This document discusses dynamic routing protocols and contains sections on dynamic routing protocols, RIPv2 configuration, routing tables, and a summary. Some key points include:
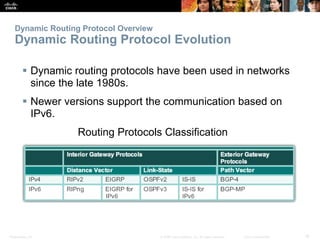
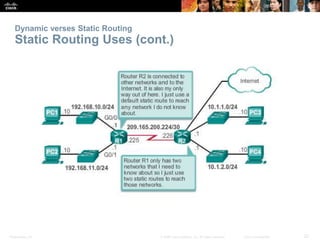
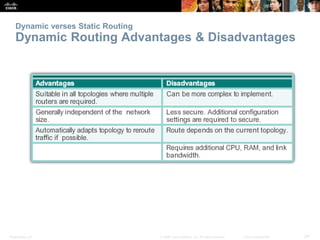
- Dynamic routing protocols allow routers to automatically learn about remote networks and maintain up-to-date routing information to choose the best path.
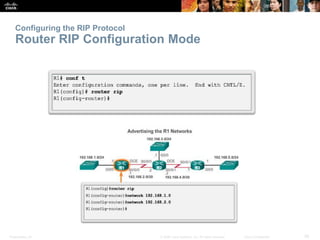
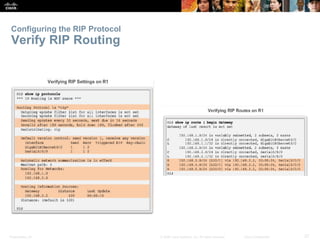
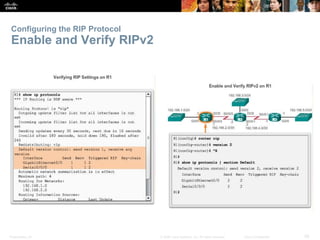
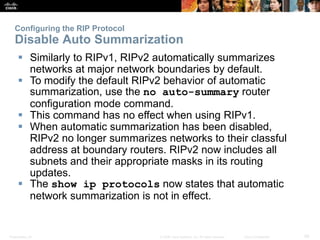
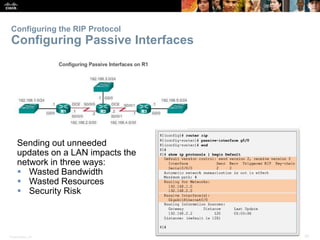
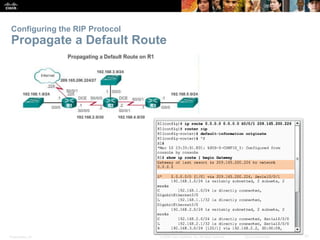
- RIPv2 is configured on routers to exchange routing information with neighboring routers using various routing protocol messages and algorithms.
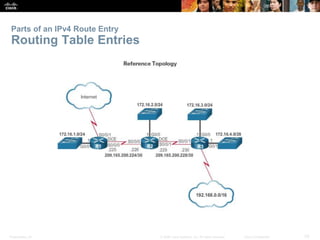
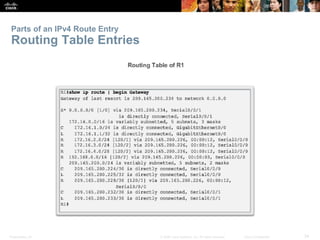
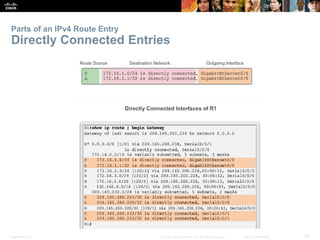
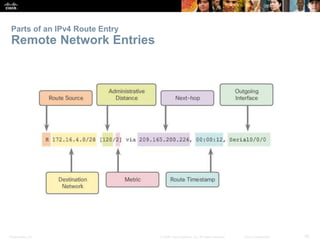
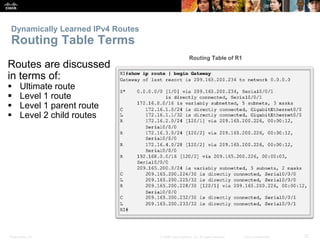
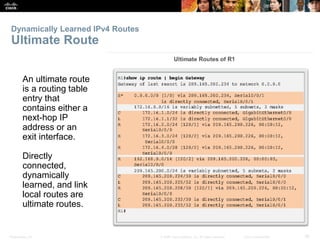
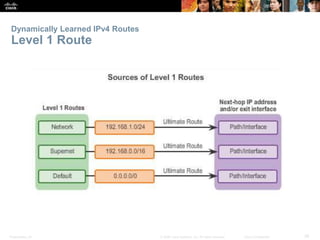
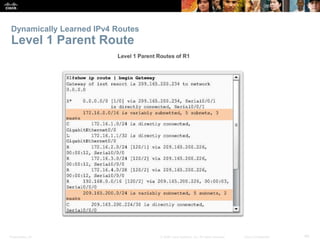
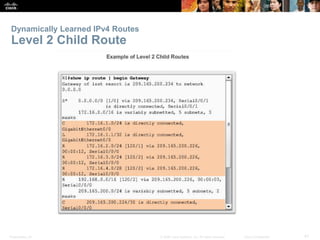
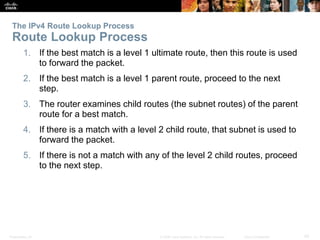
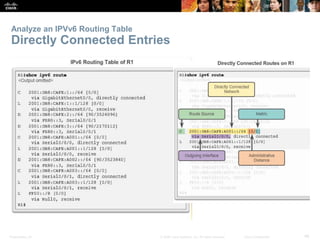
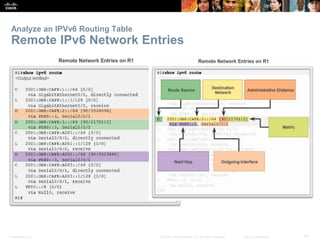
- Routing tables contain entries for directly connected networks, remote networks learned dynamically, and default routes. IPv4 tables can include ultimate, level 1, and level 2 routes while IPv6 tables contain only ultimate routes.
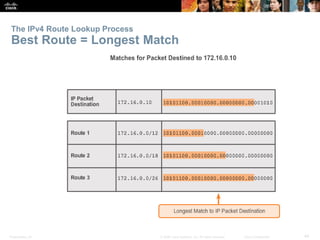
- The routing lookup process uses administrative distances and longest prefix matching to determine the best route