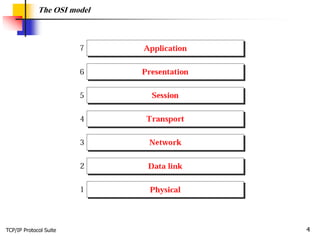
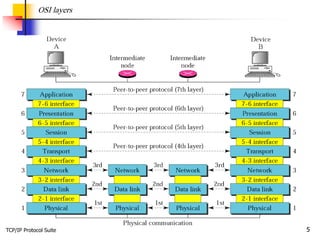
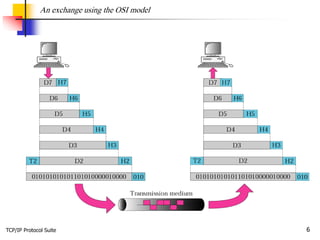
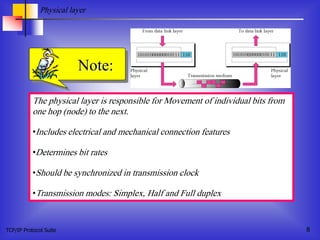
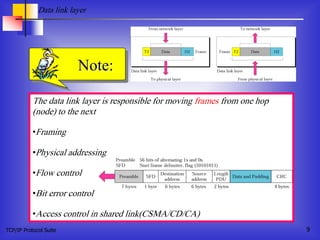
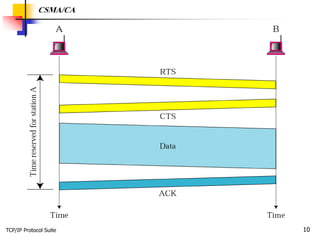
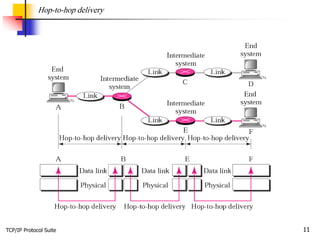
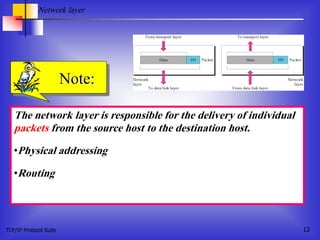
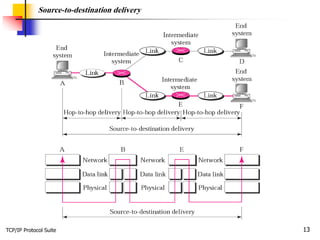
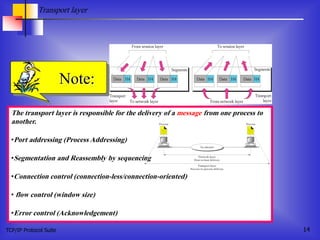
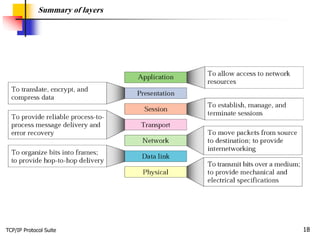
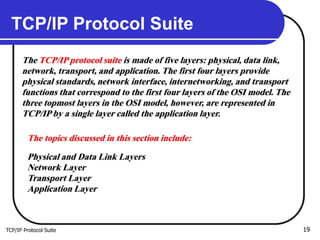
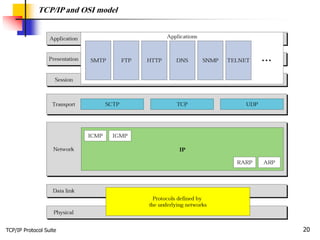
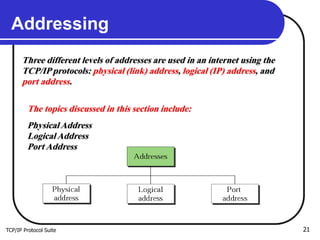
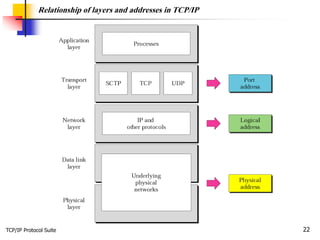
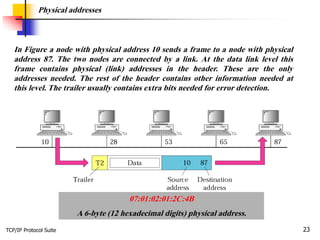
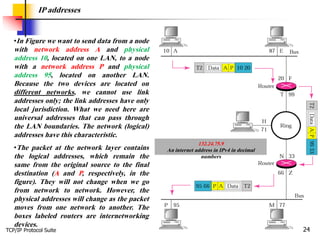
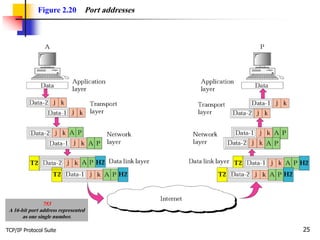
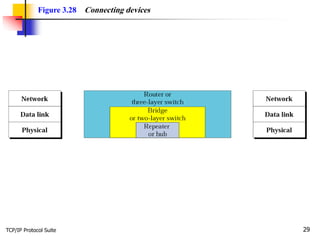
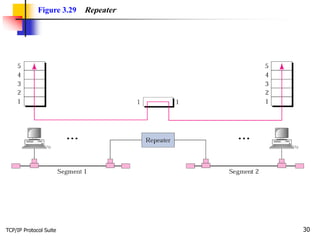
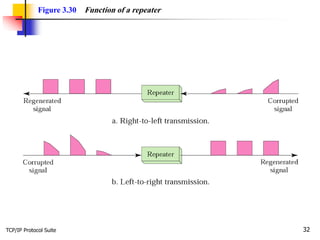
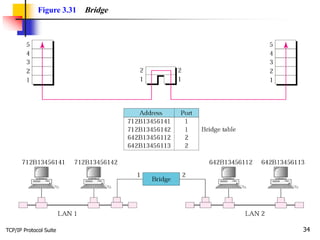
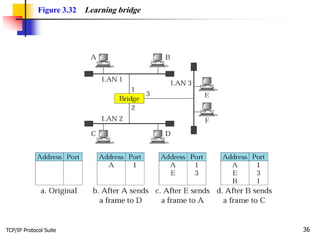
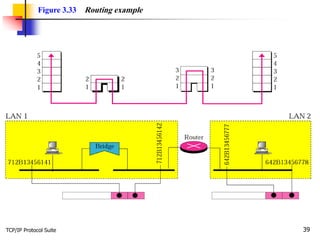
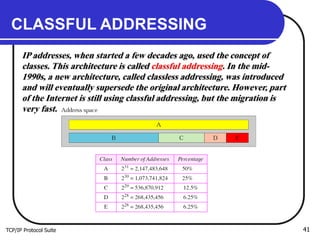
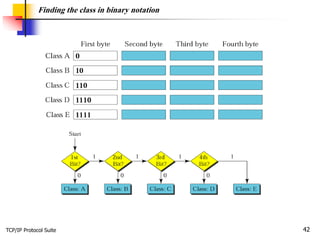
