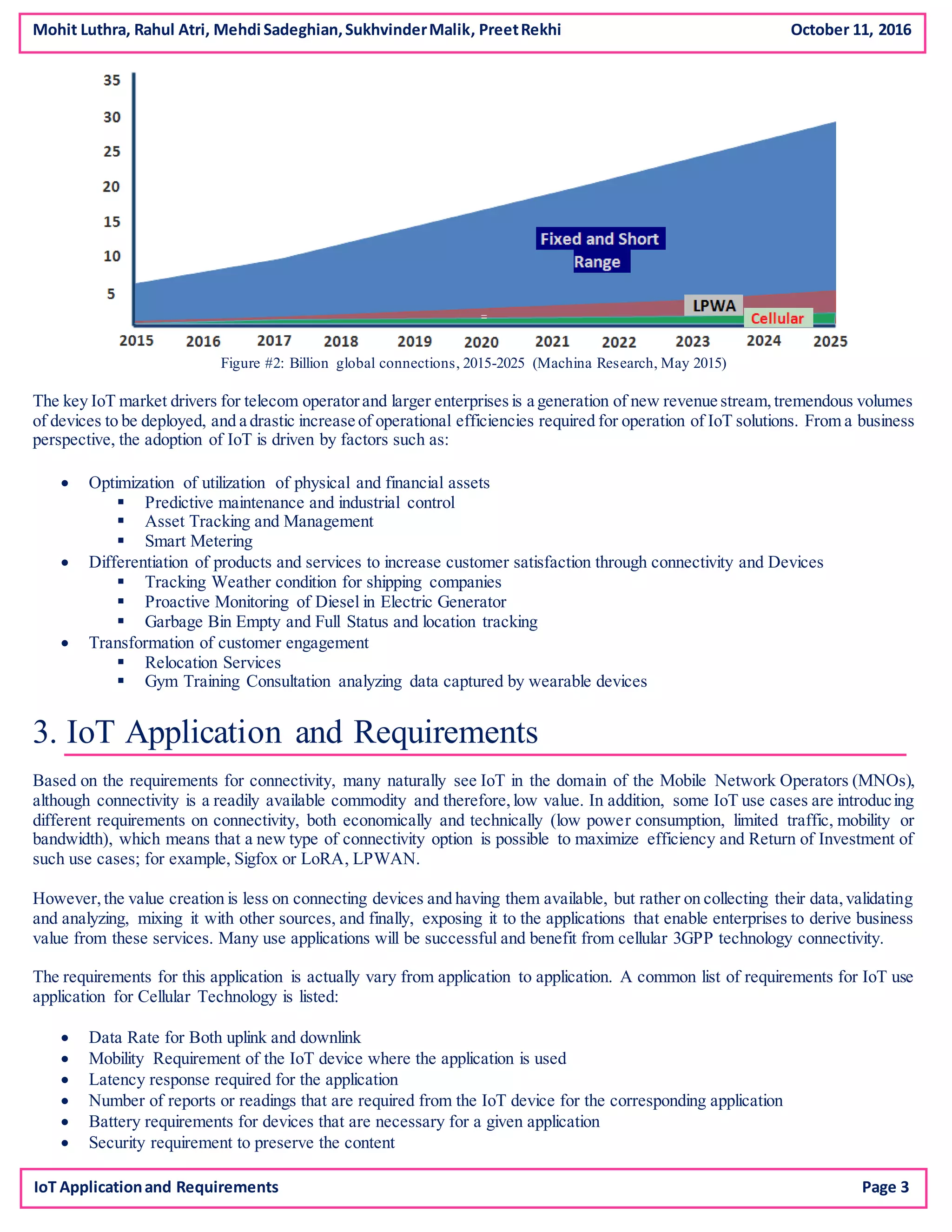
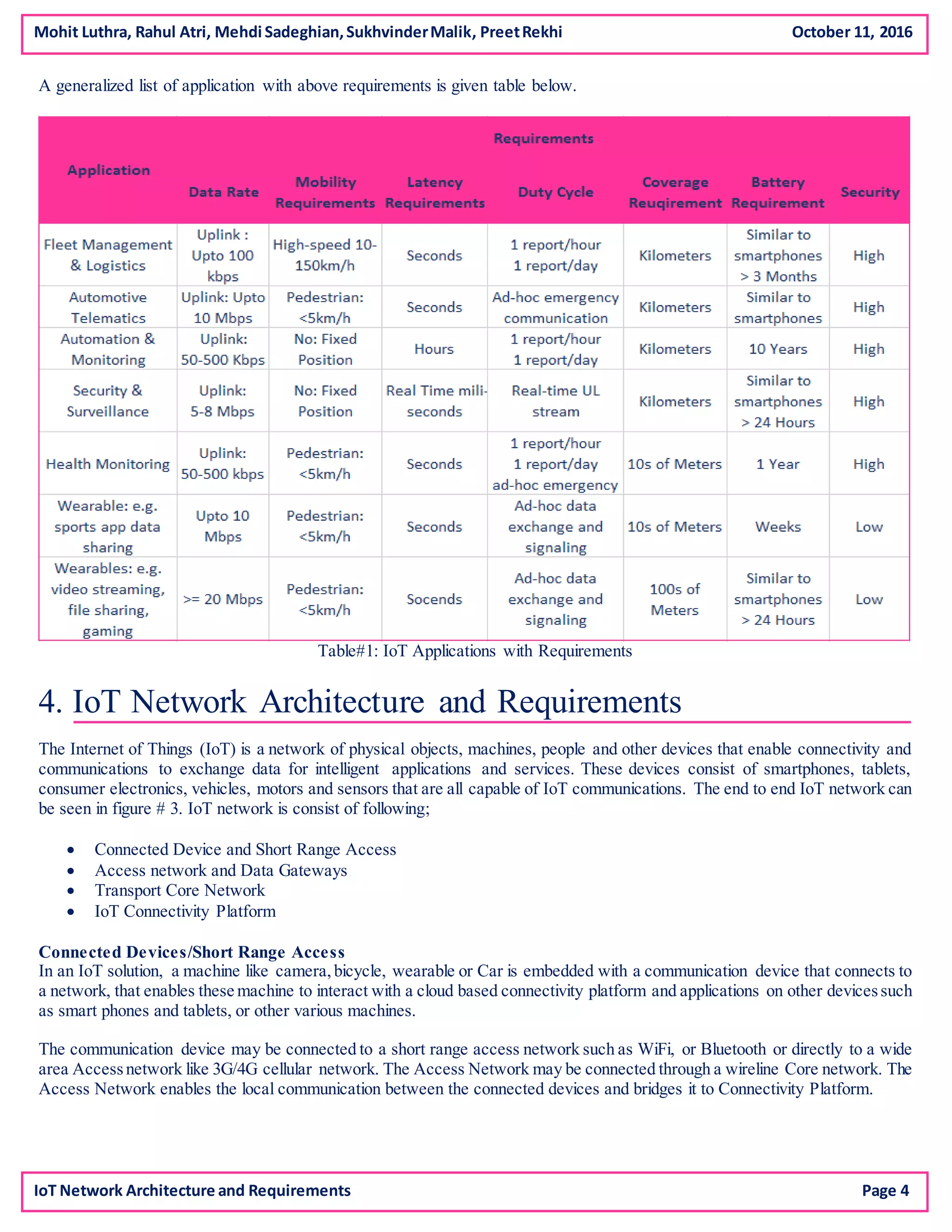
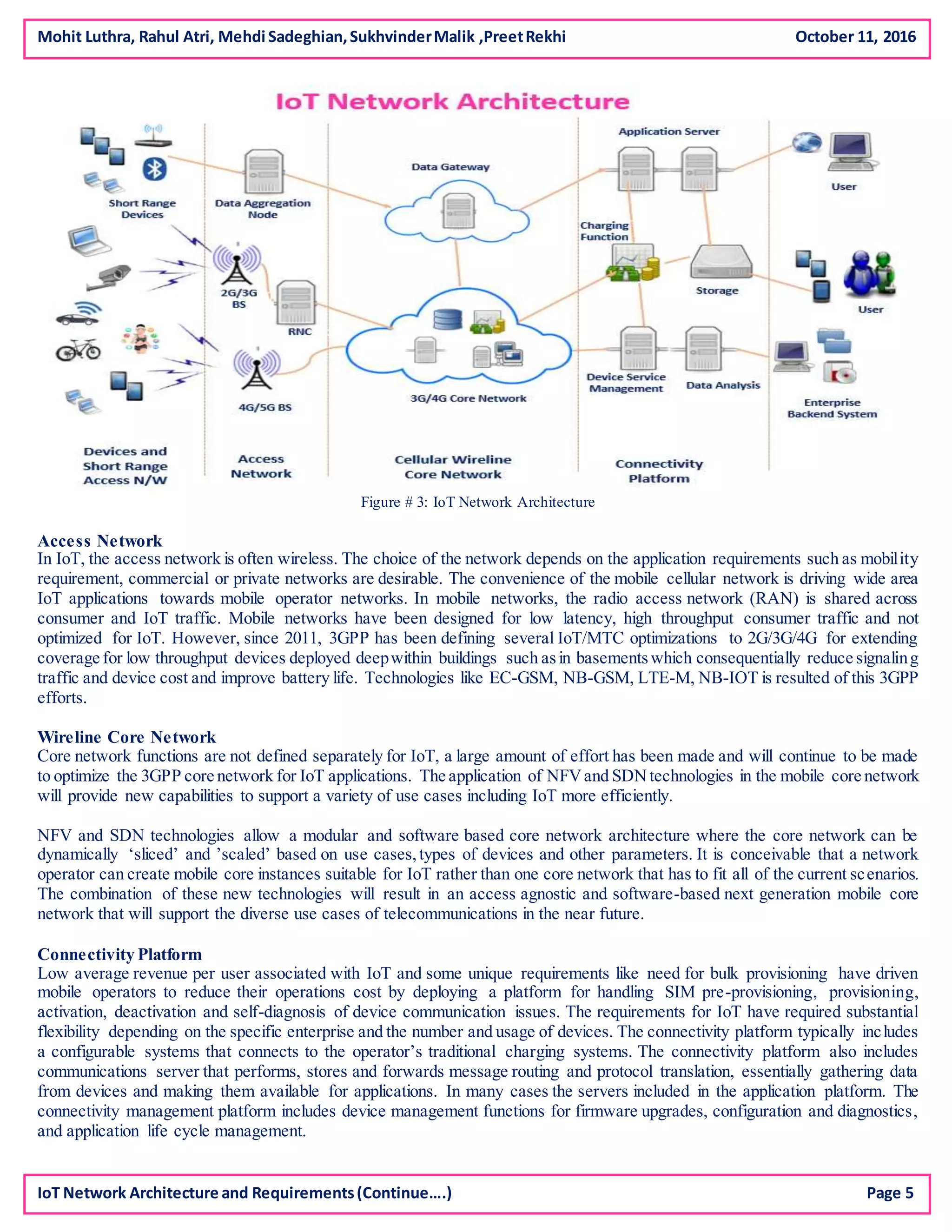
