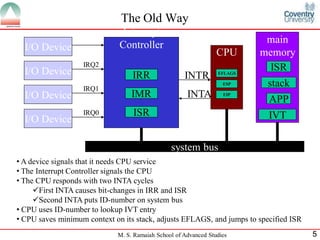
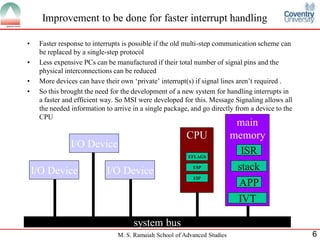
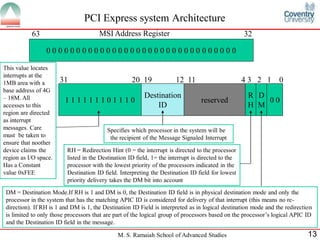
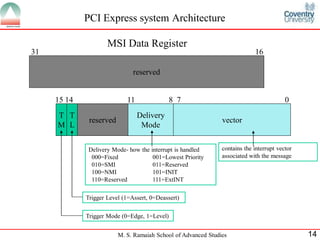
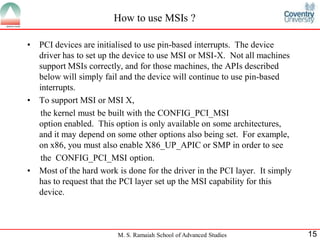
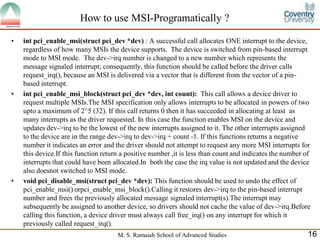
1) The document discusses Message Signaled Interrupts (MSI), an improvement over the traditional interrupt handling method. MSI allows interrupt information to be delivered in one step from a device directly to the CPU.
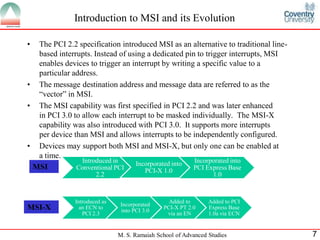
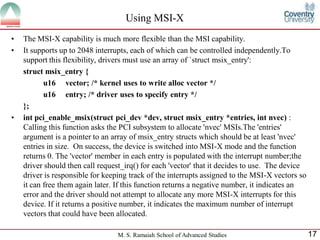
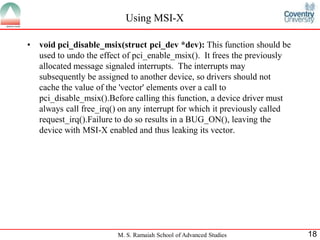
2) MSI was introduced in PCI 2.2 and improved in PCI 3.0 with MSI-X, which supports more interrupts per device. MSI uses a memory write to trigger an interrupt, while traditional interrupts use dedicated pins.
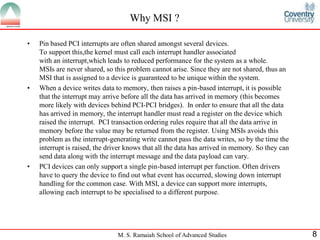
3) The benefits of MSI include faster response, less hardware requirements, guarantee of unique interrupts, and ability to send data with the interrupt. MSI also avoids ordering issues with traditional interrupts.
![M. S. Ramaiah School of Advanced Studies 23
References
[1] The MSI driver Guide How To[Online] Available From:
http://git.kernel.org/?p=linux/kernel/git/torvalds/linux-
2.6.git;a=blob;f=Documentation/PCI/MSI-HOWTO.txt;hb=HEAD
(Accessed:28 January 2013)
[2] IA-32 Intel® ArchitectureSoftware Developer’s Manual,Vol-3,2003
[3] Ravi,B.,Anderson,D.,Shanley,T.,Jow,W.(2003) PCI Express System
Archotecture,Addision-Wesley](https://image.slidesharecdn.com/cjb0412001-anshuman-asp-esd2528-presentation-130620022621-phpapp01/85/Message-Signaled-Interrupts-23-320.jpg)