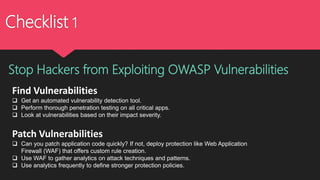
The document discusses the OWASP Top 10 vulnerabilities from the 2017 edition, emphasizing the importance of understanding and preparing for these risks in cybersecurity. It outlines various vulnerabilities such as injection attacks, broken authentication, XSS, and more, providing insights on how attackers exploit these weaknesses. The text also includes recommendations for detecting vulnerabilities, patching, and employing security measures like web application firewalls (WAF) to protect against threats.