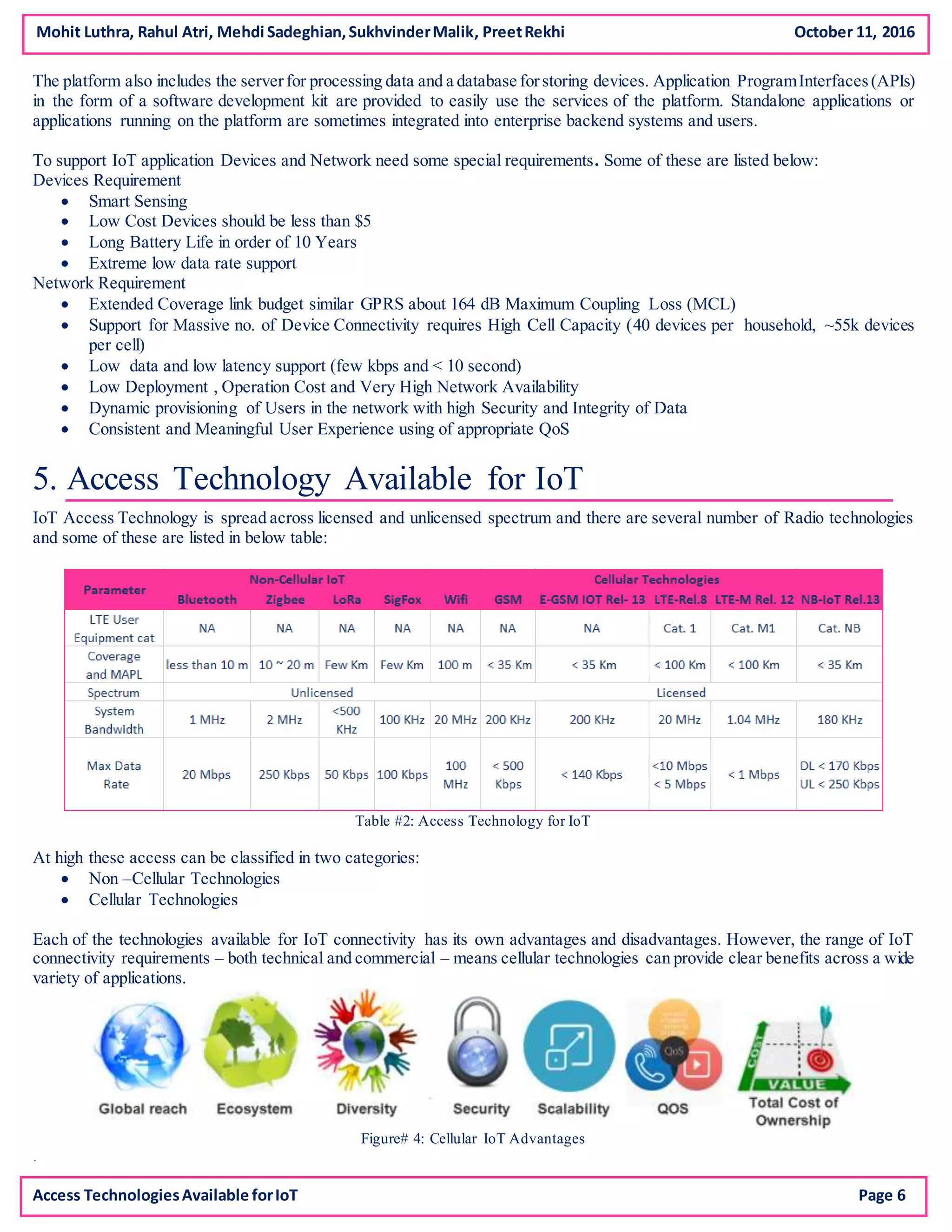
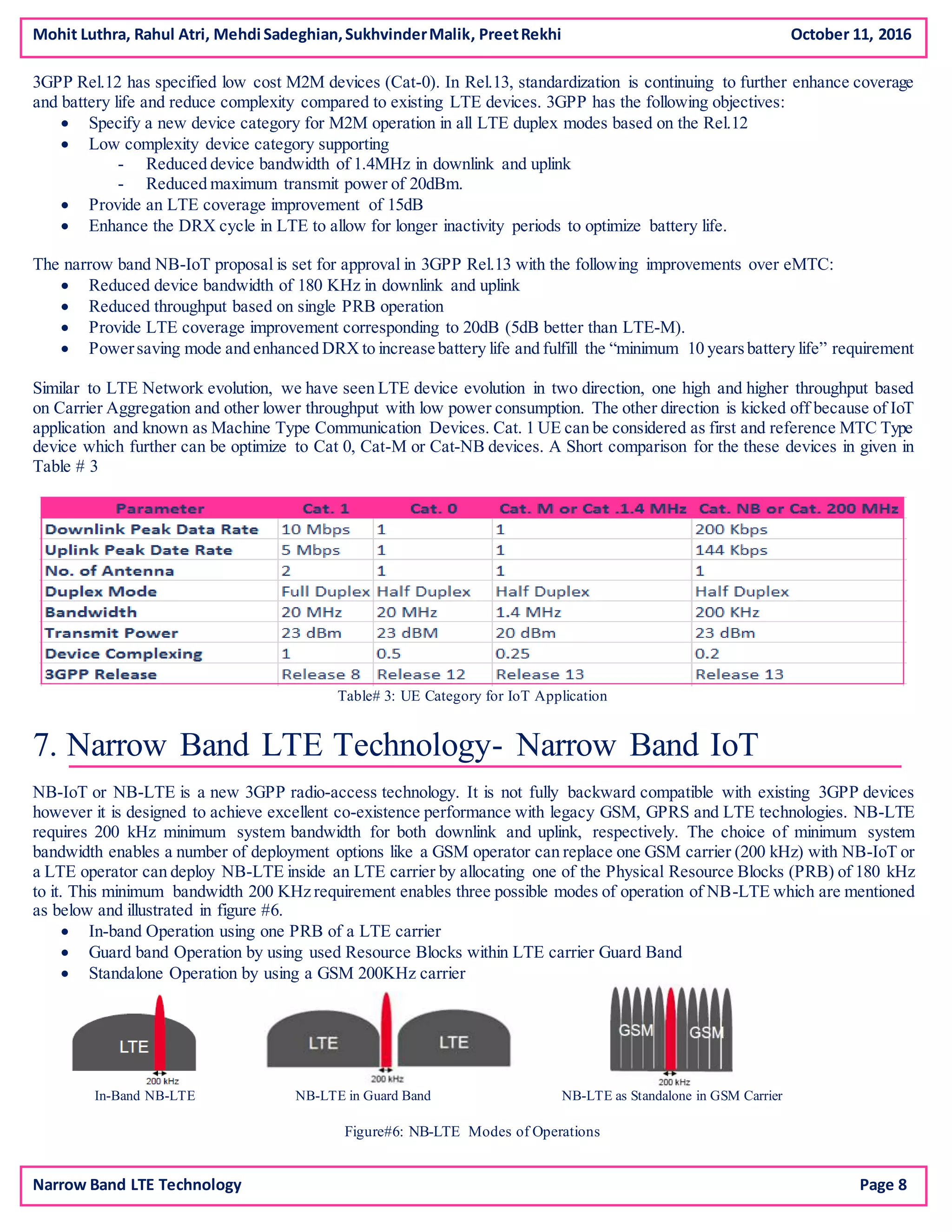
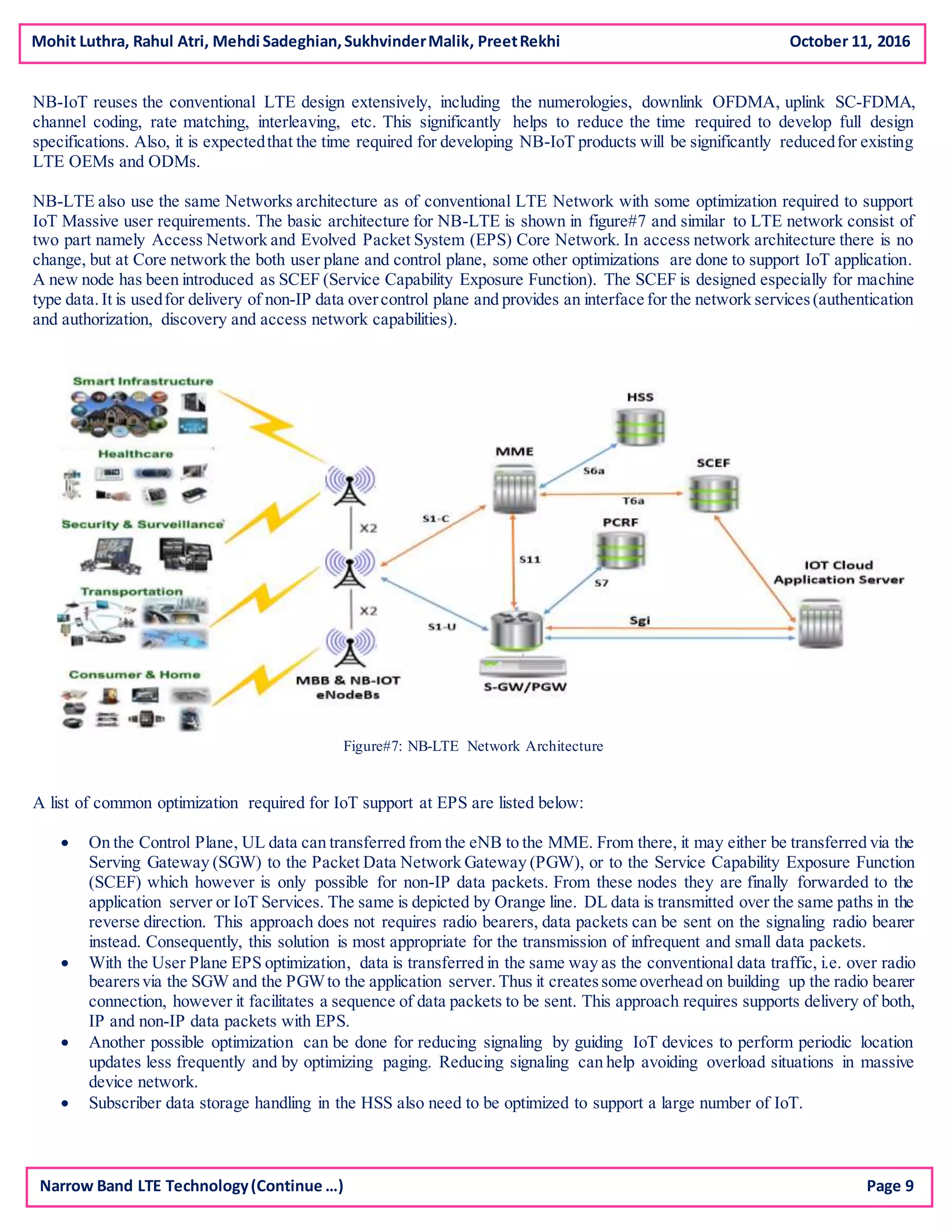
