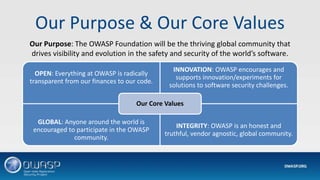
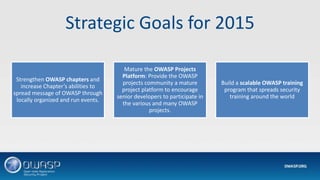
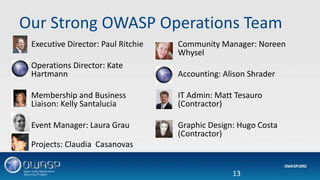
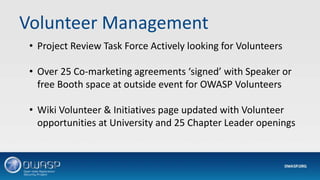
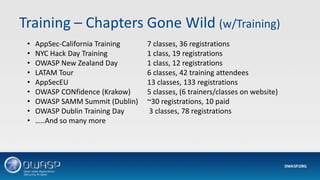
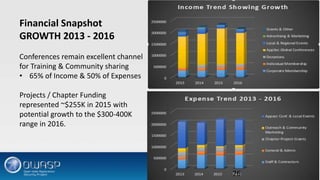
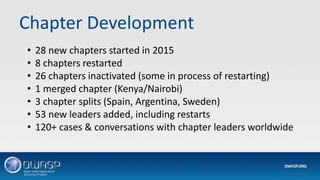
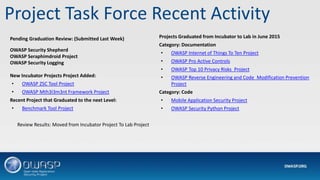
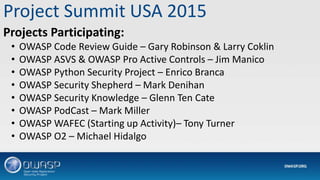
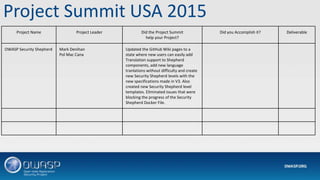
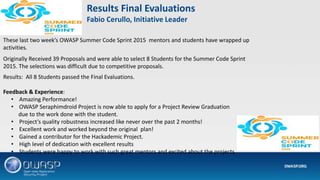
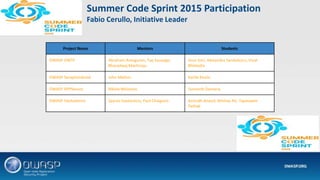
This document provides a summary of the State of OWASP in 2015. It discusses the Open Web Application Security Project (OWASP) organization, including its purpose to drive visibility and evolution of software security. Key updates are provided on OWASP's strategic goals, operations team, chapters and conferences around the world, projects, finances, and community engagement. The community manager discusses developments with chapters and communications. The project coordinator reviews the project task force, summits, and OWASP's successful summer code sprint program.