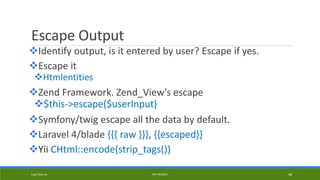
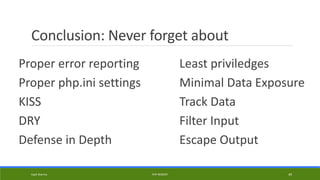
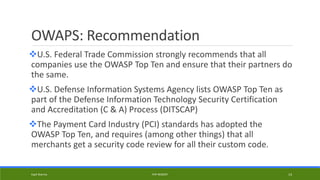
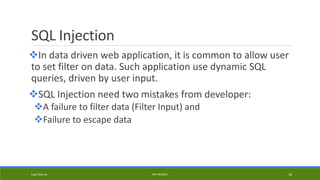
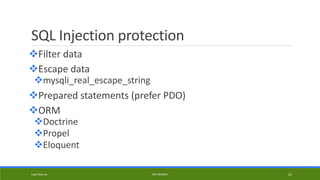
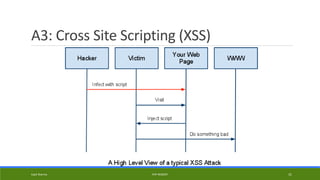
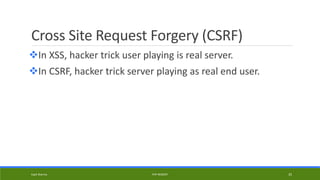
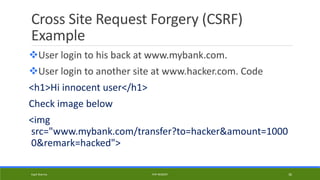
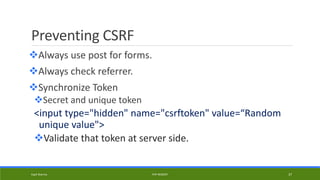
The document discusses web application security and provides an overview of common vulnerabilities like SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). It summarizes the OWASP Top 10 list of most critical web app security risks, including injection flaws, broken authentication, sensitive data exposure, and more. The document also offers best practices for developing more securely, like using prepared statements, validating and sanitizing input, and implementing authentication and session management properly.

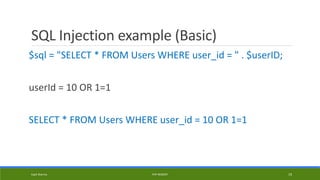
![SQL Injection example
<?PHP
$password_hash = md5($_POST['password']);
$sql = "SELECT count(*)
FROM users
WHERE username = '{$_POST['username']}'
AND password = '$password_hash' ";
Kapil Sharma PHP REBOOT 20](https://image.slidesharecdn.com/webapplicationsecurity-140803040129-phpapp02/85/Web-application-security-20-320.jpg)
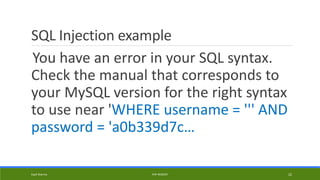
![SQL Injection example
<?PHP
$password_hash = md5($_POST['password']);
$sql = "SELECT count(*)
FROM users
WHERE username = '{$_POST['username']}'
AND password = '$password_hash' ";
mysql_query($sql) or exit(mysql_error)
Username = '
SELECT count(*)
FROM users
WHERE username = '''
AND password = '<md5 hash>'
Kapil Sharma PHP REBOOT 21](https://image.slidesharecdn.com/webapplicationsecurity-140803040129-phpapp02/85/Web-application-security-21-320.jpg)
![SQL Injection example
<?PHP
$password_hash = md5($_POST['password']);
$sql = "SELECT count(*)
FROM users
WHERE username = '{$_POST['username']}'
AND password = '$password_hash' ";
mysql_query($sql) or exit(mysql_error)
Username = kapil' or 'a' = 'a' --
Kapil Sharma PHP REBOOT 23](https://image.slidesharecdn.com/webapplicationsecurity-140803040129-phpapp02/85/Web-application-security-23-320.jpg)

![Securing Session with PHP
static protected function preventHijacking() {
if(!isset($_SESSION['IpAddress']) || !isset($_SESSION['userAgent']))
return false;
if ($_SESSION['IPaddress'] != $_SERVER['REMOTE_ADDR'])
return false;
if( $_SESSION['userAgent'] != $_SERVER['HTTP_USER_AGENT'])
return false;
return true;
}
Kapil Sharma PHP REBOOT 29](https://image.slidesharecdn.com/webapplicationsecurity-140803040129-phpapp02/85/Web-application-security-29-320.jpg)
![Non-Persistent XSS attack example
$name = $_GET['name'];
echo "Welcome $name<br>";
echo "<a href="http://mysite.com/">Click to
Download</a>";
Kapil Sharma PHP REBOOT 33](https://image.slidesharecdn.com/webapplicationsecurity-140803040129-phpapp02/85/Web-application-security-33-320.jpg)
![Non-Persistent XSS attack example
$name = $_GET['name'];
echo "Welcome $name<br>";
echo "<a
href="http://mysite.com/">Click to
Download</a>";
index.php?name=<script>windo
w.onload = function() {var
link=document.getElementsByT
agName("a");link[0].href="http:
//attacker.com/";}</script>
Kapil Sharma PHP REBOOT 34
Escape output](https://image.slidesharecdn.com/webapplicationsecurity-140803040129-phpapp02/85/Web-application-security-34-320.jpg)
![Filter Input (Core PHP)
filter_input($type, $variable_name[,$filter[,$options]])
ZF: Zend_Filter_Input, Zend_Filter
Symfony: Allow YAML, Annotation, XML and PHP filters.
Kapil Sharma PHP REBOOT 47](https://image.slidesharecdn.com/webapplicationsecurity-140803040129-phpapp02/85/Web-application-security-47-320.jpg)