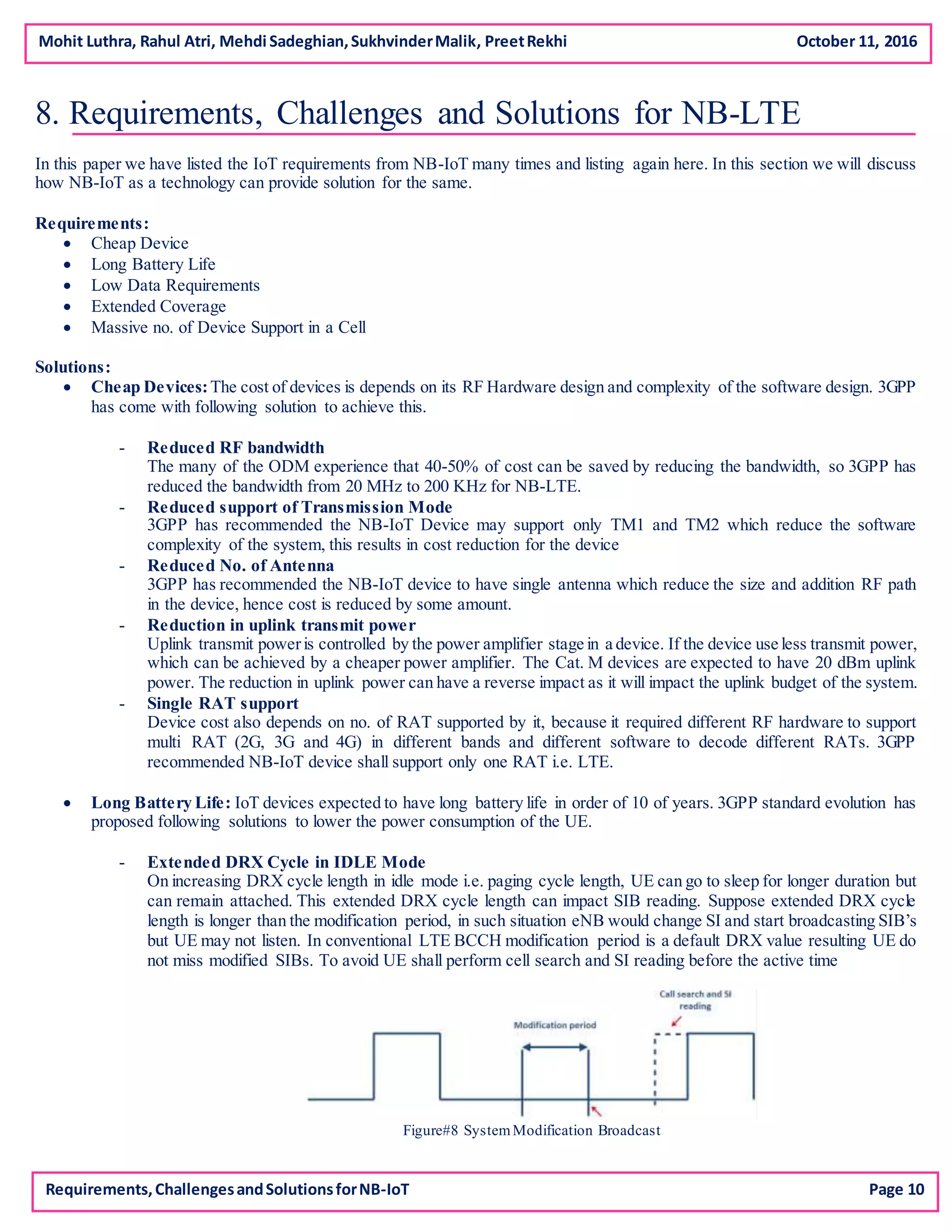
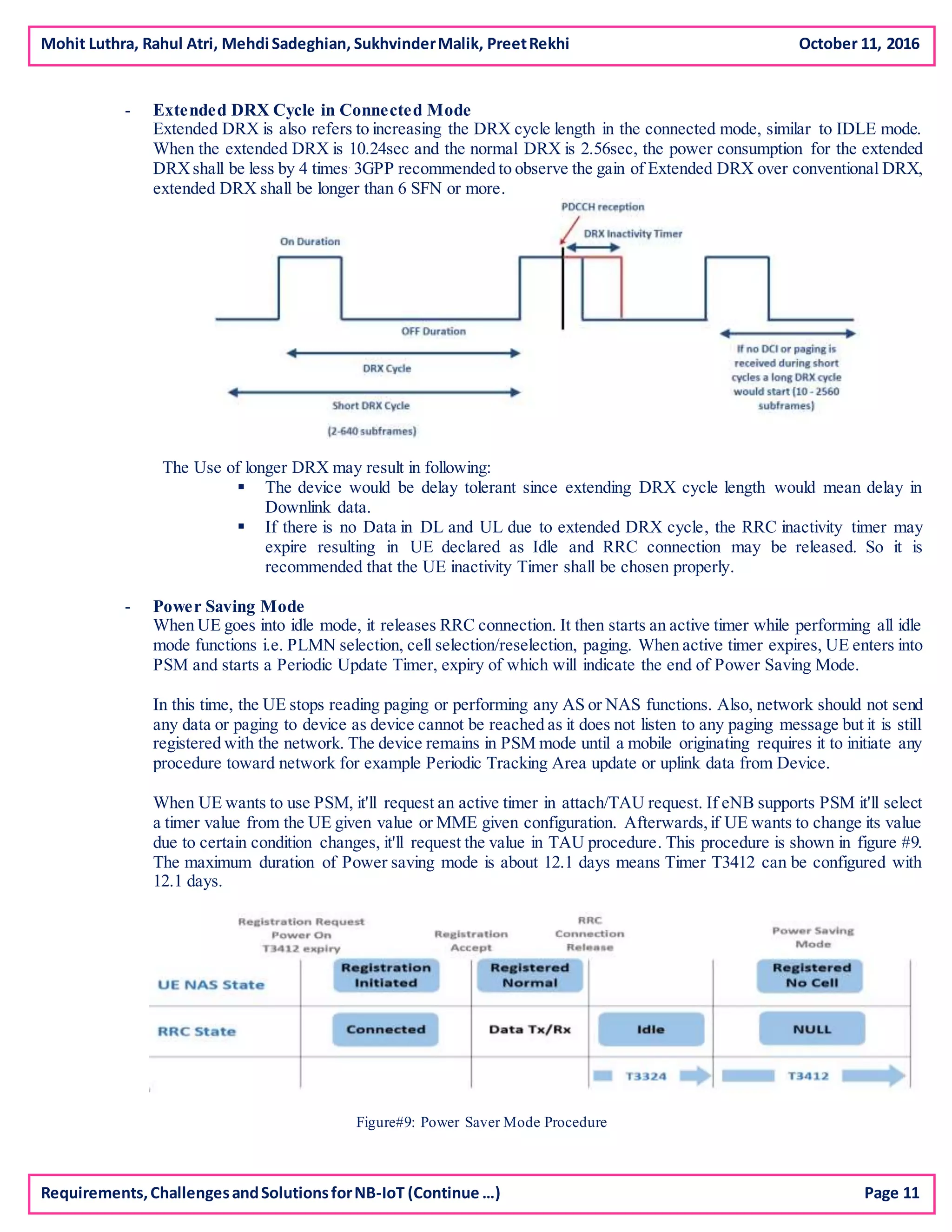
