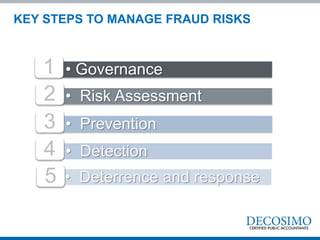
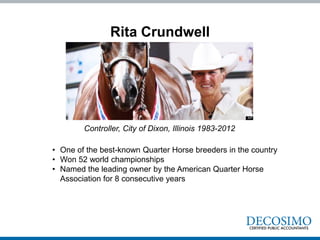
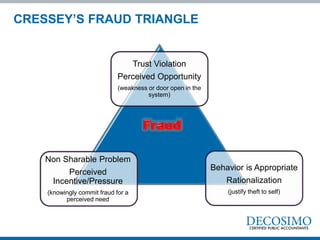
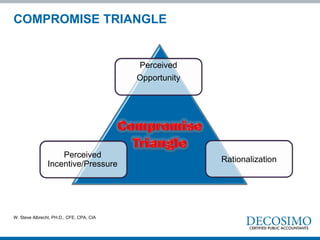
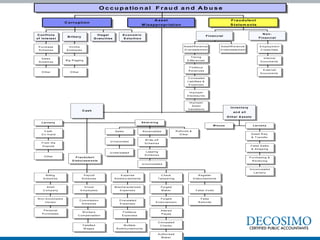
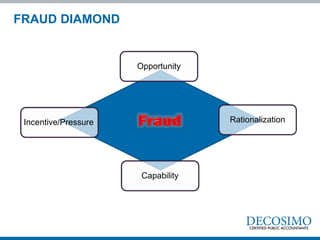
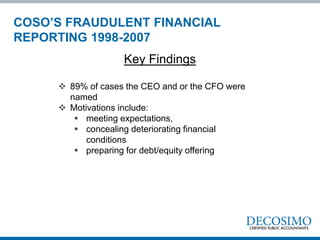
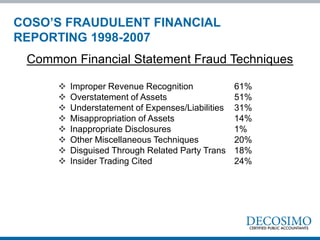
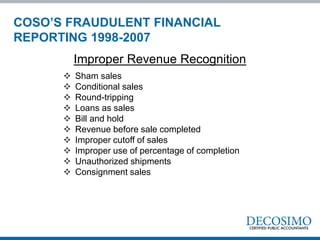
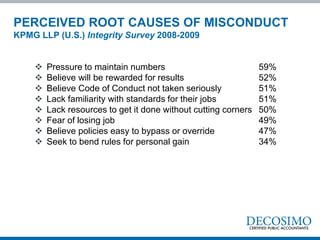
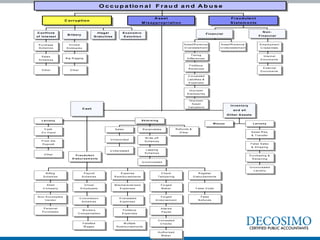
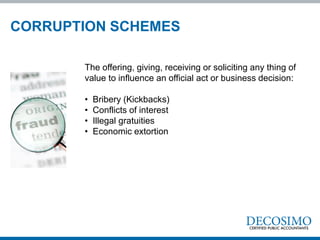
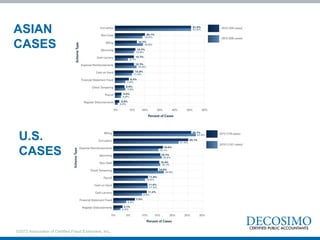
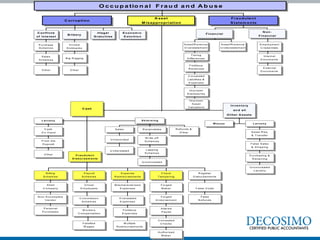
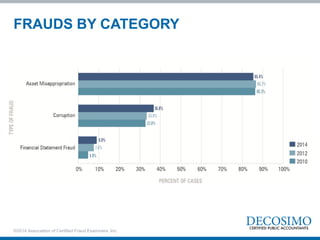
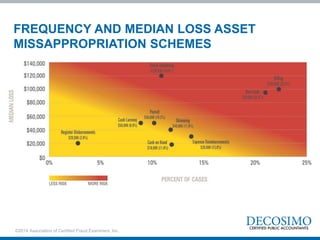
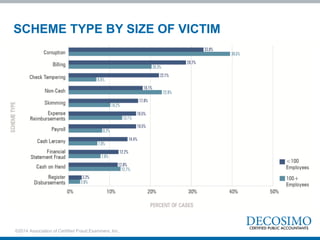
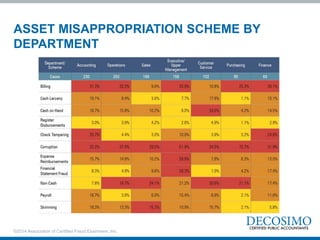
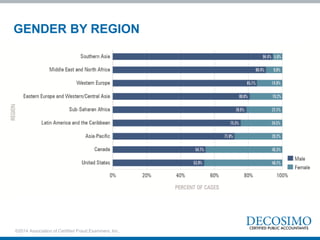
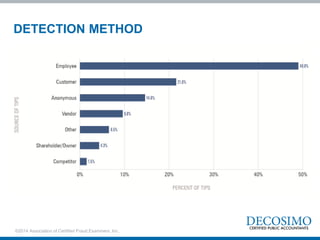
