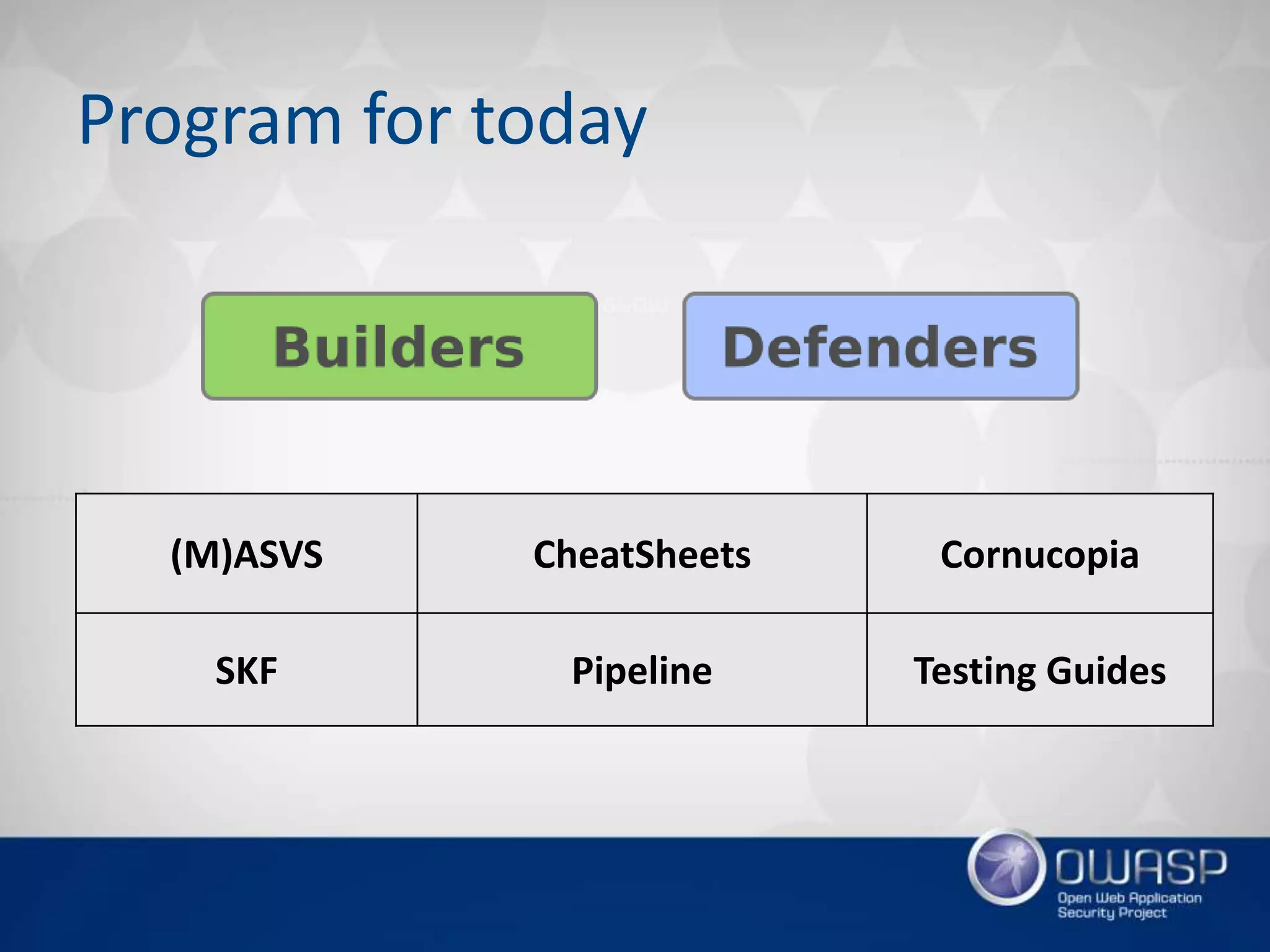
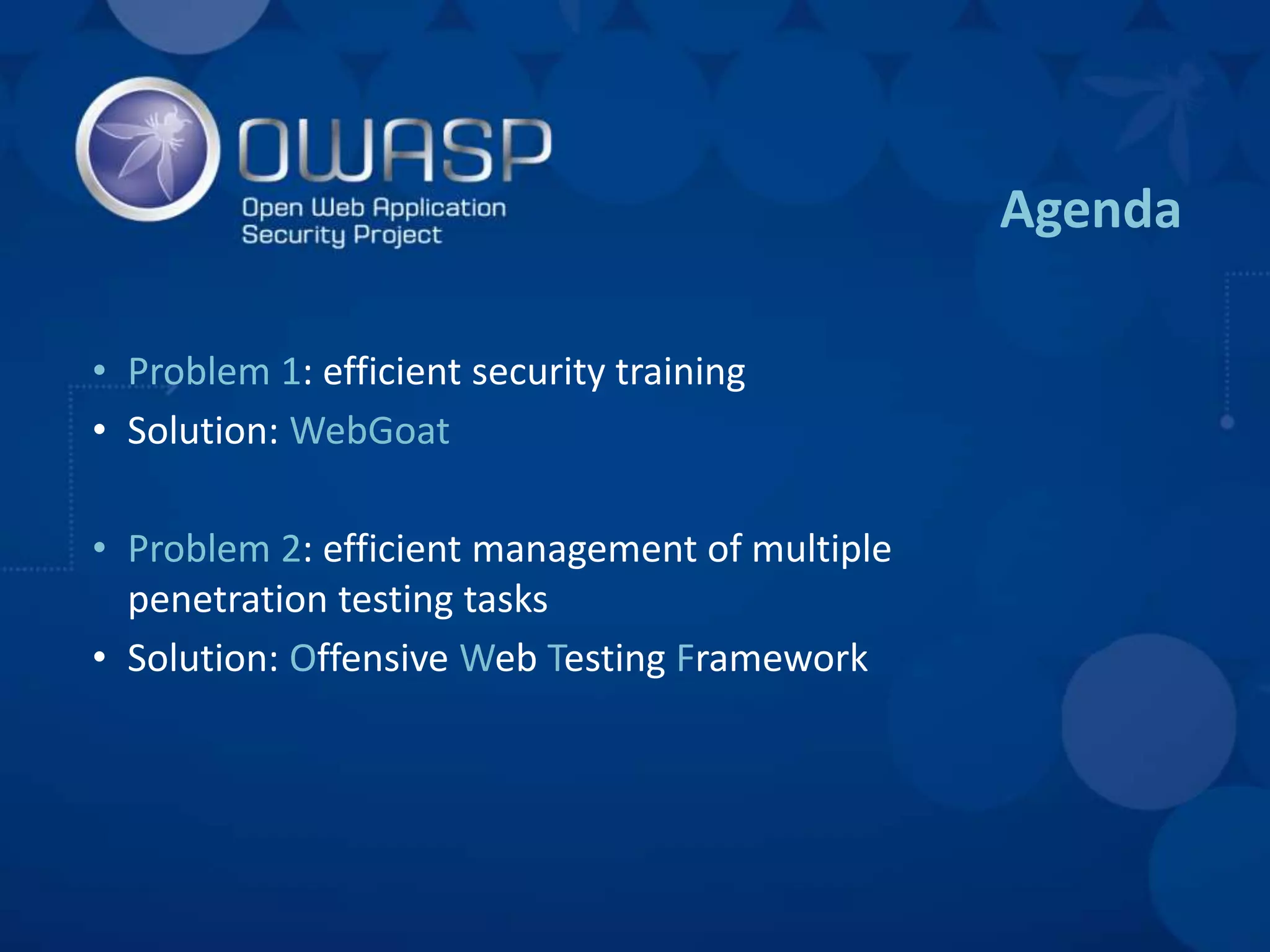
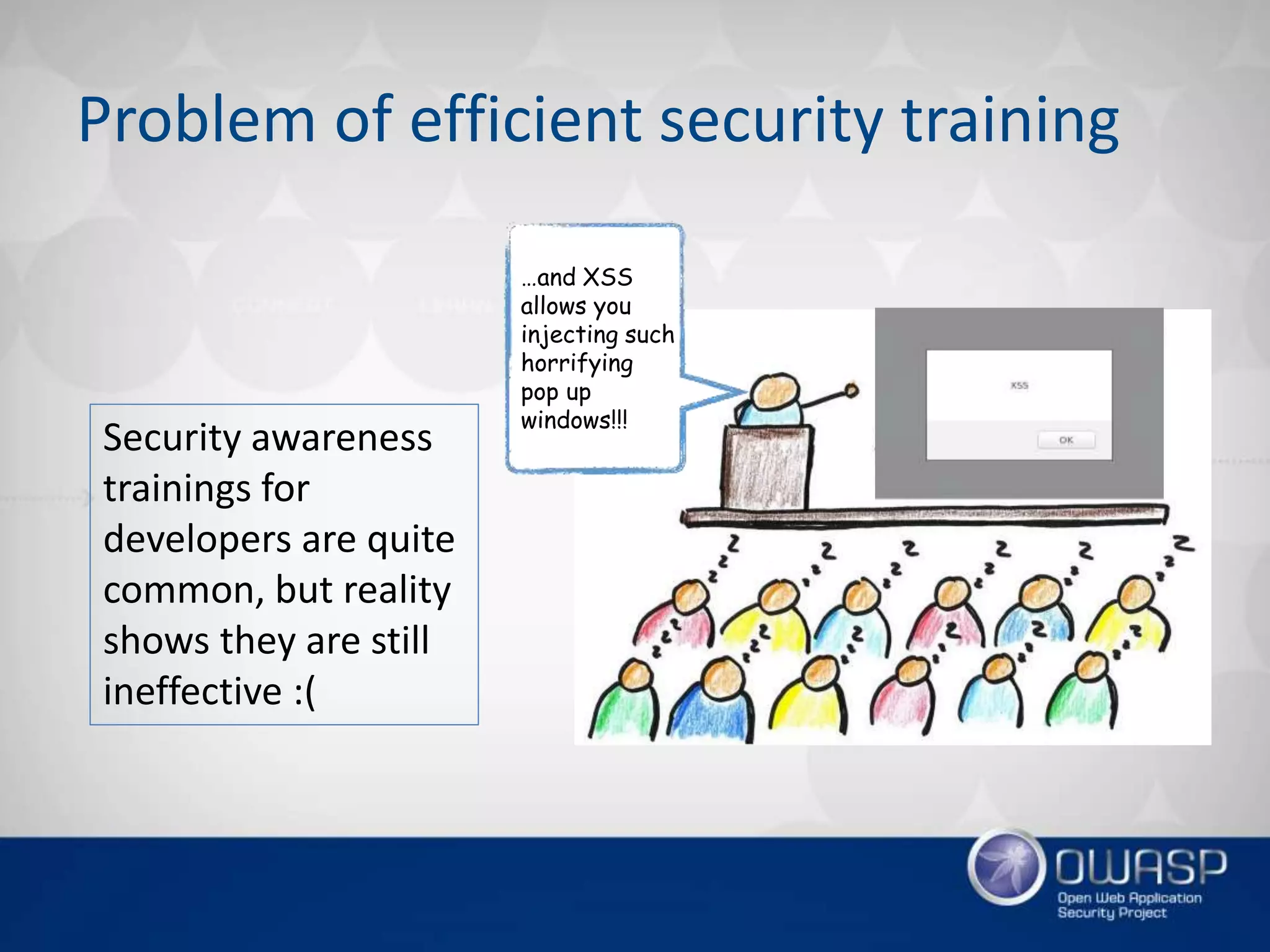
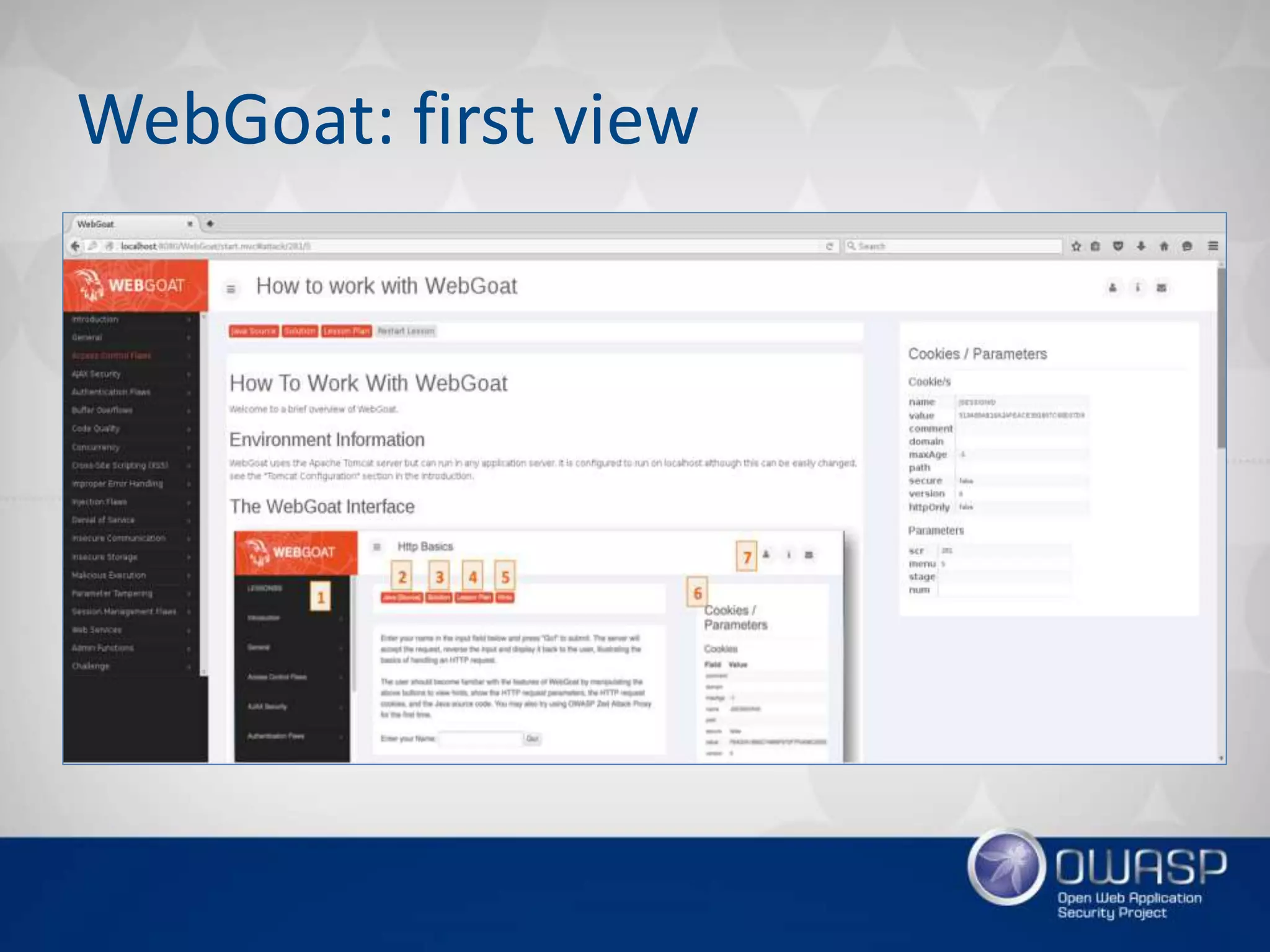
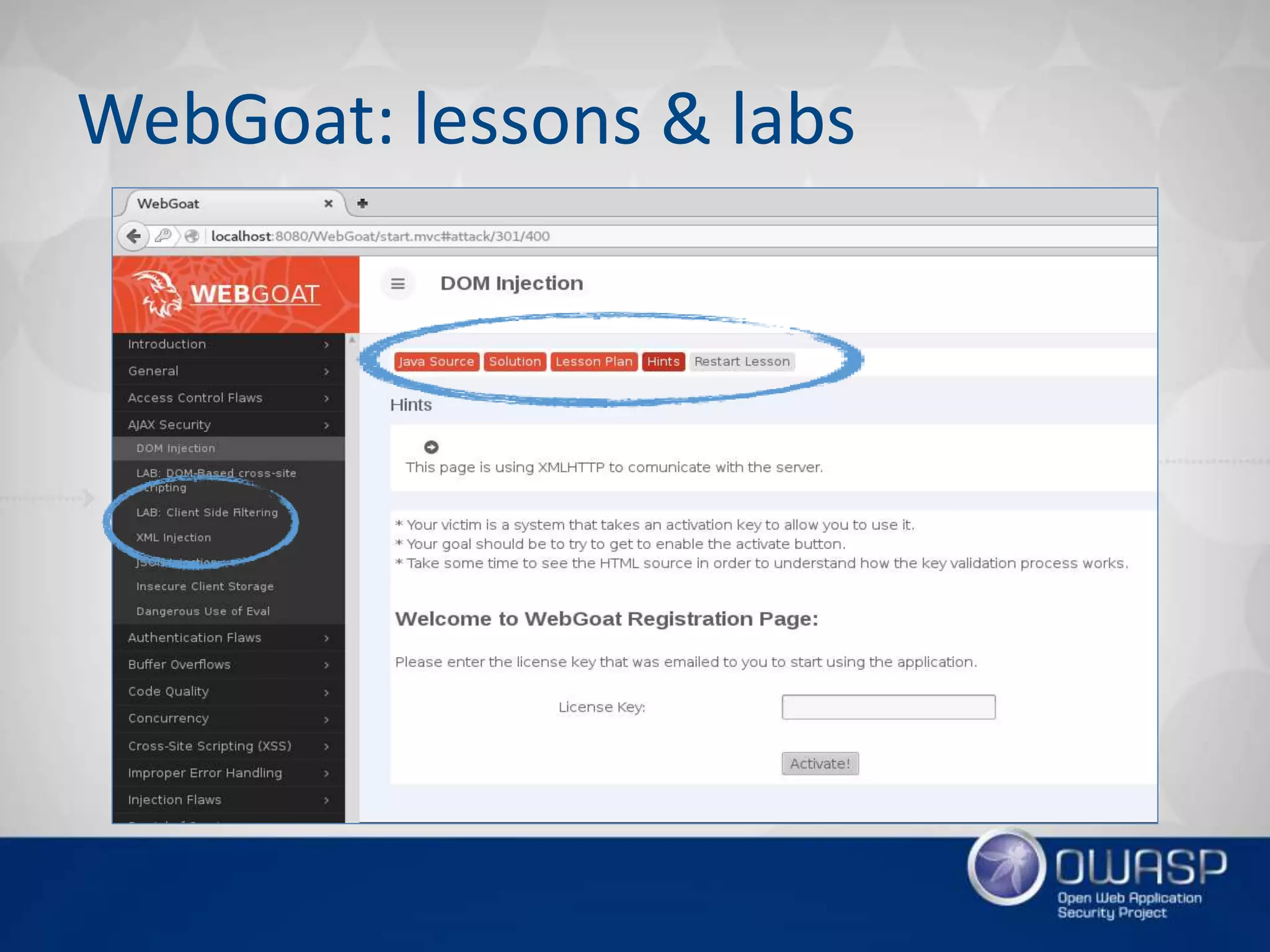
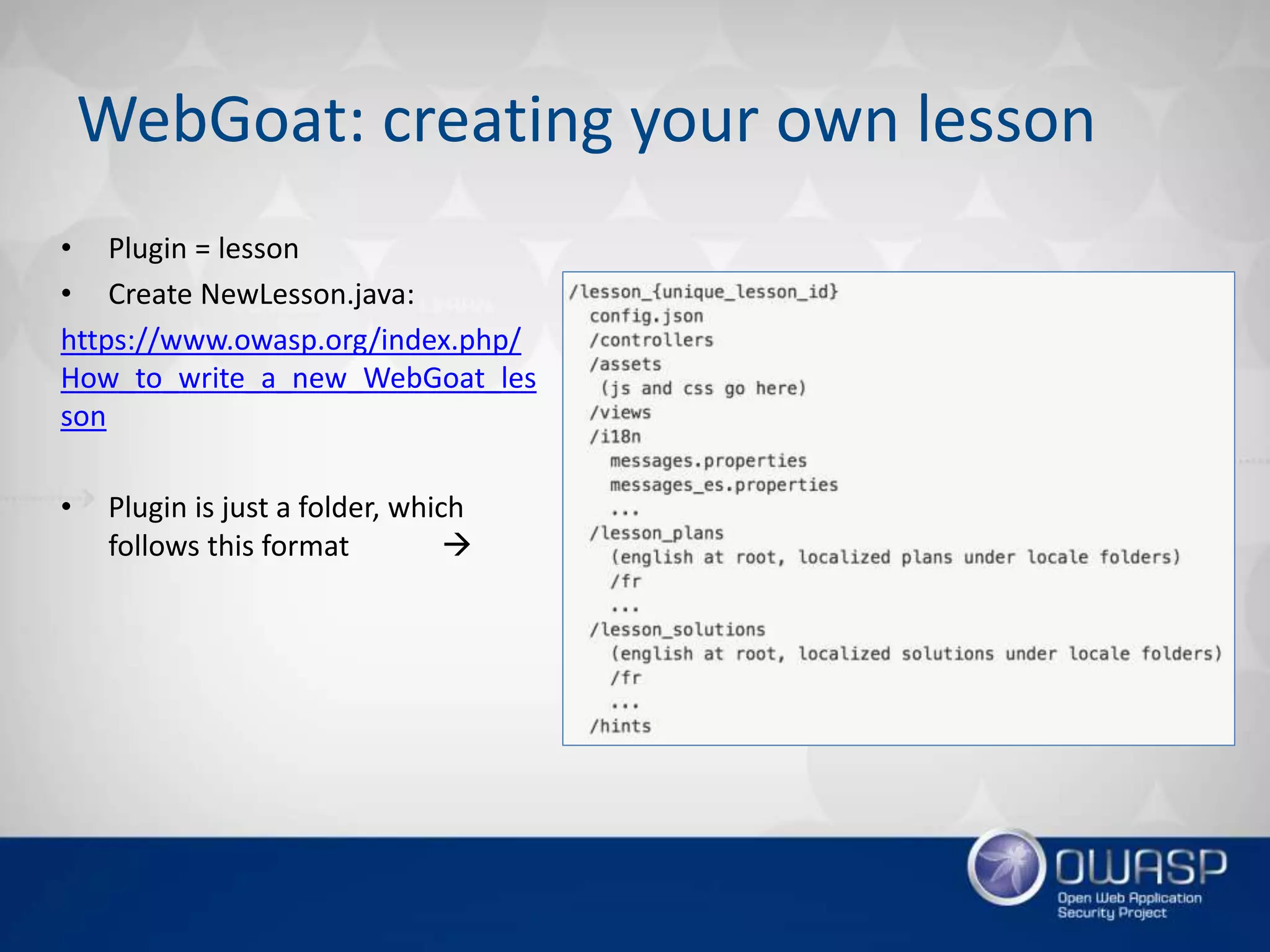
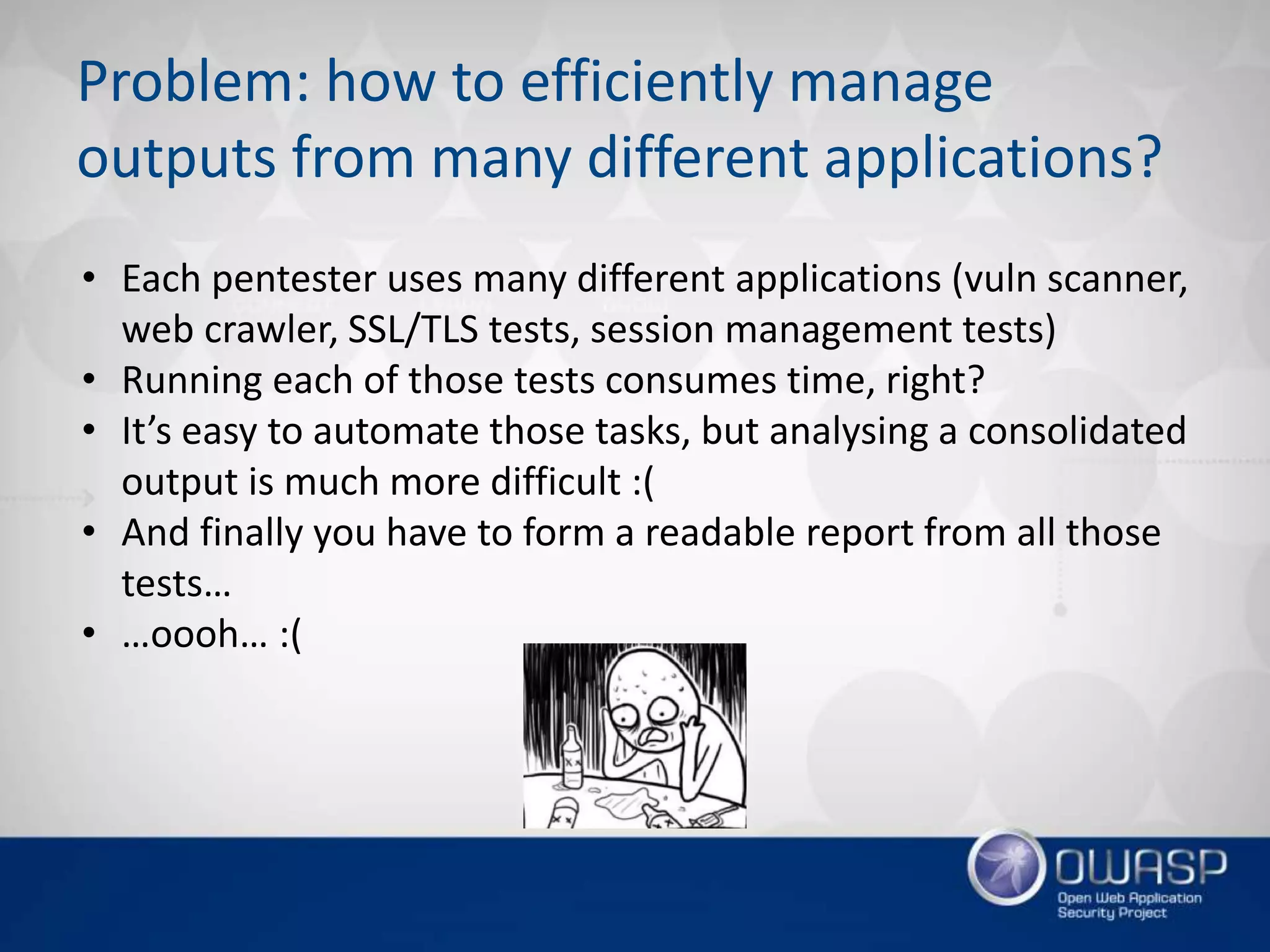
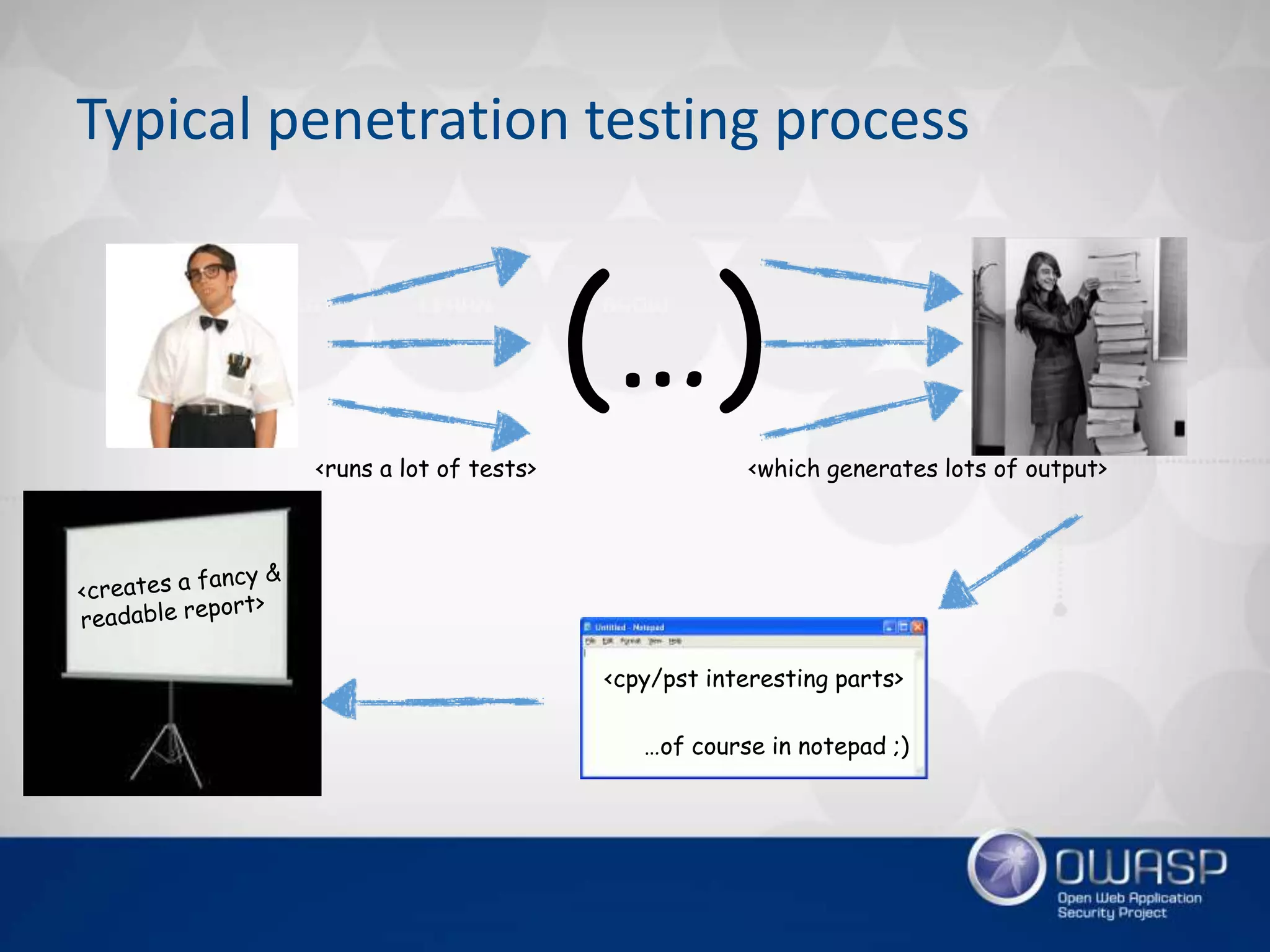