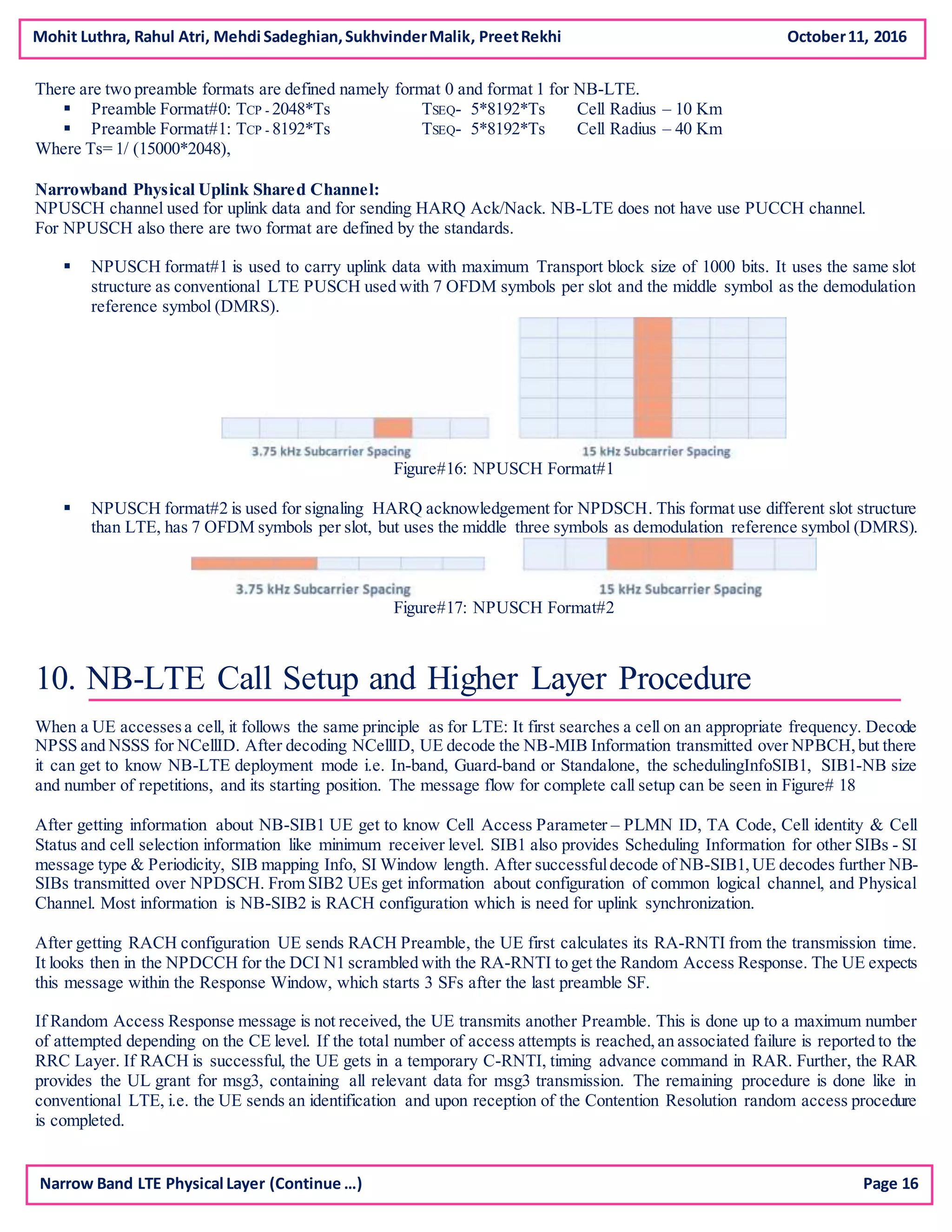
The document discusses the Internet of Things (IoT) and its potential for growth, predicting over 50 billion connected devices by 2020 and significant revenue opportunities for telecom operators. It highlights the evolution of IoT, its applications, network architecture, and the role of cellular technologies like Narrowband LTE in enabling efficient IoT communications. The analysis also emphasizes the importance of IP connectivity, new standards for IoT, and the challenges involved in managing a vast interconnected network securely and efficiently.