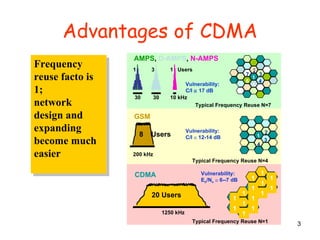
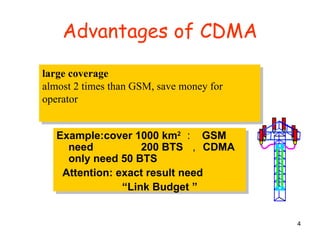
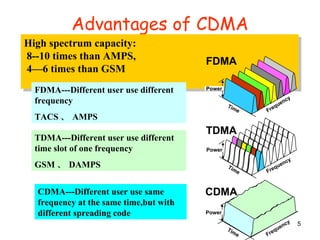
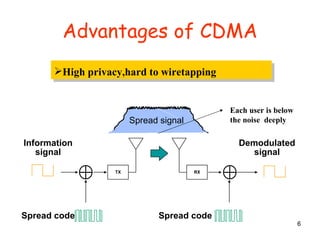
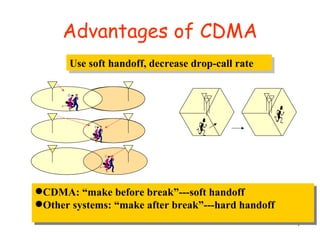
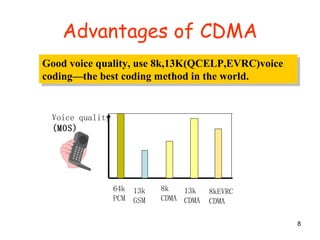
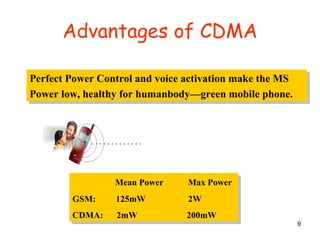
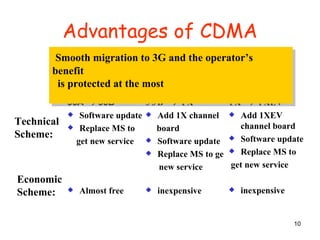
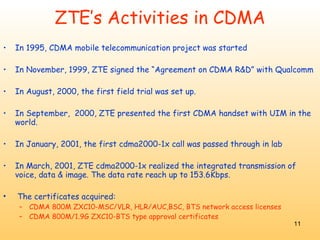
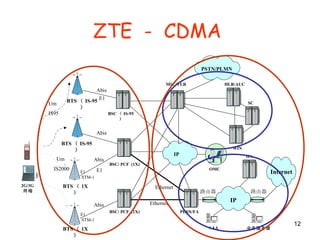
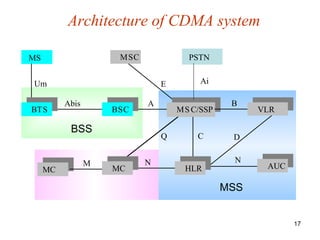
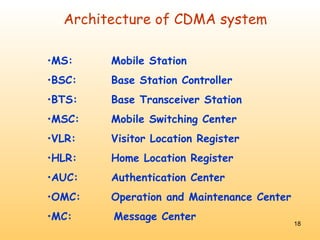
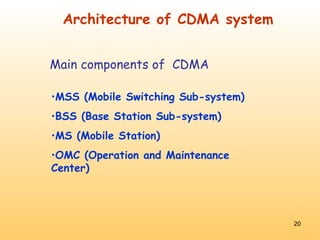
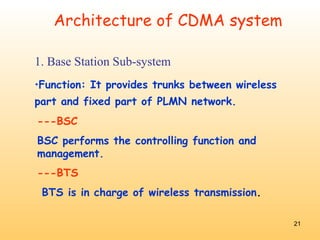
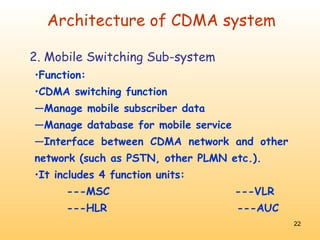
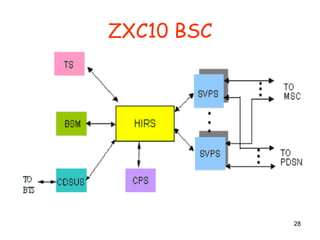
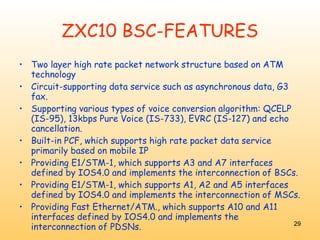
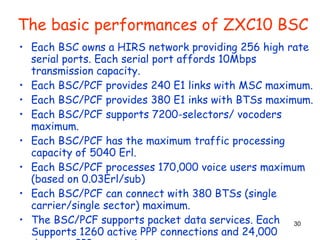
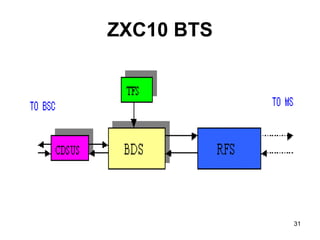
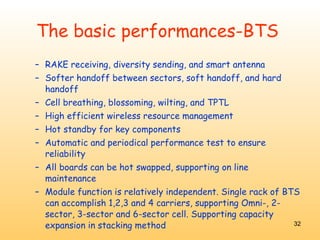
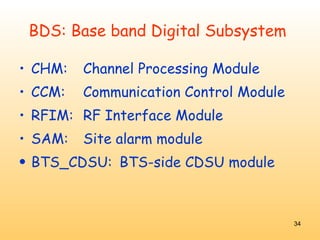
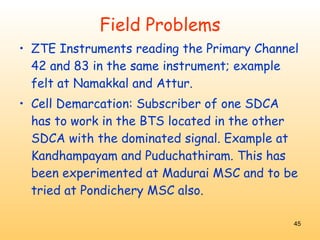
The document discusses several advantages of CDMA technology, including frequency reuse, large coverage area, high spectrum capacity, privacy, soft handoff, good voice quality, and smooth migration to 3G. It also provides details on ZTE's involvement with CDMA technology development and key components of a CDMA network such as the BSC, BTS, MSC, VLR, and HLR.