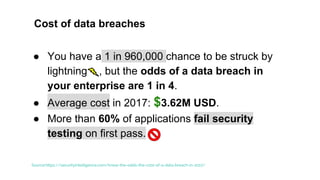
This document discusses security vulnerabilities and the OWASP Top 10. It provides background on why security is important when developing software, costs of data breaches, and an overview of the OWASP organization and Top 10 vulnerabilities. The Top 10 vulnerabilities discussed in more detail include injection, broken authentication and session management, cross-site scripting, insecure direct object references, security misconfiguration, sensitive data exposure, missing function level access control, cross-site request forgery, using components with known vulnerabilities, and unvalidated redirects/forwards. Examples are given for each vulnerability.