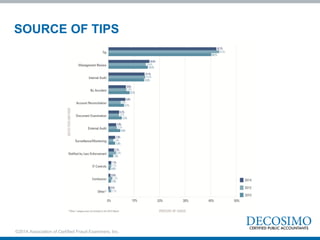
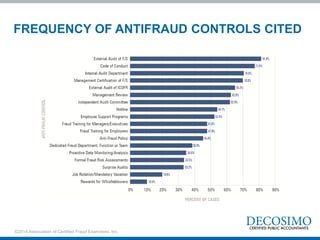
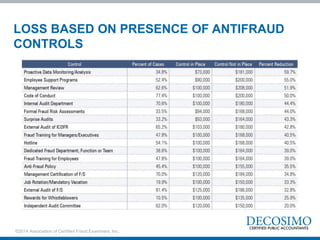
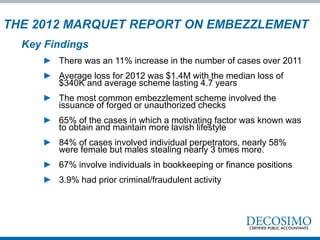
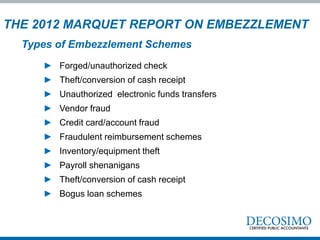
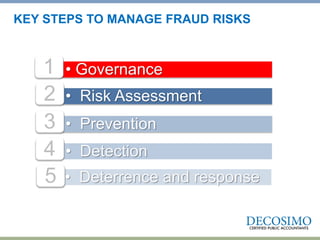
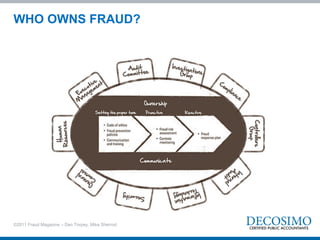
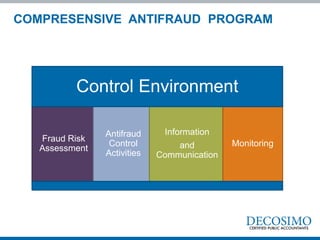
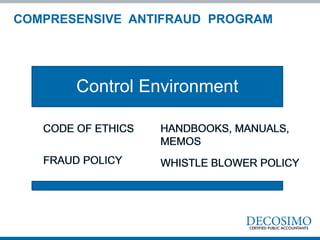
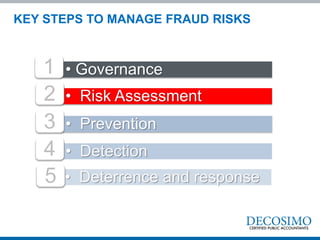
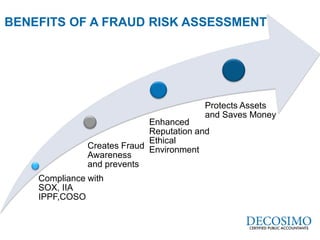
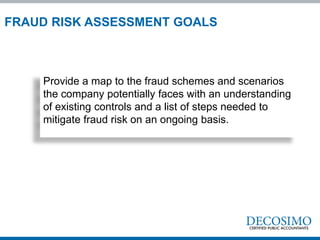
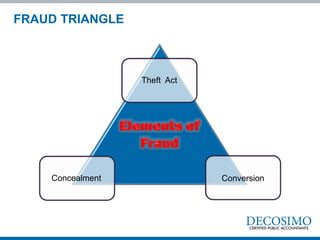
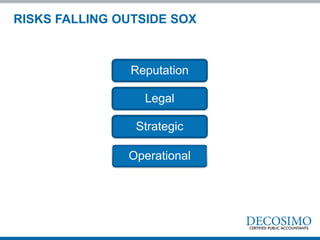
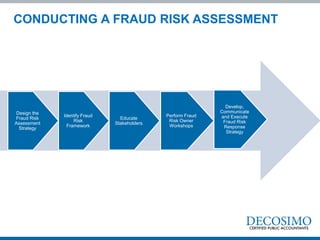
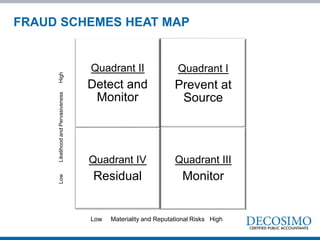
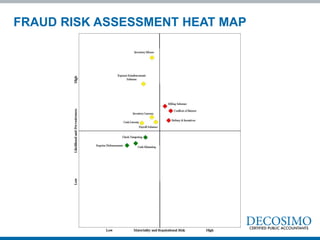
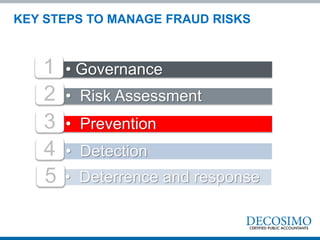
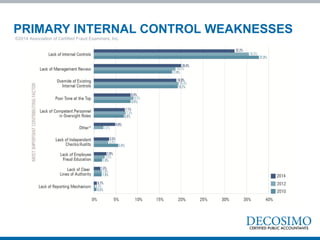
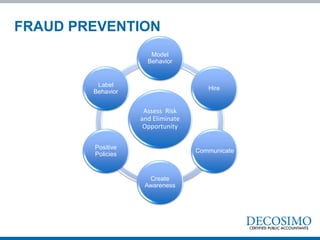
