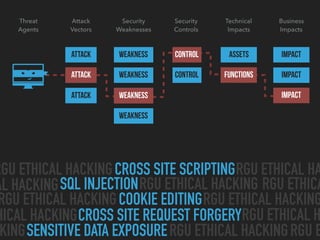
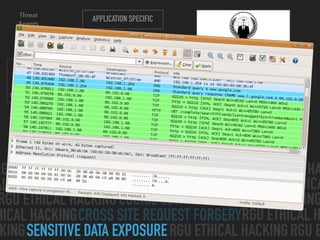
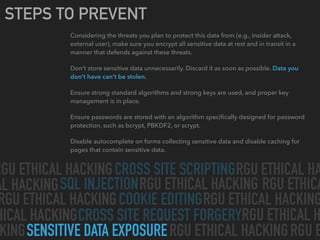
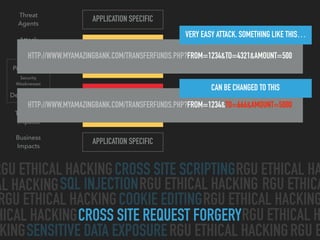
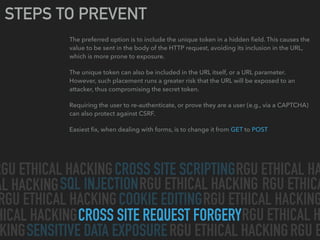
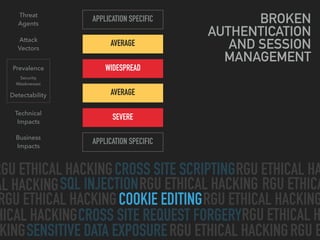
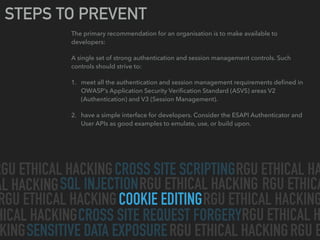
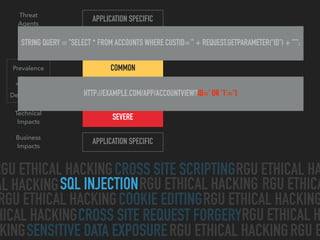
The document discusses various web application attacks like cross-site scripting, SQL injection, cross-site request forgery, sensitive data exposure, and cookie editing. For each attack, it provides information on threat agents, attack vectors, security weaknesses, impacts, prevalence, detectability, example exploits, and steps to prevent the attack. The overall document serves as an educational guide on common web hacking techniques and how to avoid falling victim to them.