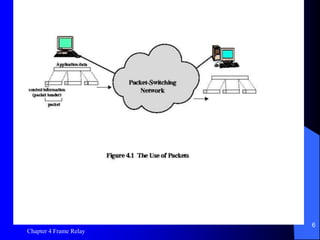
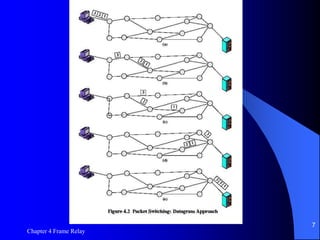
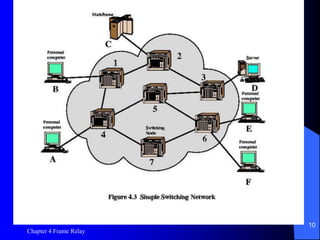
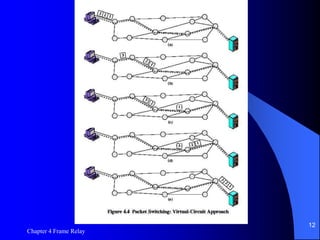
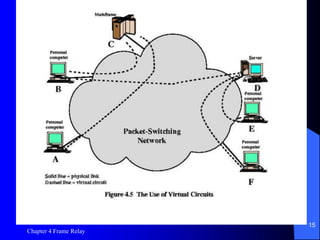
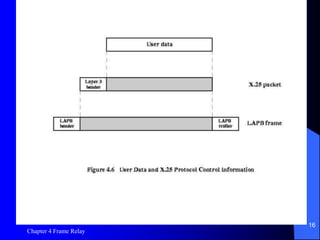
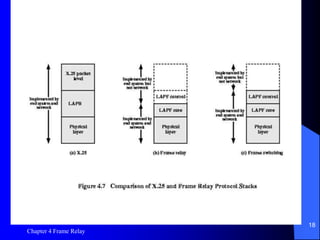
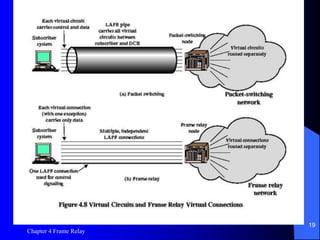
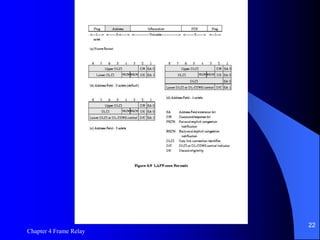
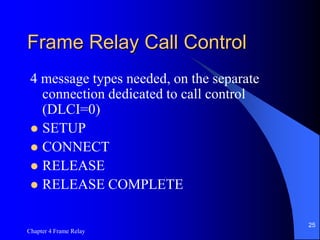
Chapter 4 discusses Frame Relay technology, a packet-switching method effective for long-distance data communications with advantages including flexibility and resource sharing, while also noting disadvantages like time delays and overhead. It contrasts Frame Relay with circuit-switching, highlighting the efficiency of packet transmission and the concept of virtual circuits. Additionally, it covers the architecture of Frame Relay networks, their call control mechanisms, and the relation to the older X.25 protocol.