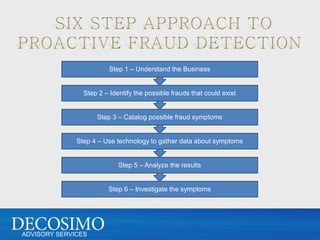
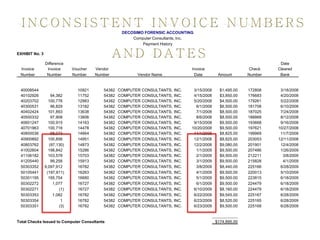
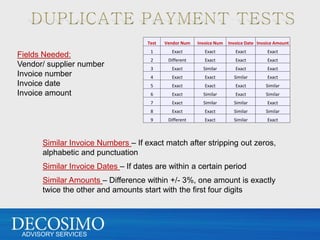
1. Collect transaction data from purchase orders, invoices, checks, and other documents from the vendor/supplier files.
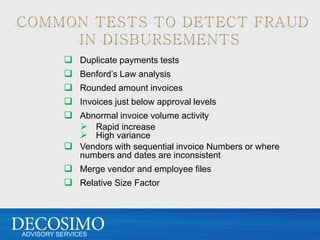
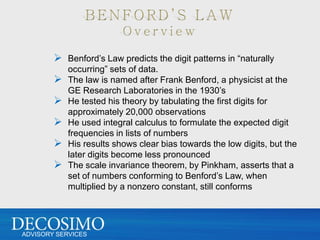
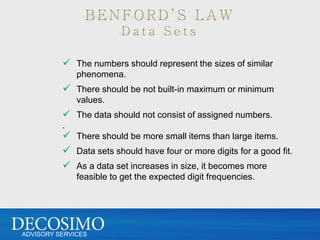
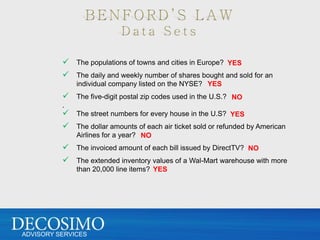
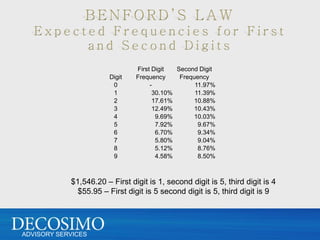
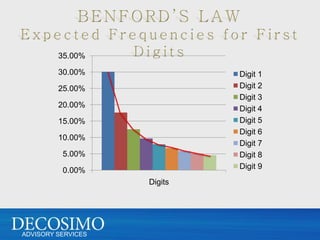
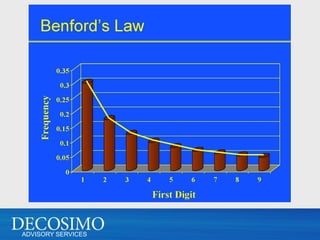
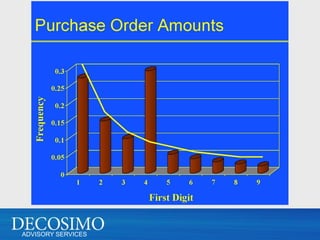
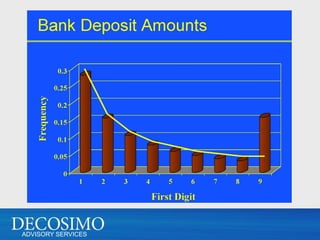
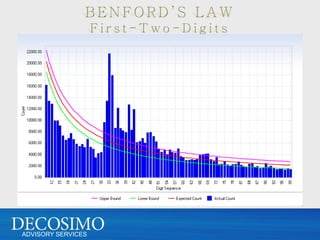
2. Analyze the first digit distributions using Benford's Law to identify anomalies.
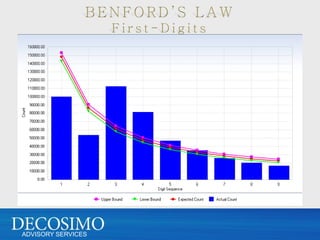
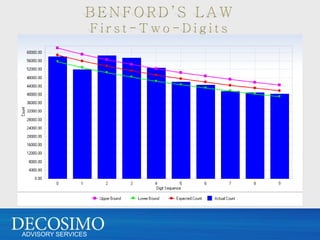
3. Group transactions by amount into strata and calculate expected distributions within each stratum.
4. Compare actual first digit distributions to expected for each strata to identify outliers.
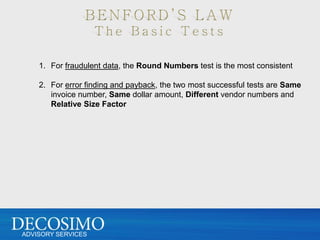
5. Investigate outliers and anomalies further to detect potential fraud patterns.