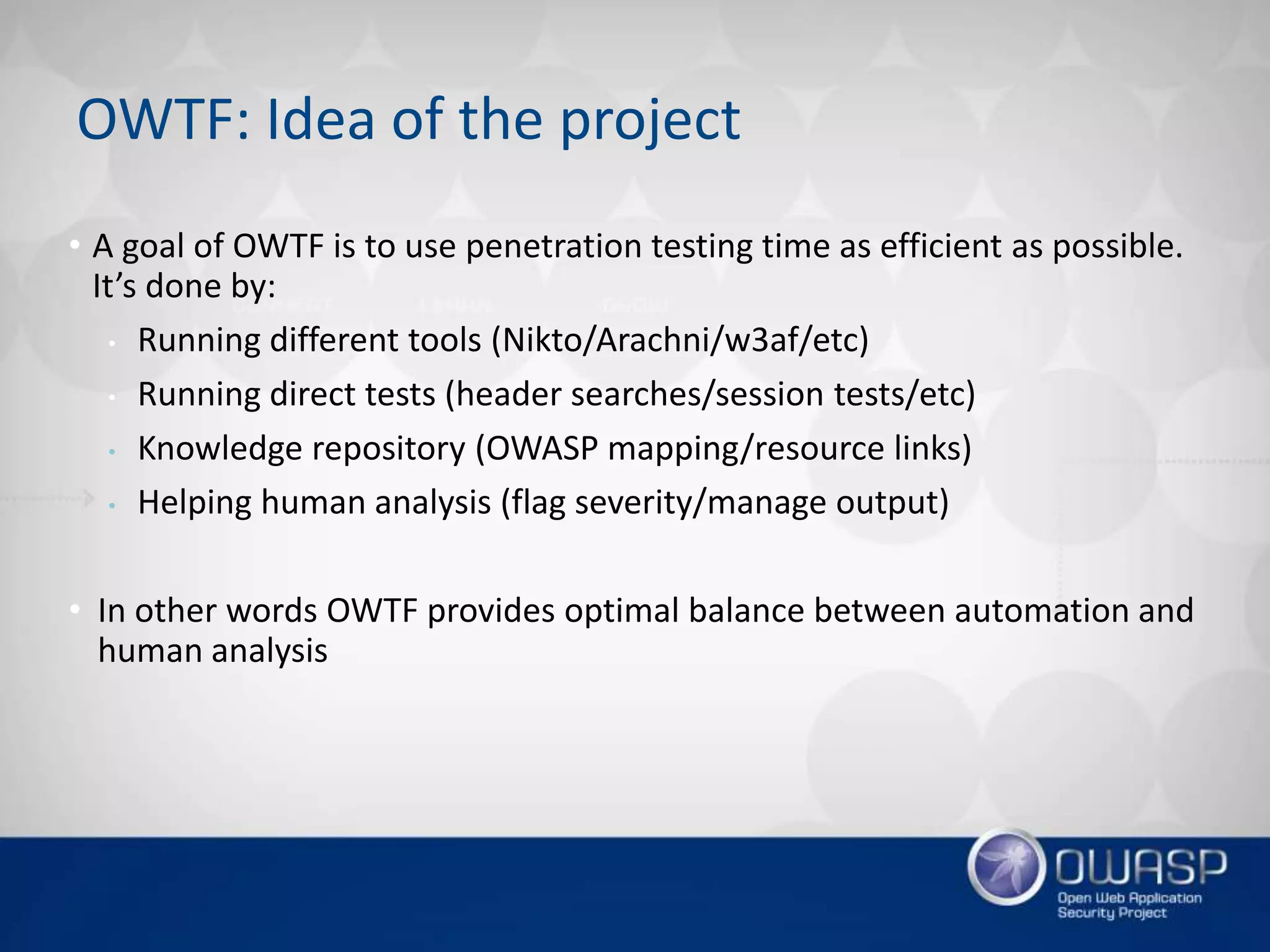
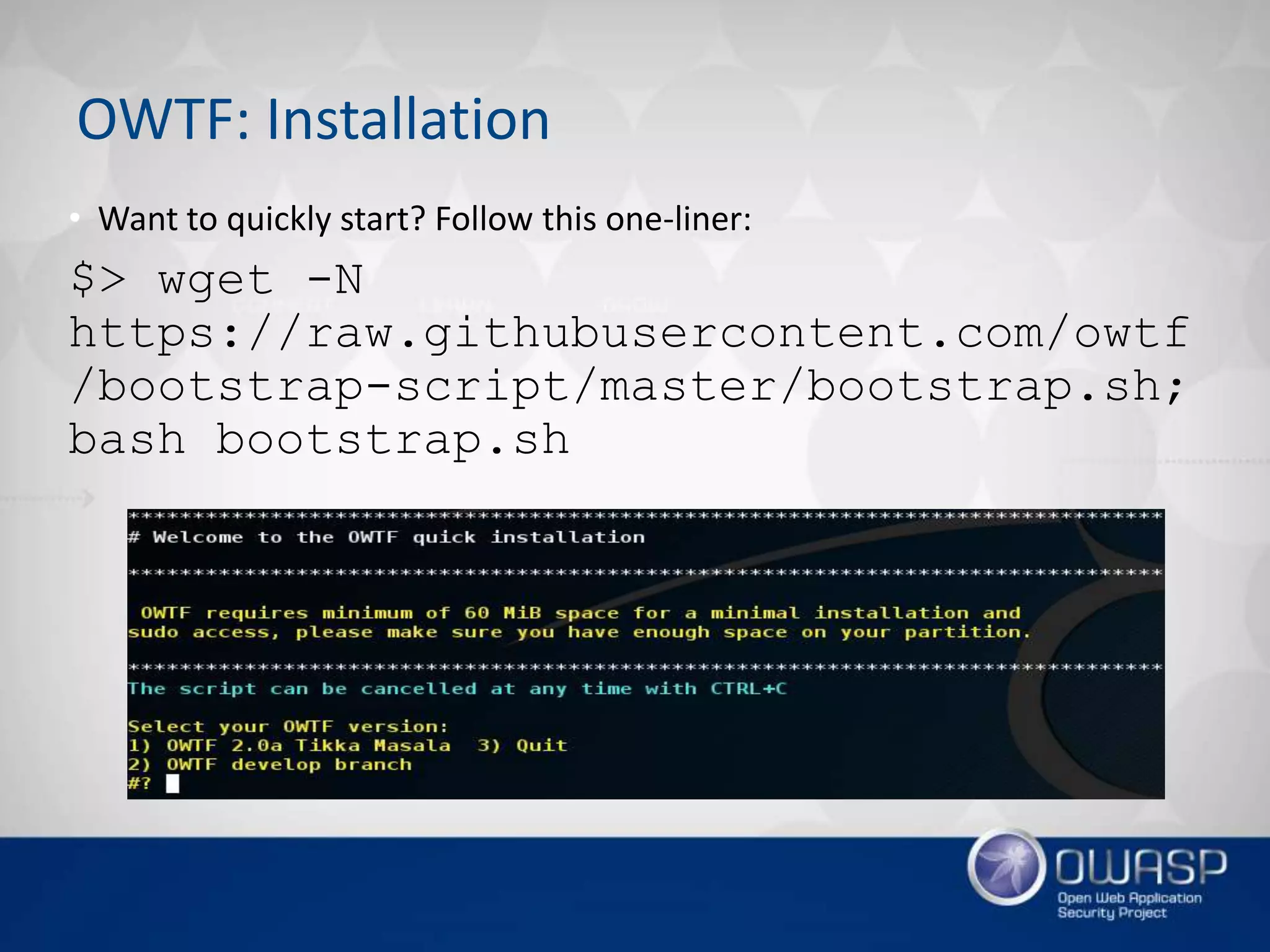
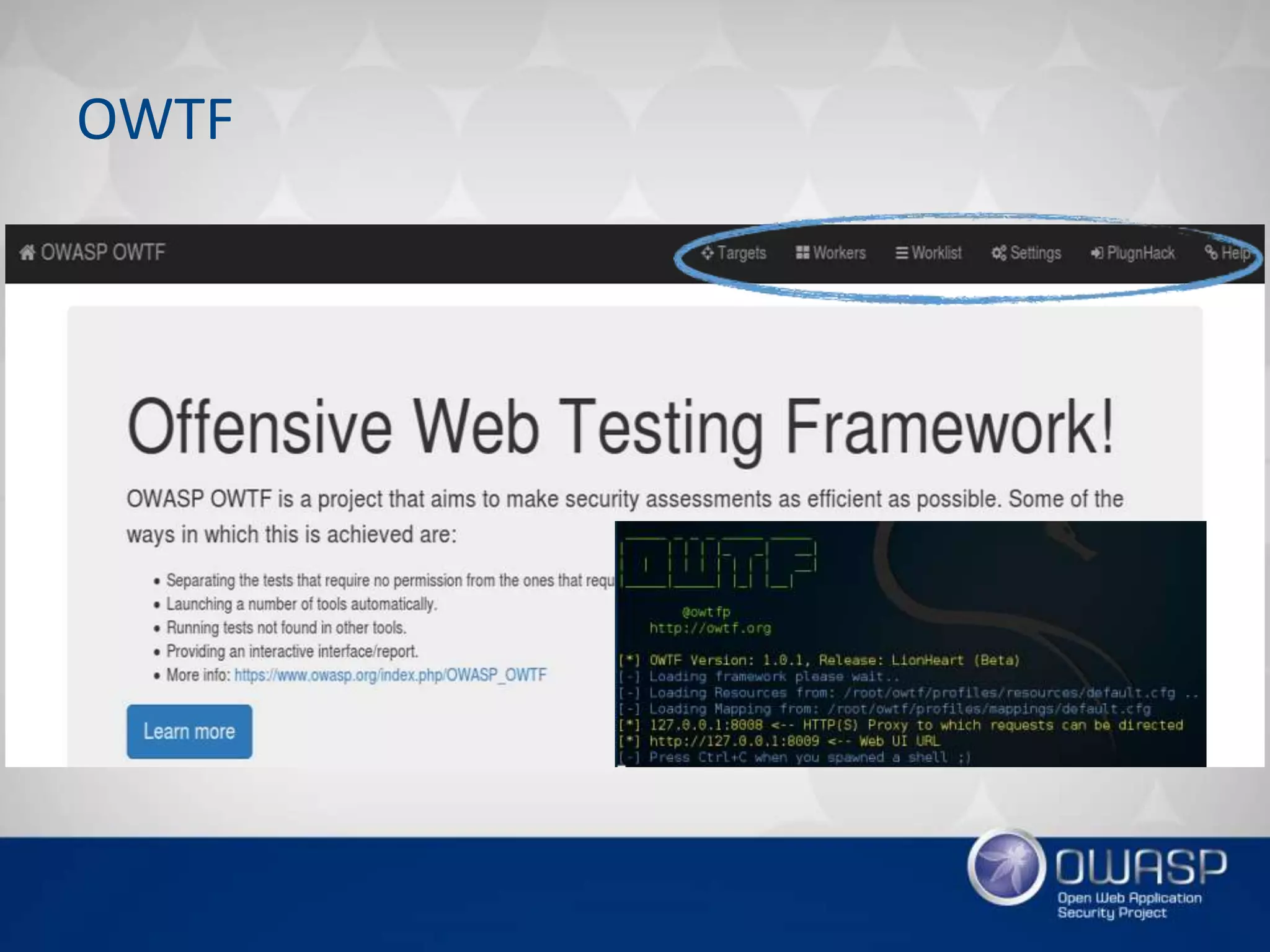
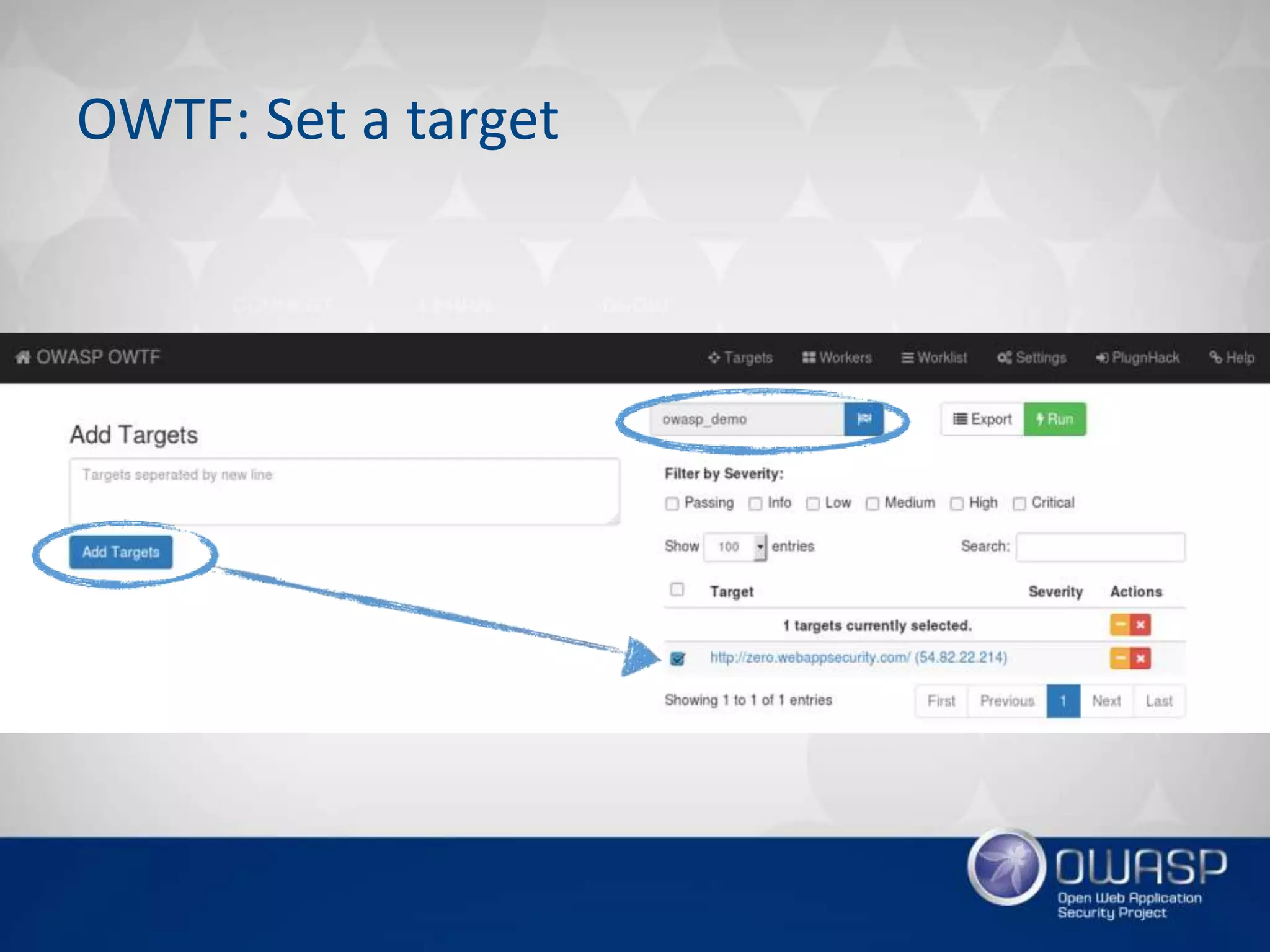
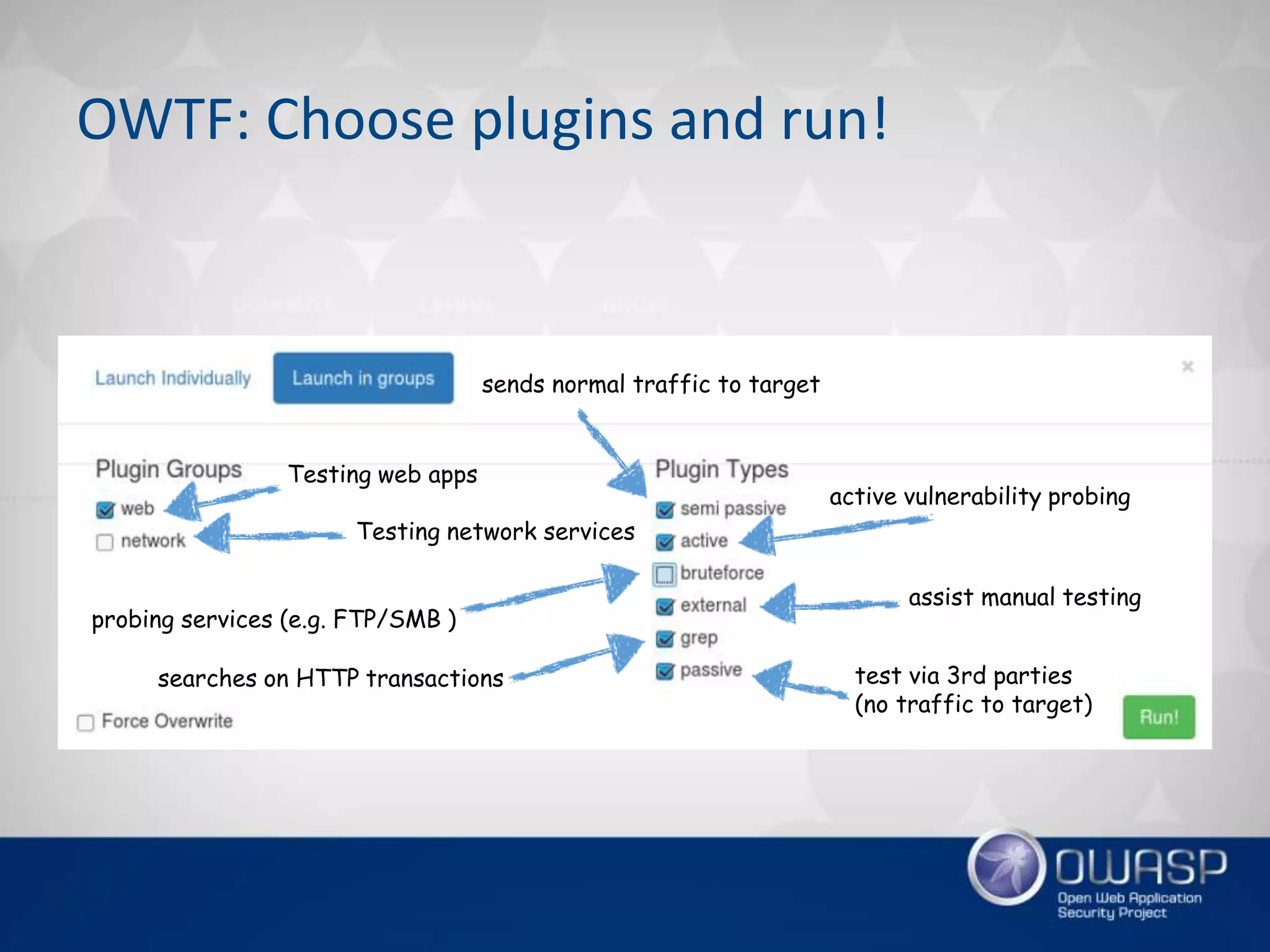
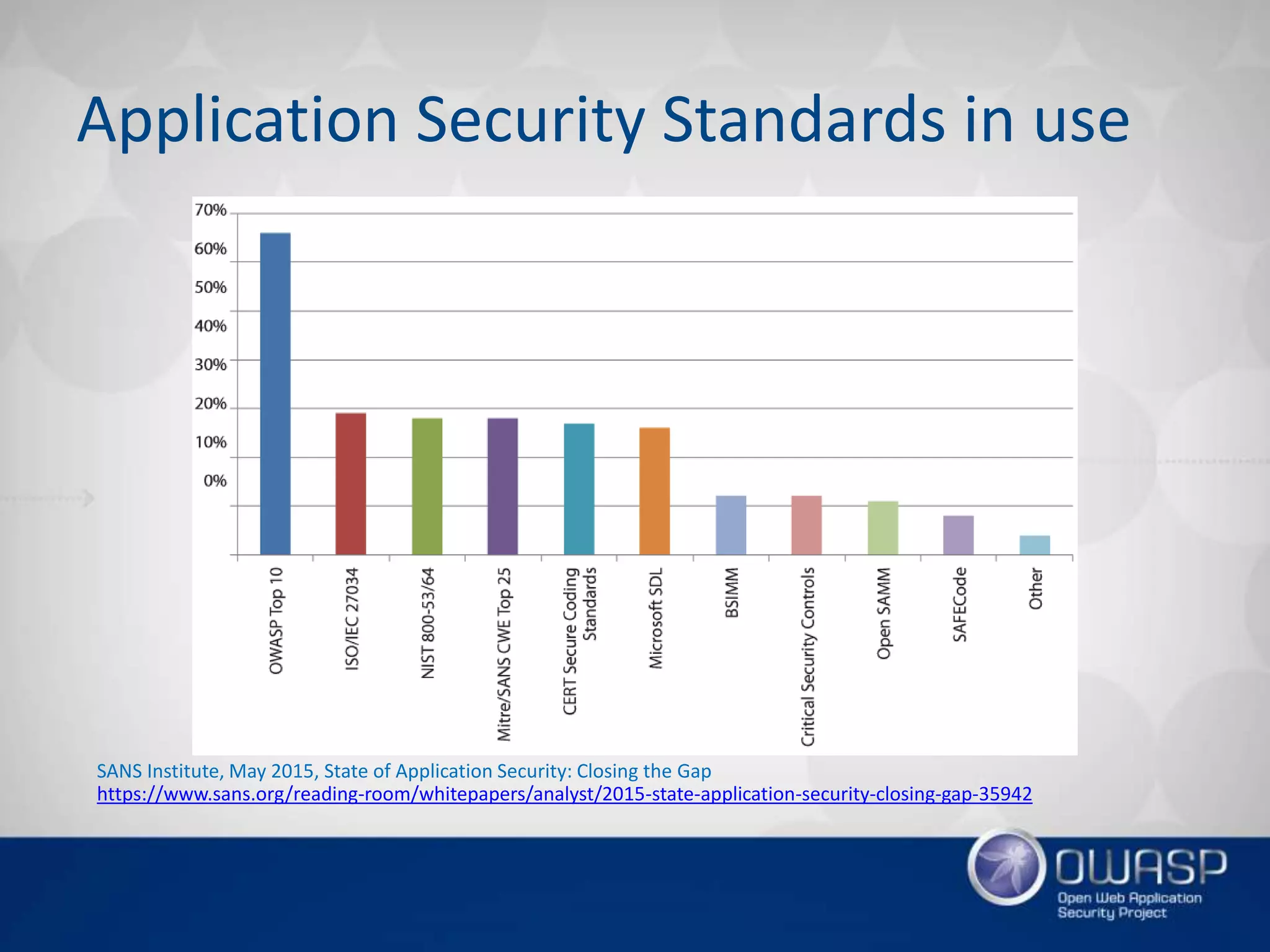
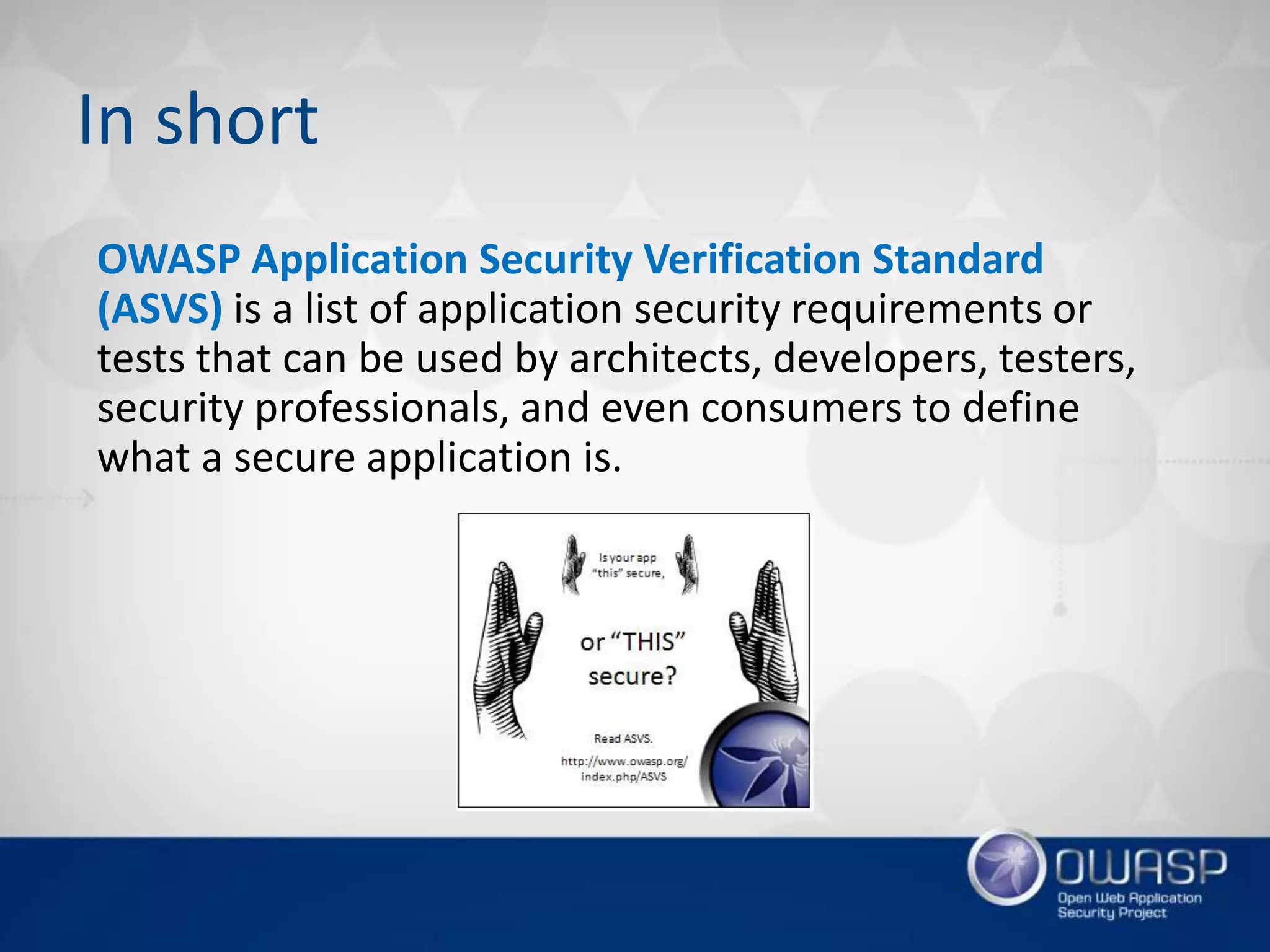
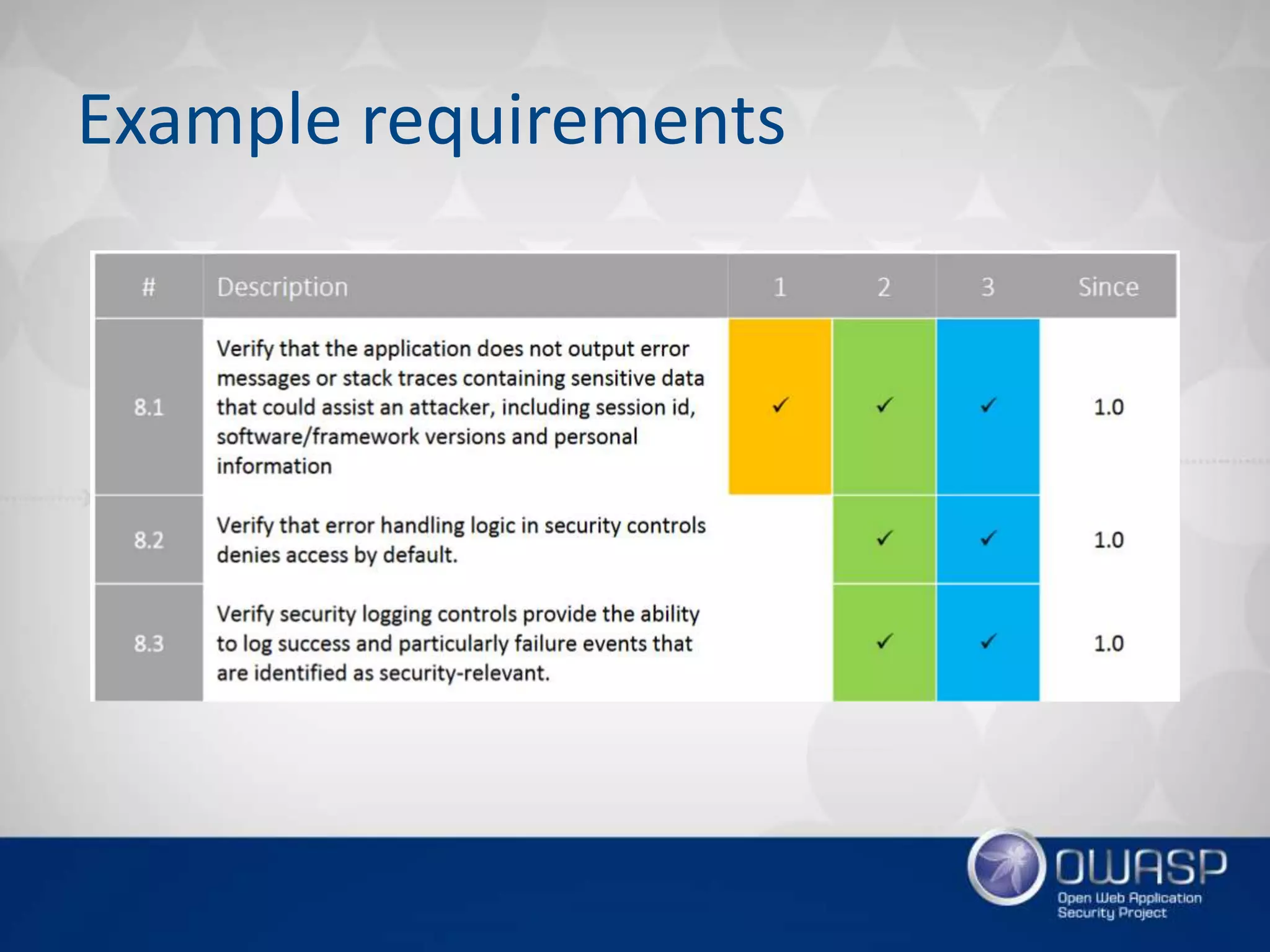
