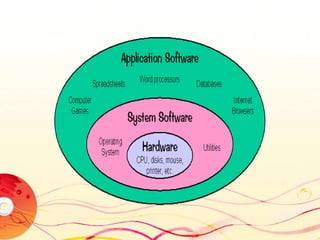
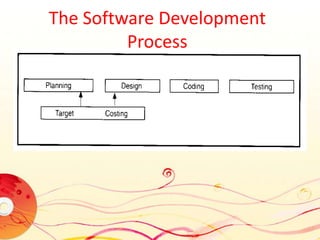
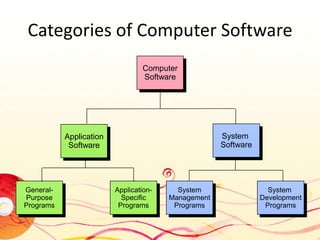
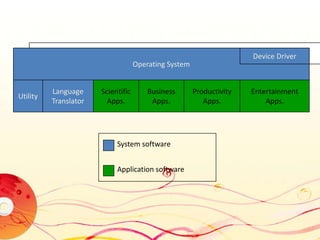
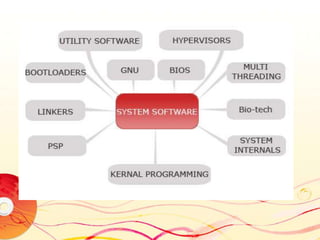
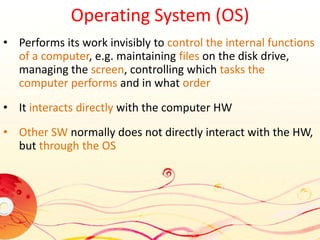
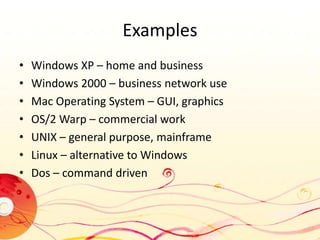
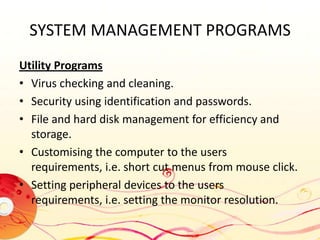
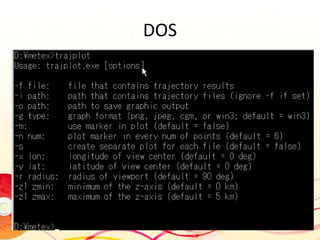
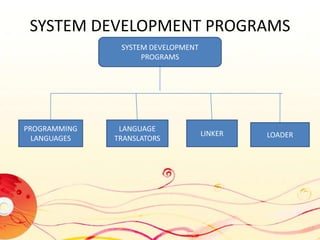
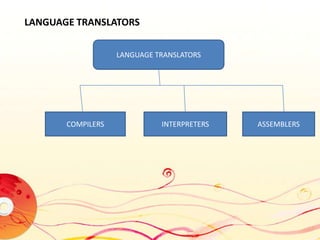
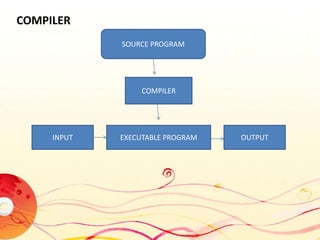
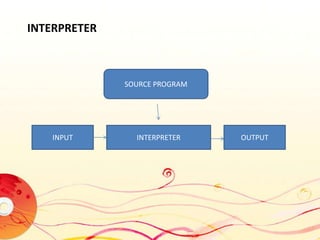
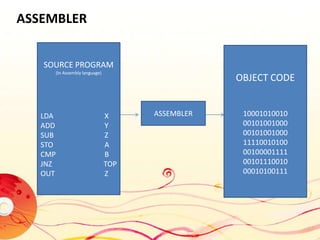
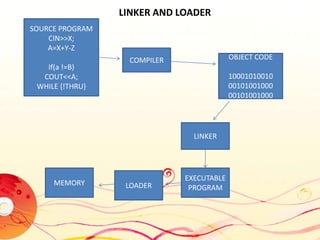
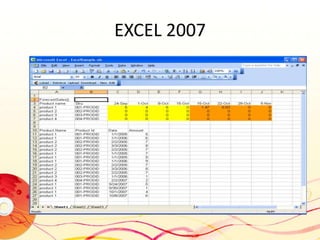
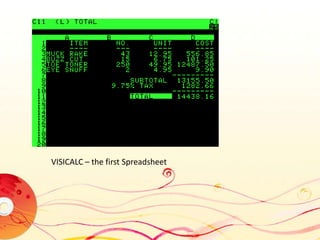
The document discusses learning goals related to software. It aims to discuss the role of software in computing systems, differentiate between system and application software, and discuss software ownership. It provides definitions of software and outlines the software development process. It categorizes computer software and provides details about system software, including operating systems, utilities, system development programs, and examples. It also discusses application software and provides examples like word processors, spreadsheets, databases, multimedia software, and more.