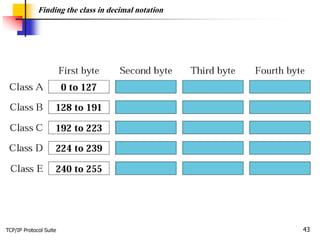
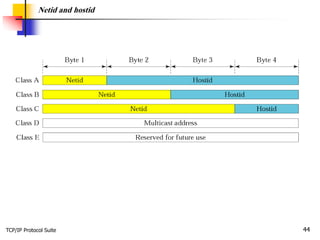
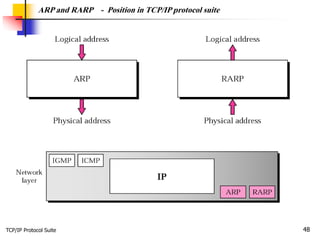
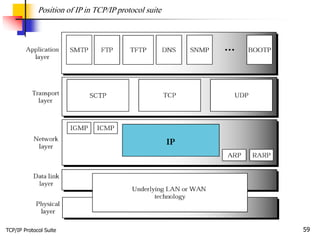
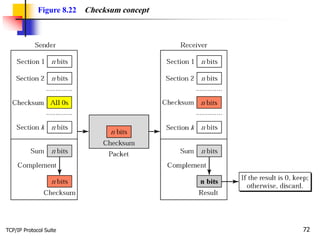
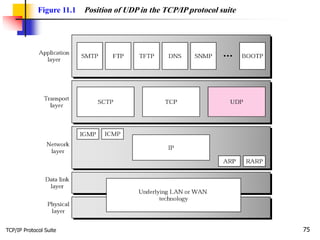
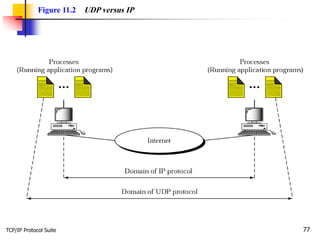
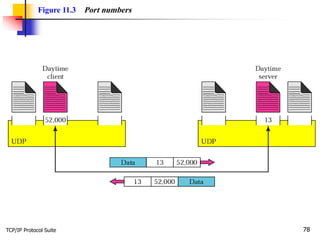
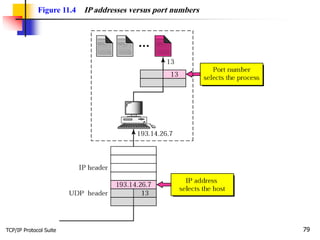
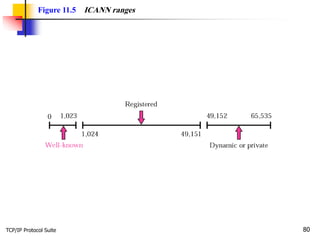
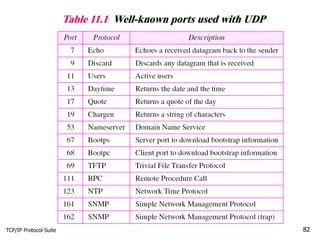
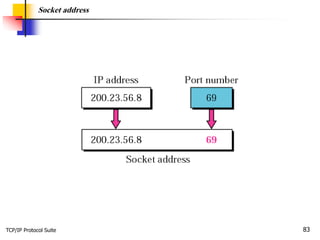
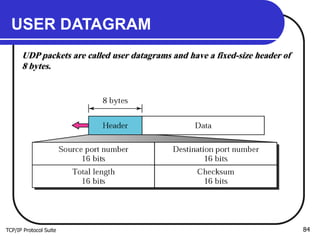
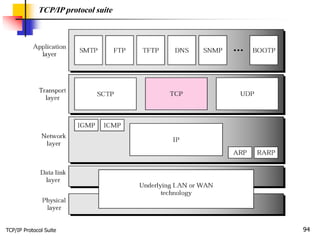
The document provides an overview of the TCP/IP protocol suite and OSI model. It discusses the seven layers of the OSI model and their functions. It then explains that the TCP/IP protocol suite consists of five layers that correspond to the bottom four layers of the OSI model, with the top three OSI layers represented by a single application layer in TCP/IP. The document goes on to cover addressing in TCP/IP networks, different versions of the IP protocol, and methods for connecting local area networks.