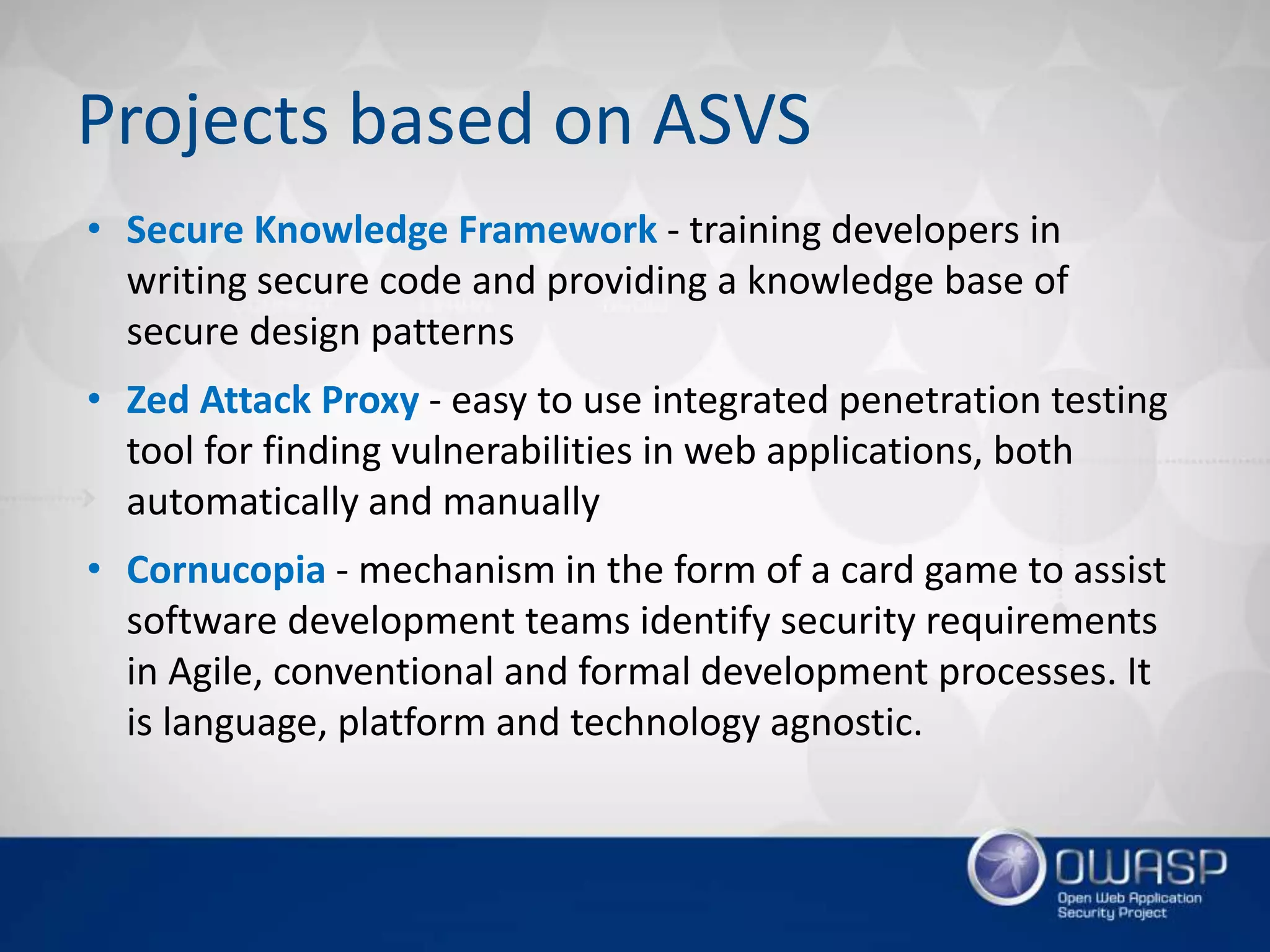
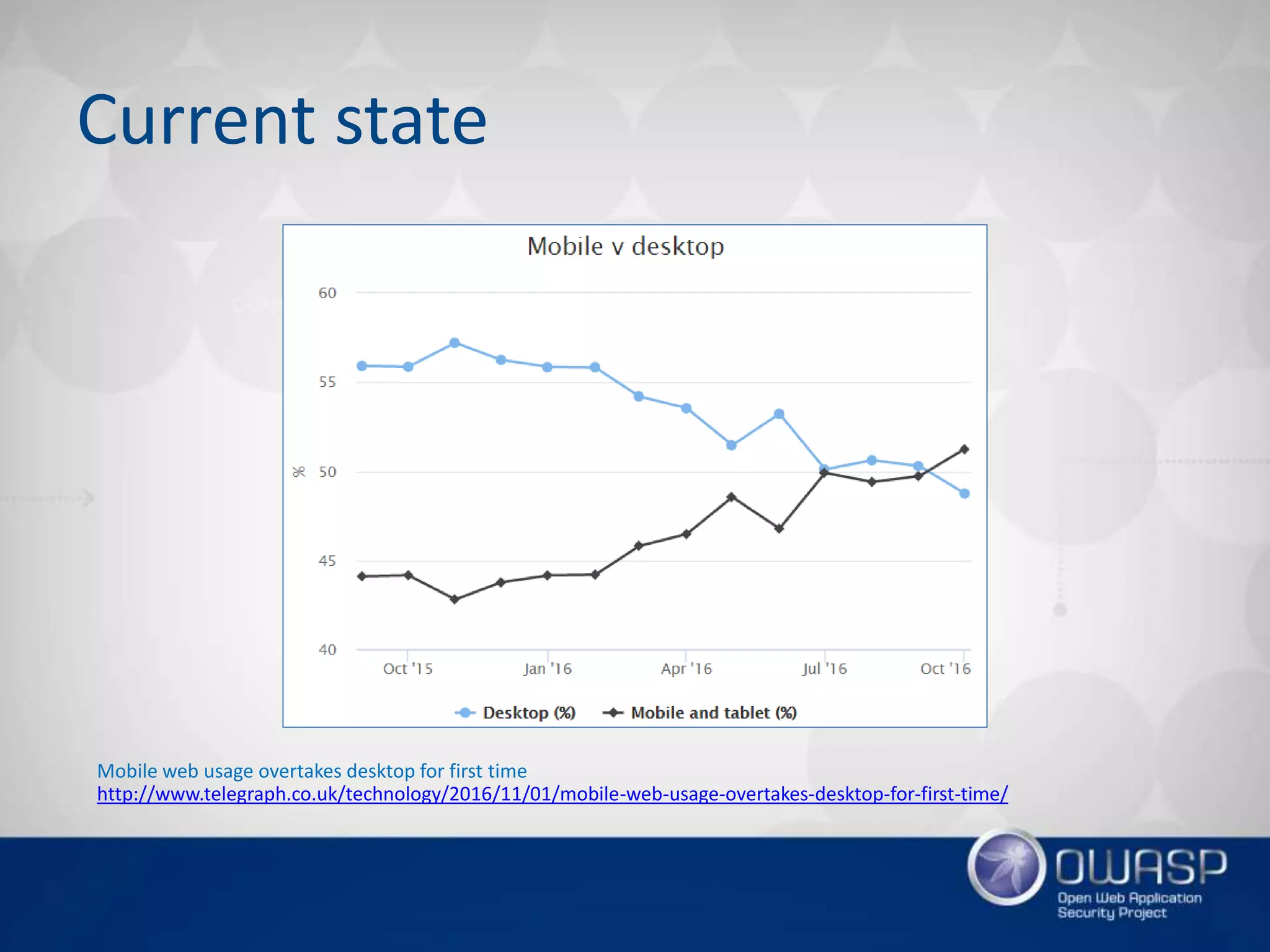
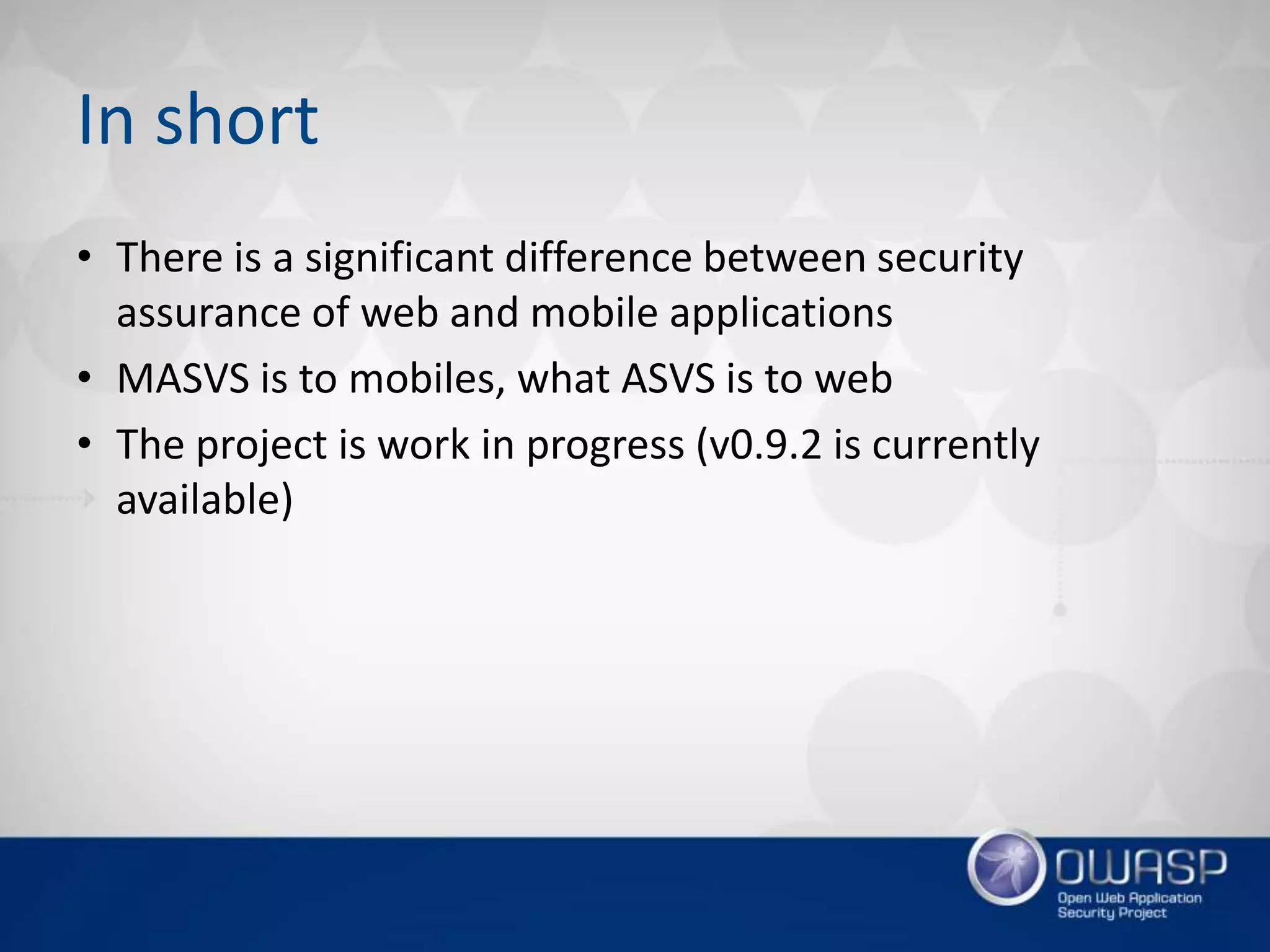
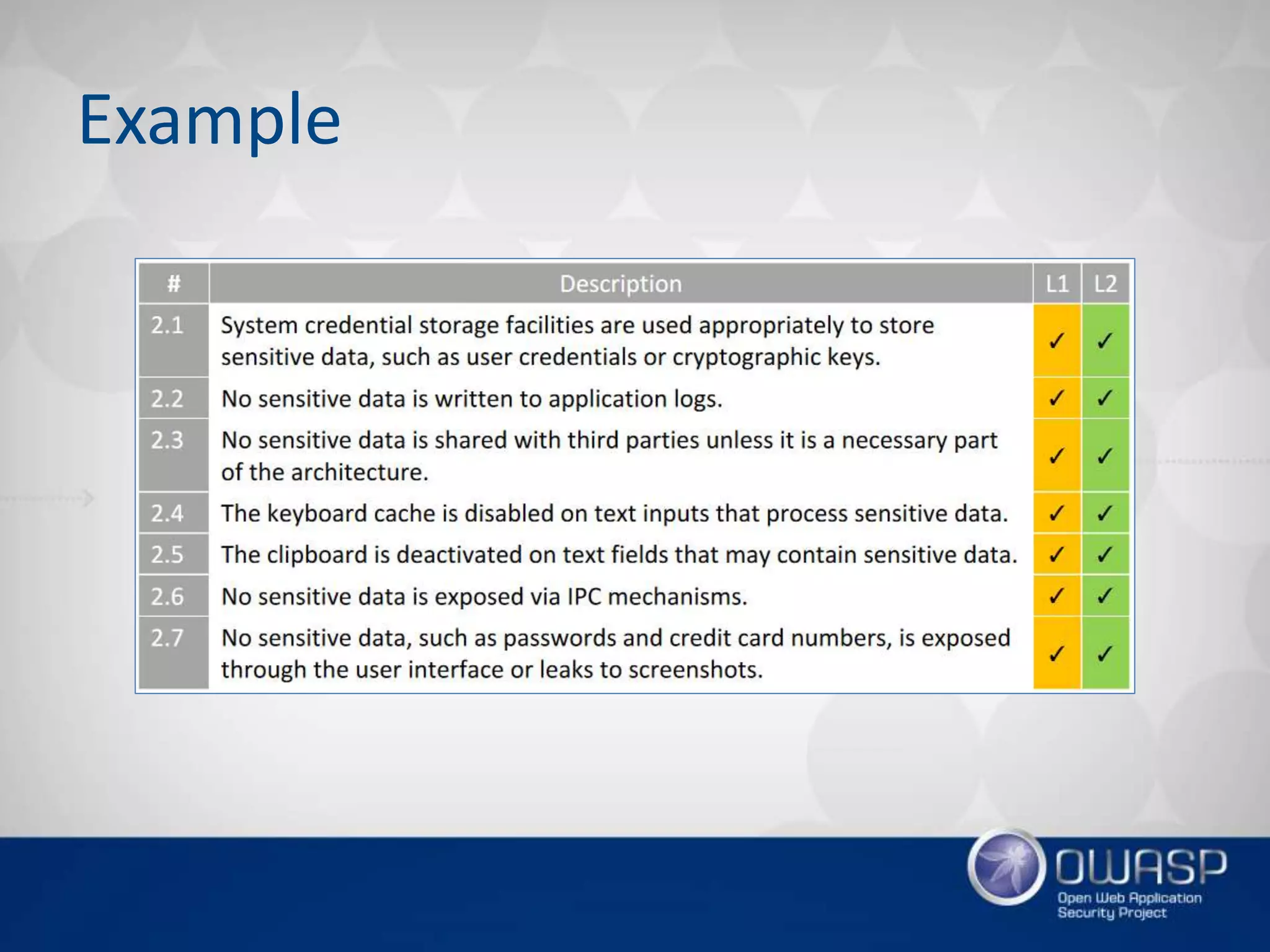
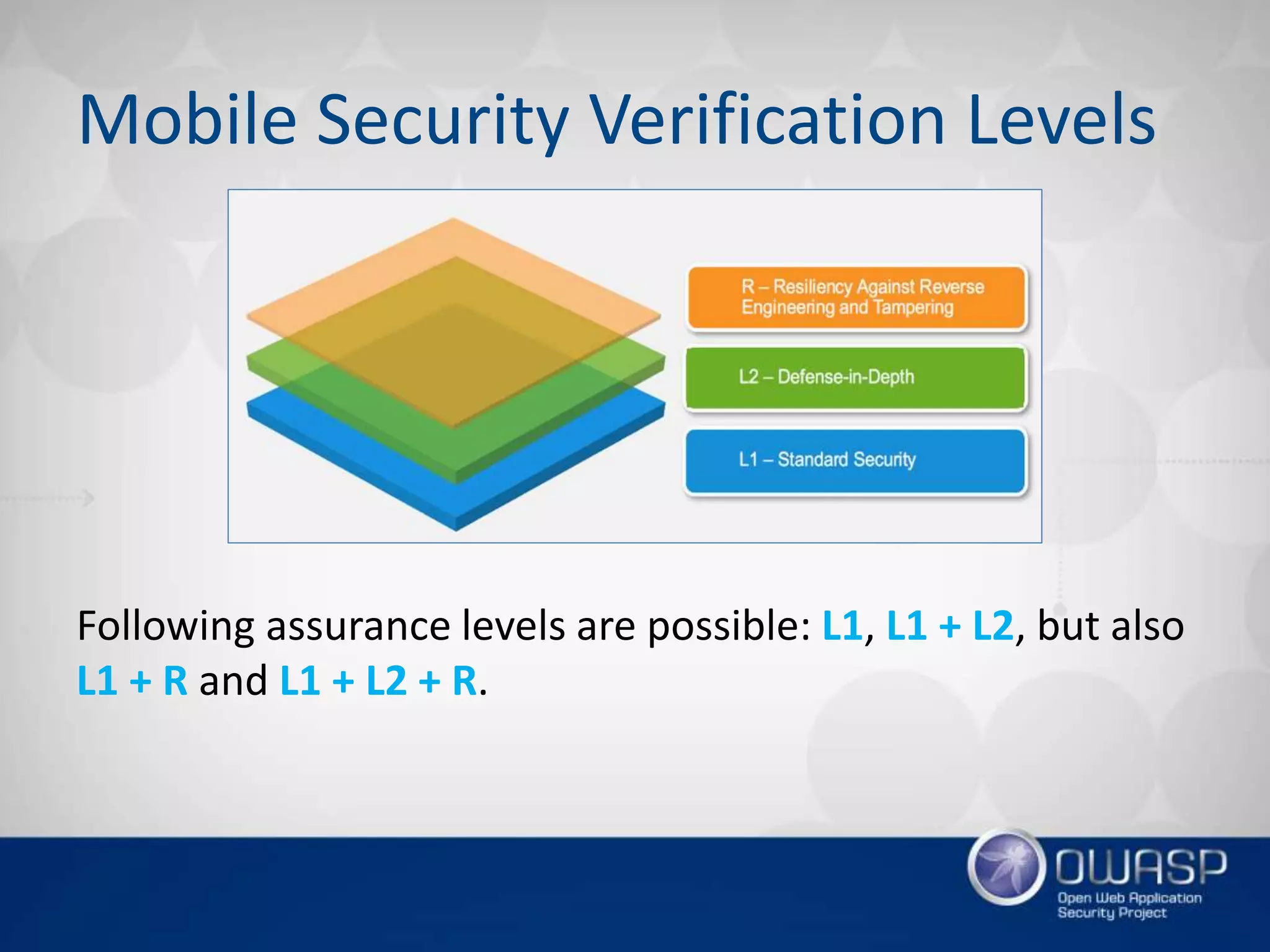
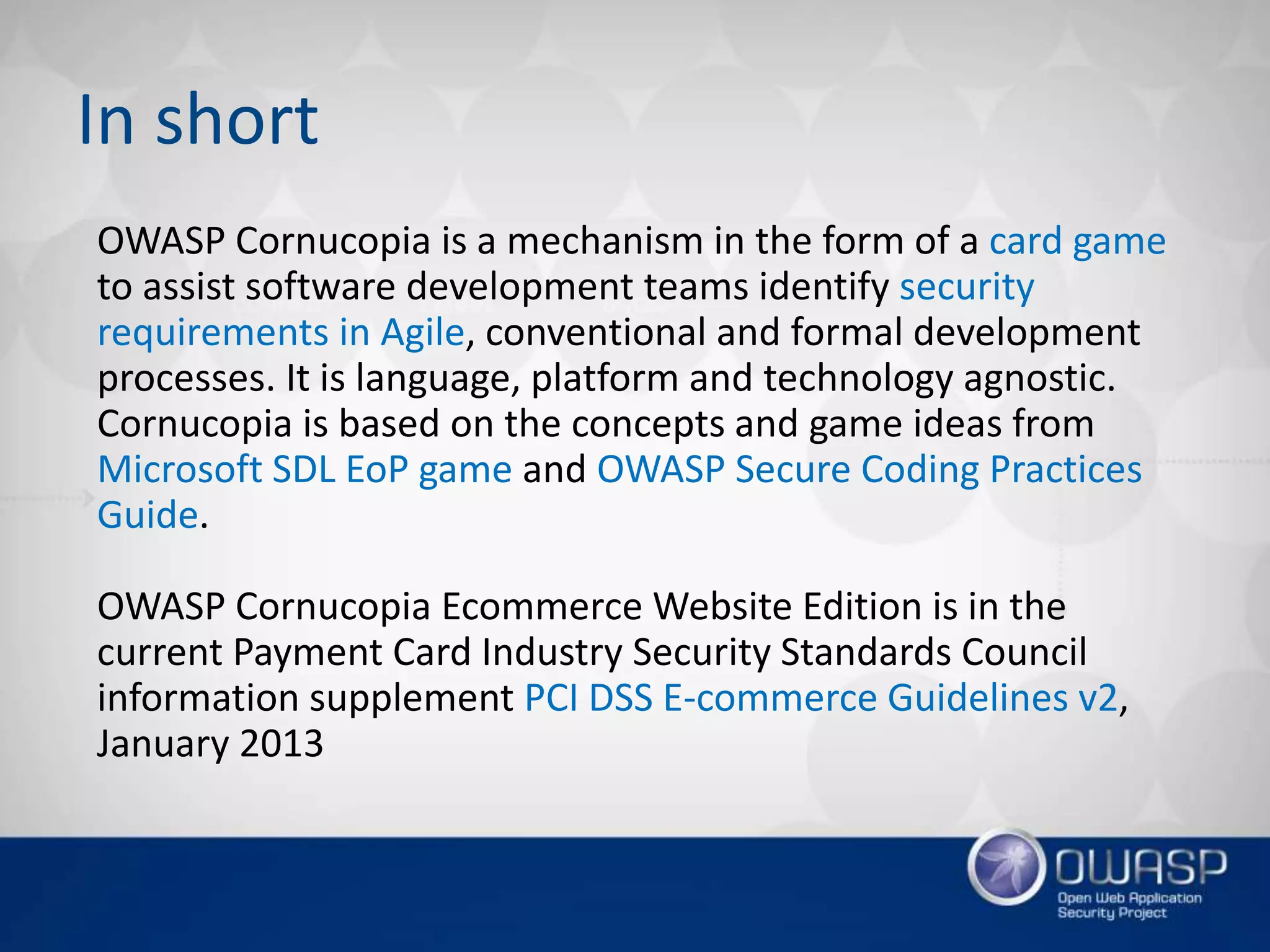
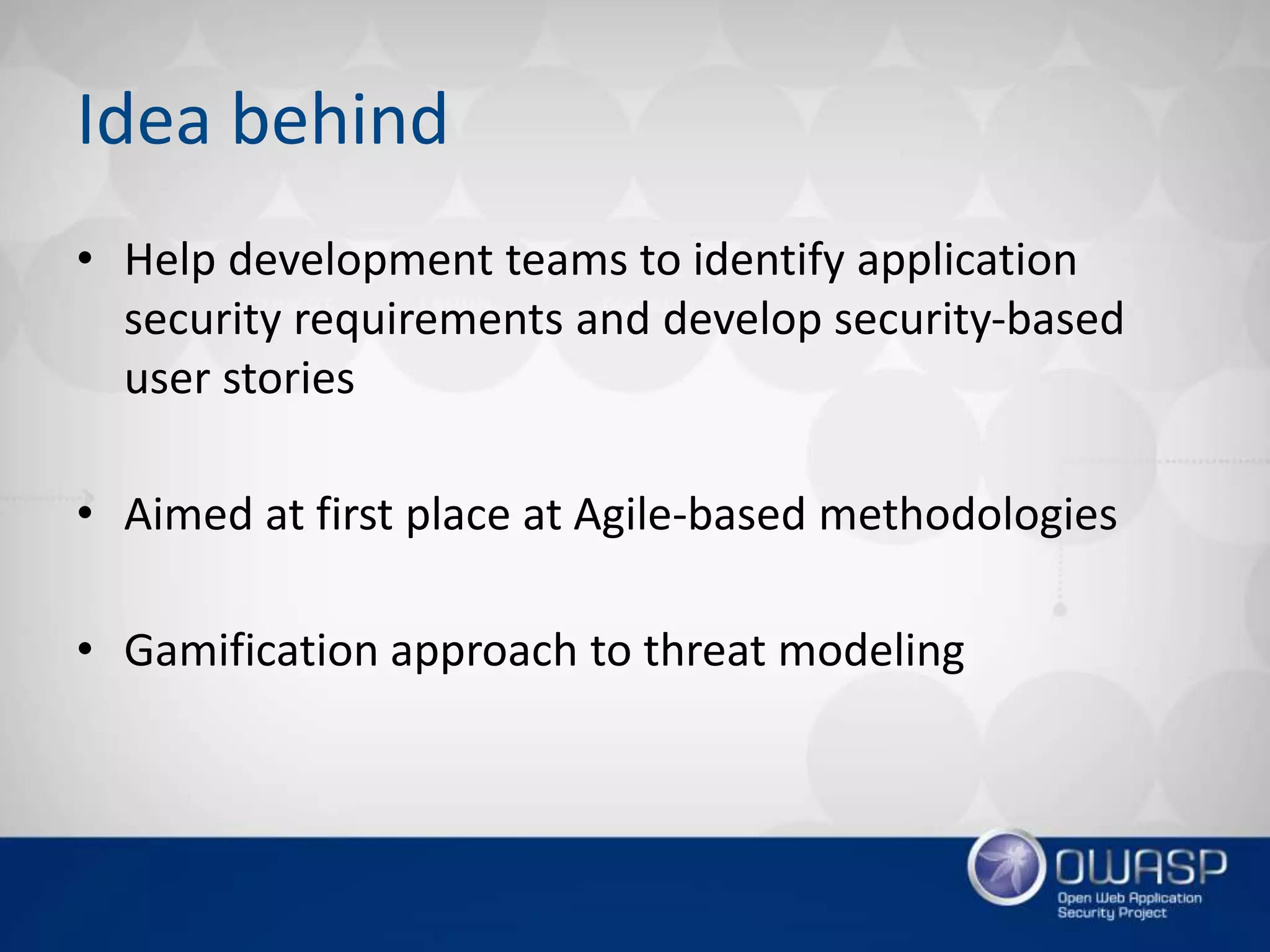
