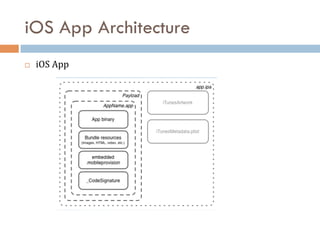
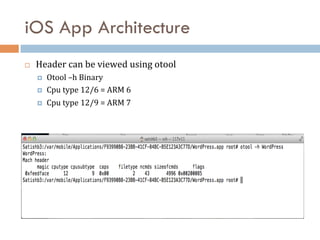
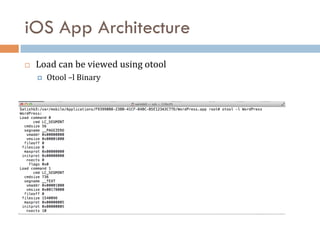
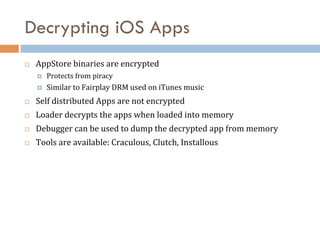
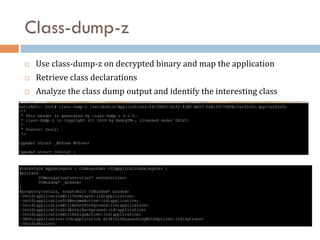
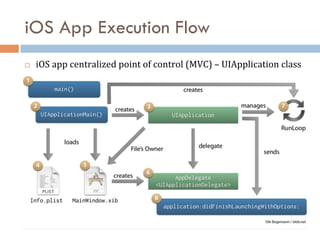
This document discusses breaking iOS apps using Cycript. It begins with an overview of Objective-C basics and iOS app architecture. It then covers decrypting iOS apps and how Cycript can be used to modify apps at runtime by accessing classes and variables. Class-dump-z is used to retrieve class declarations from decrypted binaries. Cycript allows directly accessing instance variables and methods to break app security.

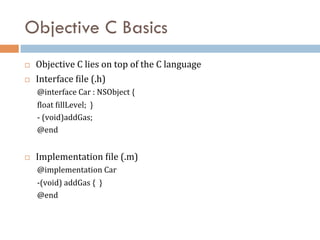
![Objective C Basics
¨ Methods
–
pass
messages
¨ C++
¤ Object-‐>Method(param1,param2)
¨ Objective-‐C
¤ [Object
method:param1
param2name:param2]](https://image.slidesharecdn.com/breakingiosappsusingcycript-130628034738-phpapp01/85/Breaking-iOS-Apps-using-Cycript-5-320.jpg)