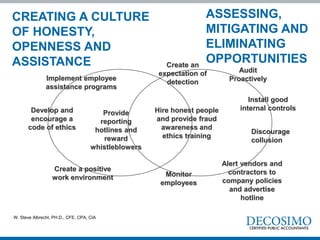
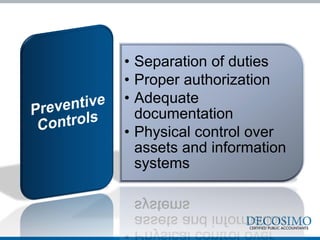
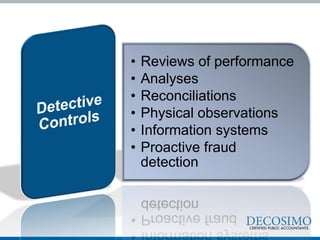
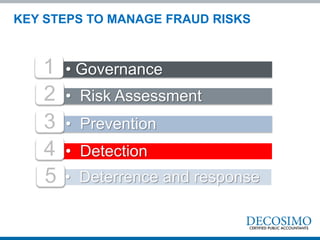
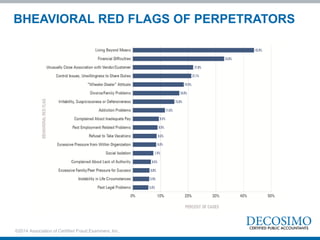
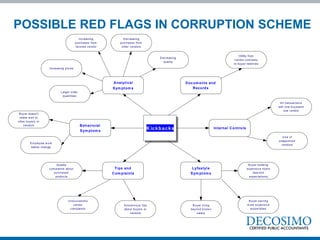
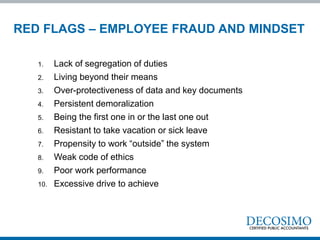
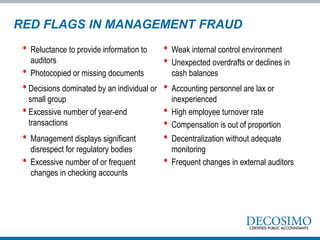
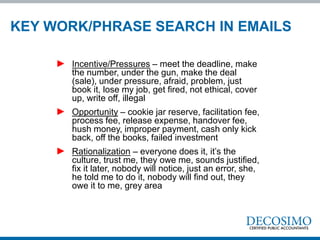
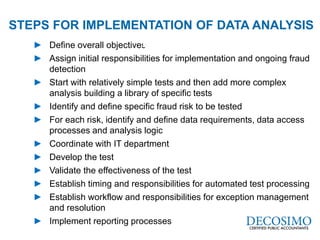
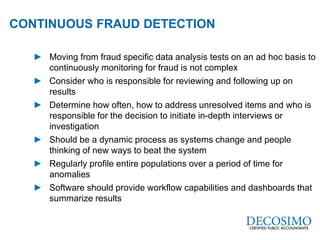
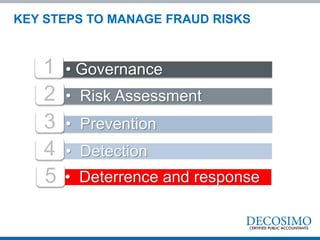
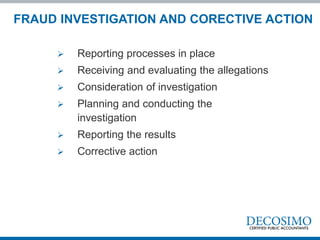
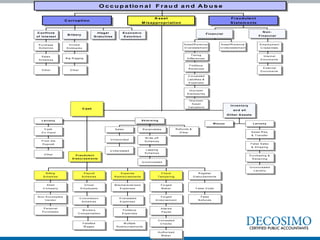
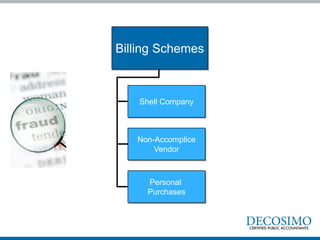
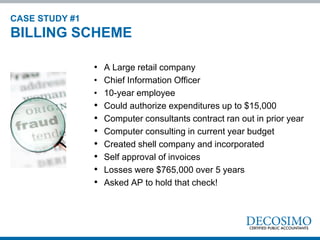
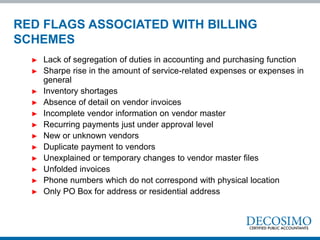
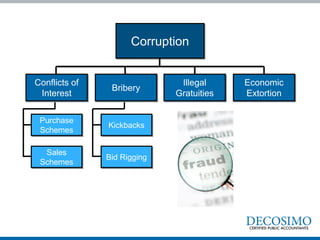
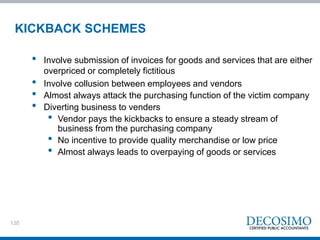
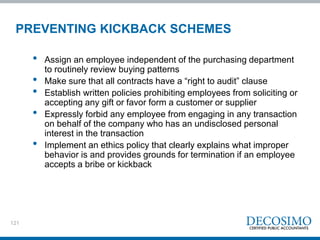
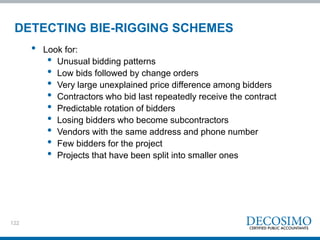
The document discusses fraud risks and provides examples of fraud cases. It discusses key steps to manage fraud risks including governance, risk assessment, prevention, detection, deterrence and response. It then summarizes several high-profile fraud cases including Rita Crundwell who embezzled $53 million from her small town as controller over 20 years through lack of segregation of duties and extravagant lifestyle. The document outlines common fraud schemes and techniques based on research from COSO and the ACFE. It discusses Donald Cressy's fraud triangle of perceived opportunity, incentive/pressure, and rationalization driving fraud. Finally, it provides charts on common financial statement fraud techniques and the distribution of fraud by category and median losses.