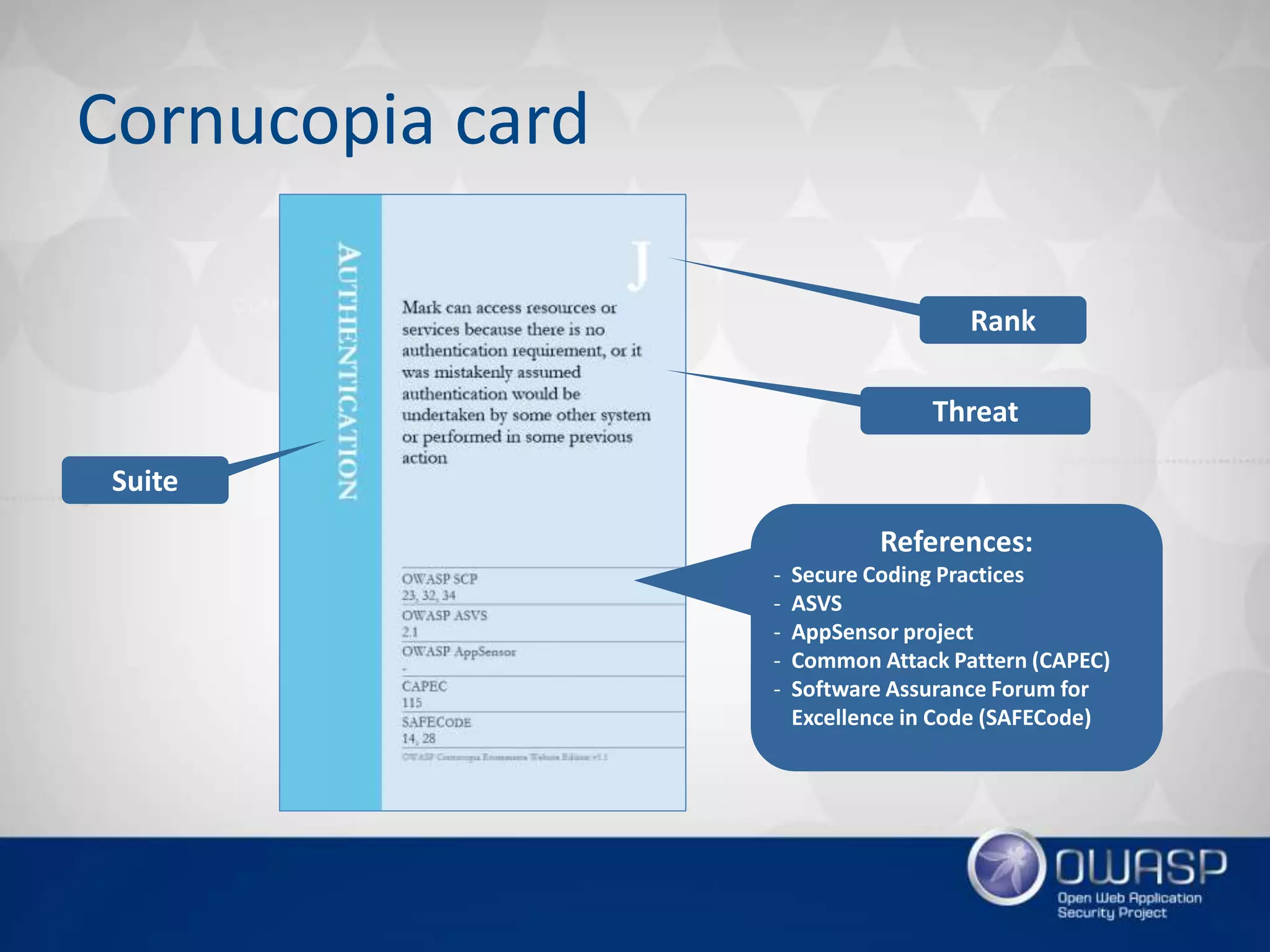
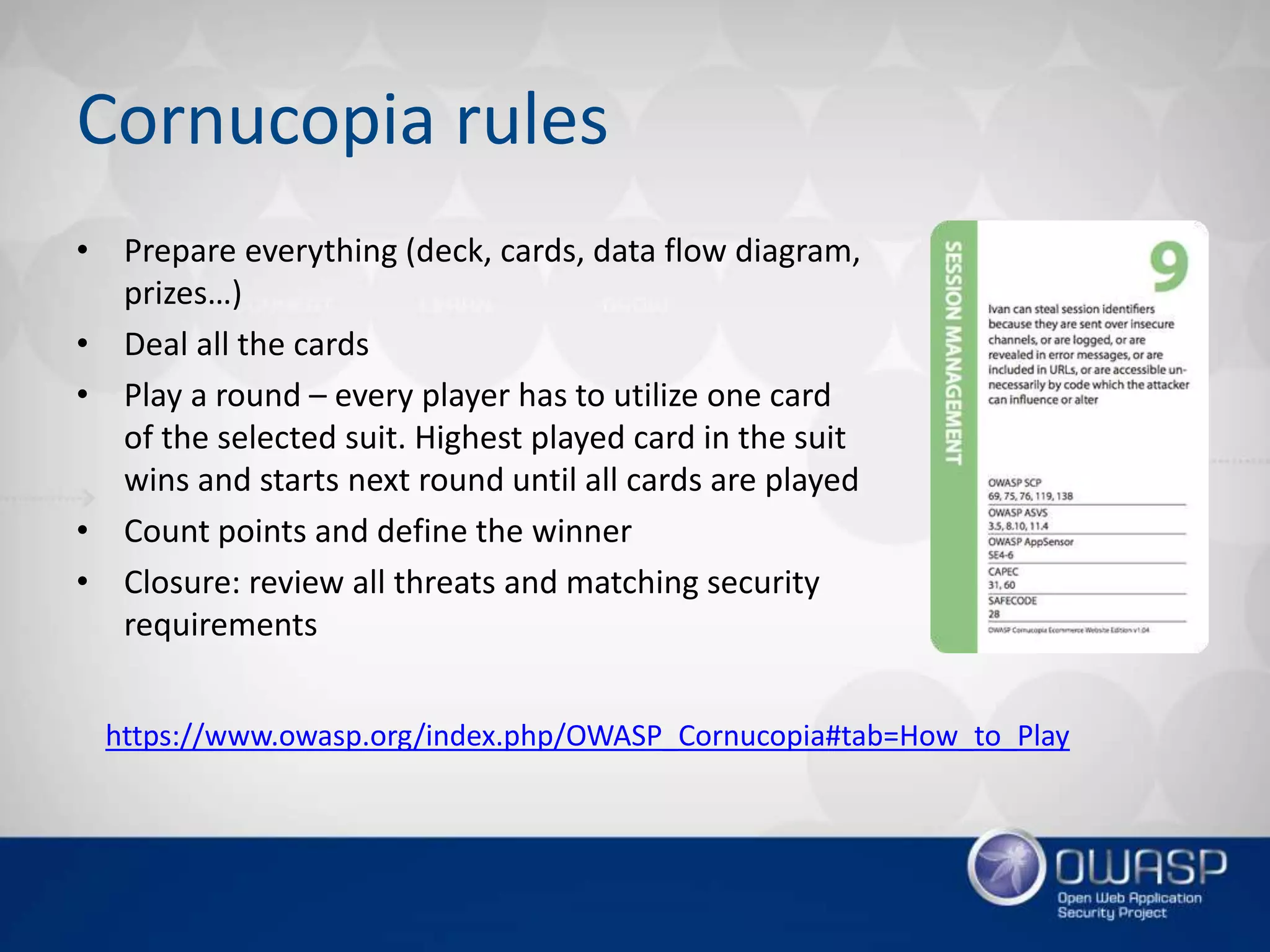
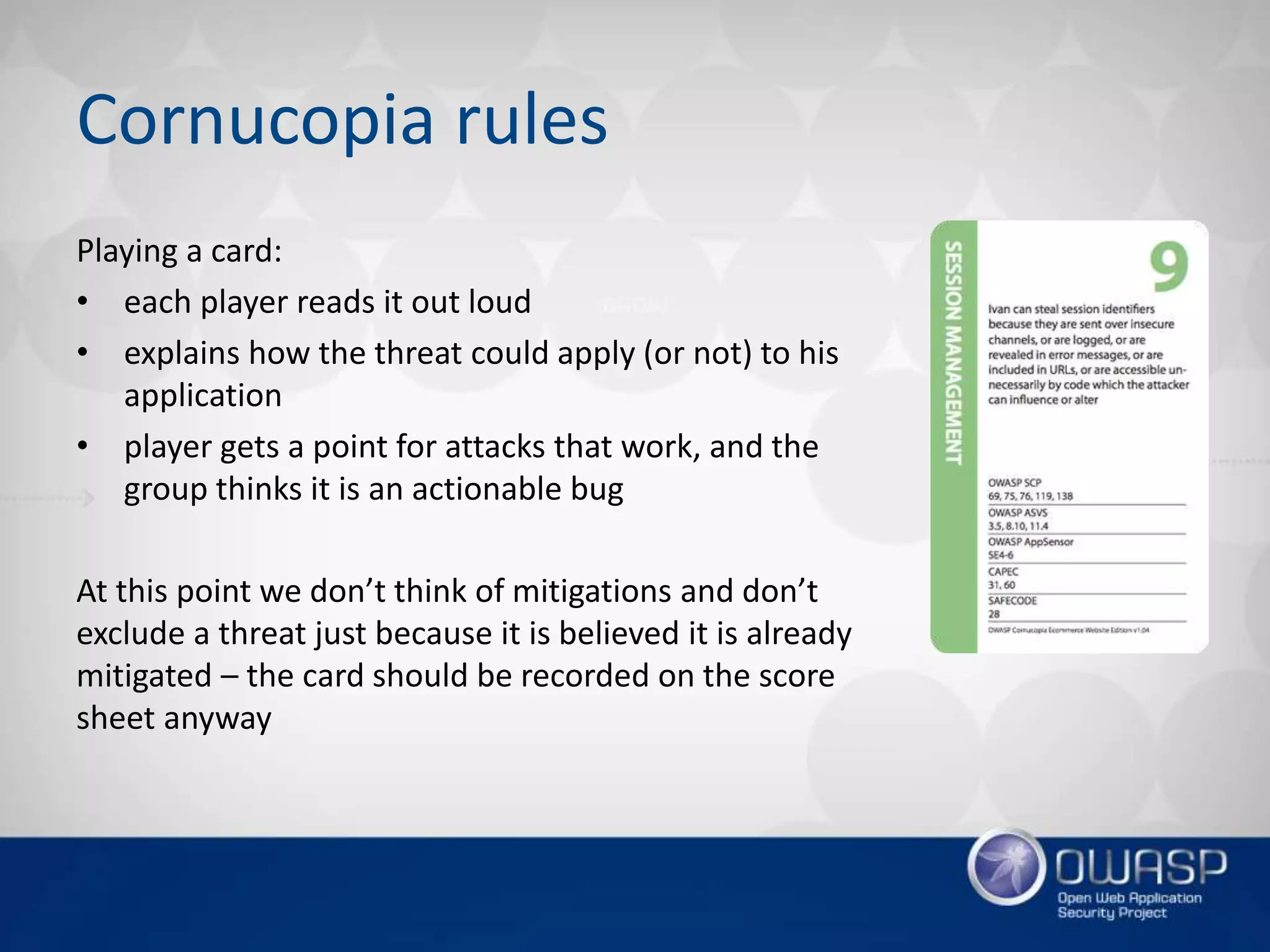
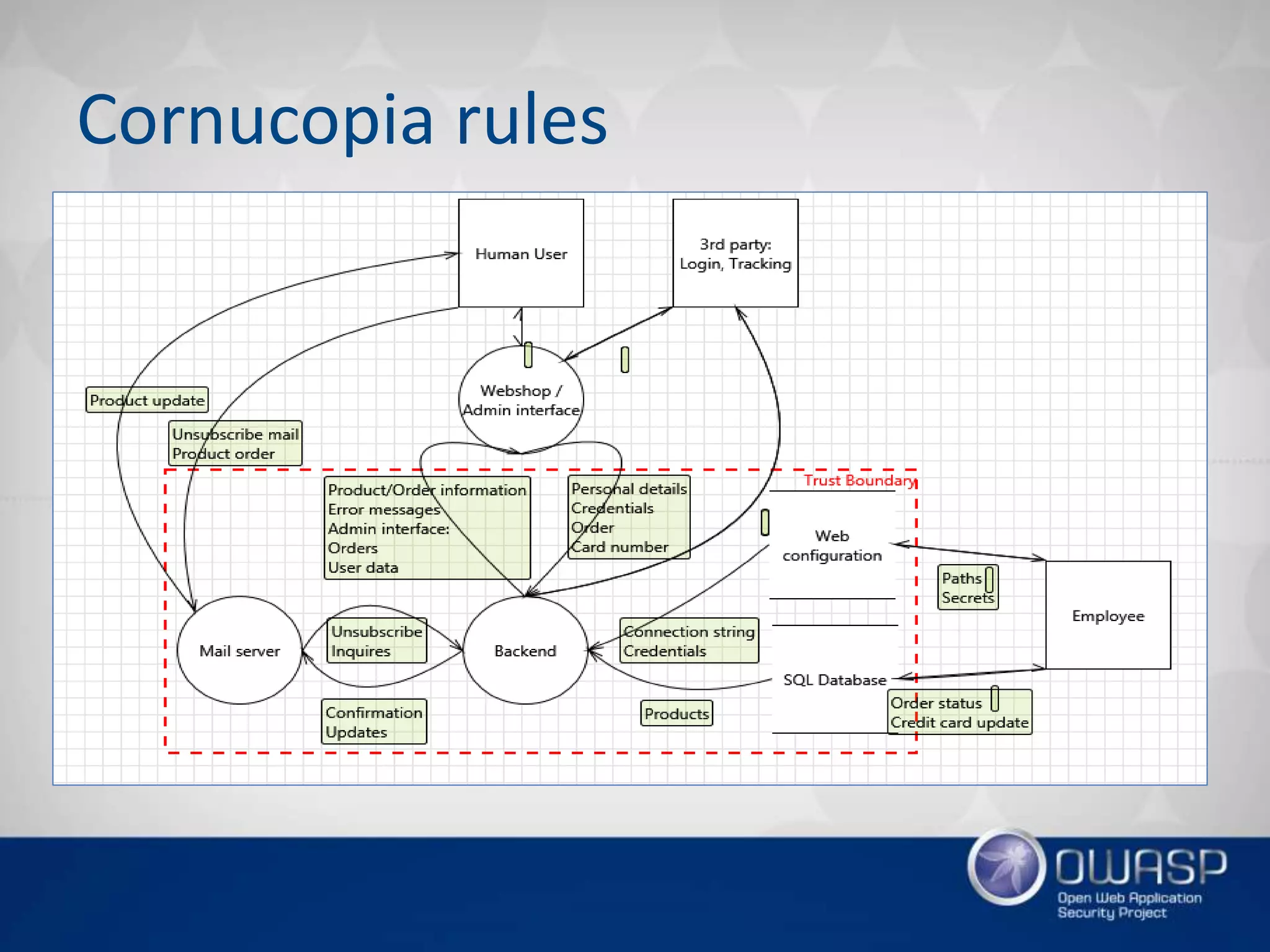
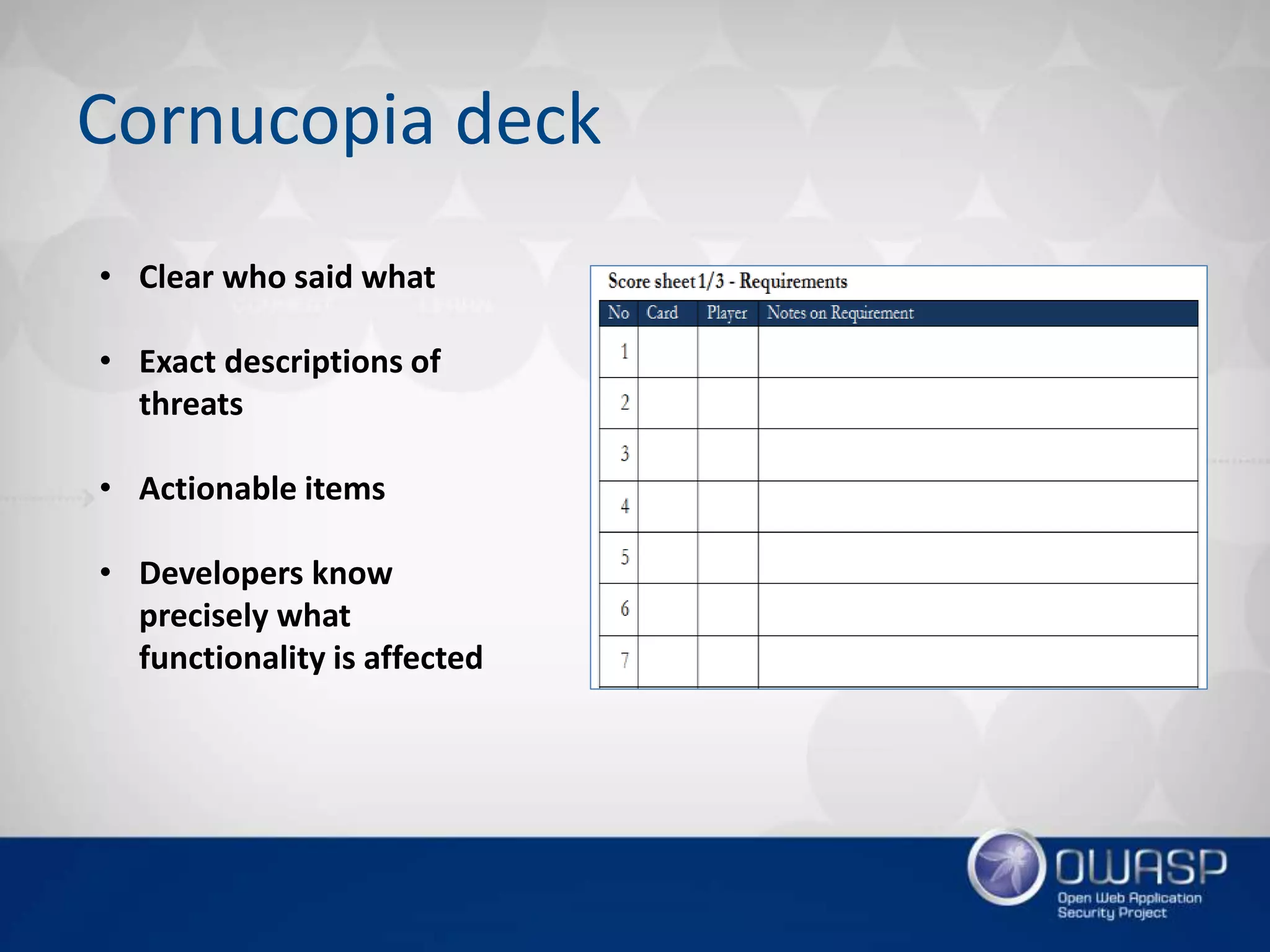
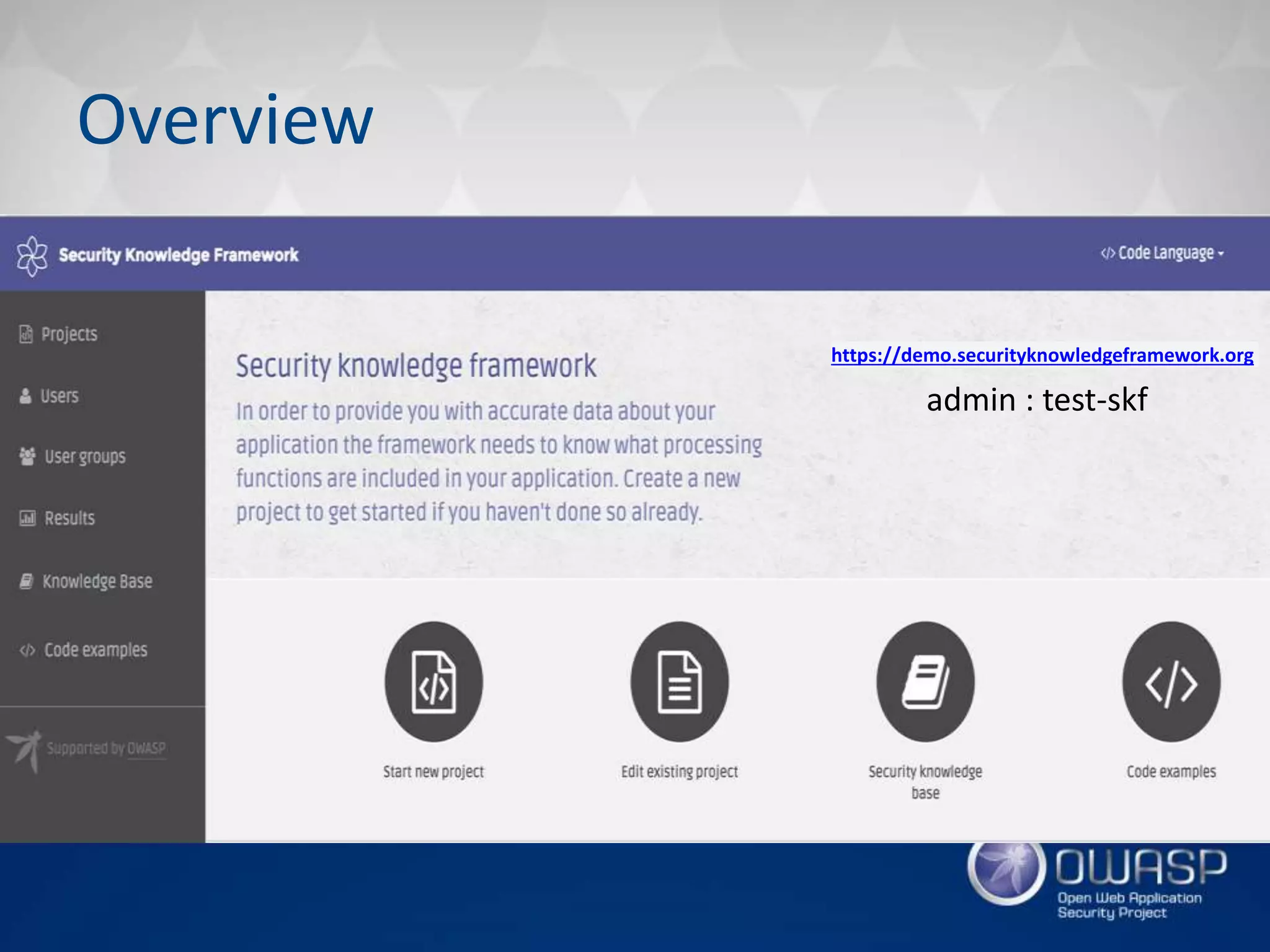
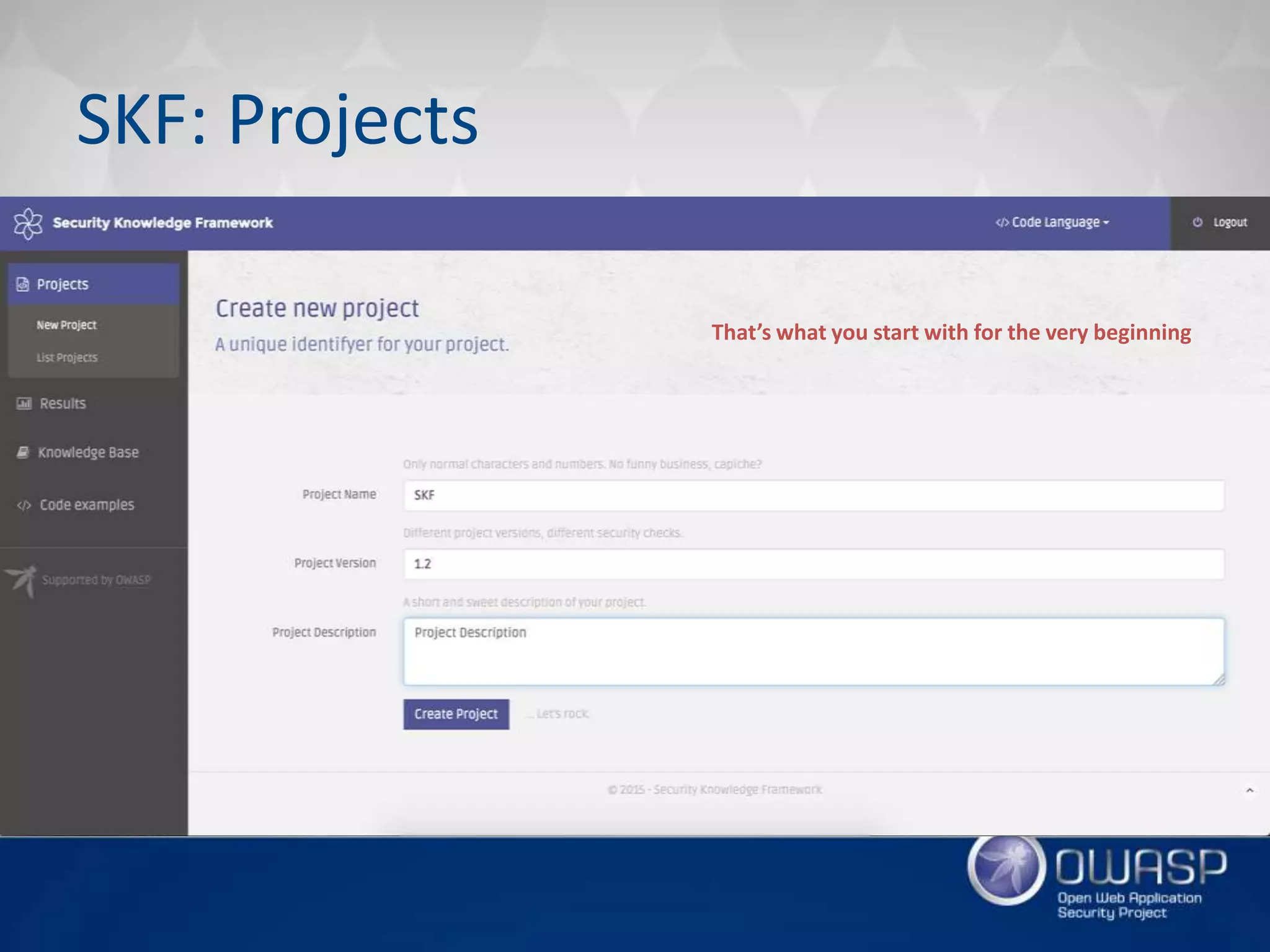
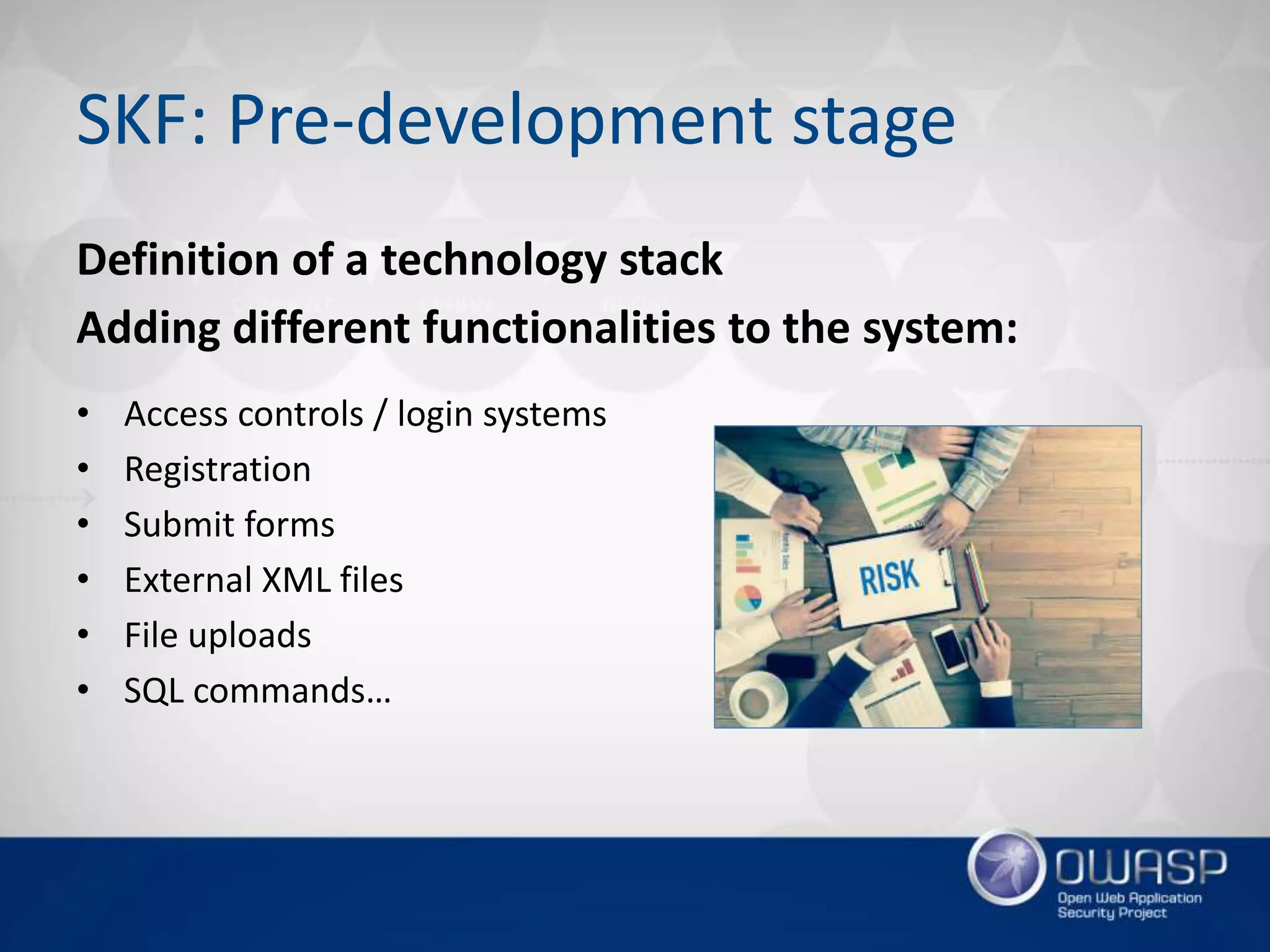
