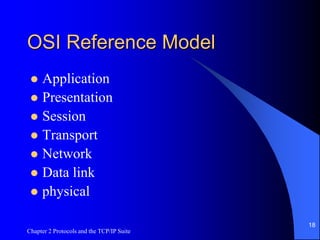
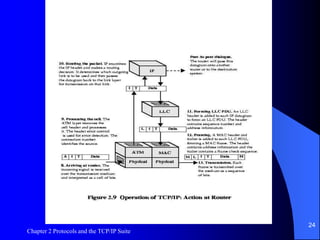
Chapter 2 of the document focuses on protocols and the TCP/IP suite, covering topics such as the architecture of high-speed networks, the functioning of TCP and IP, and network management issues like congestion control and quality of service. It outlines the layered structure of protocols, detailing how these layers interact and the essential features needed for effective communication. The chapter also highlights the importance of routers in internetworking between different subnetworks and provides specific examples of TCP applications.