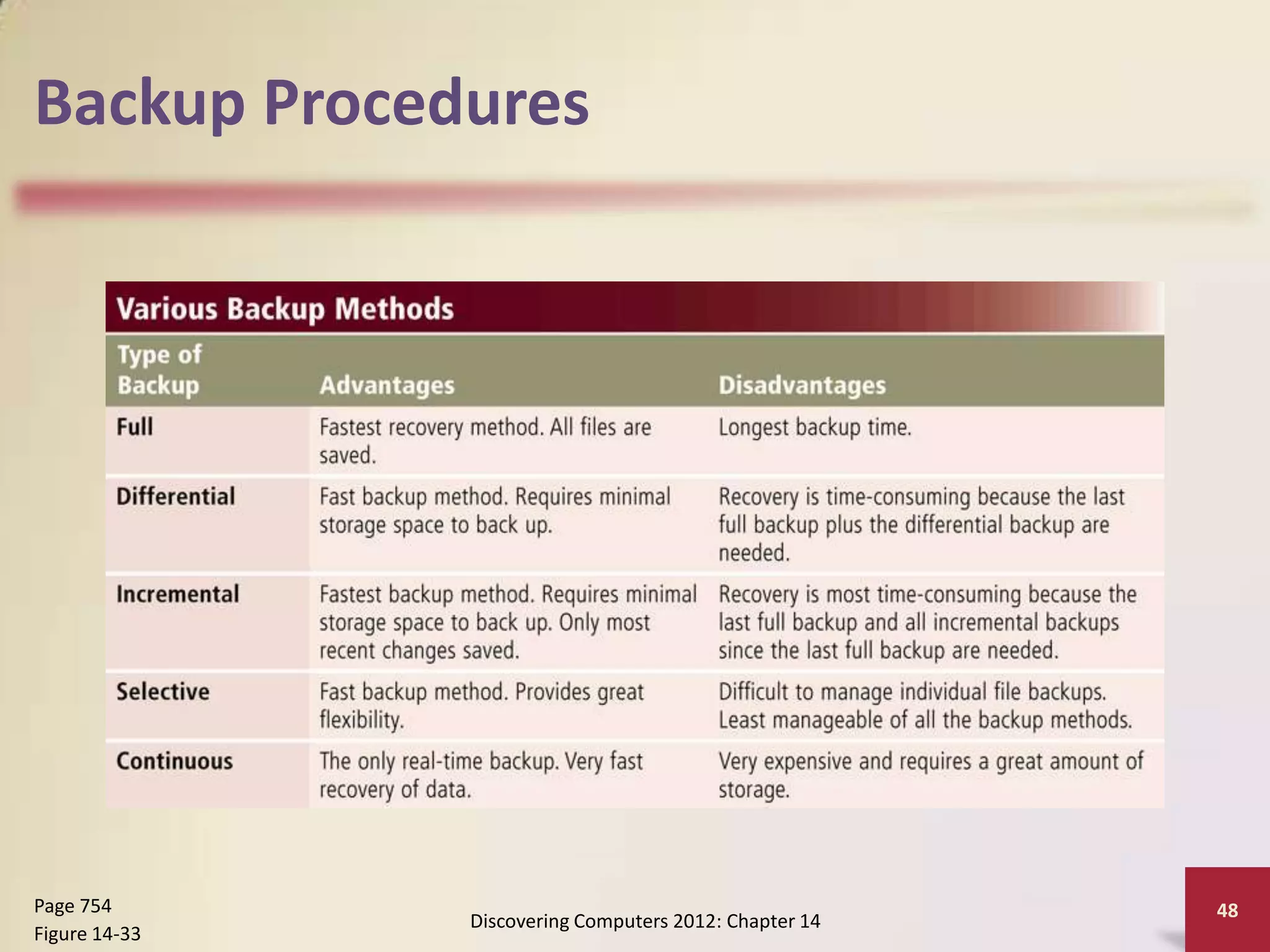
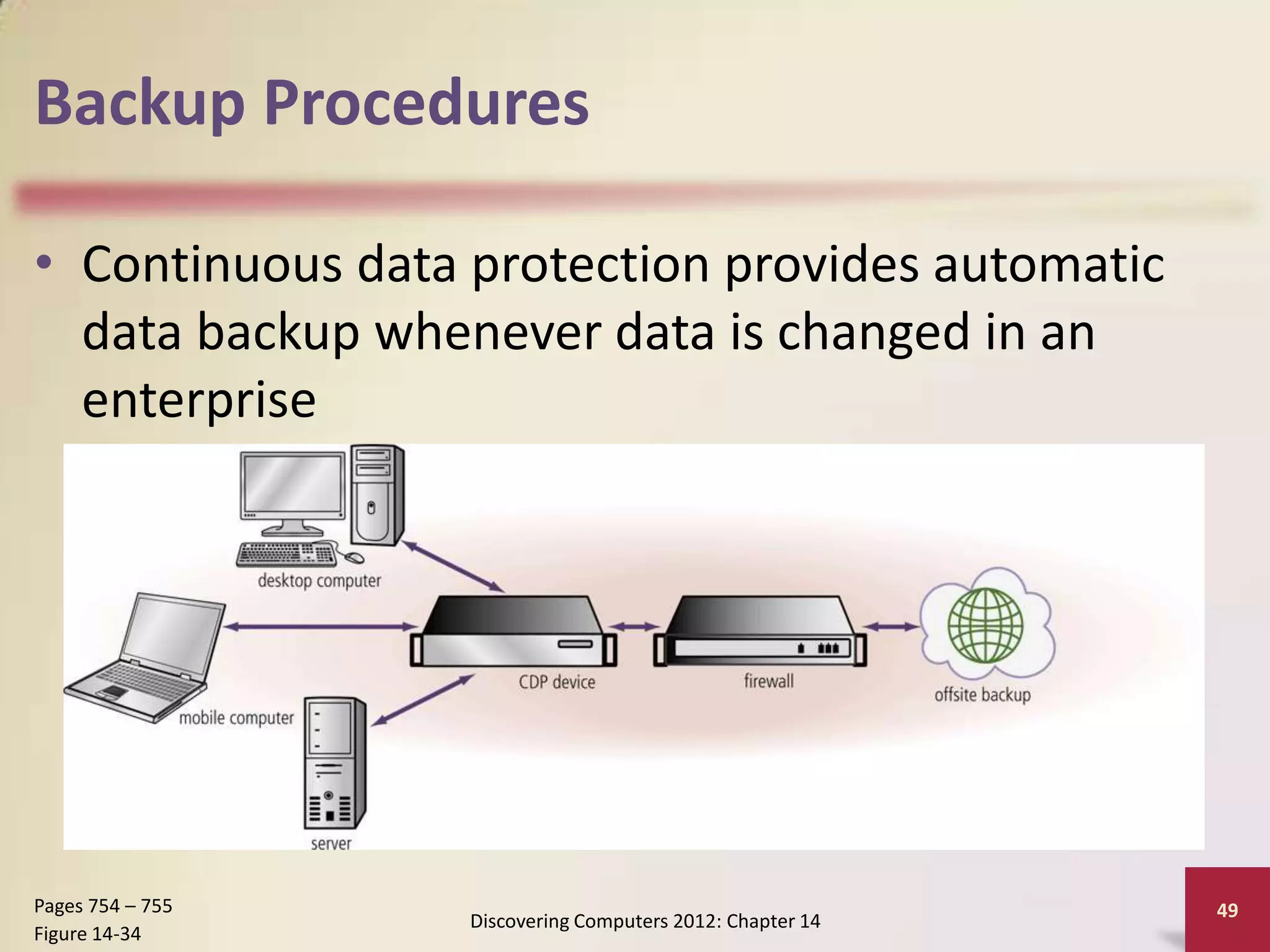
This chapter discusses enterprise computing and the special requirements of large organizations. It describes the various information systems, technologies, and software used across different business units in an enterprise. These include ERP, CRM, virtualization, and cloud computing. The chapter also covers enterprise hardware, high availability, scalability, backup procedures, and disaster recovery plans required for large computing environments.