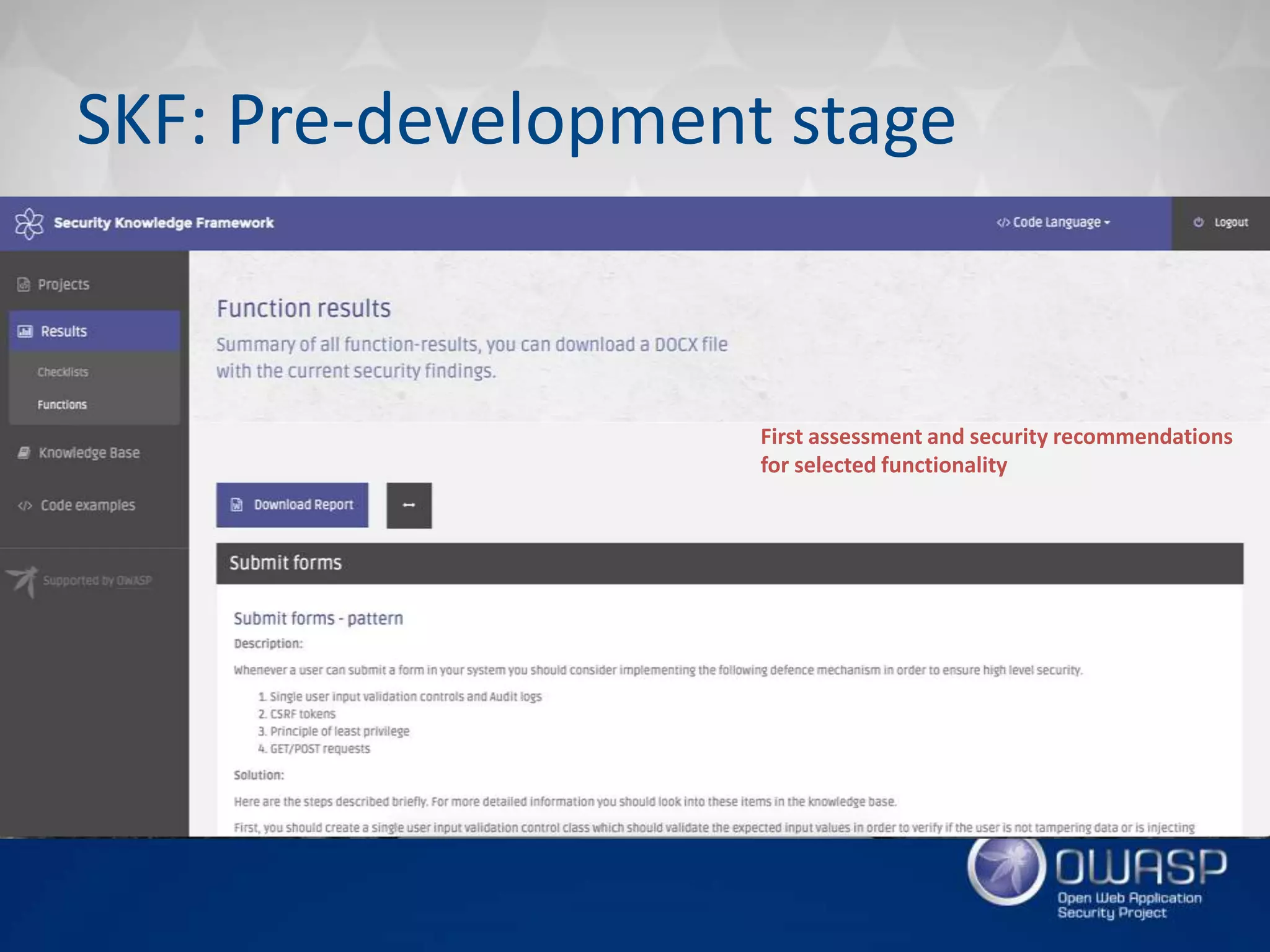
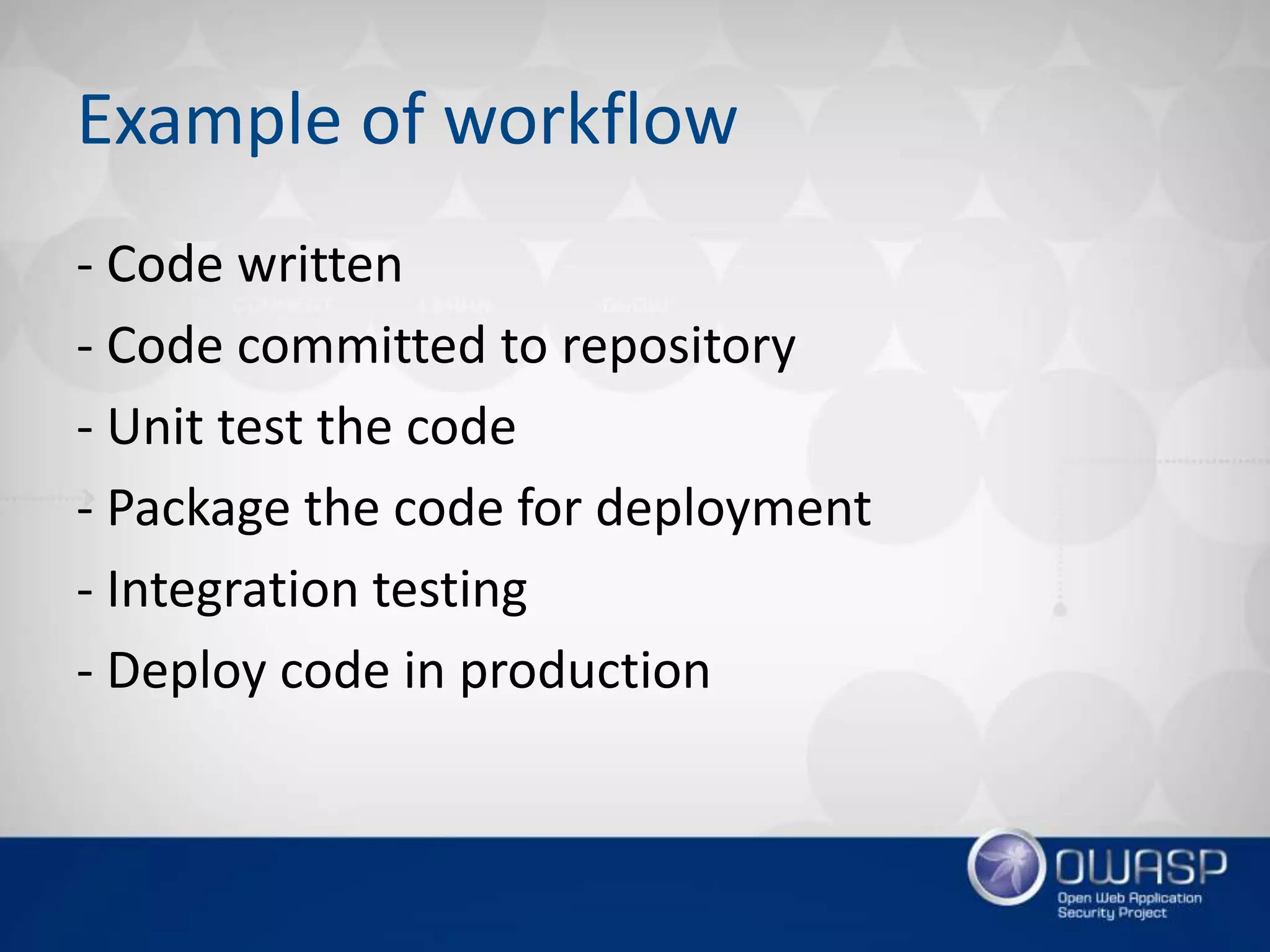
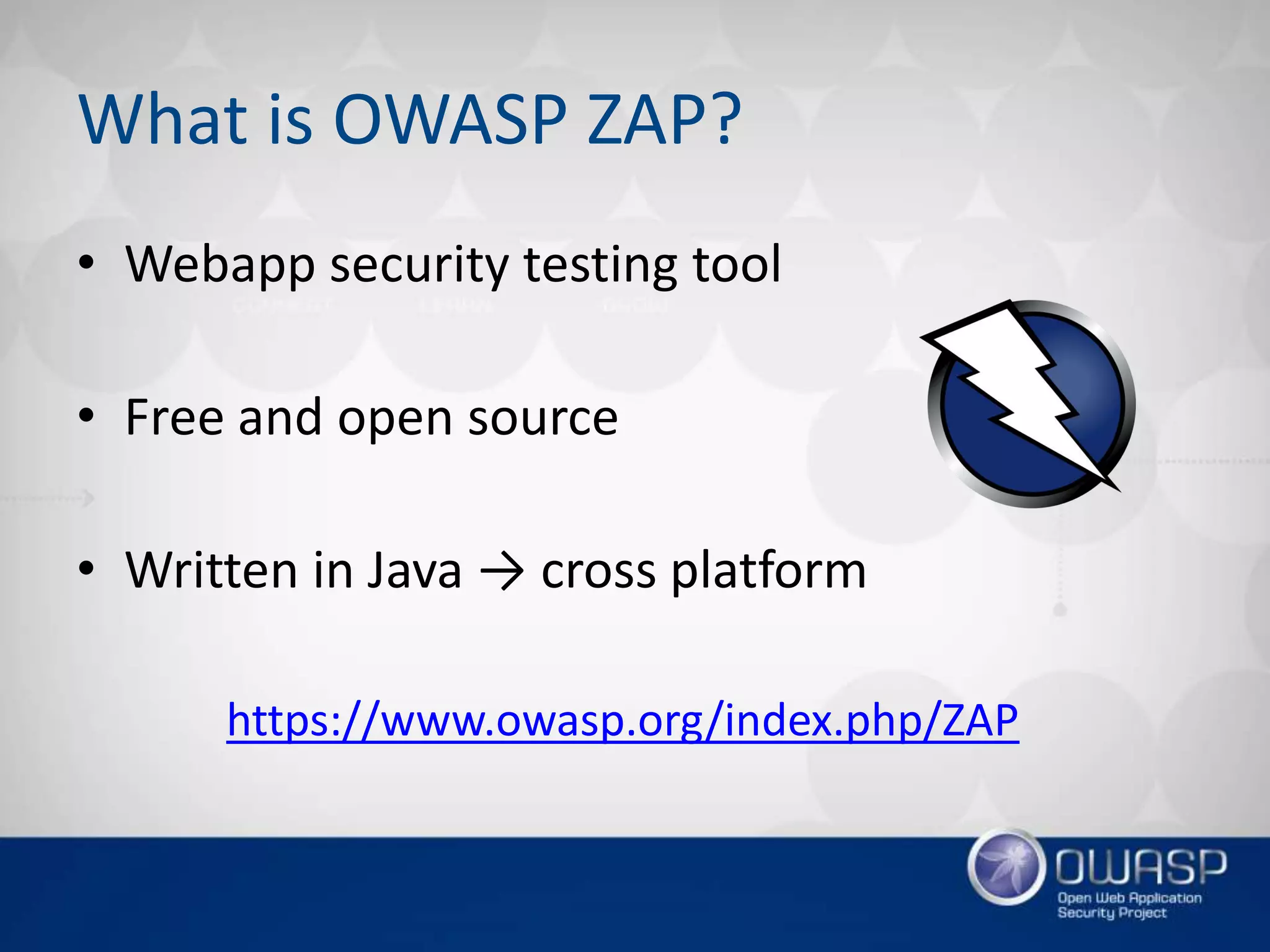
The document discusses various OWASP projects beyond the OWASP Top 10, detailing tools and frameworks such as WebGoat for hands-on security training, OWTF for efficient penetration testing, and ASVS for application security verification. It highlights issues in security training and management, presenting solutions to improve application security practices and awareness among developers. Additionally, it introduces gamification through OWASP Cornucopia to help teams identify security requirements during development.









