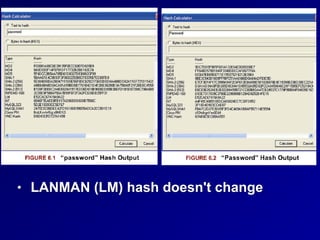
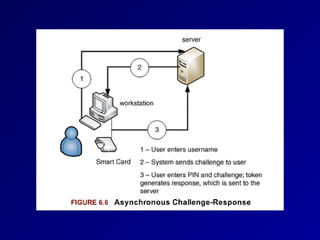
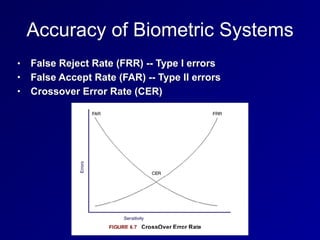
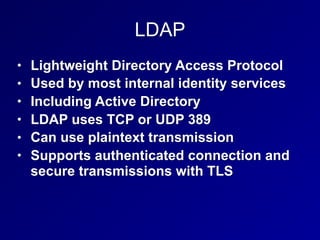
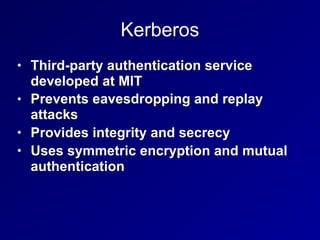
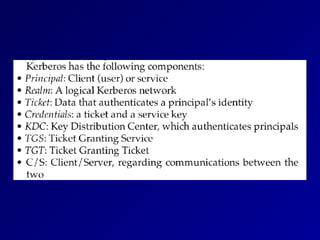
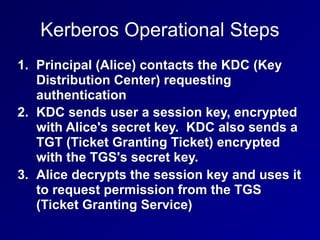
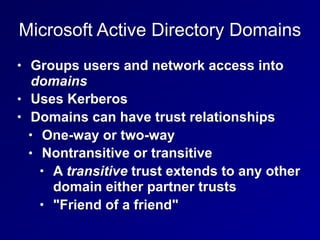
This document provides an overview of identity and access management topics including authentication methods, password types, password hashing and cracking techniques, multifactor authentication, biometric systems, access control technologies like single sign-on and Kerberos, and identity management services. The key points covered are the four types of authentication (something you know, have, are, or where you are), methods for static, one-time, and dynamic passwords, password hashing and cracking attacks, and centralized vs decentralized access control systems.