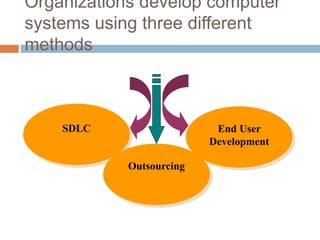
This document discusses end user development, which refers to activities and tools that allow end users who are not professional developers to program computers. It provides examples of end user development like creating 3D models, game modifications, and web mashups. The document outlines characteristics of end user development like the end user being the developer and maintainer. It notes advantages like encouraging user participation and speeding development, but also disadvantages like a lack of expertise potentially leading to underdeveloped systems.