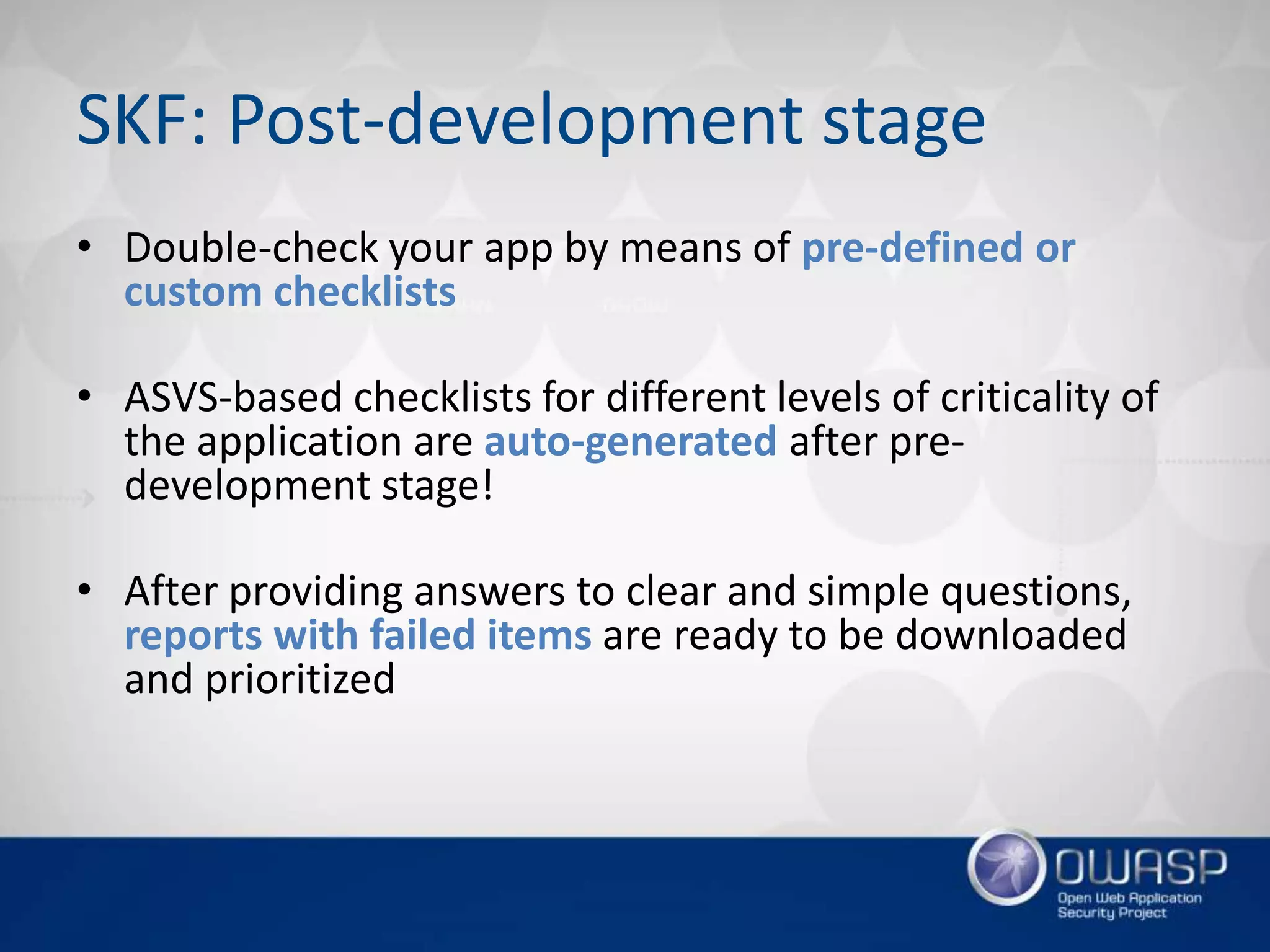
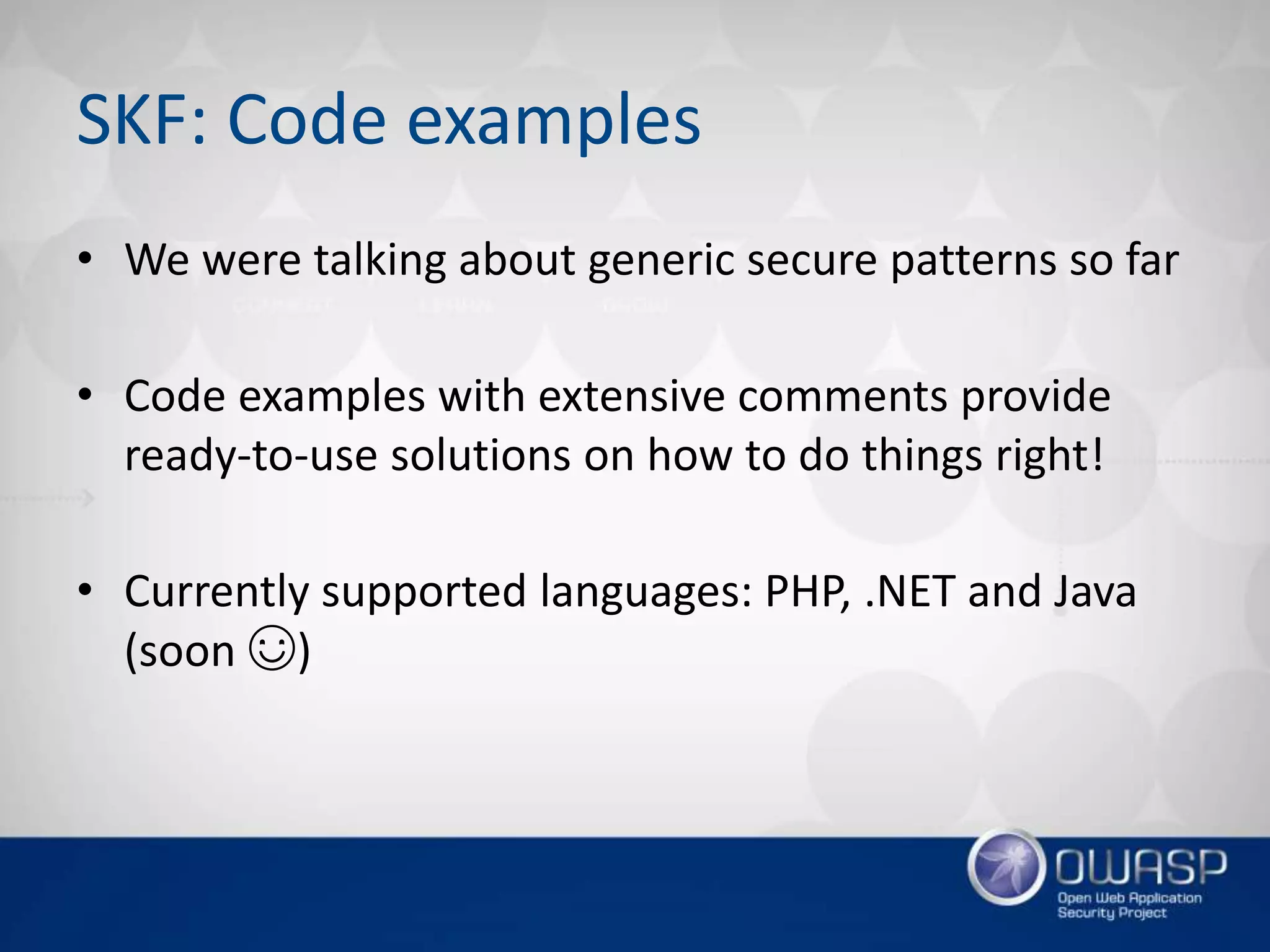



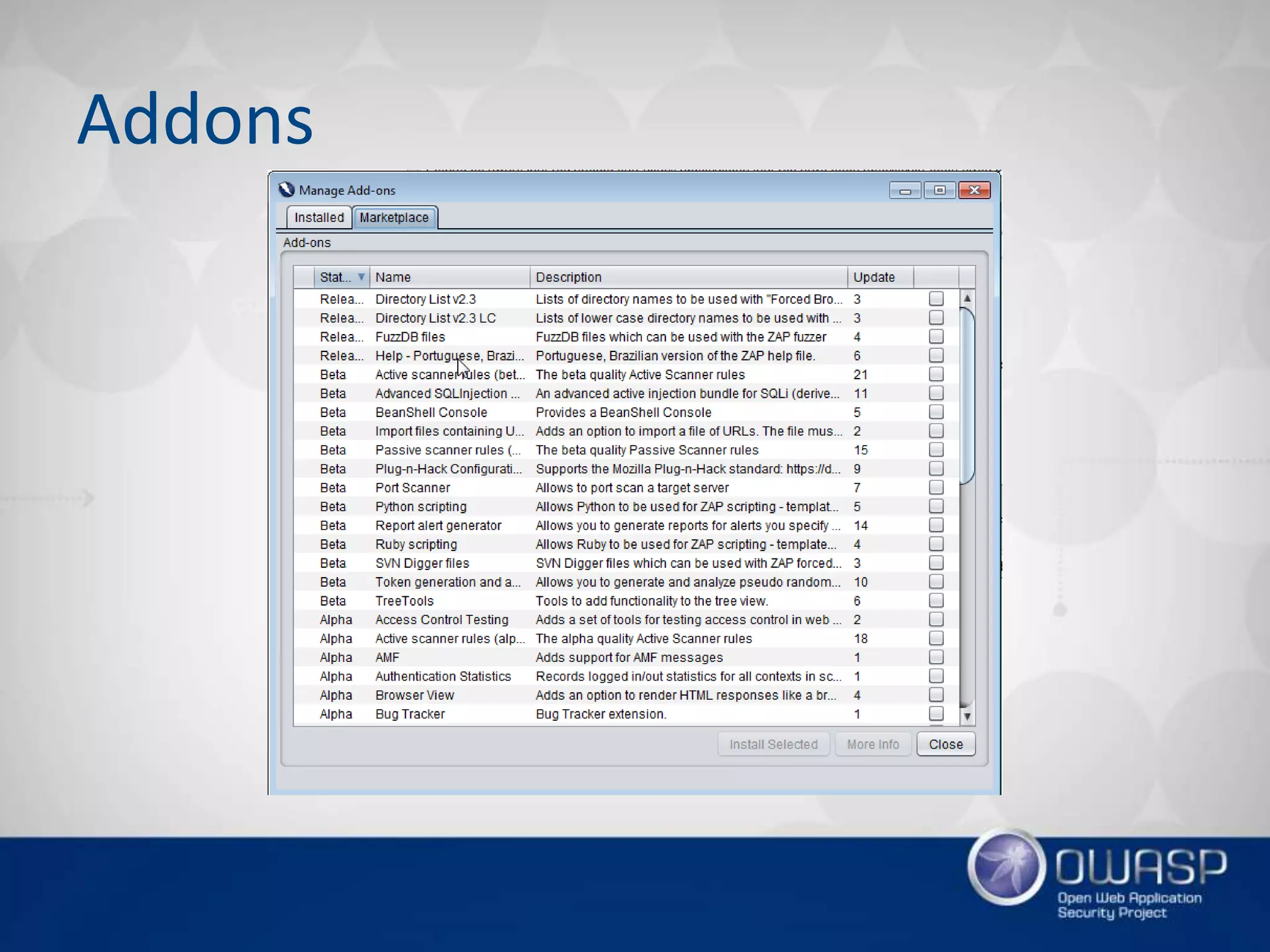
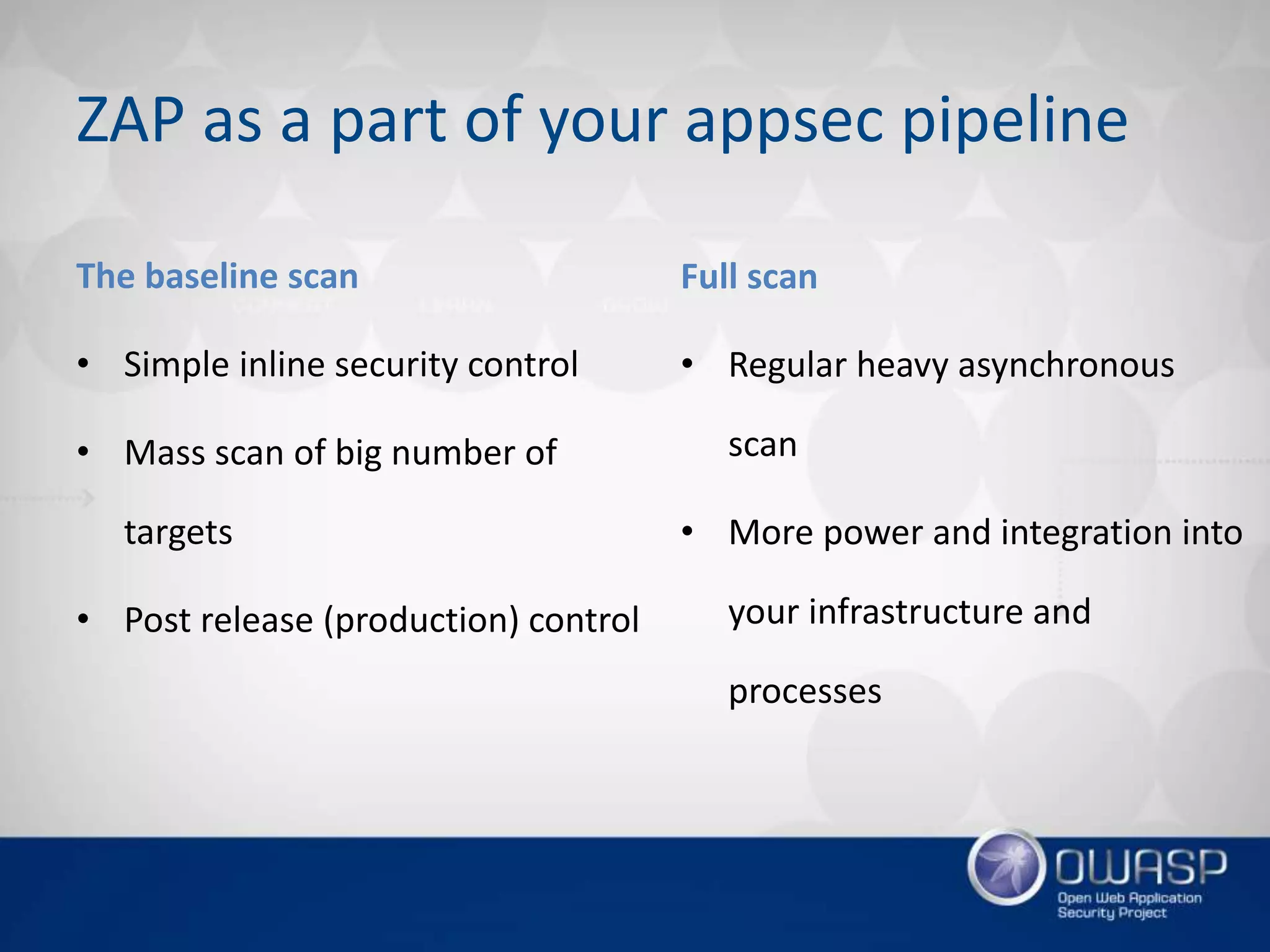
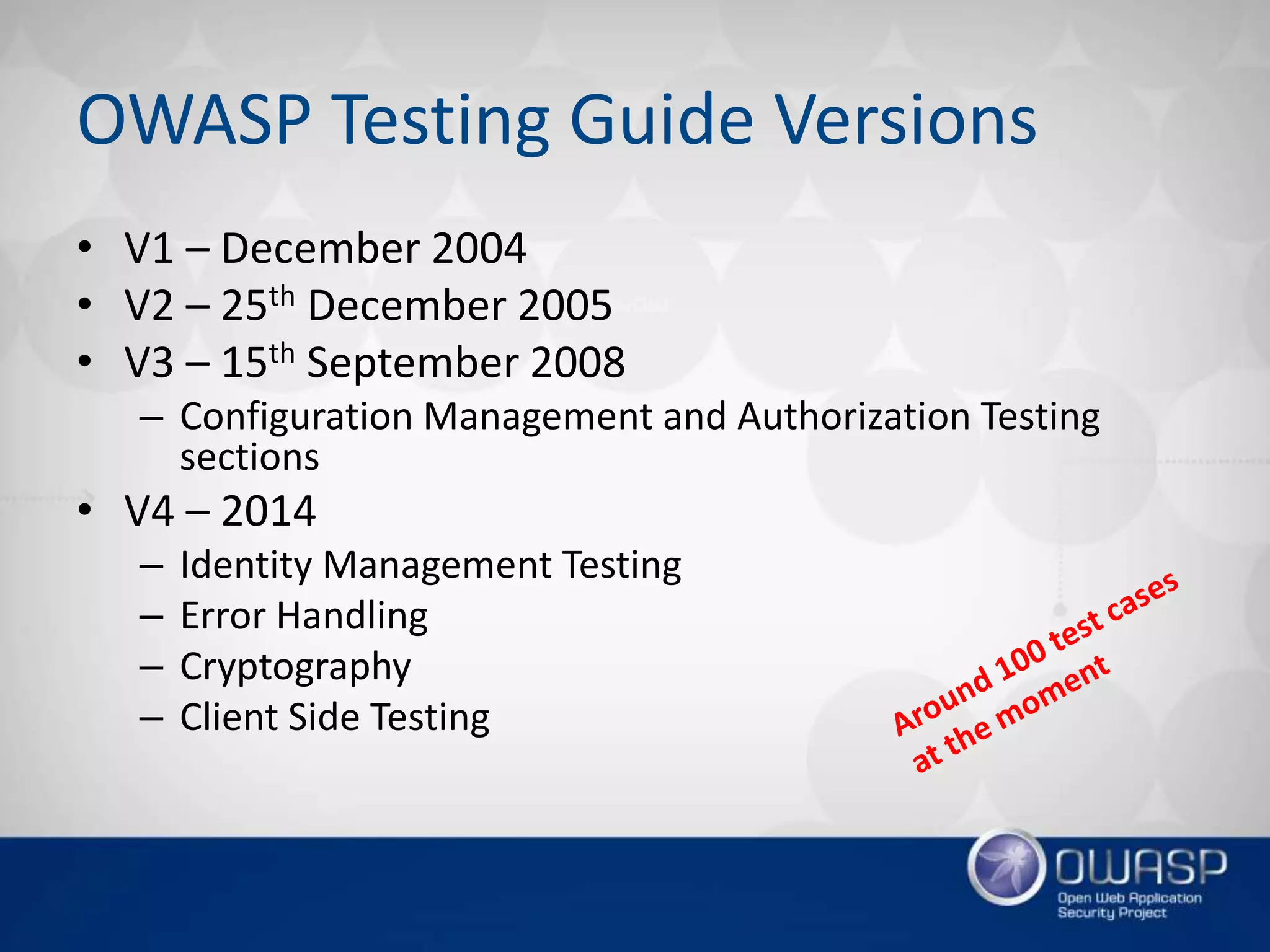
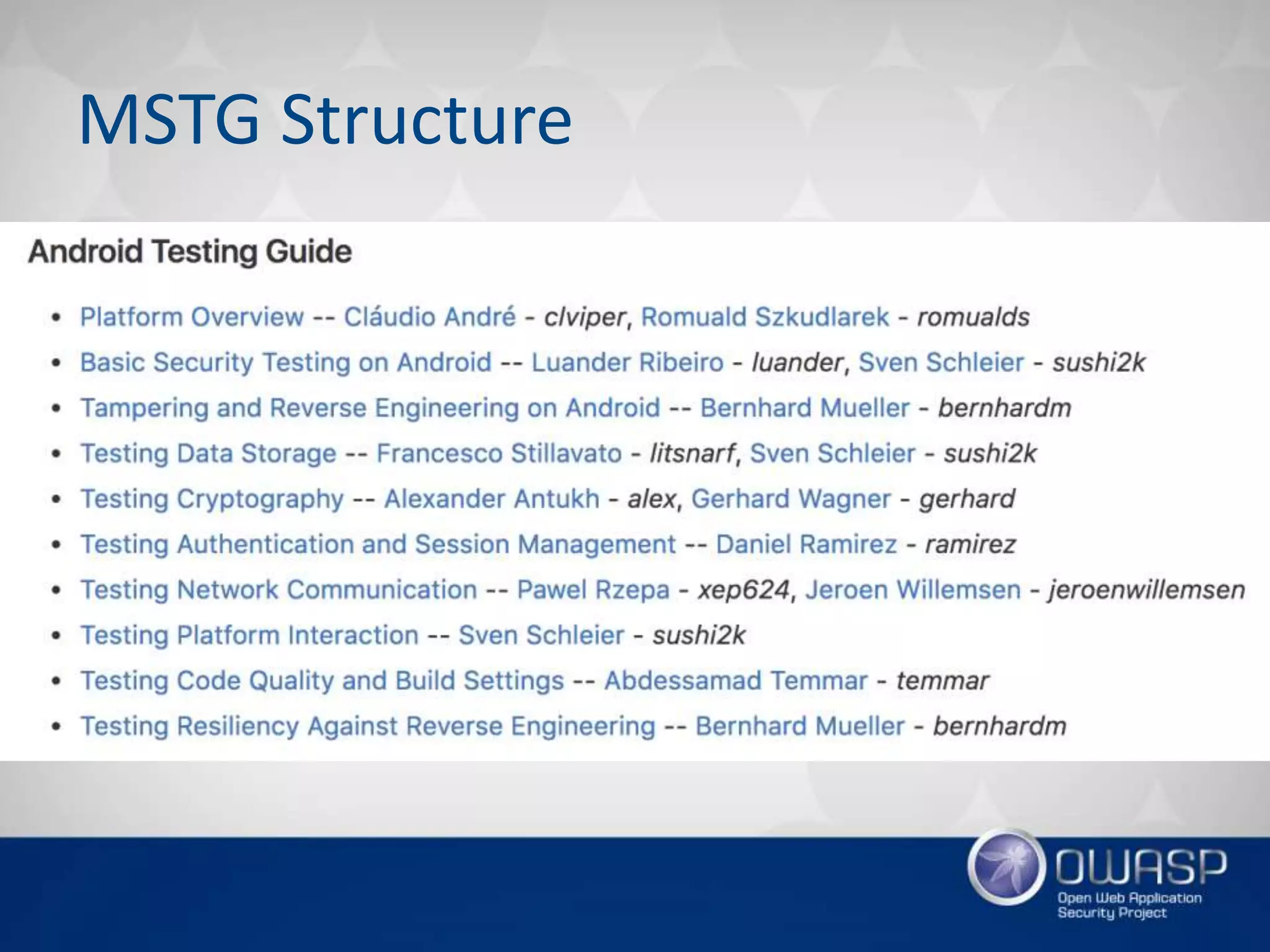
![The baseline scan example
$ docker run -t owasp/zap2docker-weekly zap-baseline.py -t https://oxdef.info
...
Total of 81 URLs
PASS: Cookie No HttpOnly Flag [10010]
...
WARN: Web Browser XSS Protection Not Enabled [10016] x 52
https://oxdef.info
...
FAIL: 0 WARN: 5 INFO: 0 IGNORE: 0 PASS: 21](https://image.slidesharecdn.com/owaspfinal-170218114136/75/Wroclaw-5-OWASP-Projects-beyond-Top-10-99-2048.jpg)
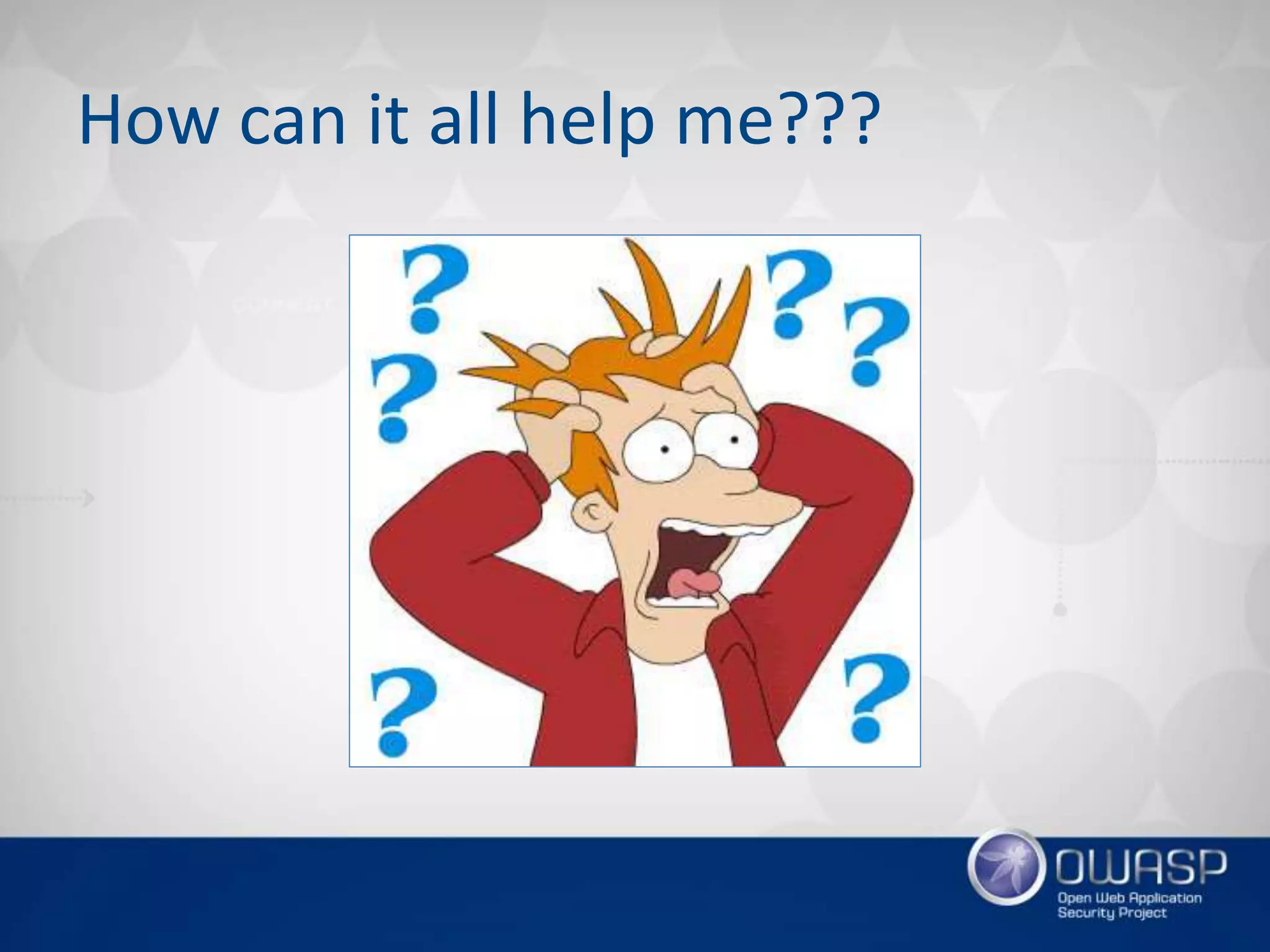
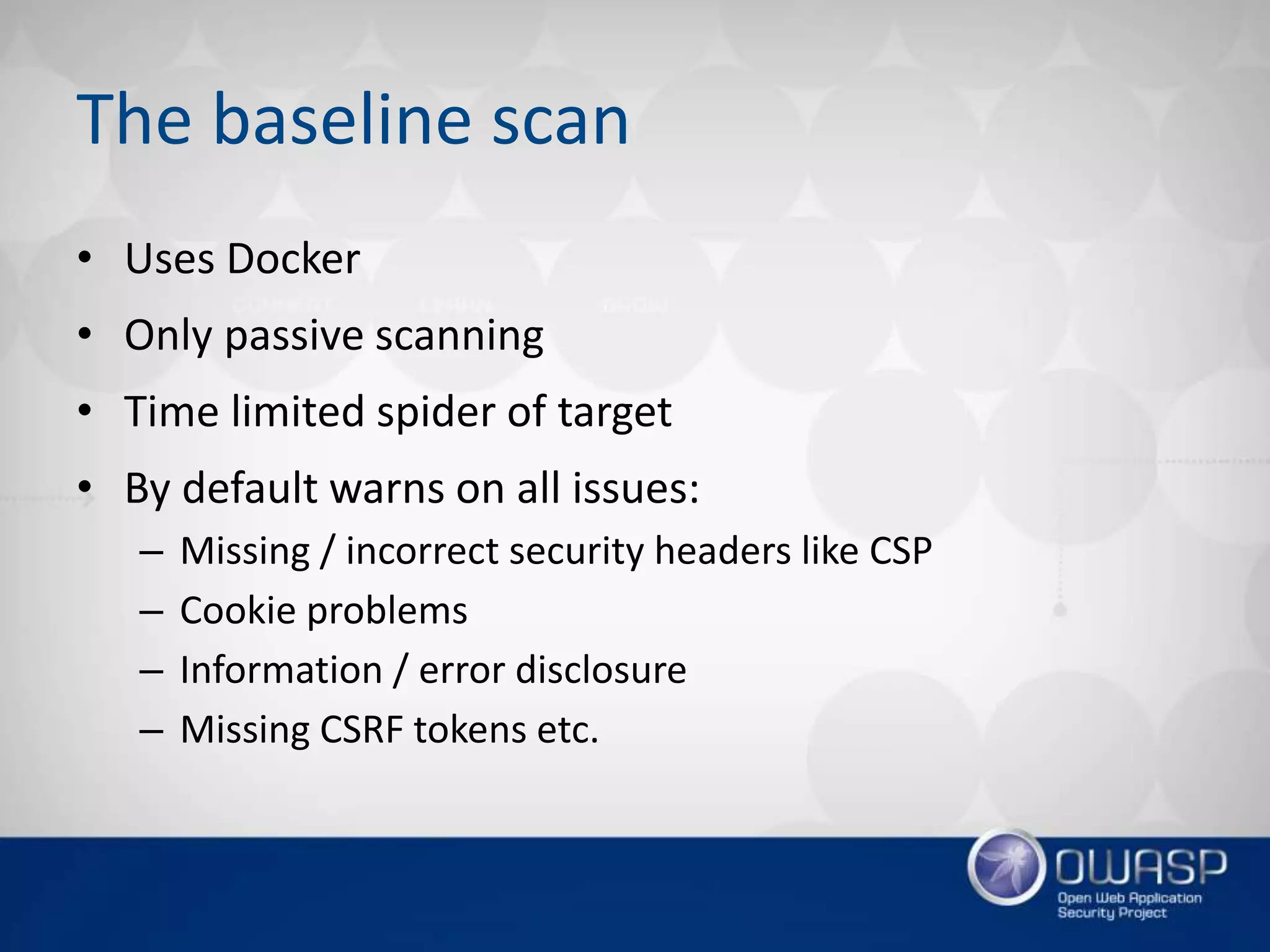
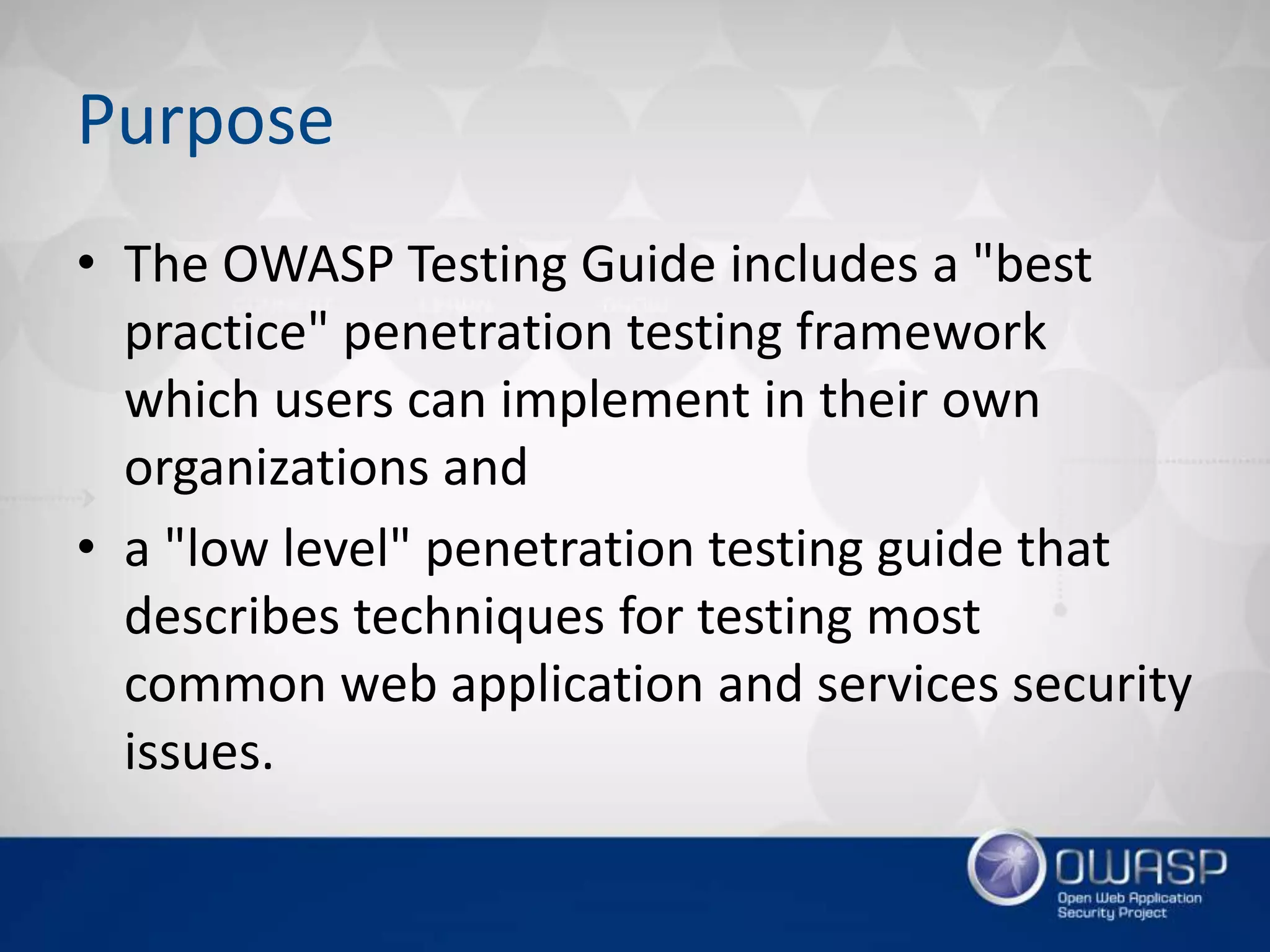
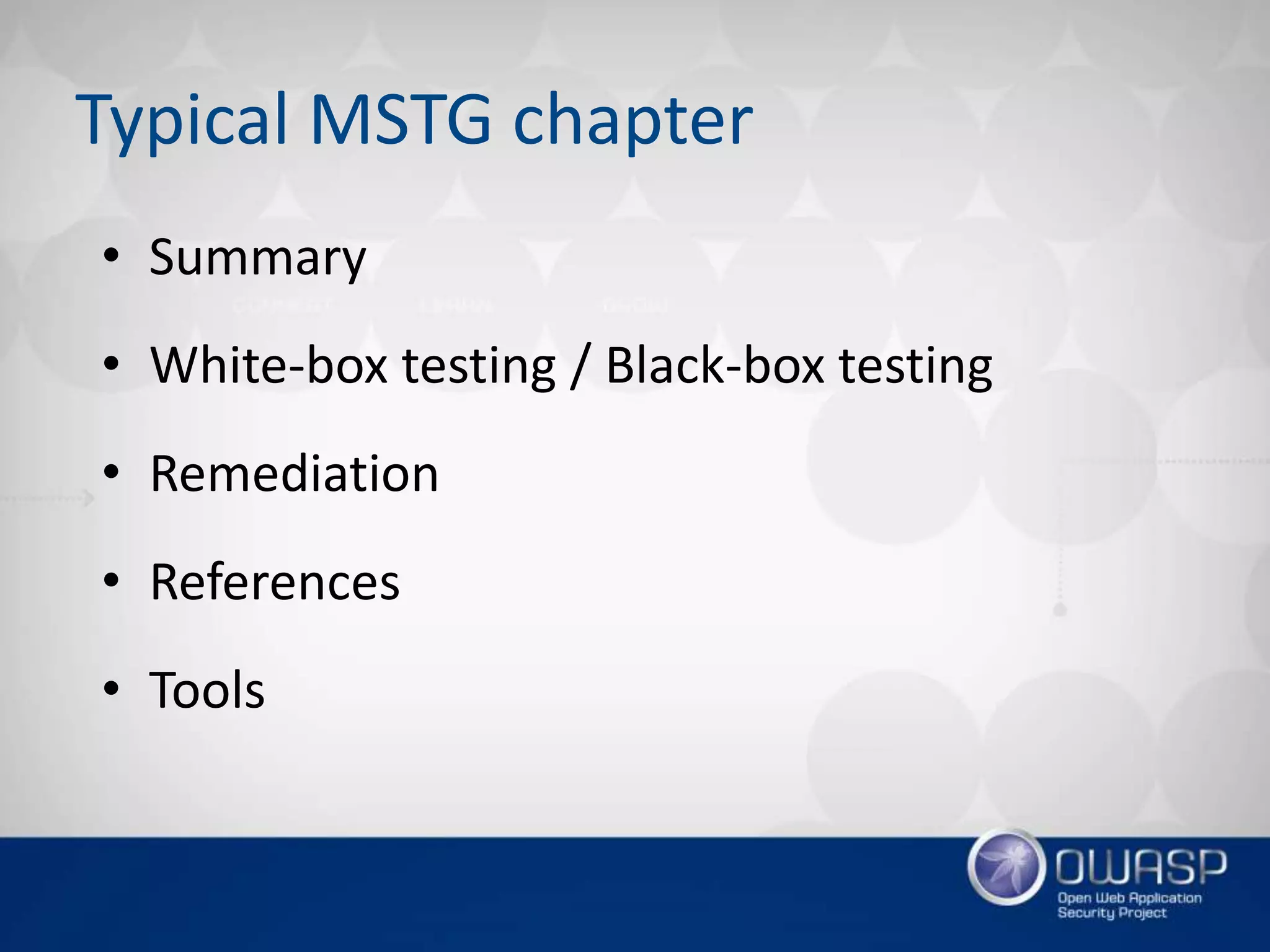
![1 n33d m0re p0w3r!
• REST API is your choice 😏
• zap.sh -daemon -host 0.0.0.0 -port 8080
• http(s)://zap/<format>/<component>/<operation>/<
op name>[/?<params>]
• Also available in Docker image owasp/zap2docker-*
• Maps closely to the UI / code
• JSON, HTML and XML formats
• Clients in: Java, Python, NodeJS, .Net, PHP, Go ...](https://image.slidesharecdn.com/owaspfinal-170218114136/75/Wroclaw-5-OWASP-Projects-beyond-Top-10-101-2048.jpg)

![[Wroclaw #5] OWASP Projects: beyond Top 10](https://image.slidesharecdn.com/owaspfinal-170218114136/75/Wroclaw-5-OWASP-Projects-beyond-Top-10-131-2048.jpg)